2011ArubaNetworksInc.
comodo 时间:2021-01-12 阅读:()
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
SupportAdvisory:ArubaOSDefaultCertificateExpirationIssuedFebruary14,2011UpdatedApril8,2011Thisdocument,includingtheinformationitcontainsandtheprogramsmadeavailablethroughthelinksthatitincludes,isprovidedtoyouonan"asis"basis.
ARUBAANDITSSUPPLIERSDONOTWARRANTTHATSUCHINFORMATIONORTHEFUNCTIONSCONTAINEDINSUCHPROGRAMSWILLMEETYOURREQUIREMENTSORTHATTHEOPERATIONOFTHEPROGRAMSWILLBEUNINTERRUPTEDORERROR-FREE.
THEINFORMATIONANDPROGRAMSAREPROVIDEDTOYOUWITHNOWARRANTYOFANYKIND,EXPRESSORIMPLIED,INCLUDINGWITHOUTLIMITATION,ANYIMPLIEDWARRANTIESOFMERCHANTABILITY,FITNESSFORAPARTICULARPURPOSEANDNONINFRINGEMENT.
INNOEVENTWILLARUBA,ITSSUPPLIERS,ORANYONEELSEWHOHASBEENINVOLVEDINTHECREATION,PRODUCTION,ORDELIVERYOFTHEINFORMATIONORPROGRAMSBELIABLEFORANYDIRECT,INDIRECT,INCIDENTALORCONSEQUENTIALDAMAGES,INCLUDINGWITHOUTLIMITATION,LOSTPROFITSORLOSTDATA,THATMAYARISEOUTOFYOURUSEOFORFAILURETOUSETHEINFORMATIONORPROGRAMS,EVENIFARUBAORSUCHOTHERENTITIESHAVEBEENADVISEDOFTHEPOSSIBILITYOFSUCHDAMAGES.
THEFOREGOINGSHALLNOTBEDEEMEDTOPRECLUDEANYLIABILITYWHICH,UNDERAPPLICABLEPRODUCTSLIABILITYLAW,CANNOTBEPRECLUDEDBYCONTRACT.
ThisdocumentisbeingprovidedtoyoupursuanttotheprovisionsofyourapplicablesoftwarelicenseagreementwithAruba,andtheinformationandprogramsmaybeusedonlypursuanttothetermsandconditionsofsuchagreement.
ThisArubaSecurityAdvisorconstitutesArubaProprietaryInformationandshouldnotbedisseminated,forwardedordisclosed.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
SummaryOnJune29,2011thedefaultSSL/TLScertificate"securelogin.
arubanetworks.
com"thatisinstalledonallArubacontrollerswillexpire.
Whilethisdefaultcertificatewasneverintendedforproductionuse,Arubaisawarethatanumberofcustomersareusingthiscertificateinproductionnetworks.
Thesecustomerswillneedtoreplacethecertificate.
Affectedcustomershavetwooptions:1.
Replacethedefaultcertificatewithacertificateissuedbyaninternalcertificateauthorityorapubliccertificateauthority.
Thisoptionisrecommendedandprovidesthegreatestsecurity.
2.
UpgradetheArubaOSimagetoaversionnumberequaltoorgreaterthan3.
3.
3.
10,3.
4.
4.
2,5.
0.
3.
2,6.
0.
1.
1,or6.
1.
0.
0.
Thesesoftwareimagescontainanewdefaultcertificatethatwillreplacetheexpiringcertificate.
Thisoptiondoesnotprovidegoodsecurity,sinceallArubacustomershaveaccesstothesamecertificateandimpersonationattacksarepossible.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
BackgroundTheArubaOSoperatingsystemloadedonallArubaMobilityControllerscontainsapre-loadeddigitalcertificatewiththename"securelogin.
arubanetworks.
com".
Thiscertificatewasissuedbyapubliccertificateauthority(CA)thatistrustedbymostbrowsersandoperatingsystems.
Bydefaultthecertificateisusedforthecontroller'smanagementinterface(WebUI),captiveportal,andEAPtermination.
Thiscertificateisintendedforquicklysettinguplabnetworks,demonstrations,andproof-of-conceptdeployments.
Asstatedintheuserguide,thedefaultcertificateisnotintendedforproductiondeployment,sinceeveryArubacontrollercontainsthesamecertificateandthisenablesimpersonationattacks.
Thefollowingtextsummarizestherisks:CaptivePortal:Anattackerimpersonatingacaptiveportalloginscreenmaybeabletoobtaintheusernameandpasswordofauthorizedusersonthesystem.
Ifcaptiveportalisusedonlyforguestaccess,thismaynotbedeemedaserioussecurityrisk.
Ifcaptiveportalisusedtoauthenticateinternalusers,thisattackcouldcausemoreseriousdamage.
