输入网站漏洞检测归类和解决方案(Website vulnerability detection, classification and solution)
网站漏洞检测归类和解决方案Website vulnerability detection,classification and solution
Everything is ready except one crucial element. Last night, thewest wind withered green trees, alone on the tall buildings,looking at the end of the road. I will mount a long wind someday and break the heavy waves, and set my cloudy sail straightand bridge the deep, deep sea。 The pen falls into the wind andrain, and the poem becomes the ghost. Who knows nothing? It' snever too late to mend. This article is contributed by s8h4a2n6DOC documents may experience poor browsing on the WAP side. Itis recommended that you first select TXT, or download the sourcefile to the local view.
A,
Typical website vulnerability classification
According to the risk level, the website vulnerability can bedivided into three kinds of high risk, medium risk and low risk.Among them, high-risk vulnerabilities must be blocked. Some ofthe loopholes in the medium and low risk vulnerabilities mustbe blocked. There are also some medium and low riskvulnerabilities, which may be selectively blocked because thecost of plugging may be higher than the losses caused by nonblocking. Tools can be used to search the platform forvulnerability scanning, the specific address is:http://www. iiscan.com typical website vulnerabilityclassification and corresponding sealing requirements as shownin the table below:
Risk level
1, the highriskof SQL injection2, cross site vulnerabilitiesMedium and low risk 1, default test case file 2, managementbackground landing portal
Medium and low risk 1, email address exists
Vulnerability name
3, XPATH injection leak 3, application error caused by 2,invalid link hole information leakage 4, backup files causedby source code leakage 3, Web application default directorySealing requirement
Must plug
Selective plugging
One
Two,
Typical website vulnerability impact and Solutions
1, SQL injection vulnerability impact: this vulnerabilitybelongs to the common vulnerabilities in Web applicationsecurity, belonging to OWASP TOP 10 (2007) in the injection
class vulnerabilities. SQL injection vulnerabilities arepresent in many WEB applications. SQL injection is an attackerwhouses code flaws to attack, and canbe used in any applicationparameter that can affect database queries. For example, theparameters of the URL itself, post data, or cookie values. Anormal SQL injection attack depends largely on the attacker' saccess to information from the error message. However, even ifno error messages are displayed, the application may still beaffected by the SQL injection. In general, SQL injection is anattack on Web applications rather than on the web server or theoperating system itself. As its name suggests, SQL injectionis the act of adding unexpected SQL commands to a query tomanipulate the database in a way that database administratorsor developers do not anticipate. If successful, you can obtain,modify, inject, or delete data from the database server thatis used by the vulnerability web application. In some cases,the SQL can be injected into the fully controlled system.Solution: protection recommendations include the deployment oflayered security measures (including in accept user input whenusing parameterized queries) , to ensure that applications useonly the expected data, strengthening the database server toprevent access data inappropriate. The following measures arerecommended to prevent SQL injection vulnerabilities:Two
Use the following suggestions for development. Written from theweb application of SQL injectionattack effect. Aparameterizedquery: SQL injection from the attacker control data to modifythe query query logic, so the best way to prevent SQL injection
attacks is to query the logic and data separation, which canprevent the execution of the injection from the user inputcommands. Defects in this way are likely to have an impact onperformance (but with little impact) , and each query on the sitemust be constructed in this way to be fully valid. Justbypassing a query inadvertently is enough to cause theapplication to be affected bySQL injection. The following codeshows an example of a SQL statement that can do SQL injection.SSql = "SELECT, Locat i onName, FROM, Locat i ons"";ssql=ssql+ “LocationID=” +要求[” ] ocmd. commandtext=ssqlLocationID”
