Tejara166dd.com
166dd.com 时间:2021-04-08 阅读:()
Copyright2018AccentureSecurity.
Allrightsreserved.
1GOLDFIN:APersistentCampaignTargetingCISCountrieswithSOCKSBOTJuly26,2018CYBERADVISORYCopyright2018AccentureSecurity.
Allrightsreserved.
2SUMMARYAnumberofsecurityvendorsreportedaseriesofcyber-attacksinvolvingtheuseofamalwarefamilycalledSOCKSBOTandclaimedtobeassociatedwithCANDLEFISH(a.
k.
a.
Patchwork,DroppingElephant).
However,asdisclosedinthisreport,researchbyiDefenseanalystsshowsthatSOCKSBOTwasinfactusedbyathreatgroupinan18-month-longcampaigndubbedGoldfin,spoofingfinancialinstitutionsintheCommonwealthofIndependentStates(CIS)countriessinceasearlyasFebruary2017toasrecentlyasMay2018.
Basedonthetactics,techniquesandprocedures(TTPs)observedinthiscampaign,iDefenseassesseswithmoderateconfidencethatthereportedcampaignisunlikelytobeassociatedwithCANDLEFISH.
Inaddition,iDefenseanalystshaveidentifiedinfrastructureoverlapandtheshareduseofaPowerShellobfuscationtechniquewithFIN7.
AlthoughtheseobservationsarenotenoughtoattributetheGoldfincampaigntoFIN7,iDefenseassessesthesetobeinterestingandnoteworthyobservationsthatfurtherhighlightsthecomplexrelationshipsthatexistbehind-the-sceneinorganizedcybercrime.
HOWTOUSETHISREPORTINTENDEDAUDIENCEiDefenseisprovidinginformationaboutthereportedcampaignstothegeneraliDefensecustomerbase,withthisreportbeingintendedforsecurityoperationscenter(SOC)analystsandengineers.
Managementandexecutiveleadershipmayalsowanttousethisinformation.
HOWTOUSETHISINTELLIGENCEiDefenseisprovidingthisinformationsothatcustomersareawareofthemodusoperandiofahighlyactivethreatgroupthatistargetingfinancialinstitutionsforfinancialgain.
SOCanalystsandengineerscanusethisIA'sdetailedinformationpertainingtotheworkingsofamalwarefamilyandindicatorsofcompromise(IoCs)tocontainormitigatethediscussedthreatthroughmonitoringorblocking.
SOCanalystscanusetheinformationprovidedintheAnalysisandMitigationsectionsofthisIAforhuntingactivitiesforsystemsthatmayhavealreadybeencompromised.
AnalystsandsecurityengineerscanusetheIoCsbyaddingthemtohuntinglistsonendpointdetectionandresponse(EDR)solutionsaswellasnetwork-andhost-basedblackliststodetectanddenymalwareimplantationandcommand-and-control(C2)communication.
IntelligenceanalystsmaywanttousetheinformationprovidedinthisIAtobetterinformtheirownanalyses.
TheprovidedinformationcanalsohelpinformongoingintelligenceCopyright2018AccentureSecurity.
Allrightsreserved.
3analysesandforensicinvestigations,particularlyforcompromisediscovery,damageassessment,andattribution.
Managementandexecutiveleadershipmayusethisinformationtoassesstherisksassociatedwiththethreatdescribedhereintomakeoperationalandpolicydecisionsaccordingly.
HOWTHISINTELLIGENCEHELPSADDRESSEXISTINGORPOTENTIALTHREATSKnowledgeofthegroup'stactics,techniques,andprocedures(TTPs)shouldhelptobetterinformdetectionandresponsetoattacksbythisthreatgroup.
CAMPAIGNANALYSISiDefenseanalystscameacrosstwospear-phishingcampaignsinOctober2017involvingtheuseofamalwarefamilypubliclyknownasSOCKSBOT.
OnecampaignspoofstheHalykBank(Exhibit1)andanotherspoofsthePrivatBank(Exhibit2):Exhibit1:Spear-PhishingEmailSpoofingHalykBankCopyright2018AccentureSecurity.