AdministrativeWebUI:Tocarryoutanimpersonationattackagainstthecontroller'sadministrativeWebUI,theattackerwouldneedtointercepttrafficbetweenasystemadministrator'scomputerandthecontroller.
Thiswouldtypicallyrequireaninsiderattack,assumingadministrativeaccessisblockedfrompublicnetworks.
Theriskisseriousinthiscase,sinceasuccessfulattackwouldallowanunauthorizedpersontoobtainadministrativecredentialsfortheArubacontroller.
TheWebUIcertificateshouldalwaysbereplaced,evenifwithaself-signedcertificatethateachsystemadministratormustexplicitlytrust.
802.
1XEAPTermination:Thisistheriskiestuseofthedefaultcertificate,becauseanimpersonationattackmaybecarriedoutoverawirelessnetwork,andasuccessfulattackmayrevealusernamesandpasswordhashes(providingmaterialforanofflinepasswordcrackingattempt)orallowtheattackertogetauserconnectedtoahostilenetworkwhiletheuserthinksheorsheisconnectedtoatrustednetwork.
Thedefaultcertificateshouldneverbeusedfor802.
1X.
Arubaisawarethatsomecustomersdousethedefaultcertificateinproduction,typicallyforsecuringthecaptiveportalloginscreeninguestnetworkswhereensuringtheidentityofthecontrollerisnotanimportantsecurityconsideration.
Thedefaultcertificatewasvalidforfiveyears,andwillexpireonJune29,2011.
Ifthenetworkadministratordoesnotreplacethecertificate,thefollowingwilloccur:1.
UsersconnectingtocaptiveportalorWebUIpageswillreceiveabrowserwarningshowingthattheservercertificatehasexpired.
Usersmaybypassthewarning(withvaryingdegreesofdifficultydependingonthebrowser)andcontinueontousethesystemnormally.
2.
IfEAPterminationhasbeenenabledfor802.
1X,andthedefaultcertificateisbeingusedastheservercertificate,manyclientoperatingsystemswillrefusetocontinuetheauthenticationprocess.
Thiswillresultinanapparentnetworkoutagefortheseusers.
Clientoperatingsystemsmayormaynotdisplayawarningmessagetotheuser.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Thisdocumentoutlinestheproceduresneededtoupdatethedefaultcertificate,inorderofpreference:Option1:InstallauniqueservercertificateOption2:UpgradeArubaOS2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Option1:InstallaUniqueServerCertificateThisistherecommendedapproachsinceitprovidesthebestsecurity.
Inthisapproach,thedefaultcertificatewillremainonthecontroller,butyouwillloadoneormorenewcertificatesandthenconfigurethesystemtousethenewcertificate(s).
Ifyourorganizationoperatesaninternalcertificateauthority(CA)andallclientsthatwillusethesystemalreadytrusttheinternalCA,youmayusetheinternalCAtoissueanewcertificatetothecontroller.
Thisoptionisrecommendedfor802.
1XEAPterminationandWebUIadministrativeaccesstothecontroller.
Itcanalsobeusedforcaptiveportalaslongasthegeneralpublicwillnotbeaccessingthesystem(sincetheinternalCAwillnotbetrusted,thegeneralpublicwouldreceivebrowserwarnings.
)Ifpresentingacaptiveportalpagetocomputersownedbythegeneralpublic,acertificateissuedbyapublicCA(VeriSign,GeoTrust,Comodo,etc.
)shouldbeusedsothatbrowserwarningsarenotgenerated.
YoumaychoosetouseacertificateissuedbyapublicCAforWebUIadministrativeaccesstothecontrollerandfor802.
1XEAPterminationaswell,butuseofapublicCAinsteadofaninternalCAprovidesnobenefitinthosecases.
Beforerequestingacertificate,decidewhetheryouneeda1024-bitkey,2048-bitkey,or4096-bitkey.
NotethatmanypublicCAsnolongerissuecertificateswith1024-bitkeys.
IfyouarerunningArubaOS6.
1orgreater,youmayuseacertificatewitha2048-bitkeyforanypurpose.
Youmayuseacertificatewitha4096-bitkeyonlyforcaptiveportalandWebUI.
ForWebUIorcaptiveportal,performanceisthegreatestwithsmallerkeysizes,butsecurityisslightlyreduced.
Tomaximizecompatibility,alwaysuseRSAunlessyouhaveaspecificreasontouseECC.
Ifyouarerunninganyreleasepriorto6.
1,youmayuseacertificatewitha2048-bitor4096-bitkeyonlyforcaptiveportalandWebUI.
802.
1XEAPterminationsupportsonly1024-bitkeys.
ForWebUIorcaptiveportal,performanceisthegreatestwithsmallerkeysizes,butsecurityisslightlyreduced.
