attentionstealthy
stealthy 时间:2021-01-12 阅读:()
WhitePaperVMwareandtheNeedforCyberSupplyChainSecurityAssuranceByJonOltsik,SeniorPrincipalAnalystSeptember2015ThisESGWhitePaperwascommissionedbyVMwareandisdistributedunderlicensefromESG.
2015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance22015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ContentsExecutiveSummary3CyberSupplyChainSecurityRealities3CyberSupplyChainSecurityCanBeDifficult4CISOsareBolsteringCyberSupplyChainSecurityOversight.
5CyberSupplyChainSecurityAssurance.
7TheVMwareTrust&AssuranceFramework.
8TheBiggerTruth10Alltrademarknamesarepropertyoftheirrespectivecompanies.
InformationcontainedinthispublicationhasbeenobtainedbysourcesTheEnterpriseStrategyGroup(ESG)considerstobereliablebutisnotwarrantedbyESG.
ThispublicationmaycontainopinionsofESG,whicharesubjecttochangefromtimetotime.
ThispublicationiscopyrightedbyTheEnterpriseStrategyGroup,Inc.
Anyreproductionorredistributionofthispublication,inwholeorinpart,whetherinhard-copyformat,electronically,orotherwisetopersonsnotauthorizedtoreceiveit,withouttheexpressconsentofTheEnterpriseStrategyGroup,Inc.
,isinviolationofU.
S.
copyrightlawandwillbesubjecttoanactionforcivildamagesand,ifapplicable,criminalprosecution.
Shouldyouhaveanyquestions,pleasecontactESGClientRelationsat508.
482.
0188.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance32015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ExecutiveSummaryThecommonsaying,"mayyouliveininterestingtimes"isactuallytheEnglishtranslationofatraditionalChinesecurse.
ThisrealityissomewhatironicasCISOsandcybersecurityprofessionalswouldlikelyagreethattheyindeedliveinaveryinterestingbutdifficulttime.
WhyCyberthreatshavebecomemoreubiquitous,stealthy,andtargetedwhiletheITattacksurfacecontinuestoexpand,drivenbycloudcomputing,InternetofThings(IoT)initiatives,andmobileapplicationuse.
EnterpriseorganizationsnowrealizethatweliveinauniquetimeofincreasingITriskandarerespondingaccordingly.
Corporateexecutivesandboardsareparticipatingmoreintheirorganizations'cybersecuritystrategiestomitigatebusinessandtechnologyrisk.
Manyfirmshaveincreasedcybersecuritybudgetsaswellandarenowpurchasinganddeployingapotpourriofnewsecurityanalyticssystemsandlayersofdefense.
Allofthisactivityisastepintherightdirection—butitisjustnotenough.
VMwarehasintroducedanewinitiativecalled"VMwareTrustandAssurance,"whichhelpsanswercustomers'questionsaboutVMware'ssecurityanddevelopmentpracticesandprovidesgreatertransparencyaroundhowitdevelops,builds,secures,andsupportsitsapplications.
Thiswhitepaperconcludes:Organizationsareexposedtovulnerabilitiesinthecybersupplychain.
Thecybersupplychainintroducestheriskthataproductorservicecouldbecompromisedbyvulnerabilitiesand/ormaliciouscodeintroducedadvertentlyorinadvertentlyduringproductdevelopmentormaintenance,dueinparttoincreasingglobalizationoftheITsupplychain.
Consequently,ITproductsandservicesbuiltonafoundationofbroaddiversecybersupplychainsmayincreasetheriskofadevastatingcyber-attacktocustomers.
ITrisksarenotlimitedtocorporateLANs,WANs,anddatacenters.
Rather,enterprisesremainatriskforcyber-attacksthattakeadvantageofvulnerabilitiesexistinginITequipment,businesspartnernetworks,non-employeedevices,etc.
Asthesayinggoes,"thecybersecuritychainisonlyasstrongasitsweakestlink.
"Regrettably,muchofthecybersecuritychainresidesoutsidetheperimeterfirewallandthusneedsproperoversight,cybersecuritybestpractices,andamplelayersofdefense.
CISOsarepushingbackonITvendors.
PragmaticcybersecurityprofessionalsnowrealizethattheirstrategicITvendorscanmakeorbreakthecybersecuritychain.
Intheworstcase,insecurepartnersorITsystemscanbeusedasastaginggroundforadevastatingdatabreach.
Tominimizerisk,manyenterpriseorganizationsareaddressingcybersupplychainsecuritybyauditingITvendors'securityprocessesandmakingpurchasingdecisionsbaseduponavendor'sabilitytomeetincreasinglyrigorouscybersecurityrequirements.
ITvendorsmustdevelopcybersupplychainsecurityassurancecapabilities;TheVMwareTrustandAssuranceFrameworkservesasamodelfortheindustry.
Enterprisecybersecurityrequirementswillcontinuetobecomemorerigidinthefuture.
Asthissituationevolves,CISOswillonlydobusinesswithtrustedITvendorswithdemonstrablecybersupplychainsecurityassuranceprogramsthatincludeallaspectsoftheirproductdevelopment,testing,distribution,deployment,customization,andsupport.
VMware'sTrust&Assuranceinitiativeservesasamodelofthetransparencyneededforcybersupplychainsecurityfortheindustry.
CISOsshoulddemandasimilarresponsefromallstrategicITvendors.
CyberSupplyChainSecurityRealitiesOrganizationslargeandsmallarechangingtheirbehaviorwithregardstocybersecurityinresponsetotheincreasinglydangerousthreatlandscapeandhighly-publicizeddatabreaches.
Infact,manyorganizationsnolongerconsidercybersecurityanITissuealone.
Alternatively,cybersecurityriskisnowabusinessprioritythatgetsampleattentionwithbusinessexecutivesandcorporateboards.
AccordingtoESGresearch:WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance42015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Whenaskedtoidentifythebiggestdriverfortechnologyspendingoverthenext12months,46%oforganizationspointedtosecurityandriskmanagementinitiatives.
Thiswasthemostpopularresponse,quiteabithigherthanthesecondmostpopularanswer,"costreductioninitiatives,"whichcameinat37%.
Justoverone-thirdoforganizations(34%)saythatInformationsecurityinitiativesarethemostimportantITprioritythisyear.
Onceagain,thiswasthetopresponse.
59%oforganizationssaidthattheirITsecuritybudgetsfor2015wouldincreasewhileonly9%saidtheywoulddecreaseinfosecbudgetsthisyear.
1Increasingfocusoncybersecurityhasresultedinlotsofactivity,asmanyorganizationsaddlayersofdefensetotheirnetworks,implementnewsolutionsforincidentdetectionandresponse,andbolstersecuritymonitoringandanalyticsefforts.
TheseinternaleffortsareagoodstartbutagrowingnumberofCISOsrealizethatcybersecurityriskextendsbeyondtheLAN,WAN,andcorporatedatacenterstoalargerpopulationofcustomers,suppliers,andbusinesspartners.