Allrightsreserved.
4Exhibit2:ContentofaSpear-PhishingE-mailSpoofingPrivatBankSharedonthePublicForumdoneckforum.
comAsExhibits1and2show,bothemailscontainanidenticalmessage,evendowntothelocationoftheembeddedhyperlinks.
TheonlydifferencesaretheembeddedURLsandthesignatureoftheemailinordertoreflectthefinancialinstitutiontheattackerswerespoofing.
Thisinformationsuggestssomesortofphishingkitwaslikelyusedtogeneratethephishingemails.
Anapproximatetranslationofthee-mailspoofingHalykBankisasfollows:Subject:Notificationofopeninganaccount(HalykBankofKazakhstan)Dearcustomer,anaccountwiththePeople'sBankofKazakhstanhasbeenopenedinyourname,youcanfinddetailedinformationintheattachedfile.
Ifyoudidnotreceiveanenvelopewithaloginandpassword,thenyouneedtoregistertoaccessthePersonalArea.
Incaseoflossoflogin/password,youcanregisteranewoneinthesection"Passwordrecovery".
Ifintheprocessofworkyouhaveanyquestionsorproblems,pleasecontacttheCustomerServiceDepartmentatthecontactslistedbelow.
Ourspecialistsarealwaysreadytohelpyou.
Theembeddedmalicioushyperlinksusedintherespectiveattacksareasfollows:hxxp://halyk-bank[.
]com/dog.
ziphxxp://privatbank-ua[.
]com/dog.
zipSubsequenttechnicalanalysisoftheinfectionchaininvolvedlediDefensetouncoveran18-monthlongcampaignofspoofingbanksinCIScountries,withthemostrecentcampaignobservedonMay28,2018spoofingtheIdeaBankCJSC:Copyright2018AccentureSecurity.
Allrightsreserved.
5Exhibit3:Spear-PhishingEmailSpoofingIdeaBankCJSCTheforummemberreportsthattwospear-phishingemailswerereceived:oneclaimingtobeanotificationaboutopeninganaccountandtheotherclaimingtobeanotificationofaloanbeingtakenout.
Thecontentofthelatteremailisapproximatelytranslatedbelow:Dearclient,inyourname,aloanwasissuedtoIdeaBank,formoredetails,seetheattachedfileinwhichthefullnameandphonenumberofyourpersonalloanexpertisindicated,theamountandconditionsforrepayingtheloan.
Anenvelopewithacreditagreementwassenttoyouraddress.
Incaseyoudidnotreceivetheenvelope,youshouldcontactyourpersonalexpert.
Incaseoflossofthecontract,youcanrestoreitatthenearestbranchofthebankorrequestaduplicatethroughyourpersonalexpert.
Foranyquestionsyouareinterestedin,youcancontactyourpersonalexpertortheCustomerServiceDepartmentatthecontactslistedbelow.
Ourspecialistsarealwaysreadytohelpyou.
Yoursfaithfully,IdeaBankCJSCPhoneforcallsfromabroad:+375(17)306-33-14Intheattacksobserved,allinvolvedaphishingemailwithtwoembeddedURLsdirectingtheusertodownloadafilenameddog.
zip.
Basedonthecontentofthee-mailsandthedomainnames,thefollowingbankswerespoofedinthiscampaign:HalykBank(Kazakhstan)PrivatBank(Ukraine)IdeaBank(Belarus)Copyright2018AccentureSecurity.
Allrightsreserved.
6TejaraBank(Iran)Itisalsonoteworthythatinbothphishingkits,therearealwaystwohyperlinkslinkingtothesamemaliciousfile:oneinthebodyofthemessageandoneattheendofthee-mailinalinkcalledДоговор(whichtranslatestoContract).
Thenextsectiondetailstheinfectionchainthatfollowstheinitialdownload.