Thefollowinginstructionsshouldbefollowedtoobtainandinstallaservercertificate.
1.
GenerateaCertificateSigningRequest(CSR)fromthecontrollerbynavigatingtoConfigurationManagementCertificatesCSR.
Filloutthenecessaryfields.
Afterclicking"GenerateNew",thecontrollerwillgenerateaprivatekey,whichremainslockedinsidethecontroller,andabase64-encodedCSR.
TheCSRcontainsallthedetailsneededforyourCAtoissuethecertificate.
TheCommonName(CN)fieldshouldcontainthefullURLthatwebbrowserswillnavigatetoinordertoreachthecontroller'sembeddedwebserver.
TakecaretofillouttheCommonNamefieldcorrectlyaccordingtothepurposeofthecertificate:a.
Forcaptiveportal,thesystemwillautomaticallyissueHTTPredirectsandspoofDNSresponsestothecaptiveportalclientsothatthebrowserappearstobeconnectingtothecorrectDNSnamethatmatchesthecertificatecommonname.
Thisistoensurethatbrowserwarningsarenotgenerated.
Ifthecertificateisonlybeingusedforcaptiveportal,thenameintheCNfieldisunimportant–butmakesureitfallswithin2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
yourdomainnamesothatapublicCAwillcorrectlyauthorizeownershipofthecertificate.
b.
ForWebUI,theCNfieldshouldmatchtheaddressyouusetomanagethecontroller.
ThiscanbeanIPaddressoraFullyQualifiedDomainName(FQDN).
c.
For802.
1XEAPTermination,theCNfieldisnotmatchedbytheclientagainstanyotherparameter.
ItissuggestedthatyouchooseaFQDNthatisownedbyyourorganization.
2.
Clickon"ViewCurrent".
Copythebase64textshown,andpastethisintothecertificaterequestwindowprovidedbyyourcertificateauthority.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
3.
Onceyouhaveobtainedthecertificate,navigatetoConfigurationManagementCertificatesUploadanduploadthecertificatetothecontroller.
ThecertificatewillmostlikelybeprovidedtoyouinPEMorDERformat–ifyouarenotsurewhichformatitisin,tryPEMfirstandifanerrormessageresults,tryDER.
APEMformatcertificatewillbebase64-encodedandwillbeginwiththetext"-----BEGINCERTIFICATE-----".
4.
Ifyouwanttousethenewcertificateforcaptiveportal,navigatetoConfigurationManagementGeneralandchangetheCaptivePortalServerCertificate.
IfyouwanttousethenewcertificateforWebUI,configurationisfoundonthesamescreenunder"WebUIManagementAuthenticationMethod".
5.
IfyouwanttousethenewcertificateforEAPTermination,navigatetoConfigurationSecurityAuthenticationL2Authentication802.
1XAuthentication2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
ProfileAdvancedandchangetheservercertificateforallactive802.
1XauthenticationprofilesthatuseEAPTermination.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Option2:UpgradeArubaOSArubahasobtainedanewcertificatelabeled"securelogin.
arubanetworks.
com"fromapublicCAthatreplacestheolddefaultcertificate.
ThenewcertificatehasanexpirationdateofNovember21,2013.
ThiscertificateisincludedaspartofthefollowingArubaOSsoftwarereleases:6.
1beginningwithrelease6.
1.
0.
06.
0beginningwithrelease6.
0.
1.
15.
0beginningwithrelease5.
0.
3.
23.
4beginningwithrelease3.
4.
4.
23.
3beginningwithrelease3.
3.
3.
10AllotherArubaOSreleasesdatedlaterthanJune1,2011Afterupgradingtooneoftheabovelistedreleases,nofurtheractionisrequiredtoenablethecertificate.
Ifthesystemwaspreviouslyconfiguredtousethedefaultcertificate,itwillautomaticallyusethenewlyupdatedcertificate.
Whilethisoptionprovidesthesamelevelofsecuritygivenbythepreviousdefaultcertificate,itisnotagoodoptionwhereanysecurityrequirementsexist.
SSL/TLSsecurityisprovidedbythecertificate'sprivatekeybeingkeptsecret.
Ifthecertificate'sprivatekeybecomesknown,itispossibleforanattackertoimpersonateanyserverorwebsiteusingthatcertificatewithouttheknowledgeoftheenduser.
BecausethesamecertificateandprivatekeyareinstalledonallArubacontrollers,anattackerneedonlyreverseengineerasinglesoftwareimagetoobtaintheprivatekey.
Whilethisprocessisnon-trivial,itiscertainlynotbeyondthemeansofaskilledanddeterminedattacker.
ItisalsopossibleforanattackertosimplypurchaseanduseanArubacontrollerforthepurposeofconductinganimpersonationattack.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
FAQQ:WhathappensifIhaveconfigured802.