Thislargercybersecurityuniverseissometimesreferredtoasthecybersupplychain,whichESGdefinesas:"Theentiresetofkeyactorsinvolvedwith/usingcyberinfrastructure:systemend-users,policymakers,acquisitionspecialists,systemintegrators,networkproviders,andsoftwarehardwaresuppliers.
Theseusers/providers'organizationalandprocess-levelinteractionstoplan,build,manage,maintain,anddefendcyberinfrastructure.
"Cybersupplychainsecurityissuesarenotuncommon.
Forexample:In2008,theFBIseized$76millionofcounterfeitCiscoequipment.
AspartoftheStuxnetincidentin2010,fivecompaniesactingascontractorsfortheIraniannuclearprogramhadtheirnetworkscompromisedinordertogaintrustedaccesstogovernmentnuclearfacilities.
Thesuccessful2013databreachatTargetCorporationwaseventuallytracedtosystemcompromisesatFazioBrothers,oneofTarget'sHVACcontractors.
HackersusedFazioBrothersasastaginggroundandusedthecompany'snetworkaccessasanattackvector.
CyberSupplyChainSecurityCanBeDifficultSomeCISOsrecognizetherisksassociatedwiththeircybersupplychainsecurityandthisisespeciallytruefororganizationsthatdependuponarmiesofexternalbusinesspartners,contractors,orsuppliersaspartoftheirbusinessoperations.
Unfortunately,cybersupplychainsecuritybestpracticesaren'teasyastheyrequireconstantoversightofthestateofcybersecurityrelatedtoITequipmentproviders,softwarevendors,connectedbusinesspartners,etc.
Infact,cybersupplychainsecurityseemstobegrowingincreasinglyproblematicforsomefirms.
InarecentESGresearchsurveyofcriticalinfrastructuresectororganizations(i.
e.
,chemicalsector,emergencyservices,energysector,financialservices,healthcare,telecommunications,etc.
),40%ofcybersecurityprofessionalsadmittedthatcybersupplychainsecurityhasbecomemoredifficultoverthepastfewyears,andthosewhodidsuppliednumerousreasonsforthatincreaseddifficulty(seeFigure1):44%ofcriticalinfrastructuresectororganizationssaythattheirorganizationhasimplementednewtypesofITinitiatives,increasingthecybersupplychainattacksurface.
TheseinitiativesincludeBYOD,cloudcomputing,InternetofThings(IoT)projects,andthegrowinguseofmobileapplicationsanddevices.
39%ofcriticalinfrastructuresectororganizationssaytheirorganizationhasmoresuppliersthanitdidtwoyearsago.
Thisistobeexpected,giventhewaveofITinnovationaroundsoftware-defineddatacenters,cloudplatforms,virtualnetworks,etc.
36%ofcriticalinfrastructuresectororganizationssaythattheirorganizationhasconsolidatedITandoperationaltechnology(OT),increasingthecomplexityofcybersupplychainsecurity.
Inthesecases,CISOs1Source:ESGResearchReport,2015ITSpendingIntentionsSurvey,February2015.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance52015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
areforcedtosecurebusiness-criticalbutunfamiliartechnologieslikeprogrammablelogiccontrollers(PLCs)andsupervisorycontrolanddataacquisition(SCADA)systemsusedforindustrialoperations.
2Figure1.
ReasonsWhyCyberSupplyChainSecurityHasBecomeMoreDifficultSource:EnterpriseStrategyGroup,2015.
AsidefromtheassortmentofissuesdescribedinFigure1,CISOsoftenvoiceotherconcernstoESG.
Forexample,manysecurityexecutivesareanxiousaboutthegrowinguseofopensourcecomponents(andvulnerabilities)aspartofcommercialsoftware(i.
e.
,Heartbleed,OpenSSL,Shellshock,etc.
).
CISOsalsoworryaboutthingslikerogueinsidersworkingforITsuppliersanddataprivacyrelatedtosensitiveinformationmovedtothecloudbyITvendorsandbusinesspartners.
Dataprivacyandcybersupplychainsecurityissuescanalsobeasourceconcerndrivenbyglobal"follow-the-sun"developmentpracticesandcloudarchitectures,aswellasemergingregulationsliketheEUDigitalSingleMarketinitiative.
CISOsareBolsteringCyberSupplyChainSecurityOversightAscybersecuritymorphsfromatechnologytoabusinessissue,CEOsandcorporateboardsaregainingabetterperspectiveofcybersupplychainsecurityrisks.
Thisisdrivingachainreaction—businessexecutivesarepushingCISOstomitigatecybersupplychainrisk,causingcybersecurityexecutivesandpurchasingmanagerstoplacemorestringentcybersecurityrequirementsontheirITvendors.
2Source:ESGResearchReport,CyberSupplyChainSecurityRevisited,September2015.
AllESGresearchreferencesandchartsinthiswhitepaperhavebeentakenfromthisresearchreportunlessotherwisenoted.
34%34%36%39%44%0%5%10%15%20%25%30%35%40%45%50%MyorganizationhassourcedITproducts,components,andservicesfromothercountriesoverthepastfewyearsandthesechangesmaybeincreasingcybersupplychainsecurityriskMyorganizationhasincreasedthenumberofexternalthird-partieswithaccesstoourinternalITassetswhichhasincreasedthecybersupplychainattacksurfaceMyorganizationhasconsolidatedITandoperationaltechnologysecuritywhichhasincreasedthecomplexityofcybersupplychainsecurityMyorganizationhasmoresuppliersthanitdidafewyearsagoMyorganizationhasimplementednewtypesofITinitiativeswhichhasincreasedthecybersupplychainattacksurfaceYouindicatedthatcybersupplychainsecurityhasbecomemoredifficultatyourorganizationoverthepastfewyears.
Whydoyoubelievethatthisisthecase(Percentofrespondents,N=180,multipleresponsesaccepted)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance62015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ESGresearchillustratesthistrendwithanextensivearrayofsecurityconsiderationsforITvendorsascriticalinfrastructuresectororganizationsevaluateandpurchaseITproductsandservices.
Forexample,35%examineavendor'sexperienceandtrackrecordrelatedtosecurityvulnerabilitiesandsoftwarepatches,35%lookatavendor'soverallsecurityexpertiseandreputation,and32%contemplateavendor'sreputationandindustryexpertise(seeFigure2).
Figure2.
CybersecurityEvaluationConsiderationsforITPurchasingofProductsandServicesSource:EnterpriseStrategyGroup,2015.
TofurtherappraiseITvendorsecurity,manyorganizationsarealsoadoptingaformalcybersecurityauditprocessaspartoftheirITprocurementprocess.
Forexample,91%ofcriticalinfrastructuresectororganizationsauditthecybersecurityoftheirstrategicsoftwarevendors(i.
e.
,alwaysconductauditsordosoonanas-neededbasis),90%auditthecybersecurityoftheircloudserviceproviders,and88%auditthecybersecurityoftheirstrategicITinfrastructurevendors.