INFECTIONCHAINANALYSISThegeneralinfectionchainobservedinthiscampaignisasshowninExhibit4:Exhibit4:TheInfectionChainUsedintheSOCKSBOTCampaignSTAGE1-JAVASCRIPTDROPPERBothlinksdeliveredaZIParchivefilenameddog.
zip:hxxp://halyk-bank[.
]com/dog.
zip-211fbf34749df5e717e8b11fecb3f648hxxp://privatbank-ua[.
]com/dog.
zip-b3fb88a5aa791aea141bf3b4cf045355BothcontainaJavaScriptfilenameddog.
jswiththeMD5signatures9a273653364dfb143ff196d826d2bac4and21a09cf81f3584a741c7167f622d6c50,respectively.
TheJavaScriptfilecontainsheavilyobfuscatedcodeasExhibit5shows.
Themaliciouscodeisinfacthiddenascommentsandisdynamicallydeobfuscatedoncethescripthasbeenexecuted.
Copyright2018AccentureSecurity.
Allrightsreserved.
7Exhibit5:ObfuscatedCodeindog.
jsOncedeobfuscated(seeExhibit6),itisclearthatthecodeisdesignedtodotwothings:1.
Tolookforarunninganti-virusprocesses,suchasavp.
exe(KasperskyAntivirus).
Notethatsomevariantsofthemalwarealsosearchforekrn.
exe(ESET),cis.
exe(Comodo)andavgnt.
exe(Avira).
2.
TodropandexecuteaPowerShellscriptnamedsetup.
ps1.
ThisscriptisgeneratedbasedonBase64encodeddatastoredinvariablesnameddllDataandcode.
3.
Deletesetup.
ps1Exhibit6:DeobfuscatedCodeindog.
jsCopyright2018AccentureSecurity.
Allrightsreserved.
8STAGE2-POWERSHELLDROPPERWITHEMPIREThePowerShellscriptsetup.
ps1usedineachattackhastherespectiveMD5signatures521c81c62836a233a6e771bc3491300fand00c38b787eac602ffaed0b9372f2c443.
Thescriptisdesignedforthefollowing(seeExhibit7):1.
CreateaPowerShellscriptnamedcheckupdate.
ps1inC:\Users\Public\Downloads\(Thispathishardcodedinthemalware).
ThecontentofthisscriptisstoredinavariablenameddataandisBased64encoded2.
Createacmdletthatwould:a.
movethescriptcheckupdate.
ps1tothehomedirectoryforthecurrentPowerShellinstallb.
establishpersistencebycreatingaWindowsservicenamedCheckforupdates,setto"delay-auto"startandexecutecheckupdate.
ps13.
UseamodifiedversionofthefunctionInvoke-EventVwrBypassfromtheEmpirePost-exploitationframeworktobypassUACandexecutetheabovecmdletExhibit7:DeobfuscatedCodeinsetup.
ps1Copyright2018AccentureSecurity.
Allrightsreserved.
9STAGE3-POWERSHELLREFLECTIVELOADERSimilarly,checkupdate.
ps1usedineachattackhastherespectiveMD5signatures54e7f3a1a1a8857e35a45f4eb2a3317dand29573b1fa60bce8e04dd2a4d554a7447.
Unsurprisingly,thisscriptalsocontainsobfuscatedcode.
Themaliciouspayloadiscompressed,Base64encoded,andembeddedwithinthescript,whichissimilartoatechniqueusedinPowerSploit.
However,theobservedtechniqueappearstobeavariantofPowerSploitastheencodedpayloadisfurthersplitintoanumberofchunksthataredynamicallyloadedintoanarrayvariablenamed$OArrasshowninExhibit8:Exhibit8:ObfuscatedCodeincheckupdate.
ps1ThecodeisinfactaPowerShellreflectiveloaderscriptwithadynamic-linklibrary(DLL)binaryembeddedasBase64-encodeddata(Exhibit9).
Copyright2018AccentureSecurity.
Allrightsreserved.