1Xdevicesinmynetworktoonlytrustthe"securelogin.
arubanetworks.
com"certificate,ortoonlytrusttheEquifaxSecureCertificateAuthorityA:Thesedeviceswillneedtobereconfiguredafterinstallationofanewcertificate.
IftheseareWindowsdevices,UNCHECK"Connecttotheseservers"andUNCHECK"EquifaxSecureCertificateAuthority"intheTrustedRootCertificationAuthorities.
Afterconnectingtothecontrollerwiththenewcertificateinstalled,Windowswillupdatethesesettingsbypromptingtheuser.
Q:IsthecertificatebuiltintotheTPMchipaffectedbythisadvisoryA:No.
AllArubacontrollersthatcontainaTrustedPlatformModule(TPM),includingtheM3,3000series,and600series,containacertificateuniquetothecontrollerthathasbeenprogrammedatthefactory.
Thiscertificateisnotexpiringandisnotaffectedbythisadvisory.
ThiscertificateisusedforMaster-Localauthentication,ControlPlaneSecurity(CPsec),andRAPauthentication.
ItisnotsuitableforuseasanSSLcertificatesinceitwasissuedbyAruba'smanufacturingCA,whichisnottrustedbybrowsers.
Q:WhatcertificateauthoritywasusedtogeneratethenewcertificateWhatchainsdoesitcontain2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
A:ThenewcertificatewasissuedbyPositiveSSL,andultimatelychainsbackuptoUSERTrust,whichisissuedbyAddTrustExternalCARoot.
DevicesconnectingtothenetworkmusthaveUSERTrustinstalledasatrustedrootCAinorderfortheArubafactorydefaultcertificatetobetrusted.
UnderaWindowssystem,thecertificatechainappearsas
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
SupportAdvisory:ArubaOSDefaultCertificateExpirationIssuedFebruary14,2011UpdatedApril8,2011Thisdocument,includingtheinformationitcontainsandtheprogramsmadeavailablethroughthelinksthatitincludes,isprovidedtoyouonan"asis"basis.
ARUBAANDITSSUPPLIERSDONOTWARRANTTHATSUCHINFORMATIONORTHEFUNCTIONSCONTAINEDINSUCHPROGRAMSWILLMEETYOURREQUIREMENTSORTHATTHEOPERATIONOFTHEPROGRAMSWILLBEUNINTERRUPTEDORERROR-FREE.
THEINFORMATIONANDPROGRAMSAREPROVIDEDTOYOUWITHNOWARRANTYOFANYKIND,EXPRESSORIMPLIED,INCLUDINGWITHOUTLIMITATION,ANYIMPLIEDWARRANTIESOFMERCHANTABILITY,FITNESSFORAPARTICULARPURPOSEANDNONINFRINGEMENT.
INNOEVENTWILLARUBA,ITSSUPPLIERS,ORANYONEELSEWHOHASBEENINVOLVEDINTHECREATION,PRODUCTION,ORDELIVERYOFTHEINFORMATIONORPROGRAMSBELIABLEFORANYDIRECT,INDIRECT,INCIDENTALORCONSEQUENTIALDAMAGES,INCLUDINGWITHOUTLIMITATION,LOSTPROFITSORLOSTDATA,THATMAYARISEOUTOFYOURUSEOFORFAILURETOUSETHEINFORMATIONORPROGRAMS,EVENIFARUBAORSUCHOTHERENTITIESHAVEBEENADVISEDOFTHEPOSSIBILITYOFSUCHDAMAGES.
THEFOREGOINGSHALLNOTBEDEEMEDTOPRECLUDEANYLIABILITYWHICH,UNDERAPPLICABLEPRODUCTSLIABILITYLAW,CANNOTBEPRECLUDEDBYCONTRACT.
ThisdocumentisbeingprovidedtoyoupursuanttotheprovisionsofyourapplicablesoftwarelicenseagreementwithAruba,andtheinformationandprogramsmaybeusedonlypursuanttothetermsandconditionsofsuchagreement.
ThisArubaSecurityAdvisorconstitutesArubaProprietaryInformationandshouldnotbedisseminated,forwardedordisclosed.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
SummaryOnJune29,2011thedefaultSSL/TLScertificate"securelogin.
arubanetworks.
com"thatisinstalledonallArubacontrollerswillexpire.
Whilethisdefaultcertificatewasneverintendedforproductionuse,Arubaisawarethatanumberofcustomersareusingthiscertificateinproductionnetworks.
Thesecustomerswillneedtoreplacethecertificate.
Affectedcustomershavetwooptions:1.
Replacethedefaultcertificatewithacertificateissuedbyaninternalcertificateauthorityorapubliccertificateauthority.
Thisoptionisrecommendedandprovidesthegreatestsecurity.
2.
UpgradetheArubaOSimagetoaversionnumberequaltoorgreaterthan3.
