anddoesn[小学]tcp-ip day4 国外大学课件
TCP/IP
ARP c ontinued,ARP c ache pois oning
ARP resolution–the details
First, we' ll look at the format of an ARP message (see text, or look it up ongoogle) .
The protocol has three aspects: it specifies what a requester is to do, what areceiver is to do, and what a responder is to do. A requester is a machine thatsends an ARP request, a receiver is a machine that receives any ARP message, anda responder is a machine that sends an ARP reply.
On our Ethernet network, here' s the process in detail; for a requester:
Create an ARP message:
1. Set HW type to ' 1' (for Ethernet)
2. Set Protocol type to 080016 (for IP)
3. Set HLEN to 6 (6x8=48 bits)
4. Set PLEN to 4 (4x8=32 bits)
5. Set OPERATION to 1 (for ARP request)
6. Fill in SENDER' s HW ADD
7. Fill in SENDER' s PROT ADD
8. Set TARGET HW ADD to 0 (doesn' t know)
9. Fill in TARGET PROT ADD.
Broadcast the ARP message in an Ethernet frame.
For a receiver (of either an ARP request or reply) or responder
Extract the ARP request
If the SENDER' s PROT address in in my cache, update it with the SENDER' s HWaddress and reset the timer on that pairing
If the TARGET PROT address is identical with my IP address, carry on, otherwise,quit
Update my cache (again) , regardless of wh'ether an entry exists for that PROTaddress. (all this is done even if it isn t a request)
[ [Here it would be possible for the arp request to contain a protocol addressidentical with the protocol address of the target. We noted that Windowsoperating systems detect this, and make a note on 'the console. I tested Linux,and i't simply ignores the arp request, i. e. , doesn t generate a reply, anddoesn t update its arp cache. ] ]
If the OPERATION is a request, carry on; otherwise quit.
Fill in TARGET HW address with my Ethernet address, swap SENDER and TARGETaddresses, and set OPERATION to 2
Encapsulate ARP reply in a frame addressed to TARGET HW address.
QUESTIONS
Why does the ARP request recipient try to update its cache twice before evenexamining whether the message is a request? And once before even examiningwhether it is the intended recipient ?
( ( 1st time: save on traffic ) )
( ( 2nd: save repeating the process in reverse ) )
Gratuitous ARP
One other application of ARP that I' ll mention briefly is gratuitous ARP. Some OSs employs ARP to make sure that there are not duplicate IP addresses onthe physical network. (In fact OpenBSD does this. )
It broadcasts an ARP looking for the HW address of itself, i.e. , of its IPaddress.
If it receives a reply, it knows there is another host with its IP address, andputs a message on the console.
ARP Cache Poisoning
- ARP is a protocol which generates mappings between IP addresses and hardwareaddresses
- The basic idea, you will recall, is as follows:
- |A|-------|B|
- Host A wants to talk to host B, but A doesn’ t know B’ s HW addr
- A sends an ARP request to B, containing a mapping between A’ s HW and IPaddr
- B caches this mapping, and returns a reply with its mapping
- Communication proceeds
- There are three aspects to ARP cache poisoning that I want to discuss: (1)
What is it? (2) How do you do it? (3) Why do it?
- (1) ARP cache poisoning is when one machi’ne on a network, s’ay C, causes afalse entry to be placed in another host s, for example C s, ARP cache.- (2) It is very easy to poison ARP caches, and operating systems have triedvarious methods to protect against it, the main one being the creation of an
incomplete entry in the arp cache, and updating according to the steps aboveonly if that incomplete entry exists; this will go some way to protectingagainst unsolicited arp replies. ‘ However’ , this creates a race condition,poisoning i‘s still possible’by spaming unsolicited arp replies, in thehopes of winning the race against legitimate, solicited arp replies.
(3) Poisoning Effects
ARP cache poisoning can be used in various ways, the three most fundamentalof which are:
- (a) Eavesdropping
- Now suppose that an attacker, host C, wants to eavesdrop on communicationbetween host A and host B, but that the LAN is switched Ethernet. (How doesswitched Ethernet work?)
- |A|--------|B|
- |
- |C|
- If’ C could convince A that B’ s HW addr is C’ s, and could convince B thatA s is also C, then all traffic from B to A, and vice versa, would go to C.- Moreover, if C turned on forwarding, and had the correct HW-IP mappings, Cwould in effect become a kind of router between A and B, and would
consequently have access to all communication between A and B.
- The effect of this attack would be the disclosure of potentially confidentialinformation.
- (b) Denial of service
- On the other hand, perhaps C is not interested in eavesdropping, but wouldrather deny A and B the ability to communicate with one another.
- In this case, it would suffice for C to poison A’ s and B’ s caches withmappings eit’her to non-existent hardware addresses, or alternately, again useits own – C s – HW address, and simply not forward (the former makes iteasier for the attacker to hide his/her tracks) .
- (c) Hijacking
- Another possibility is that C is not interested in eavesdropping or DoS, butrather, wants to take over one end of the conversation.
- This would be a kind of combination of the previous two attacks: First, Cwould need to eavesdrop using the method previously outlined.
- Then, after (e.g. ) authentication, C performs a DoS on A, and takes over A’ srole in this 2-way conversation.o (Another example, besides authentication, that A might wait until thetwo hosts are communicating, is in order to sample TCP sequence andacknowledgement numbers, which is necessary in order to successfullyhijack a TCP session. This will make more sense when we come to TCP. )- This is called session hijacking (normally TCP sessions) , and there arevariations on this theme. E.g. , C could maintain the connection between Aand B, yet insert data into the communication channel.