10Exhibit9:DeobfuscatedCodeincheckupdate.
ps1STAGE4-SOCKSBOTThespecificSOCKSBOTsampleanalyzedinthisreporthasthefollowingproperties:Filename:socksbot.
dllMD5:90f35fd205556a04d13216c33cb0dbe3FileSize:17.
0KB(17408bytes)CompiledTimeStamp:2017-10-2717:46:05Copyright2018AccentureSecurity.
Allrightsreserved.
11Asmentionedinthelastsection,theSOCKSBOTimplantistypicallydeliveredasaBase64-encodedstringreflectivelyloaded(viatheReflectiveLoader@@YGKPAX@Zexportedfunction)inanewlystartedsvchost.
exeprocess.
Assuch,theimplantexistsonlyinmemoryandnevertouchesthedisk.
Theimplantwillfirstverifyifanyofthemutexesinthefollowingformatarepresentinordertonotruntwice:Global\%snpsGlobal\%sstpExhibit10showsanexampleofacreatedmutex.
Exhibit10:MutexCreationa321c0d8979a05bdnpsTheSOCKSBOTimplanthasthefollowingcapabilities:Enumerateprocesses(processlist)TakescreenshotsDownload,upload,write,andexecutefilesCreateandinjectintonewprocessesCommunicatetoC2viasocketsThisimplantwillcommunicatewiththedesignatedC2serverbyfirstcreatingabufferandwill,onfirstexecution,communicatetotheC2serverthatithassuccessfullyinfectedatargetbyusinga.
phpURIthatispseudo-randomlygenerated.
SOCKSBOTusestheObtainUserAgentStringAPItodeterminethedefaultuser-agentofthemachine.
AnexampleofarequesttotheC246.
166.
163[.
]243isshowninExhibit11.
Exhibit11:TraffictotheC2ServerTheC2serverortheoperatoroftheSOCKSBOTimplantcanthenrespondwithaspecificHTTPstatuscodetoperformasetofactions.
Exhibit12showsthisoptionintheimplant.
Copyright2018AccentureSecurity.
Allrightsreserved.
12Exhibit12:C2OptionsThefollowingstatuscodesaresupported:200:createandstartnewsocket202:enumerateprocessesandtakescreenshot203:performasetofactions(download,upload,execute)Exhibit13showsanexampleofpossibleactions:Exhibit13:HTTPStatusCode203ReturnOptionsTheactionsthattheoperatorcanperformareasfollows:WriteandexecutefilesCopyright2018AccentureSecurity.
Allrightsreserved.
13ExecutePowerShellscriptsExecuteaPowerShellscriptandexitSOCKSBOTcanthuswriteotherPowerShellscriptstothe%TEMP%folderandexecutethesehiddenfromtheuser.
Thisisachievedwiththefollowingcommand:%s\System32\WindowsPowerShell\v1.
0\powershell.
exe-ExecutionPolicyBypass-NoLogo-NonInteractive-NoProfile-WindowStyleHidden-File"%s"ThisallowstheattackertouploadotherobfuscatedPowerShellscriptsonthemachineand,assuch,makesSOCKSBOTapowerfulandpersistentbackdoor.
Altogether,theSOCKSBOTsamplesobservedandanalyzedinthisreportareasfollows:90f35fd205556a04d13216c33cb0dbe32a4d16ddad27c6eb60e197b6b07c2df014f71d5cb8f15f0a9943b5d709a85b7392dfd0534b080234f9536371be63e37a039d9e47e4474bee24785f8ec530769555a57741f49d6c887992353bc47846bcOnlythreedifferentC2servershavebeenobserved:5.
8.
88[.
]6446.
166.
163[.
]2435.
135.
73[.
]113INFECTIONCHAINVARIATIONSWhilethedescribedinfectionchainaboveisthemostcommoninfectionchainobserved,iDefenseanalystshavealsoobservedanumberofdifferentvariationsinrelatedcampaigns:1.
SOCKSBOTDropper2.
dog.
jsObfuscation3.
RandomPowerShellScriptNames4.