3.
3.
10,3.
4.
4.
2,5.
0.
3.
2,6.
0.
1.
1,or6.
1.
0.
0.
Thesesoftwareimagescontainanewdefaultcertificatethatwillreplacetheexpiringcertificate.
Thisoptiondoesnotprovidegoodsecurity,sinceallArubacustomershaveaccesstothesamecertificateandimpersonationattacksarepossible.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
BackgroundTheArubaOSoperatingsystemloadedonallArubaMobilityControllerscontainsapre-loadeddigitalcertificatewiththename"securelogin.
arubanetworks.
com".
Thiscertificatewasissuedbyapubliccertificateauthority(CA)thatistrustedbymostbrowsersandoperatingsystems.
Bydefaultthecertificateisusedforthecontroller'smanagementinterface(WebUI),captiveportal,andEAPtermination.
Thiscertificateisintendedforquicklysettinguplabnetworks,demonstrations,andproof-of-conceptdeployments.
Asstatedintheuserguide,thedefaultcertificateisnotintendedforproductiondeployment,sinceeveryArubacontrollercontainsthesamecertificateandthisenablesimpersonationattacks.
Thefollowingtextsummarizestherisks:CaptivePortal:Anattackerimpersonatingacaptiveportalloginscreenmaybeabletoobtaintheusernameandpasswordofauthorizedusersonthesystem.
Ifcaptiveportalisusedonlyforguestaccess,thismaynotbedeemedaserioussecurityrisk.
Ifcaptiveportalisusedtoauthenticateinternalusers,thisattackcouldcausemoreseriousdamage.
AdministrativeWebUI:Tocarryoutanimpersonationattackagainstthecontroller'sadministrativeWebUI,theattackerwouldneedtointercepttrafficbetweenasystemadministrator'scomputerandthecontroller.
Thiswouldtypicallyrequireaninsiderattack,assumingadministrativeaccessisblockedfrompublicnetworks.
Theriskisseriousinthiscase,sinceasuccessfulattackwouldallowanunauthorizedpersontoobtainadministrativecredentialsfortheArubacontroller.
TheWebUIcertificateshouldalwaysbereplaced,evenifwithaself-signedcertificatethateachsystemadministratormustexplicitlytrust.
802.
1XEAPTermination:Thisistheriskiestuseofthedefaultcertificate,becauseanimpersonationattackmaybecarriedoutoverawirelessnetwork,andasuccessfulattackmayrevealusernamesandpasswordhashes(providingmaterialforanofflinepasswordcrackingattempt)orallowtheattackertogetauserconnectedtoahostilenetworkwhiletheuserthinksheorsheisconnectedtoatrustednetwork.
Thedefaultcertificateshouldneverbeusedfor802.
1X.
Arubaisawarethatsomecustomersdousethedefaultcertificateinproduction,typicallyforsecuringthecaptiveportalloginscreeninguestnetworkswhereensuringtheidentityofthecontrollerisnotanimportantsecurityconsideration.
Thedefaultcertificatewasvalidforfiveyears,andwillexpireonJune29,2011.
Ifthenetworkadministratordoesnotreplacethecertificate,thefollowingwilloccur:1.
UsersconnectingtocaptiveportalorWebUIpageswillreceiveabrowserwarningshowingthattheservercertificatehasexpired.
Usersmaybypassthewarning(withvaryingdegreesofdifficultydependingonthebrowser)andcontinueontousethesystemnormally.
2.
IfEAPterminationhasbeenenabledfor802.
1X,andthedefaultcertificateisbeingusedastheservercertificate,manyclientoperatingsystemswillrefusetocontinuetheauthenticationprocess.
Thiswillresultinanapparentnetworkoutagefortheseusers.
Clientoperatingsystemsmayormaynotdisplayawarningmessagetotheuser.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Thisdocumentoutlinestheproceduresneededtoupdatethedefaultcertificate,inorderofpreference:Option1:InstallauniqueservercertificateOption2:UpgradeArubaOS2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Option1:InstallaUniqueServerCertificateThisistherecommendedapproachsinceitprovidesthebestsecurity.
Inthisapproach,thedefaultcertificatewillremainonthecontroller,butyouwillloadoneormorenewcertificatesandthenconfigurethesystemtousethenewcertificate(s).
Ifyourorganizationoperatesaninternalcertificateauthority(CA)andallclientsthatwillusethesystemalreadytrusttheinternalCA,youmayusetheinternalCAtoissueanewcertificatetothecontroller.
Thisoptionisrecommendedfor802.
1XEAPterminationandWebUIadministrativeaccesstothecontroller.
Itcanalsobeusedforcaptiveportalaslongasthegeneralpublicwillnotbeaccessingthesystem(sincetheinternalCAwillnotbetrusted,thegeneralpublicwouldreceivebrowserwarnings.