- ARP Poisoning: not just a LAN issue
- These attacks are not limited to hosts on a single LAN. In fact, provided wehave LAN access to anynetwork on the path between A and B, these attacks arepossible.
- Examples:
- C
- |------------
- | |
- A B
- Here we merely poison A and R1.
- C
- |------------R1-----Internet----
- | |
- A B
- Poison B and R2
- C
- |------------R1-----Internet-----R2----R3---------|
- | |
- A B
- Poison R2 and R3
- anddoesn[小学]tcp-ip day4 国外大学课件相关文档
- lecture[说明]tcp-ip_day2 国外大学课件
- 美国[攻略]国外ip地址
- 产权IP版权交易平台如何进行融资交易,国外有哪些模式值得借鉴
Hostodo(年付12美元)斯波坎VPS六六折,美国西海岸机房
Hostodo是一家成立于2014年的国外VPS主机商,现在主要提供基于KVM架构的VPS主机,美国三个地区机房:拉斯维加斯、迈阿密和斯波坎,采用NVMe或者SSD磁盘,支持支付宝、PayPal、加密货币等付款方式。商家最近对于上架不久的斯波坎机房SSD硬盘VPS主机提供66折优惠码,适用于1GB或者以上内存套餐年付,最低每年12美元起。下面列出几款套餐配置信息。CPU:1core内存:256MB...

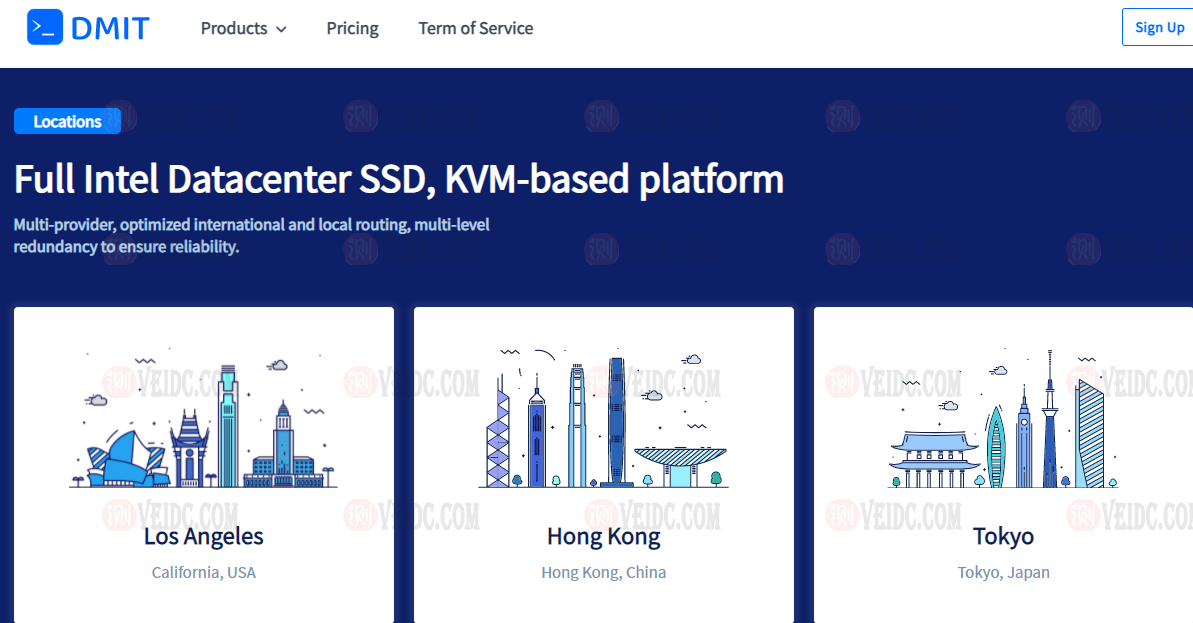
DMIT:新推出美国cn2 gia线路高性能 AMD EPYC/不限流量VPS(Premium Unmetered)$179.99/月起
DMIT,最近动作频繁,前几天刚刚上架了日本lite版VPS,正在酝酿上线日本高级网络VPS,又差不多在同一时间推出了美国cn2 gia线路不限流量的美国云服务器,不过价格太过昂贵。丐版只有30M带宽,月付179.99 美元 !!目前美国云服务器已经有个4个套餐,分别是,Premium(cn2 gia线路)、Lite(普通直连)、Premium Secure(带高防的cn2 gia线路),Prem...
RAKsmart 2021新年新增韩国服务器及香港美国日本VPS半价
RAKsmart 商家我们肯定不算陌生,目前主要的营销客户群肯定是我们。于是在去年的时候有新增很多很多的机房,比如也有测试过的日本、香港、美国机房,这不今年有新增韩国机房(记得去年是不是也有增加过)。且如果没有记错的话,之前VPS主机也有一次磁盘故障的问题。 这不今天有看到商家新增韩国服务器产品,当然目前我还不清楚商家韩国服务器的线路和速度情况,后面我搞一台测试机进行...

-
directional163存在问题的应用软件名单(2020年第四批)支持ipad支持ipad支持ipad支持ipadipad上网新买的ipad怎么用。什么装程序 怎么上网tcpip上的netbios怎么启用TCP/IP上的NetBIOS联通版iphone4s怎么知道到苹果4s是联通版,还是移动版重庆电信宽带管家重庆电信宽带安装收费