ReflectiveloadingPowerShellScriptObfuscationVARIATION1:SOCKSBOTDROPPERAsidefromthePowerShellreflectiveloader,iDefenseanalystshavealsoidentifiedadropperexecutablebinarywiththefollowingpropertiesthatwasusedtoreflectivelyloadSOCKSBOTintoachosenprocess(usuallysvchost.
exe):Filename:MD5:14f71d5cb8f15f0a9943b5d709a85b73FileSize:23.
6KB(24200bytes)CompiledTimeStamp:2017-02-0113:40:14Copyright2018AccentureSecurity.
Allrightsreserved.
14Signer:MagnumTravelClub(Serial:1F8A3E60EEC1E3AA63B39BDD26E110FB)Notethatthebinarywassignedwithacode-signingcertificatepurportedlyfromanorganizationcalledMagnumTravelClub.
ThisdropperwillcreateacopyofitselfinC:\Programdata\Logsasahiddensystemfileandwillthendeletetheoriginalfile.
Anothercopywillbecreatedin%appdata%\Microsoft\Windows\StartMenu\Programs\Startupwiththesamepropertiestoensurepersistence.
Finally,thedropperwillstartanewsvchost.
exeprocessinasuspendedstateandconsequentlyreflectivelyload(andinject)theSOCKSBOTimplantintotheprocess.
AnadditionalWindowsservicemaybecreatedforpersistenceaswell,whichisdonebyfirstenumeratingexistinglegitimateservicesandcreatinganewservicespoofingoneoftheserviceswithanalmostidenticalname.
Inthiscase,anewservicenamedXindowsErrorReportingServicewascreated(seeExhibit14).
Exhibit14:ServiceCreationWhilethisdropperdoesindeedloadtheSOCKSBOTimplant,allotheriterationsorcampaignshaveusedscripts,inparticularJavaScriptandPowerShell,toreflectivelyloadtheSOCKSBOTpayload.
VARIATION2:DOG.
JSOBFUSCATIONWhilemostdog.
jssamplesobservedwereobfuscatedasreportedintheinfectionchainsection,therearealsoversionsthatwerenotobfuscatedatallorwereobfuscatedusingadifferentobfuscationtechniquesuchasdifferentcharacterencoding(Exhibit15):Copyright2018AccentureSecurity.
Allrightsreserved.
15Exhibit15:ADifferentObfuscationTechniqueUsedindog.
jsOnceexecuted,thissample(MD5:b01cf8f375bc0aff2cfe3dc1b4c1823c)willdeobfuscateandgenerateanewfilecalled~~1.
tmpin%appdata%\Futures.
Thescriptisdeletedafterexecution.
VARIATION3:RANDOMPOWERSHELLSCRIPTNAMESCertainvariantsofdog.
jsalsohaveanewfunctiontorandomlygeneratefilenamesforthesecond-andthird-stagePowerShellscripts:functionmakerndps1(){vartext="";varpossible="ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789";for(vari=0;i<5;i++)text+=possible.
charAt(Math.
floor(Math.
random()*possible.
length));returntext+'.
ps1';}4.
REFLECTIVELOADINGPOWERSHELLSCRIPTOBFUSCATIONAsidefromchangestothedog.
jsobfuscation,iDefenseanalystshavealsofoundadifferentobfuscationtechniqueusedtoobscurethecodeinthereflectiveloadingscript(seeExhibit16):Copyright2018AccentureSecurity.
Allrightsreserved.
16Exhibit16:DifferentObfuscationTechniqueUsedintheReflectiveLoadingPowerShellScriptThesampleconcernedhastheMD5signaturec38b06f871d2268972fa01725b59d7ed.
Notealsothattheexecutioncommandusedforpersistenceisagainencoded(seeExhibit17):Exhibit17:ObfuscatedExecutionCommandinCheckforupdateServiceUsedforPersistenceATTRIBUTIONBasedonthepreferencetospooffinancialinstitutionsinCIScountries,thenetworkinfrastructureusedandtheobservedtargeting,iDefenseassesseswithmoderateconfidencethatthereportedcampaignisunlikelytobeassociatedwithCANDLEFISH.