)Ifpresentingacaptiveportalpagetocomputersownedbythegeneralpublic,acertificateissuedbyapublicCA(VeriSign,GeoTrust,Comodo,etc.
)shouldbeusedsothatbrowserwarningsarenotgenerated.
YoumaychoosetouseacertificateissuedbyapublicCAforWebUIadministrativeaccesstothecontrollerandfor802.
1XEAPterminationaswell,butuseofapublicCAinsteadofaninternalCAprovidesnobenefitinthosecases.
Beforerequestingacertificate,decidewhetheryouneeda1024-bitkey,2048-bitkey,or4096-bitkey.
NotethatmanypublicCAsnolongerissuecertificateswith1024-bitkeys.
IfyouarerunningArubaOS6.
1orgreater,youmayuseacertificatewitha2048-bitkeyforanypurpose.
Youmayuseacertificatewitha4096-bitkeyonlyforcaptiveportalandWebUI.
ForWebUIorcaptiveportal,performanceisthegreatestwithsmallerkeysizes,butsecurityisslightlyreduced.
Tomaximizecompatibility,alwaysuseRSAunlessyouhaveaspecificreasontouseECC.
Ifyouarerunninganyreleasepriorto6.
1,youmayuseacertificatewitha2048-bitor4096-bitkeyonlyforcaptiveportalandWebUI.
802.
1XEAPterminationsupportsonly1024-bitkeys.
ForWebUIorcaptiveportal,performanceisthegreatestwithsmallerkeysizes,butsecurityisslightlyreduced.
Thefollowinginstructionsshouldbefollowedtoobtainandinstallaservercertificate.
1.
GenerateaCertificateSigningRequest(CSR)fromthecontrollerbynavigatingtoConfigurationManagementCertificatesCSR.
Filloutthenecessaryfields.
Afterclicking"GenerateNew",thecontrollerwillgenerateaprivatekey,whichremainslockedinsidethecontroller,andabase64-encodedCSR.
TheCSRcontainsallthedetailsneededforyourCAtoissuethecertificate.
TheCommonName(CN)fieldshouldcontainthefullURLthatwebbrowserswillnavigatetoinordertoreachthecontroller'sembeddedwebserver.
TakecaretofillouttheCommonNamefieldcorrectlyaccordingtothepurposeofthecertificate:a.
Forcaptiveportal,thesystemwillautomaticallyissueHTTPredirectsandspoofDNSresponsestothecaptiveportalclientsothatthebrowserappearstobeconnectingtothecorrectDNSnamethatmatchesthecertificatecommonname.
Thisistoensurethatbrowserwarningsarenotgenerated.
Ifthecertificateisonlybeingusedforcaptiveportal,thenameintheCNfieldisunimportant–butmakesureitfallswithin2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
yourdomainnamesothatapublicCAwillcorrectlyauthorizeownershipofthecertificate.
b.
ForWebUI,theCNfieldshouldmatchtheaddressyouusetomanagethecontroller.
ThiscanbeanIPaddressoraFullyQualifiedDomainName(FQDN).
c.
For802.
1XEAPTermination,theCNfieldisnotmatchedbytheclientagainstanyotherparameter.
ItissuggestedthatyouchooseaFQDNthatisownedbyyourorganization.
2.
Clickon"ViewCurrent".
Copythebase64textshown,andpastethisintothecertificaterequestwindowprovidedbyyourcertificateauthority.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
3.
Onceyouhaveobtainedthecertificate,navigatetoConfigurationManagementCertificatesUploadanduploadthecertificatetothecontroller.
ThecertificatewillmostlikelybeprovidedtoyouinPEMorDERformat–ifyouarenotsurewhichformatitisin,tryPEMfirstandifanerrormessageresults,tryDER.
APEMformatcertificatewillbebase64-encodedandwillbeginwiththetext"-----BEGINCERTIFICATE-----".
4.
Ifyouwanttousethenewcertificateforcaptiveportal,navigatetoConfigurationManagementGeneralandchangetheCaptivePortalServerCertificate.
IfyouwanttousethenewcertificateforWebUI,configurationisfoundonthesamescreenunder"WebUIManagementAuthenticationMethod".
5.
IfyouwanttousethenewcertificateforEAPTermination,navigatetoConfigurationSecurityAuthenticationL2Authentication802.
1XAuthentication2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
ProfileAdvancedandchangetheservercertificateforallactive802.
1XauthenticationprofilesthatuseEAPTermination.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
Option2:UpgradeArubaOSArubahasobtainedanewcertificatelabeled"securelogin.
arubanetworks.
com"fromapublicCAthatreplacestheolddefaultcertificate.
ThenewcertificatehasanexpirationdateofNovember21,2013.