9%14%17%18%20%22%24%29%31%32%35%35%0%10%20%30%40%Locationofvendor'scorporateheadquartersLocationofvendor'sproductdevelopmentand/ormanufacturingoperationsVendor'suseofthird-partiesaspartofitsoverallproductdevelopment,manufacturing,testing,andmaintenanceVendor'sformalanddocumentedsecureproductdevelopmentprocessesVendor'sISOcertificationSecuritybreachesofvendororganizationVendor'semergencyresponse/problemescalationproceduresVendor'sprofessionalservicesofferingsforsecureITproductassessment,planning,anddeploymentVendor'sreputationandexpertiseinourindustryVendor'scybersupplychainriskmanagementprocessesVendor'soverallsecurityexpertise/reputationVendor'sexperienceandtrackrecordrelatedtosecurityvulnerabilitiesandsubsequentfixesofitsproductsThefollowingisalistofsecurityconsiderationsanorganizationmayevaluatebeforepurchasingITproductsandservices.
Whichofthefollowingconsiderationsaremostimportanttoyourorganizationduringtheproductevaluationandpurchaseprocess(Percentofrespondents,N=303,threeresponsesacceptedperrespondent)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance72015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Theseauditsarebecomingincreasinglycomprehensive.
AsESGresearchillustrates,ITvendorcybersecurityauditsincludethingslikehandsonreviewsofavendor'ssecurityhistory,reviewsofavendor'ssecuritydocumentation,processes,andmetrics,andreviewsofvendors'owninternalITandcomplianceaudits(seeFigure3).
Figure3.
MechanismsUsedInITVendorAuditsSource:EnterpriseStrategyGroup,2015.
CyberSupplyChainSecurityAssuranceTheESGresearchpresentsaclearpicture—high-securityenterpriseorganizationsareincreasinglydemandinggreatercybersecuritybestpracticesfromtheirstrategicITvendors.
Furthermore,vendors'cybersecuritypolicies,processes,andmetricsarebecomingadeterminingfactorforITprocurementasadvancedorganizationsarenowselectingstrategicITvendorsbaseduponanewstandard,cybersupplychainsecurityassurance,definedas:28%30%40%42%44%49%51%52%54%0%10%20%30%40%50%60%SendvendorastandardlistofquestionsonpaperandthenreviewtheirresponsesOn-siteinspection(s)ofvendor'sfacilitiesReviewanyrecentpenetrationtestingresultsandsubsequentremediationplansDemandvendorcertificationsHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'ssecurityprocessesHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'sproductdevelopmentprocessesReviewofvendor'ssecurityauditsHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'ssupplychainsecurityprocessesHands-onreviewofvendor'ssecurityhistoryYouhaveindicatedthatyourorganizationconductsauditsofitsITvendors'securityprocesses.
WhichofthefollowingmechanismsdoesyourorganizationusetoconducttheseITvendorsecurityaudits(Percentofrespondents,N=294,multipleresponsesaccepted)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance82015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Cybersupplychainsecurityassuranceisthepracticeofmanagingcybersupplychainrisksrelatedtothepeople,processes,andtechnologiesusedtodesign,develop,produce,distribute,andimplementIThardware,software,andservices.
Toparsethisdefinitionfurther,cybersupplychainsecurityassuranceincludes:Secureproductdevelopment.
Thisincludesasecuresoftwaredevelopmentlifecycle,assessment,andtestingofopensourceandthirdpartycodeincludedinvendorproducts,andconsiderationofthecybersecuritypracticesofallcontractorsandsuppliersthatparticipateinsoftwaredevelopmentorhardwarebillofmaterials.
Adequatesecurityskills.
Tominimizerisksassociatedwithhumanerror,productdevelopers,testers,andotherhandlersmusthavesuitableandup-to-datecybersecurityskills.
Therightcybersecurityprocessesandprocedures.
Vendorsmustbacktheirday-to-dayoperationswithcybersecuritybestpracticesforriskmanagement,threatprevention,andincidentresponse.
Additionally,ITvendorsmustemploycybersecuritybestpracticesforinternalITthemselves.
Field-levelcybersecurityexpertise.
EvenwhencybersecurityfeaturesareembeddedinITsystems,overwhelmedcustomersmaynotknowhowtoconfiguredevicesorcustomizesystemsfortheirindividualsecurityneeds.
Vendorswithleadingcybersupplychainsecurityassuranceskillshavefield-levelemployeesorpartnerswhocanhelpcustomersconsumeandbenefitfromproductsecurityfeaturesandfunctionalityupondeploymentandcontinuallyovertime.
Strongcybersecuritycustomersupport.
Whilevendorsshoulddoalltheycantodevelop,distribute,anddeploysecureproducts,theyalsomusthavetherightpreparationforinevitablesecurityvulnerabilities.
Cybersupplychainsecurityassurancedemandsthatvendors'securityteamsmonitorthelatestattacktrendsandworkwiththegreatersecuritycommunitytoensuretimelyawarenessofnewvulnerabilitiesthatcouldimpacttheirproducts.
Oncevulnerabilitiesaredetected,vendorsmustalsohavehighlyefficientprocessesfordeveloping,testing,anddistributingsoftwarepatches.
Finally,vendorsmusthaveahighlytrainedstafftoguidecustomersthroughsecurityfixesasneeded.
TheVMwareTrust&AssuranceFrameworkESGbelievesthatcybersupplychainsecurityassuranceisstartingtohaveamarketimpact,creatingaclearlineofdelineationbetweenITvendorswithtruecybersecuritycommitmentsandthosethatremainbehind.
Sadly,manyITvendorshavenotembracedtherightlevelofcybersupplychainsecurityassurance,puttingtheircustomersatrisk.
Sinceitsformationin1998,VMwareCorporationhasgrownandevolveditsroleatenterpriseorganizations.
Earlyon,VMwareservervirtualizationtechnologywasusedprimarilybyITdepartmentsforsoftwaretestinganddevelopment.
Overtime,largeorganizationsembracedVMwareinproductiondatacentersforserverconsolidation.
Mostrecently,VMwarehasbecomeastrategicITvendoratmanyenterpriseorganizationsasVMwaretechnologyisoftendeployedonendpoints,indatacenters,andacrosspublicandprivatecloudinfrastructure.
AsitadvancedfromtacticaltostrategicITvendor,VMwarefacedapatternofincreasingcybersecurityscrutinyfromdemandingpublicandprivatesectorcustomers.
Toaddressthis,VMwaremanagementintroducedaninternalfocusoncontinuouscybersecurityimprovementseveralyearsago.
ThiseffortculminatedrecentlywithaninitiativecalledVMwareTrust&Assurance,whichiscomposedoffourguidingprinciples:Reliability.
WithintheVMwareTrust&Assuranceframework,thecommitmenttoreliabilityincludes:ProductperformanceandscalabilityinordertoensurethatVMwareproductscanmeetenterprisedemands.
ApervasivecultureofevangelismandeducationtokeepVMwareemployeesandcustomerseducatedandengagedonrapidly-changingcybersecurityrisks.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance92015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ResearchdedicatedtoenhancingVMwareproductperformanceandreliabilitywhileworkingwithcustomersonassociatedprojectplanning,testing,deployment,andoptimization.