下面的例子使用了参数化的查询不受SQL注入攻击的影响。ssql = “SELECT * FROM位置” ssql = ssql + “Locat ionID = @LocationID” ocmd. commandtext =ssql ocmd。参数。添加 “@LocationID” 要求“LocationID [” ]
应用程序没有包含用户输入向服务器发送SQL语句而是使用@LocationID-参数替代该输入这样用户输入就无法成为SQL执行的命令。
三
这种方式可以有效的拒绝攻击者所注入的任何输入尽管仍会生成错误但仅为数据类型转换错误而不是黑客可以利用的错误。以下代码示例显示从HTTP查询字符串中获得产品ID并使用到SQL查询中。请注意传送给SqlCommand的包含有选择的字符串仅仅是个静
态字符串不是从输入中截取的。此外还请注意使用Sql Parame ter对象传送输入参数的方式该对象的名称@ PID匹配SQL查询中所使用的名称。
C #示例
一串connstring
=webconf igurationmanager。 connectionStrings [ “myconn” ] 。connectionstr ING使用SqlConnection conn=新的SqlConnectionconnstring {康涅狄格州open() SqlCommand CMD =新SqlCommand “select count *从产品prodid= “PID” CONNSqlParameter prm =新的SqlParameter “PID”
SqlDbType.VarChar 50 PRM。值=请求。 QueryString [ “PID” ] CMD参数。添加PRM int reccount=int命令。executescalar() }
四vb.net示例
昏暗的connstring
作为
字符串
=webconf igurationmanager。 ConnectionStrings “ConnectionString myconn” 。
使用新的SqlConnection conn connstring康涅狄格州open()暗淡CMD为SqlCommand=新SqlCommand “sel ect count *从产品prodid = “PID” CONN昏暗的PRM为SqlParameter =新的SqlParameter “PID”
SqlDbType.VarChar 50 PRM。值=请求。 QueryString “PID” 命令参数。添加PRM昏暗的reccount整数=CMD executescalar()端使用。
验证输入可通过正确验证用户输入的类型和格式防范大多数SQL注入攻击最佳方式是通过白名单定义方法为对于相关的字段只接受特定的帐号号码或帐号类型或对于其他仅接受英文字母表的整数或字母。很多开发人员都试图使用黑名单字符或转义的方式验证输入。总体上讲这种方式通过在恶意数据前添加转义字符来拒绝已知的恶意数据如单引号这样之后的项就可以用作文字值。
五
这种方式没有白名单有效 因为不可能事先知道所有形式的恶意数据。
对于安全操作============
使用以下建议帮助防范对Web应用的SQL注入攻击。
限制应用程序权限限制用户凭据仅使用应用运行所必需权限的任何成功的SQL注入攻击都会运行在用户凭据的环境中
Although restricting permissions can not completely preventSQL injection attacks, it can greatly increase the difficulty.Strong system administrator password policy: usually theattacker needs to function to the administrator account usingspecific SQL command, if the system administrator password isthen easier to violent speculation, increasing the likelihoodof success of SQL injection attacks. Another option is not touse the system administrator password at all, but to create aspecific account for a specific purpose.
Consistent error message program: make sure you provide aslittle information as possible when a database error occurs.Do not leak the entire error message and process error messageson both the web and the application server. When a web serverencounters a processing error, a generic web page responseshouldbeused, or theuser redirectedto the standard location.Never release debug information or other details that might beuseful to attackers.
For instructions onhow to close verbose errormessages in IIS,see:
Six
Http://www.microsoft.com/windows2000/en/server/i is/default.asp? Url= /windows2000/en/server/i is/htm/core/iierrcst.htm?
Use the syntax below to suppress error messages on the Apacheserver:
Syntax: , ErrorDocument, <3-digi t-code>, Examp le: ,
ErrorDocument, 500, /webserver_errors/server_error500. txtApplication servers like WebSphere usually default byinstalling error messages or debugging settings. Forinformation about how to suppress these error messages, referto the application server document.
Stored procedures: if not used, delete the SQL storedprocedures such as master. .Xp_cmdshell, xp_startmail,xp_sendmail, sp_makewebtask, and so on.
The SQL injection vulnerability fundamentally depends on thecode for the web application. Although not a fix, you can detectSQL injection attacks by adding rules that incorporate regularexpressions to IDS as an emergency measure. Although it isimpossible to fix all possible SQL injection vulnerabilities,it is easy to implement and requires attackers to improve theirmethods in order to achieve successful attacks. Regularexpressions can be used as follows.
Delete the SQL regular expression metacharacters: / (\%27) |(' ) | (\-\-) | (\%23) | (#) /ix
Seven
Following the regular expression canbe added to the Snort alertTCP$EXTERNAL_NET ru l es: any-> $HTTP_SERVERS$HTTP_PORTS (msg:
"SQL Injection-
Paranoid; flow:to_server, established; uricontent: .Pl ; pcre:/ (\%27) | (' ) | (\-\ -) | (%23) | (#) ;classtype:Web-application-attack; sid:9099; /i rev:5) ;The regular expression of traditional SQL injection attacks:/\w* ((\%27) | (' ) ( |o| ) (\%6F) (\%4F) ( |r| ) (\%72) (\%52)) /ixThe regular expression to delete the UNION keyword SQLinjection attack: / ((\%27) | (' )) union/ix (\%27) | (' )Similar regular expressions can be written for other SQLqueries such as select, insert, update, delete, drop, and soon.