ThiscertificateisincludedaspartofthefollowingArubaOSsoftwarereleases:6.
1beginningwithrelease6.
1.
0.
06.
0beginningwithrelease6.
0.
1.
15.
0beginningwithrelease5.
0.
3.
23.
4beginningwithrelease3.
4.
4.
23.
3beginningwithrelease3.
3.
3.
10AllotherArubaOSreleasesdatedlaterthanJune1,2011Afterupgradingtooneoftheabovelistedreleases,nofurtheractionisrequiredtoenablethecertificate.
Ifthesystemwaspreviouslyconfiguredtousethedefaultcertificate,itwillautomaticallyusethenewlyupdatedcertificate.
Whilethisoptionprovidesthesamelevelofsecuritygivenbythepreviousdefaultcertificate,itisnotagoodoptionwhereanysecurityrequirementsexist.
SSL/TLSsecurityisprovidedbythecertificate'sprivatekeybeingkeptsecret.
Ifthecertificate'sprivatekeybecomesknown,itispossibleforanattackertoimpersonateanyserverorwebsiteusingthatcertificatewithouttheknowledgeoftheenduser.
BecausethesamecertificateandprivatekeyareinstalledonallArubacontrollers,anattackerneedonlyreverseengineerasinglesoftwareimagetoobtaintheprivatekey.
Whilethisprocessisnon-trivial,itiscertainlynotbeyondthemeansofaskilledanddeterminedattacker.
ItisalsopossibleforanattackertosimplypurchaseanduseanArubacontrollerforthepurposeofconductinganimpersonationattack.
2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
FAQQ:WhathappensifIhaveconfigured802.
1Xdevicesinmynetworktoonlytrustthe"securelogin.
arubanetworks.
com"certificate,ortoonlytrusttheEquifaxSecureCertificateAuthorityA:Thesedeviceswillneedtobereconfiguredafterinstallationofanewcertificate.
IftheseareWindowsdevices,UNCHECK"Connecttotheseservers"andUNCHECK"EquifaxSecureCertificateAuthority"intheTrustedRootCertificationAuthorities.
Afterconnectingtothecontrollerwiththenewcertificateinstalled,Windowswillupdatethesesettingsbypromptingtheuser.
Q:IsthecertificatebuiltintotheTPMchipaffectedbythisadvisoryA:No.
AllArubacontrollersthatcontainaTrustedPlatformModule(TPM),includingtheM3,3000series,and600series,containacertificateuniquetothecontrollerthathasbeenprogrammedatthefactory.
Thiscertificateisnotexpiringandisnotaffectedbythisadvisory.
ThiscertificateisusedforMaster-Localauthentication,ControlPlaneSecurity(CPsec),andRAPauthentication.
ItisnotsuitableforuseasanSSLcertificatesinceitwasissuedbyAruba'smanufacturingCA,whichisnottrustedbybrowsers.
Q:WhatcertificateauthoritywasusedtogeneratethenewcertificateWhatchainsdoesitcontain2011ArubaNetworksInc.
FurtherdistributionprohibitedwithoutpriorwrittenconsentfromArubaNetworksInc.
ForArubaCustomers,EmployeesandAuthorizedChannelPartnersOnly.
A:ThenewcertificatewasissuedbyPositiveSSL,andultimatelychainsbackuptoUSERTrust,whichisissuedbyAddTrustExternalCARoot.
DevicesconnectingtothenetworkmusthaveUSERTrustinstalledasatrustedrootCAinorderfortheArubafactorydefaultcertificatetobetrusted.
UnderaWindowssystem,thecertificatechainappearsas
- 2011ArubaNetworksInc.相关文档
- cmdmcomodo
- WayBillcomodo
- impactcomodo
- VarParseNumFromStrcomodo
- 丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂丂comodo
- Europeacomodo
创梦网络-新上雅安电信200G防护值内死扛,无视CC攻击,E5 32核高配/32G内存/1TB SSD/100Mbps独享物理机,原价1299,年未上新促销6折,仅779.4/月,续费同价
创梦网络怎么样,创梦网络公司位于四川省达州市,属于四川本地企业,资质齐全,IDC/ISP均有,从创梦网络这边租的服务器均可以****,属于一手资源,高防机柜、大带宽、高防IP业务,另外创梦网络近期还会上线四川眉山联通、广东优化线路高防机柜,CN2专线相关业务。广东电信大带宽近期可以预约机柜了,成都优化线路,机柜租用、服务器云服务器租用,适合建站做游戏,不须要在套CDN,全国访问快,直连省骨干,大网...