QualitymetricsandcontinuousimprovementassociatedwithVMwareproducts,people,andpartners.
Integrity.
ThisprinciplealignswithVMware'ssoftwaredevelopmentandcomprises:TheVMwaresoftwaredevelopmentlifecycle.
VMwarehadbuiltadevelopmentprocessthatincludesformalrepeatableprocessesforsoftwaredesign,testing,documentation,release,andongoingsupport.
Complianceandrisk.
Alongwithitspartners,VMwaredevelopedthecompliancereferencearchitectureframework(RAF)thatalignsitstechnologywithregulatorycompliancerequirementsacrossindustries.
Softwaresupplychainmanagement.
VMwareisaddressingitsowncybersupplychainpracticesinanumberofareasincludingIPprotection,sourcecodesharing,riskmanagementassessment,andproactivesoftwaresecurityprogramswithstrategicpartnersandsuppliers.
Privacy.
Toprotectcustomerprivacy,VMwaredefinesitsprivacypolicytocustomers,specifyingwhatdataitcollectsandhowitisused.
VMwarefollowsa"privacybydesign"frameworktoprovidetransparencyonprivacyasitrelatestoproducts,services,andsupport.
Security.
VMwarehasintroducedstrongcybersecuritythroughoutitsorganization.
Examplesofthisinclude:Productsecurity.
VMwarehascreatedaproductsecurityteamresponsibleforoversightofallproductsecurity.
Thisgroupsupervisessecuritydevelopmentprocessesandmetricswitheachproductteamandisresponsiblefordemonstratingcontinuousimprovement.
Securitydevelopmentlifecycle.
Thisextendsbeyondthesecuresoftwaredevelopmentlifecycleandincludessecuritytraining,planning,serviceability,aswellasresponseplanning,productsecurityrequirementsassessment,andoverallsecuritymonitoring.
Thesecurityresponsecenter.
VMwareemploysateamofsecurityresearchers,softwaredevelopers,andsupportstafftofindvulnerabilities,developfixes,andworkwithcustomersandpartnersfortimelydistributionanddeploymentofsecurityfixes.
ITsecurity.
Likealllargeenterprises,VMware'scorporateinfrastructureisundercontinualattacksfrommaliciousindividualsandentities.
Toaddressthisrisk,VMwaremaintainscybersecuritybestpracticesoninternalnetworksandsystems.
Commitment.
Tomakecybersupplychainsecurityassurancepervasiveineverythingitdoes,VMwarehasmadecybersecuritypartofitscorporateculture.
Ofcourse,thisrequiresatruecybersecuritycommitmentincluding:Continuingproductdevelopment.
VMwarehasestablishedacontinuingproductdevelopmentorganization,whichactsasasinglepoint-of-contactforaddressing,escalating,andresolvingproductandcustomercybersecurityissues.
Ecosystemservices.
VMwareunderstandsthatitscybersecuritysupplychainincludesanetworkofhundredsofotherITvendorandservicespartners.
VMwareprovidestechnicalsupport,testing,cooperativesupportservices,andrules-of-engagementtoensurestrongcybersecurityinthefield.
Customeradvocacy.
VMwarerecognizesthatcybersecurityprofessionalsareacommunityoflike-mindedindividualswithafewcommongoals—mitigatingITriskandprotectingcriticalITassetsanddata.
Tosucceed,VMwaredependsuponapartnershipofequalswithVMwareWhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance102015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
participatinginthecybersecuritycommunityratherthandictatingitsownITvendoragenda.
VMwareseekstofacilitatethisrelationshipwithsecurityresearch,workshops,benchmarks,securityeducation,andsocialmediacampaigns.
WithitsTrust&Assuranceinitiative,VMwareistakinga360degreeperspectiveoncybersecuritythatencompassesitsproducts,partners,customers,employees,andthecybersecuritycommunityatlarge.
Inthisway,VMwarehasnotonlyrespondedtoitsenterprisecustomers'needforgreatertransparencyrelatedtocybersupplychainsecurity,butisalsosettinganexamplethatshouldbeemulatedbyotherITvendors.
TheBiggerTruthCISOsfaceadauntingareaofchallenges.
Cyberthreatsgrowmorevoluminous,sophisticated,andtargetedwhileITinfrastructuregetsmorecomplexasnetworkperimetersdisappear.
Yes,thesechangesdemandanincreasingcommitmenttocybersecurityoversight,riskmanagement,andtightsecuritycontrolsbuttheseeffortssimplycan'tbelimitedtocorporateLANs,WANs,anddatacenters.
Rather,CISOsmustunderstandtherisksassociatedwiththeircybersupplychains,andestablishbestpracticesforcybersupplychainsecurity.
ESGresearchindicatesthatthistransitionisalreadyinprogress,causingmanyorganizationstoauditthesecurityoftheirITproductandservicesvendors.
Leadingedgeenterprisesarealsomakingpurchasingdecisionsbasedupontheirvendors'cybersupplychainsecurityassuranceprograms.
Movingforward,moreorganizationswilllikelyfollowsuit.
UnlikemanyotherenterpriseITvendors,VMwareiswellpreparedforthisincreasinglevelofcybersecurityoversight.
Infact,theVMwareTrust&Assuranceinitiativeisdesignedtomeetandexceedthegrowingneedforgreatertransparencyrelatedtoenterprisecybersecurity.
Assuch,VMwareissettinganexamplefortheITindustryatlarge.
CISOswouldbewellservedtodemandsimilarcybersupplychainsecurityassurancefromALLoftheirstrategicITvendors.
20AsylumStreet|Milford,MA01757|Tel:508.
482.
0188Fax:508.
482.
0218|www.
esg-global.
com
2015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance22015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ContentsExecutiveSummary3CyberSupplyChainSecurityRealities3CyberSupplyChainSecurityCanBeDifficult4CISOsareBolsteringCyberSupplyChainSecurityOversight.
5CyberSupplyChainSecurityAssurance.
7TheVMwareTrust&AssuranceFramework.
8TheBiggerTruth10Alltrademarknamesarepropertyoftheirrespectivecompanies.
InformationcontainedinthispublicationhasbeenobtainedbysourcesTheEnterpriseStrategyGroup(ESG)considerstobereliablebutisnotwarrantedbyESG.
ThispublicationmaycontainopinionsofESG,whicharesubjecttochangefromtimetotime.
ThispublicationiscopyrightedbyTheEnterpriseStrategyGroup,Inc.
Anyreproductionorredistributionofthispublication,inwholeorinpart,whetherinhard-copyformat,electronically,orotherwisetopersonsnotauthorizedtoreceiveit,withouttheexpressconsentofTheEnterpriseStrategyGroup,Inc.
,isinviolationofU.
S.
copyrightlawandwillbesubjecttoanactionforcivildamagesand,ifapplicable,criminalprosecution.
Shouldyouhaveanyquestions,pleasecontactESGClientRelationsat508.
482.
0188.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance32015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ExecutiveSummaryThecommonsaying,"mayyouliveininterestingtimes"isactuallytheEnglishtranslationofatraditionalChinesecurse.