Furthermore,iDefenseanalystshaveidentifiedanumberofinterestingandnoteworthyoverlapswithFIN7:IdenticalWHOISinformationusedindomainsassociatedwiththeGoldfincampaignandFIN7,aswellasnetworkhostingoverlapShareduseofaPowerShellobfuscationtechniqueCopyright2018AccentureSecurity.
Allrightsreserved.
17OVERLAP1:IDENTICALWHOISINFORMATIONANDNETWORKHOSTINGOVERLAPResearchshowsthatthedomainsprivat-bankau[.
]com,halyk-bank[.
]com,andtejara-bank[.
]comallhavetheorganizationnameGoldfinLLC,anear-identicalregistrantaddress(seebelow),anda@rambler.
rue-mailaddressusedastheregistrante-mailaddress.
RegistrantOrganization:GoldfinLLCRegistrantStreet:ulArbat5RegistrantCity:MoscowRegistrantState/Province:MoscowRegistrantPostalCode:115343RegistrantCountry:RUThispatternoverlapswithtwootherdomains-despanabrandfood[.
]comandsilverdiners[.
]com(seeExhibit18)-thatiDefensecurrentassesseswithlowconfidencearelikelyassociatedwithFIN7duetothefollowing:1.
SpoofingrestaurantchainsDespaaBrandFoods(legitimatedomaindespanabrandfoods.
com)andSilverDiner(legitimatedomainsilverdiners.
com),aknowntechniqueassociatedwithFIN7.
Thewebsitedespanabrandfood[.
]comremainsindexedbyGoogle(seeExhibit19)2.
PreviouslyresolvedtotheIPaddress192.
99.
14[.
]211,whichwasreportedbyTrustwaveandtr1dxasassociatedwithFIN7towardslate2016andearly2017.
Inaddition,likemanydomainsassociatedwithFIN7aswellastheCarbanakgroup,manyofthedomainsusedintheGoldfincampaignwerealsoparkedat31.
41.
41[.
]41whichisassociatedwithCISHosting.
However,iDefenseanalystsareawarebothhostsarelikelytobeshared/parkinghostshencetheassociationwithFIN7basedonthisoverlapisoflowconfidence.
Exhibit18:WHOISInformationSimilaritiesbetweenDomainsUsedintheGoldfinCampaignandThoseAssociatedwithFIN7Copyright2018AccentureSecurity.
Allrightsreserved.
18Exhibit19:Spoofingdomaindespanabrandfood[.
]comremainsindexedbyGoogleatthetimeofwriting,showingtheattacker'sintentiontoplagiarisethelegitimatewebsitedespanabrandfoods[.
]comExhibit20illustratestheoverlappinginfrastructurebetweentheGoldfincampaignandinfrastructureassociatedwithFIN7:Exhibit20:MaltegoGraphShowingtheOverlappingInfrastructurebetweenGoldfinCampaignandFIN7Copyright2018AccentureSecurity.
Allrightsreserved.
19OVERLAP2:SHAREDUSEOFAPOWERSHELLOBFUSCATIONTECHNIQUEAsmentionedintheinfectionchainanalysis,thecodeembeddedwithinthethird-stagePowerShellscriptcheckupdate.
ps1isobfuscatedusingatechniquesimilartothatofPowerSploit.
However,thetechniqueusedappearstobeanichevariantastheembeddedpayloadisfurthersplitintochunksanddynamicallyaddedtoanarrayvariablenamed$OArr.
Interestingly,iDefenseanalystshavepreviouslyobservedthisobfuscationusedinaPowerShellcomponent(MD5:87327b4045b9d004697aec7e7a4b9ba8)thatwasdroppedbyaHALFBAKEDsample(MD5:31fcf8a4ec7a4c693eda9336321cf401)backinAugust2017.
HALFBAKEDisamalwarefamilyassociatedwithFIN7.