HostYun(22元/月)全场88折优惠香港原生IP大带宽
在之前的一些文章中有提到HostYun商家的信息,这个商家源头是比较老的,这两年有更换新的品牌域名。在陆续的有新增机房,价格上还是走的低价格路线,所以平时的折扣力度已经是比较低的。在前面我也有介绍到提供九折优惠,这个品牌商家就是走的低价量大为主。中秋节即将到,商家也有推出稍微更低的88折。全场88折优惠码:moon88这里,整理部分HostYun商家的套餐。所有的价格目前都是原价,我们需要用折扣码...

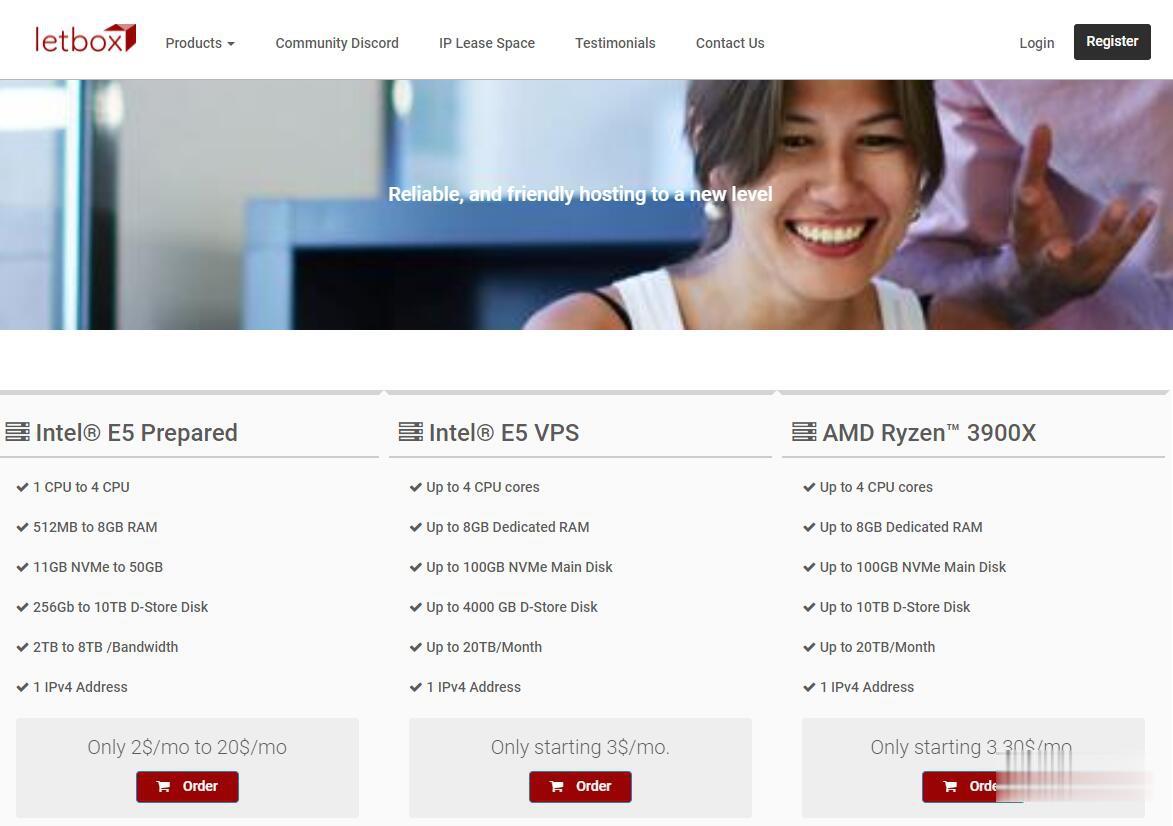
LetBox:美国洛杉矶/新泽西AMD大硬盘VPS,10TB流量,充值返余额,最低3.3美元两个月
LetBox此次促销依然是AMD Ryzen处理器+NVME硬盘+HDD大硬盘,以前是5TB月流量,现在免费升级到10TB月流量。另外还有返余额的活动,如果月付,月付多少返多少;如果季付或者半年付,返25%;如果年付,返10%。依然全部KVM虚拟化,可自定义ISO系统。需要大硬盘vps、大流量vps、便宜AMD VPS的朋友不要错过了。不过LetBox对帐号审核严格,最好注册邮箱和paypal帐号...
comodo为你推荐
-
.net虚拟主机虚拟主机如何设置net版本?美国主机空间美国主机空间不限制内容吗服务器租赁服务器租赁怎么回事的?linux主机linux主机与Windows主机的区别?谢谢中文域名注册查询怎么查我们公司的中文域名是被谁注册的?ip代理地址使用IP代理会有什么坏处吗?成都虚拟空间成都有没有能玩ps主机游戏的网咖?虚拟空间哪个好虚拟内存设在哪个盘最好虚拟主机评测网请问这几个哪个虚拟主机好100m虚拟主机一般100-200M虚拟主机一天最多支持多少人访问啊?