ThisrealityissomewhatironicasCISOsandcybersecurityprofessionalswouldlikelyagreethattheyindeedliveinaveryinterestingbutdifficulttime.
WhyCyberthreatshavebecomemoreubiquitous,stealthy,andtargetedwhiletheITattacksurfacecontinuestoexpand,drivenbycloudcomputing,InternetofThings(IoT)initiatives,andmobileapplicationuse.
EnterpriseorganizationsnowrealizethatweliveinauniquetimeofincreasingITriskandarerespondingaccordingly.
Corporateexecutivesandboardsareparticipatingmoreintheirorganizations'cybersecuritystrategiestomitigatebusinessandtechnologyrisk.
Manyfirmshaveincreasedcybersecuritybudgetsaswellandarenowpurchasinganddeployingapotpourriofnewsecurityanalyticssystemsandlayersofdefense.
Allofthisactivityisastepintherightdirection—butitisjustnotenough.
VMwarehasintroducedanewinitiativecalled"VMwareTrustandAssurance,"whichhelpsanswercustomers'questionsaboutVMware'ssecurityanddevelopmentpracticesandprovidesgreatertransparencyaroundhowitdevelops,builds,secures,andsupportsitsapplications.
Thiswhitepaperconcludes:Organizationsareexposedtovulnerabilitiesinthecybersupplychain.
Thecybersupplychainintroducestheriskthataproductorservicecouldbecompromisedbyvulnerabilitiesand/ormaliciouscodeintroducedadvertentlyorinadvertentlyduringproductdevelopmentormaintenance,dueinparttoincreasingglobalizationoftheITsupplychain.
Consequently,ITproductsandservicesbuiltonafoundationofbroaddiversecybersupplychainsmayincreasetheriskofadevastatingcyber-attacktocustomers.
ITrisksarenotlimitedtocorporateLANs,WANs,anddatacenters.
Rather,enterprisesremainatriskforcyber-attacksthattakeadvantageofvulnerabilitiesexistinginITequipment,businesspartnernetworks,non-employeedevices,etc.
Asthesayinggoes,"thecybersecuritychainisonlyasstrongasitsweakestlink.
"Regrettably,muchofthecybersecuritychainresidesoutsidetheperimeterfirewallandthusneedsproperoversight,cybersecuritybestpractices,andamplelayersofdefense.
CISOsarepushingbackonITvendors.
PragmaticcybersecurityprofessionalsnowrealizethattheirstrategicITvendorscanmakeorbreakthecybersecuritychain.
Intheworstcase,insecurepartnersorITsystemscanbeusedasastaginggroundforadevastatingdatabreach.
Tominimizerisk,manyenterpriseorganizationsareaddressingcybersupplychainsecuritybyauditingITvendors'securityprocessesandmakingpurchasingdecisionsbaseduponavendor'sabilitytomeetincreasinglyrigorouscybersecurityrequirements.
ITvendorsmustdevelopcybersupplychainsecurityassurancecapabilities;TheVMwareTrustandAssuranceFrameworkservesasamodelfortheindustry.
Enterprisecybersecurityrequirementswillcontinuetobecomemorerigidinthefuture.
Asthissituationevolves,CISOswillonlydobusinesswithtrustedITvendorswithdemonstrablecybersupplychainsecurityassuranceprogramsthatincludeallaspectsoftheirproductdevelopment,testing,distribution,deployment,customization,andsupport.
VMware'sTrust&Assuranceinitiativeservesasamodelofthetransparencyneededforcybersupplychainsecurityfortheindustry.
CISOsshoulddemandasimilarresponsefromallstrategicITvendors.
CyberSupplyChainSecurityRealitiesOrganizationslargeandsmallarechangingtheirbehaviorwithregardstocybersecurityinresponsetotheincreasinglydangerousthreatlandscapeandhighly-publicizeddatabreaches.
Infact,manyorganizationsnolongerconsidercybersecurityanITissuealone.
Alternatively,cybersecurityriskisnowabusinessprioritythatgetsampleattentionwithbusinessexecutivesandcorporateboards.
AccordingtoESGresearch:WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance42015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Whenaskedtoidentifythebiggestdriverfortechnologyspendingoverthenext12months,46%oforganizationspointedtosecurityandriskmanagementinitiatives.
Thiswasthemostpopularresponse,quiteabithigherthanthesecondmostpopularanswer,"costreductioninitiatives,"whichcameinat37%.
Justoverone-thirdoforganizations(34%)saythatInformationsecurityinitiativesarethemostimportantITprioritythisyear.
Onceagain,thiswasthetopresponse.
59%oforganizationssaidthattheirITsecuritybudgetsfor2015wouldincreasewhileonly9%saidtheywoulddecreaseinfosecbudgetsthisyear.
1Increasingfocusoncybersecurityhasresultedinlotsofactivity,asmanyorganizationsaddlayersofdefensetotheirnetworks,implementnewsolutionsforincidentdetectionandresponse,andbolstersecuritymonitoringandanalyticsefforts.
TheseinternaleffortsareagoodstartbutagrowingnumberofCISOsrealizethatcybersecurityriskextendsbeyondtheLAN,WAN,andcorporatedatacenterstoalargerpopulationofcustomers,suppliers,andbusinesspartners.
Thislargercybersecurityuniverseissometimesreferredtoasthecybersupplychain,whichESGdefinesas:"Theentiresetofkeyactorsinvolvedwith/usingcyberinfrastructure:systemend-users,policymakers,acquisitionspecialists,systemintegrators,networkproviders,andsoftwarehardwaresuppliers.
Theseusers/providers'organizationalandprocess-levelinteractionstoplan,build,manage,maintain,anddefendcyberinfrastructure.
"Cybersupplychainsecurityissuesarenotuncommon.
Forexample:In2008,theFBIseized$76millionofcounterfeitCiscoequipment.
AspartoftheStuxnetincidentin2010,fivecompaniesactingascontractorsfortheIraniannuclearprogramhadtheirnetworkscompromisedinordertogaintrustedaccesstogovernmentnuclearfacilities.
Thesuccessful2013databreachatTargetCorporationwaseventuallytracedtosystemcompromisesatFazioBrothers,oneofTarget'sHVACcontractors.
HackersusedFazioBrothersasastaginggroundandusedthecompany'snetworkaccessasanattackvector.
CyberSupplyChainSecurityCanBeDifficultSomeCISOsrecognizetherisksassociatedwiththeircybersupplychainsecurityandthisisespeciallytruefororganizationsthatdependuponarmiesofexternalbusinesspartners,contractors,orsuppliersaspartoftheirbusinessoperations.
Unfortunately,cybersupplychainsecuritybestpracticesaren'teasyastheyrequireconstantoversightofthestateofcybersecurityrelatedtoITequipmentproviders,softwarevendors,connectedbusinesspartners,etc.
Infact,cybersupplychainsecurityseemstobegrowingincreasinglyproblematicforsomefirms.
InarecentESGresearchsurveyofcriticalinfrastructuresectororganizations(i.
e.
,chemicalsector,emergencyservices,energysector,financialservices,healthcare,telecommunications,etc.