Exhibit21:SimilarPowerShellObfuscationTechniqueUsedbetweentheGoldfinCampaignandFIN7WhiletheaboveoverlappingfeaturesarenotstrongenoughtobeusedtoconcludethattheGoldfincampaignisassociatedwithFIN7,iDefenseanalystsbelievetheyaresignificantandnoteworthyandmaywelladdtonewevidencethatmaycometolightinthefutureasresearchcontinues.
Theyalsohighlightthecomplexhiddenrelationshipsthatexistbehind-the-scenesinorganizedcybercrime.
MITIGATIONToeffectivelydefendagainstthethreatsdescribedinthisreport,iDefenserecommendsblockingthefollowingaccessURIsandIPaddress:blopsadmvdrl[.
]combipovnerlvd[.
]comkiprovolswe[.
]comkiprovol[.
]comvoievnenibrinw[.
]combnrnboerxce[.
]comtejara-bank[.
]comprivat-bankau[.
]comCopyright2018AccentureSecurity.
Allrightsreserved.
20halyk-bank[.
]comwedogreatpurchases[.
]comprivatbank-ua[.
]commoneyma-r[.
]comfisrteditionps[.
]comessentialetimes[.
]comdewifal[.
]commicro-earth[.
]com5.
8.
88[.
]6446.
166.
163[.
]2435.
135.
73[.
]113Itwillalsobeusefulforincidentresponseandthreat-huntingpurposestoverifytheexistenceofanyofthefollowingartefacts:ArandomlynamedfileinC:\Programdata\Logsor%appdata%\Microsoft\Windows\StartMenu\Programs\StartupRandomlynamedPowerShellorJavaScriptfilesin%temp%Afilenameddog.
zipanddog.
jsAfilenamed~~1.
tmpin%appdata%\FuturesAservicenamewithsignificantspellingerrorsAservicenamedCheckforupdatesAPowerShellscriptnamedcheckupdate.
ps1indefaultPowerShellinstallationdirectoryAsvchost.
exeprocessthatdoesnothavewininit.
exeasparentprocessItwillalsobeusefultoverifytheexistenceofanyofthefollowinghashesonthehost:de394e9d294d2c325298eb54826ba11609d43765c2259a8df868a5fa6206ae2b9a273653364dfb143ff196d826d2bac46da6025fc7956f644b0b161781071cec211fbf34749df5e717e8b11fecb3f648dae11ed0013d58000f10919b8cba8023949b7e0f9d309e8a7ab32fa4664a7906bdaa27c6284ff95c01178db7a96121a450598c4dc7c299d0cbd92c128a56944e21a09cf81f3584a741c7167f622d6c50b3fb88a5aa791aea141bf3b4cf04535554e7f3a1a1a8857e35a45f4eb2a3317d29573b1fa60bce8e04dd2a4d554a74477b528c9d8150e4a4ab27b90a4e3337637f1aa2b2d539aa7d3dbb067417457309b10c3d00a7ceff0b7050f450968c8f6929573b1fa60bce8e04dd2a4d554a7447c38b06f871d2268972fa01725b59d7edCopyright2018AccentureSecurity.
Allrightsreserved.
21CONTACTUSJoshuaRayjoshua.
a.
ray@accenture.
comHowardMarshallhoward.
marshall@accenture.
comRobertCoderrerobert.
c.
coderre@accenture.
comJaysonJeanjayson.
jean@accenture.
comEmilyCodyemily.
a.
cody@accenture.
comABOUTACCENTUREAccentureisaleadingglobalprofessionalservicescompany,providingabroadrangeofservicesandsolutionsinstrategy,consulting,digital,technologyandoperations.
Combiningunmatchedexperienceandspecializedskillsacrossmorethan40industriesandallbusinessfunctions—underpinnedbytheworld'slargestdeliverynetwork—Accentureworksattheintersectionofbusinessandtechnologytohelpclientsimprovetheirperformanceandcreatesustainablevaluefortheirstakeholders.
