权限动网先锋论坛-『 web开发讨论区 』-针对sql injection的sql server安全设置初级篇(Mobile pioneer Forum - Web Development Forum - for SQL Injection´s SQL Server Security Settings)
动网先锋论坛- 『 web开发讨论区』 -针对sql injection的sqlserver安全设置初级篇Mobile pioneer Forum-Web DevelopmentForum - for SQL Injection' s SQL Server Security SettingsMobile pioneer Forum - "WEB Development Forum" - for SQLINJECTION' s SQL SERVER security settings
Collect this page
Contact us
Forum Help
Qmtxf re login, stealth user control panel, SMS search style,forum status, forum exhibition, props center exit
Website development, database development exchange, variousWEB development technology exchange, base camp, my inbox (0)Mobile network pioneer Forum - computer technology - "WEBDevelopment Forum" - for SQL INJECTION SQL SERVER securitysettings junior article
You are the 1369th person reading this post AP
* posting theme: initial article on security settings for SQLINJECTION' s SQL SERVER
Jadesun
Title: people don't want to say
Class: VIP
Article: 1338
Points: 2527
Registration: 2000-7-31
The landlord
For SQL INJECTION SQL SERVER security settings junior articleThe day before the SQL INJECTION attack testing intensified,many large websites and forums have been injected. These sitesgenerally use more than SQL
SERVER database, and because of this, many people begin to doubtthe security of SQL SERVER. Actually, SQL SERVER
2000 has passed the U.S. government' s C2 level securitycertification - this is the industry can have the highestcertification level, so the use of SQL
SERVER is pretty safe. Of course, there is still a gap betweenORCAL and DB2, but SQL
The ease of use and universality of SERVER can still be a reasonfor us to continue using it. How can you make the SQL SERVERsettings reassuring?
The first step must be to hit SQL
SERVER' s latest security patch, and now the patch is out of SP3.Download address:http://www.microsoft.com/sql/downloads/2000/sp3.asp. If thisstep is not done well, then we do not have the necessary tocont inue.
The second step is to modify the default 1433 port andhide theSQL SERVER. This prevents attempts to enumerate existing SQLServer on the network
The broadcast sent by the client responds. In addition, youneedto screen the 1433 port from the TCP/IP filter and hide yourSQL as much as possible
SERVER database. This way, but let the attack create SQLSERVER accounts can not immediately use the query analyzerremote login for the next attack. From the ASP, PHP and otherpages to construct malicious statements, there is also need tocheck the return value of the problem, than the direct queryanalyzer to benefit from the fall. So the first thing we needto do even let others into, nor allow an attacker to do nextsmoothly. Modification method: Enterprise Manager
Taking your database group-- >attributes-->-->-->TCP/IP- > conventional network configuration attributes
Here, modify your default port and hide the SQL SERVER.
The third step is an important step, and SQL INJECTION tendsto be in WEB
Generated in CODE. As a system administrator or databaseadministrator, you can't always look at each piece of code. Evenif we often look at the code, we can not guarantee our negligenceon the above. What can we do?We' ll start with the database roleto get the database users' rights to the lowest point. SQLSERVER' s default permissions are really a headache, very highpermissions, no permissions, and nothing to do, SYSADMIN anddb_owner is really a love and hate. An attacker, however,confirmed that the site had SQL
INJECTION vulnerability, there must be a step in the processof testing the site' s SQL SERVER users have much authority.Usually with the help of SELECT
IS_SRVROLEMEMBER (' sysadmin' ) , or SELECT IS_MEMBER
('db_owner' ) , or user
= 0 (compare characters with numbers, SQL
The SERVER will prompt the error message, which can be used totest some sensitive information, and so on. And, I dare not saymore. One is afraid of being wrong, and the other is afraid ofthe people in the alliance. At present, if the database userof the web site uses SA privileges, plus the absolute path ofthe WEB, the OVER of your website is declared. Db_ownerpermissions are the same. If the absolute path is confirmed,there is a 50% chance to give WEB in your machine
A Trojan horse, such as Haiyang. So here we've got a point. Wehave to create our own privileges so that the attacker can'tfind a place to go. Quote a SQL here
Examples of SERVER online help:
Method for creating SQL Server database roles (EnterpriseManager)
Create SQL Server database roles
1. expand the server group, and then expand the server.
2. expand the database folder, and then expand the databasewhere you want to create the roles.
3. right click on roles, and then click new database roles.
4. enter the name of the new role in the name box.
5. click Add to add members to the standard roles list, and thenclick one or more users you want to add. (optional)
Only users in the selected database can be added to the role.Object permission
A class of permissions that is called object permissions whenprocessing data or executing procedures:
? SELECT, INSERT, UPDATE, and DELETE statement permiss ions,which can be applied to the entire table or view.
SELECT and UPDATE statement permissions, which can beselectively applied to a single column in a table or view.SELECT permissions, which can be applied to user-definedfunctions.
INSERT and DELETE statement permissions that affect entire rows,sotheycanonlybeappliedtotables orviews, not to individualcolumns.
EXECUTE statement permissions, which can affect storedprocedures and functions.