),40%ofcybersecurityprofessionalsadmittedthatcybersupplychainsecurityhasbecomemoredifficultoverthepastfewyears,andthosewhodidsuppliednumerousreasonsforthatincreaseddifficulty(seeFigure1):44%ofcriticalinfrastructuresectororganizationssaythattheirorganizationhasimplementednewtypesofITinitiatives,increasingthecybersupplychainattacksurface.
TheseinitiativesincludeBYOD,cloudcomputing,InternetofThings(IoT)projects,andthegrowinguseofmobileapplicationsanddevices.
39%ofcriticalinfrastructuresectororganizationssaytheirorganizationhasmoresuppliersthanitdidtwoyearsago.
Thisistobeexpected,giventhewaveofITinnovationaroundsoftware-defineddatacenters,cloudplatforms,virtualnetworks,etc.
36%ofcriticalinfrastructuresectororganizationssaythattheirorganizationhasconsolidatedITandoperationaltechnology(OT),increasingthecomplexityofcybersupplychainsecurity.
Inthesecases,CISOs1Source:ESGResearchReport,2015ITSpendingIntentionsSurvey,February2015.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance52015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
areforcedtosecurebusiness-criticalbutunfamiliartechnologieslikeprogrammablelogiccontrollers(PLCs)andsupervisorycontrolanddataacquisition(SCADA)systemsusedforindustrialoperations.
2Figure1.
ReasonsWhyCyberSupplyChainSecurityHasBecomeMoreDifficultSource:EnterpriseStrategyGroup,2015.
AsidefromtheassortmentofissuesdescribedinFigure1,CISOsoftenvoiceotherconcernstoESG.
Forexample,manysecurityexecutivesareanxiousaboutthegrowinguseofopensourcecomponents(andvulnerabilities)aspartofcommercialsoftware(i.
e.
,Heartbleed,OpenSSL,Shellshock,etc.
).
CISOsalsoworryaboutthingslikerogueinsidersworkingforITsuppliersanddataprivacyrelatedtosensitiveinformationmovedtothecloudbyITvendorsandbusinesspartners.
Dataprivacyandcybersupplychainsecurityissuescanalsobeasourceconcerndrivenbyglobal"follow-the-sun"developmentpracticesandcloudarchitectures,aswellasemergingregulationsliketheEUDigitalSingleMarketinitiative.
CISOsareBolsteringCyberSupplyChainSecurityOversightAscybersecuritymorphsfromatechnologytoabusinessissue,CEOsandcorporateboardsaregainingabetterperspectiveofcybersupplychainsecurityrisks.
Thisisdrivingachainreaction—businessexecutivesarepushingCISOstomitigatecybersupplychainrisk,causingcybersecurityexecutivesandpurchasingmanagerstoplacemorestringentcybersecurityrequirementsontheirITvendors.
2Source:ESGResearchReport,CyberSupplyChainSecurityRevisited,September2015.
AllESGresearchreferencesandchartsinthiswhitepaperhavebeentakenfromthisresearchreportunlessotherwisenoted.
34%34%36%39%44%0%5%10%15%20%25%30%35%40%45%50%MyorganizationhassourcedITproducts,components,andservicesfromothercountriesoverthepastfewyearsandthesechangesmaybeincreasingcybersupplychainsecurityriskMyorganizationhasincreasedthenumberofexternalthird-partieswithaccesstoourinternalITassetswhichhasincreasedthecybersupplychainattacksurfaceMyorganizationhasconsolidatedITandoperationaltechnologysecuritywhichhasincreasedthecomplexityofcybersupplychainsecurityMyorganizationhasmoresuppliersthanitdidafewyearsagoMyorganizationhasimplementednewtypesofITinitiativeswhichhasincreasedthecybersupplychainattacksurfaceYouindicatedthatcybersupplychainsecurityhasbecomemoredifficultatyourorganizationoverthepastfewyears.
Whydoyoubelievethatthisisthecase(Percentofrespondents,N=180,multipleresponsesaccepted)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance62015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ESGresearchillustratesthistrendwithanextensivearrayofsecurityconsiderationsforITvendorsascriticalinfrastructuresectororganizationsevaluateandpurchaseITproductsandservices.
Forexample,35%examineavendor'sexperienceandtrackrecordrelatedtosecurityvulnerabilitiesandsoftwarepatches,35%lookatavendor'soverallsecurityexpertiseandreputation,and32%contemplateavendor'sreputationandindustryexpertise(seeFigure2).
Figure2.
CybersecurityEvaluationConsiderationsforITPurchasingofProductsandServicesSource:EnterpriseStrategyGroup,2015.
TofurtherappraiseITvendorsecurity,manyorganizationsarealsoadoptingaformalcybersecurityauditprocessaspartoftheirITprocurementprocess.
Forexample,91%ofcriticalinfrastructuresectororganizationsauditthecybersecurityoftheirstrategicsoftwarevendors(i.
e.
,alwaysconductauditsordosoonanas-neededbasis),90%auditthecybersecurityoftheircloudserviceproviders,and88%auditthecybersecurityoftheirstrategicITinfrastructurevendors.
9%14%17%18%20%22%24%29%31%32%35%35%0%10%20%30%40%Locationofvendor'scorporateheadquartersLocationofvendor'sproductdevelopmentand/ormanufacturingoperationsVendor'suseofthird-partiesaspartofitsoverallproductdevelopment,manufacturing,testing,andmaintenanceVendor'sformalanddocumentedsecureproductdevelopmentprocessesVendor'sISOcertificationSecuritybreachesofvendororganizationVendor'semergencyresponse/problemescalationproceduresVendor'sprofessionalservicesofferingsforsecureITproductassessment,planning,anddeploymentVendor'sreputationandexpertiseinourindustryVendor'scybersupplychainriskmanagementprocessesVendor'soverallsecurityexpertise/reputationVendor'sexperienceandtrackrecordrelatedtosecurityvulnerabilitiesandsubsequentfixesofitsproductsThefollowingisalistofsecurityconsiderationsanorganizationmayevaluatebeforepurchasingITproductsandservices.
Whichofthefollowingconsiderationsaremostimportanttoyourorganizationduringtheproductevaluationandpurchaseprocess(Percentofrespondents,N=303,threeresponsesacceptedperrespondent)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance72015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Theseauditsarebecomingincreasinglycomprehensive.
AsESGresearchillustrates,ITvendorcybersecurityauditsincludethingslikehandsonreviewsofavendor'ssecurityhistory,reviewsofavendor'ssecuritydocumentation,processes,andmetrics,andreviewsofvendors'owninternalITandcomplianceaudits(seeFigure3).
Figure3.
MechanismsUsedInITVendorAuditsSource:EnterpriseStrategyGroup,2015.
CyberSupplyChainSecurityAssuranceTheESGresearchpresentsaclearpicture—high-securityenterpriseorganizationsareincreasinglydemandinggreatercybersecuritybestpracticesfromtheirstrategicITvendors.