Regular expressions for SQL injection attacks are detected onthe MS SQL server: /exec (\s|\+) + (s|x) p\w+/ix
For quality assurance ============
E i gh t
Addressing SQL injection defects ultimately requires codebased fixes, providing information necessary to fix thesevulnerabilities for development and for the steps described inthe security operations section. The following steps outlinehow to manually test SQL injection for an application.How do you manually test SQL injection into an application?:
- 输入网站漏洞检测归类和解决方案(Website vulnerability detection, classification and solution)相关文档
- 模块网站漏洞检测软件WEBSCAN的策划和完成.doc
- 输入网站漏洞检测归类和解决方案(Site vulnerability detection, classification and solution)
- 漏洞网站漏洞检测软件的设计与应用
- 病毒学校规章制度之中学网站病毒检测和网络安全漏洞监测制度
- 漏洞网站漏洞检测软件的设计与应用(本科范文)
- 网站漏洞检测谁有网站漏洞检测工具?一般黑客使用的,急需!可以发到我邮箱qiutiandaole010@163.com
legionbox:美国、德国和瑞士独立服务器,E5/16GB/1Gbps月流量10TB起/$69/月起
legionbox怎么样?legionbox是一家来自于澳大利亚的主机销售商,成立时间在2014年,属于比较老牌商家。主要提供VPS和独立服务器产品,数据中心包括美国洛杉矶、瑞士、德国和俄罗斯。其中VPS采用KVM和Xen架构虚拟技术,硬盘分机械硬盘和固态硬盘,系统支持Windows。当前商家有几款大硬盘的独立服务器,可选美国、德国和瑞士机房,有兴趣的可以看一下,付款方式有PAYPAL、BTC等。...
提速啦(24元/月)河南BGP云服务器活动 买一年送一年4核 4G 5M
提速啦的来历提速啦是 网站 本着“良心 便宜 稳定”的初衷 为小白用户避免被坑 由赣州王成璟网络科技有限公司旗下赣州提速啦网络科技有限公司运营 投资1000万人民币 在美国Cera 香港CTG 香港Cera 国内 杭州 宿迁 浙江 赣州 南昌 大连 辽宁 扬州 等地区建立数据中心 正规持有IDC ISP CDN 云牌照 公司。公司购买产品支持3天内退款 超过3天步退款政策。提速啦的市场定位提速啦主...

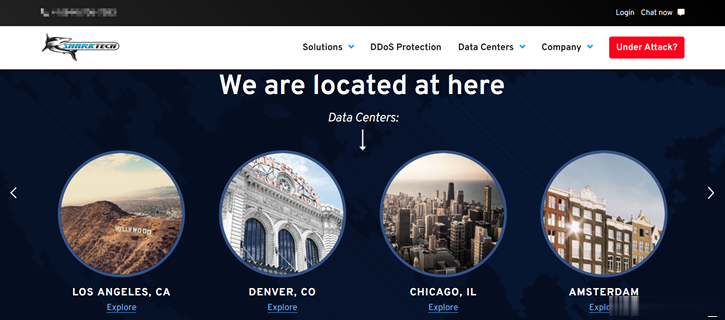
Sharktech($49/月),10G端口 32GB内存,鲨鱼机房新用户赠送$50
Sharktech 鲨鱼机房商家我们是不是算比较熟悉的,因为有很多的服务商渠道的高防服务器都是拿他们家的机器然后部署高防VPS主机的,不过这几年Sharktech商家有自己直接销售云服务器产品,比如看到有新增公有云主机有促销活动,一般有人可能买回去自己搭建虚拟主机拆分销售的,有的也是自用的。有看到不少网友在分享到鲨鱼机房商家促销活动期间,有赠送开通公有云主机$50,可以购买最低配置的,$49/月的...
-
present37eacceleratoraccess violation问题的解决办法!photoshop技术ps几大关键技术?canvas2七尾奈留除了DC canvas2 sola EF 快乐小兔幸运草 以外改编成动画的作品有哪些?icloudiphone自己用icloud把iPhone抹掉了.激活却不是自己的id怎么破css3按钮html点击按钮怎么弹出一个浮动的窗体firefoxflash插件火狐安装不了FLASH为什么?下载完后明明安装完成,火狐却仍然提示“缺少插件”firefoxflash插件火狐浏览器怎么安装flashwin7还原系统win7如何一键还原电脑系统怎么操作win7还原系统win7怎么初始化系统?系统还原?