Statement permission
The activities involved in creating items in a database ordatabase, such as tables or stored procedures, require anotherclass of permissions called statement rights. For example, ifa user must be able to create a table in the database, the usershould be granted it
CREATE TABLE statement permissions. Statement permissions(such as CREATE, DATABASE) apply to the statement itself,rather than to specific objects defined in the database.Statement authority:
? BACKUP DATABASE
? BACKUP LOG
? CREATE DATABASE
? CREATE DEFAULT
? CREATE FUNCTION
? CREATE PROCEDURE
·创建规则
·创建表
·创建视图
暗示性权限
暗示性权限控制那些只能由预定义系统角色的成员或数据库对象所有者执行的活动。例如 固定服务器角色成员自动继承在SQLsysadmin
服务器安装中进行操作或查看的全部权限。
数据库对象所有者还有暗示性权限可以对所拥有的对象执行一切活动。例如拥有表的用户可以查看、添加或删除数据更改表定义或控制允许其他用户对表进行操作的权限。d b_o wn e r在数据库中有全部权限。
db_accessadmin可以添加或删除用户ID。db_securityadmin可以管理全部权限、对象所有权、角色和角色成员资格。db_ddladmin可以发出所有DDL但不能发出格兰特、撤销或否认语句。db_backupoperator可以发出DBCC、检查站和备份语句。db_datareader可以选择数据库内任何用户表中的所有数据。db_datawri ter可以更改数据库内任何用户表中的所有数据。db_denydatareader不能选择数据库内任何用户表中的任何数据。db_denydatawriter不能更改数据库内任何用户表中的任何数据。在这儿把新建的数据库角色的权限配置好比如需要使用哪个表、视图、存储过程等。然后把db_owner和db_securityadmin、db_backupoperator取消不给攻击者备份
和创建数据库
表的机会一但攻击者具有这两个权限那么你的网站就还处在十分危险的状态。还有注意一下在创建数据库账号时千万不能对服务器角色进行选择。
第四步是修改内置存储过程SQL SQL Server。
服务器估计是为了安装或者其它方面它内置了一批危险的存储过程。能读到注册表信息能写入注册表信息能读磁盘共享信息等等. . . . . .各位看到这儿心里可能会在想我的网站中有其它的代码又不像查询分析器那样能查接将结果输出。给你这个权限又不能怎么样还是看不到信息。如果各位这样想就大错特错了提示一下如果攻击者有创建。
表的权限那么创建一个临时表然后将信息插入到表中然选择出来接着跟数字进行比较让SQL
服务器报错那么结果就全出来了. . . . . .所以我们要报着宁错杀不放过的态度进行修补。
先来列出危险的内置存储过程xp_cmdshellxp_regaddmultistringxp_regdeletekeyxp_regdeletevaluexp_regenumkeysxp_regenumvaluesxp_regreadxp_regremovemult istring
- 权限动网先锋论坛-『 web开发讨论区 』-针对sql injection的sql server安全设置初级篇(Mobile pioneer Forum - Web Development Forum - for SQL Injection´s SQL Server Security Settings)相关文档
- 论坛南方动漫网论坛管理办法
- 设置动网论坛基本设置教程
- 版主南方网动漫论坛管理制度
- 键入抓取动网论坛 Email 地址的一段代码源码精华教程
- 信息技术浅谈“动网论坛”在高中信息技术课堂中的应用
- 您的动网论坛前台使用手册_ASP_82.
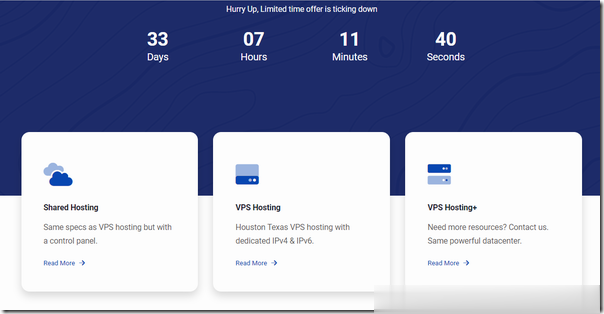
Boomer.Host(年付3.5美)休斯敦便宜VPS
Boomer.Host是一家比较新的国外主机商,虽然LEB自述 we’re now more than 2 year old,商家提供虚拟主机和VPS,其中VPS主机基于OpenVZ架构,数据中心为美国得克萨斯州休斯敦。目前,商家在LET发了两款特别促销套餐,年付最低3.5美元起,特别提醒:低价低配,且必须年付,请务必自行斟酌确定需求再入手。下面列出几款促销套餐的配置信息。CPU:1core内存:...
易探云美国云服务器评测,主机低至33元/月,336元/年
美国服务器哪家平台好?美国服务器无需备案,即开即用,上线快。美国服务器多数带防御,且有时候项目运营的时候,防御能力是用户考虑的重点,特别是网站容易受到攻击的行业。现在有那么多美国一年服务器,哪家的美国云服务器好呢?美国服务器用哪家好?这里推荐易探云,有美国BGP、美国CN2、美国高防、美国GIA等云服务器,线路优化的不错。易探云刚好就是做香港及美国云服务器的主要商家之一,我们来看一下易探云美国云服...
舍利云30元/月起;美国CERA云服务器,原生ip,低至28元/月起
目前舍利云服务器的主要特色是适合seo和建站,性价比方面非常不错,舍利云的产品以BGP线路速度优质稳定而著称,对于产品的线路和带宽有着极其严格的讲究,这主要表现在其对母鸡的超售有严格的管控,与此同时舍利云也尽心尽力为用户提供完美服务。目前,香港cn2云服务器,5M/10M带宽,价格低至30元/月,可试用1天;;美国cera云服务器,原生ip,低至28元/月起。一、香港CN2云服务器香港CN2精品线...

-
视频制作软件哪个好我想学做视频跟作图,推荐下什么软件好涡轮增压和自然吸气哪个好涡轮增压和自然吸气哪个好录音软件哪个好手机录音软件哪个好用51空间登录手机怎么登陆51空间啊网通dns服务器地址湖北省鄂州市葛店镇DNS服务器IP地址是多少网通dns服务器地址网通的DNS是多少?广东联通营业厅广东省广州市联通营业厅在哪里?广东联通官方旗舰店广东联通沃商城什么快递最便宜最便宜的是什么快递便宜摩托车我想问下现在到底买什么摩托车省油、便宜、实用??