Furthermore,vendors'cybersecuritypolicies,processes,andmetricsarebecomingadeterminingfactorforITprocurementasadvancedorganizationsarenowselectingstrategicITvendorsbaseduponanewstandard,cybersupplychainsecurityassurance,definedas:28%30%40%42%44%49%51%52%54%0%10%20%30%40%50%60%SendvendorastandardlistofquestionsonpaperandthenreviewtheirresponsesOn-siteinspection(s)ofvendor'sfacilitiesReviewanyrecentpenetrationtestingresultsandsubsequentremediationplansDemandvendorcertificationsHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'ssecurityprocessesHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'sproductdevelopmentprocessesReviewofvendor'ssecurityauditsHands-onreviewofdocumentation,processes,securitymetrics,andpersonnelrelatedtoavendor'ssupplychainsecurityprocessesHands-onreviewofvendor'ssecurityhistoryYouhaveindicatedthatyourorganizationconductsauditsofitsITvendors'securityprocesses.
WhichofthefollowingmechanismsdoesyourorganizationusetoconducttheseITvendorsecurityaudits(Percentofrespondents,N=294,multipleresponsesaccepted)WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance82015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
Cybersupplychainsecurityassuranceisthepracticeofmanagingcybersupplychainrisksrelatedtothepeople,processes,andtechnologiesusedtodesign,develop,produce,distribute,andimplementIThardware,software,andservices.
Toparsethisdefinitionfurther,cybersupplychainsecurityassuranceincludes:Secureproductdevelopment.
Thisincludesasecuresoftwaredevelopmentlifecycle,assessment,andtestingofopensourceandthirdpartycodeincludedinvendorproducts,andconsiderationofthecybersecuritypracticesofallcontractorsandsuppliersthatparticipateinsoftwaredevelopmentorhardwarebillofmaterials.
Adequatesecurityskills.
Tominimizerisksassociatedwithhumanerror,productdevelopers,testers,andotherhandlersmusthavesuitableandup-to-datecybersecurityskills.
Therightcybersecurityprocessesandprocedures.
Vendorsmustbacktheirday-to-dayoperationswithcybersecuritybestpracticesforriskmanagement,threatprevention,andincidentresponse.
Additionally,ITvendorsmustemploycybersecuritybestpracticesforinternalITthemselves.
Field-levelcybersecurityexpertise.
EvenwhencybersecurityfeaturesareembeddedinITsystems,overwhelmedcustomersmaynotknowhowtoconfiguredevicesorcustomizesystemsfortheirindividualsecurityneeds.
Vendorswithleadingcybersupplychainsecurityassuranceskillshavefield-levelemployeesorpartnerswhocanhelpcustomersconsumeandbenefitfromproductsecurityfeaturesandfunctionalityupondeploymentandcontinuallyovertime.
Strongcybersecuritycustomersupport.
Whilevendorsshoulddoalltheycantodevelop,distribute,anddeploysecureproducts,theyalsomusthavetherightpreparationforinevitablesecurityvulnerabilities.
Cybersupplychainsecurityassurancedemandsthatvendors'securityteamsmonitorthelatestattacktrendsandworkwiththegreatersecuritycommunitytoensuretimelyawarenessofnewvulnerabilitiesthatcouldimpacttheirproducts.
Oncevulnerabilitiesaredetected,vendorsmustalsohavehighlyefficientprocessesfordeveloping,testing,anddistributingsoftwarepatches.
Finally,vendorsmusthaveahighlytrainedstafftoguidecustomersthroughsecurityfixesasneeded.
TheVMwareTrust&AssuranceFrameworkESGbelievesthatcybersupplychainsecurityassuranceisstartingtohaveamarketimpact,creatingaclearlineofdelineationbetweenITvendorswithtruecybersecuritycommitmentsandthosethatremainbehind.
Sadly,manyITvendorshavenotembracedtherightlevelofcybersupplychainsecurityassurance,puttingtheircustomersatrisk.
Sinceitsformationin1998,VMwareCorporationhasgrownandevolveditsroleatenterpriseorganizations.
Earlyon,VMwareservervirtualizationtechnologywasusedprimarilybyITdepartmentsforsoftwaretestinganddevelopment.
Overtime,largeorganizationsembracedVMwareinproductiondatacentersforserverconsolidation.
Mostrecently,VMwarehasbecomeastrategicITvendoratmanyenterpriseorganizationsasVMwaretechnologyisoftendeployedonendpoints,indatacenters,andacrosspublicandprivatecloudinfrastructure.
AsitadvancedfromtacticaltostrategicITvendor,VMwarefacedapatternofincreasingcybersecurityscrutinyfromdemandingpublicandprivatesectorcustomers.
Toaddressthis,VMwaremanagementintroducedaninternalfocusoncontinuouscybersecurityimprovementseveralyearsago.
ThiseffortculminatedrecentlywithaninitiativecalledVMwareTrust&Assurance,whichiscomposedoffourguidingprinciples:Reliability.
WithintheVMwareTrust&Assuranceframework,thecommitmenttoreliabilityincludes:ProductperformanceandscalabilityinordertoensurethatVMwareproductscanmeetenterprisedemands.
ApervasivecultureofevangelismandeducationtokeepVMwareemployeesandcustomerseducatedandengagedonrapidly-changingcybersecurityrisks.
WhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance92015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
ResearchdedicatedtoenhancingVMwareproductperformanceandreliabilitywhileworkingwithcustomersonassociatedprojectplanning,testing,deployment,andoptimization.
QualitymetricsandcontinuousimprovementassociatedwithVMwareproducts,people,andpartners.
Integrity.
ThisprinciplealignswithVMware'ssoftwaredevelopmentandcomprises:TheVMwaresoftwaredevelopmentlifecycle.
VMwarehadbuiltadevelopmentprocessthatincludesformalrepeatableprocessesforsoftwaredesign,testing,documentation,release,andongoingsupport.
Complianceandrisk.
Alongwithitspartners,VMwaredevelopedthecompliancereferencearchitectureframework(RAF)thatalignsitstechnologywithregulatorycompliancerequirementsacrossindustries.
Softwaresupplychainmanagement.
VMwareisaddressingitsowncybersupplychainpracticesinanumberofareasincludingIPprotection,sourcecodesharing,riskmanagementassessment,andproactivesoftwaresecurityprogramswithstrategicpartnersandsuppliers.
Privacy.
Toprotectcustomerprivacy,VMwaredefinesitsprivacypolicytocustomers,specifyingwhatdataitcollectsandhowitisused.
VMwarefollowsa"privacybydesign"frameworktoprovidetransparencyonprivacyasitrelatestoproducts,services,andsupport.
Security.
VMwarehasintroducedstrongcybersecuritythroughoutitsorganization.
Examplesofthisinclude:Productsecurity.
VMwarehascreatedaproductsecurityteamresponsibleforoversightofallproductsecurity.
Thisgroupsupervisessecuritydevelopmentprocessesandmetricswitheachproductteamandisresponsiblefordemonstratingcontinuousimprovement.
Securitydevelopmentlifecycle.
Thisextendsbeyondthesecuresoftwaredevelopmentlifecycleandincludessecuritytraining,planning,serviceability,aswellasresponseplanning,productsecurityrequirementsassessment,andoverallsecuritymonitoring.
Thesecurityresponsecenter.
VMwareemploysateamofsecurityresearchers,softwaredevelopers,andsupportstafftofindvulnerabilities,developfixes,andworkwithcustomersandpartnersfortimelydistributionanddeploymentofsecurityfixes.
ITsecurity.
Likealllargeenterprises,VMware'scorporateinfrastructureisundercontinualattacksfrommaliciousindividualsandentities.
Toaddressthisrisk,VMwaremaintainscybersecuritybestpracticesoninternalnetworksandsystems.
Commitment.
Tomakecybersupplychainsecurityassurancepervasiveineverythingitdoes,VMwarehasmadecybersecuritypartofitscorporateculture.
Ofcourse,thisrequiresatruecybersecuritycommitmentincluding:Continuingproductdevelopment.
VMwarehasestablishedacontinuingproductdevelopmentorganization,whichactsasasinglepoint-of-contactforaddressing,escalating,andresolvingproductandcustomercybersecurityissues.
Ecosystemservices.
VMwareunderstandsthatitscybersecuritysupplychainincludesanetworkofhundredsofotherITvendorandservicespartners.
VMwareprovidestechnicalsupport,testing,cooperativesupportservices,andrules-of-engagementtoensurestrongcybersecurityinthefield.
Customeradvocacy.
VMwarerecognizesthatcybersecurityprofessionalsareacommunityoflike-mindedindividualswithafewcommongoals—mitigatingITriskandprotectingcriticalITassetsanddata.
Tosucceed,VMwaredependsuponapartnershipofequalswithVMwareWhitePaper:VMwareandtheNeedforCyberSupplyChainSecurityAssurance102015byTheEnterpriseStrategyGroup,Inc.
AllRightsReserved.
participatinginthecybersecuritycommunityratherthandictatingitsownITvendoragenda.
VMwareseekstofacilitatethisrelationshipwithsecurityresearch,workshops,benchmarks,securityeducation,andsocialmediacampaigns.
WithitsTrust&Assuranceinitiative,VMwareistakinga360degreeperspectiveoncybersecuritythatencompassesitsproducts,partners,customers,employees,andthecybersecuritycommunityatlarge.
Inthisway,VMwarehasnotonlyrespondedtoitsenterprisecustomers'needforgreatertransparencyrelatedtocybersupplychainsecurity,butisalsosettinganexamplethatshouldbeemulatedbyotherITvendors.
TheBiggerTruthCISOsfaceadauntingareaofchallenges.
Cyberthreatsgrowmorevoluminous,sophisticated,andtargetedwhileITinfrastructuregetsmorecomplexasnetworkperimetersdisappear.
Yes,thesechangesdemandanincreasingcommitmenttocybersecurityoversight,riskmanagement,andtightsecuritycontrolsbuttheseeffortssimplycan'tbelimitedtocorporateLANs,WANs,anddatacenters.
Rather,CISOsmustunderstandtherisksassociatedwiththeircybersupplychains,andestablishbestpracticesforcybersupplychainsecurity.
ESGresearchindicatesthatthistransitionisalreadyinprogress,causingmanyorganizationstoauditthesecurityoftheirITproductandservicesvendors.
Leadingedgeenterprisesarealsomakingpurchasingdecisionsbasedupontheirvendors'cybersupplychainsecurityassuranceprograms.
Movingforward,moreorganizationswilllikelyfollowsuit.
UnlikemanyotherenterpriseITvendors,VMwareiswellpreparedforthisincreasinglevelofcybersecurityoversight.
Infact,theVMwareTrust&Assuranceinitiativeisdesignedtomeetandexceedthegrowingneedforgreatertransparencyrelatedtoenterprisecybersecurity.
Assuch,VMwareissettinganexamplefortheITindustryatlarge.
CISOswouldbewellservedtodemandsimilarcybersupplychainsecurityassurancefromALLoftheirstrategicITvendors.
20AsylumStreet|Milford,MA01757|Tel:508.
482.
0188Fax:508.
482.
0218|www.
esg-global.
com
- attentionstealthy相关文档
- HowtheF-35AandtheF-15EXcompare
- denesstealthy
- ensurestealthy
- approachstealthy
- CYBERstealthy
- victoriousstealthy
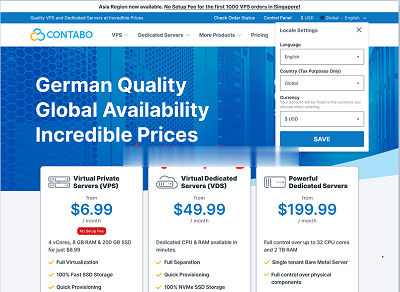
#消息# contabo:德国老牌机房新增美国“纽约、西雅图”数据中心,免设置费
运作了18年的德国老牌机房contabo在继去年4月开办了第一个美国数据中心(中部城市:圣路易斯)后立马在本月全新上马两个数据中心:纽约、西雅图。当前,为庆祝美国独立日,美国三个数据中心的VPS全部免除设置费,VPS本身的配置很高,价格适中,有较高的性价比!官方网站:https://contabo.com/en/SSD VPSKVM虚拟,纯SSD阵列,不限制流量,自带一个IPv4内存CPUSSD带...
buyvm美国大硬盘VPS,1Gbps带宽不限流量
buyvm正式对外开卖第四个数据中心“迈阿密”的块存储服务,和前面拉斯维加斯、纽约、卢森堡一样,依旧是每256G硬盘仅需1.25美元/月,最大支持10T硬盘。配合buyvm自己的VPS,1Gbps带宽、不限流量,在vps上挂载块存储之后就可以用来做数据备份、文件下载、刷BT等一系列工作。官方网站:https://buyvm.net支持信用卡、PayPal、支付宝付款,支付宝付款用的是加元汇率,貌似...

白丝云-美国圣何塞4837/德国4837大带宽/美西9929,26元/月起
官方网站:点击访问白丝云官网活动方案:一、KVM虚拟化套餐A1核心 512MB内存 10G SSD硬盘 800G流量 2560Mbps带宽159.99一年 26一月套餐B1核心 512MB内存 10G SSD硬盘 2000G流量 2560Mbps带宽299.99一年 52一月套餐...

stealthy为你推荐
-
注册域名个人如何注册域名免费虚拟主机申请在哪个网站申请的免费虚拟主机可以绑定顶级域名?求高手指点!免费国内空间现在国内比较好的免费网站空间有那个啊?免费网站域名申请那里 可以申请免费的 网站域名啊??香港虚拟空间请大哥帮个忙,介绍可靠的香港虚拟主机?网站空间租用公司网站租用什么样的网站空间合适虚拟主机控制面板我想问下虚拟主机的控制面板有哪些还不错的品牌呢?价格不能太高最好是性价比比较高一点就行了虚拟主机系统虚拟主机上的系统与电脑操作系统差别?安徽虚拟主机安徽众仁联合科技有限公司是做什么的啊??域名邮箱域名是干什么的?域名邮箱和自己注册的邮箱有什么不一样吗?