Withapproximately425,000peopleservingclientsinmorethan120countries,Accenturedrivesinnovationtoimprovethewaytheworldworksandlives.
Visitusatwww.
accenture.
comABOUTACCENTURESECURITYAccentureSecurityhelpsorganizationsbuildresiliencefromtheinsideout,sotheycanconfidentlyfocusoninnovationandgrowth.
Leveragingitsglobalnetworkofcybersecuritylabs,deepindustryunderstandingacrossclientvaluechainsandservicesthatspanthesecuritylifecycle,Accentureprotectsorganization'svaluableassets,end-to-end.
Withservicesthatincludestrategyandriskmanagement,cyberdefense,digitalidentity,applicationsecurityandmanagedsecurity,Accentureenablesbusinessesaroundtheworldtodefendagainstknownsophisticatedthreats,andtheunknown.
Followus@AccentureSecureonTwitterorvisittheAccentureSecurityblog.
LEGALNOTICE&DISCLAIMER:2018Accenture.
Allrightsreserved.
Accenture,theAccenturelogo,iDefenseandothertrademarks,servicemarks,anddesignsareregisteredorunregisteredtrademarksofAccentureanditssubsidiariesintheUnitedStatesandinforeigncountries.
Alltrademarksarepropertiesoftheirrespectiveowners.
Allmaterialsareintendedfortheoriginalrecipientonly.
ThereproductionanddistributionofthismaterialisforbiddenwithoutexpresswrittenpermissionfromiDefense.
Theopinions,statements,andassessmentsinthisreportaresolelythoseoftheindividualauthor(s)anddonotconstitutelegaladvice,nordotheynecessarilyreflecttheviewsofAccenture,itssubsidiaries,oraffiliates.
Giventheinherentnatureofthreatintelligence,thecontentcontainedinthisalertisbasedoninformationgatheredandunderstoodatthetimeofitscreation.
Itissubjecttochange.
ACCENTUREPROVIDESTHEINFORMATIONONAN"AS-IS"BASISWITHOUTREPRESENTATIONORWARRANTYANDACCEPTSNOLIABILITYFORANYACTIONORFAILURETOACTTAKENINRESPONSETOTHEINFORMATIONCONTAINEDORREFERENCEDINTHISALERT.
Allrightsreserved.
1GOLDFIN:APersistentCampaignTargetingCISCountrieswithSOCKSBOTJuly26,2018CYBERADVISORYCopyright2018AccentureSecurity.
Allrightsreserved.
2SUMMARYAnumberofsecurityvendorsreportedaseriesofcyber-attacksinvolvingtheuseofamalwarefamilycalledSOCKSBOTandclaimedtobeassociatedwithCANDLEFISH(a.
k.
a.
Patchwork,DroppingElephant).
However,asdisclosedinthisreport,researchbyiDefenseanalystsshowsthatSOCKSBOTwasinfactusedbyathreatgroupinan18-month-longcampaigndubbedGoldfin,spoofingfinancialinstitutionsintheCommonwealthofIndependentStates(CIS)countriessinceasearlyasFebruary2017toasrecentlyasMay2018.
Basedonthetactics,techniquesandprocedures(TTPs)observedinthiscampaign,iDefenseassesseswithmoderateconfidencethatthereportedcampaignisunlikelytobeassociatedwithCANDLEFISH.
Inaddition,iDefenseanalystshaveidentifiedinfrastructureoverlapandtheshareduseofaPowerShellobfuscationtechniquewithFIN7.
AlthoughtheseobservationsarenotenoughtoattributetheGoldfincampaigntoFIN7,iDefenseassessesthesetobeinterestingandnoteworthyobservationsthatfurtherhighlightsthecomplexrelationshipsthatexistbehind-the-sceneinorganizedcybercrime.
HOWTOUSETHISREPORTINTENDEDAUDIENCEiDefenseisprovidinginformationaboutthereportedcampaignstothegeneraliDefensecustomerbase,withthisreportbeingintendedforsecurityoperationscenter(SOC)analystsandengineers.
Managementandexecutiveleadershipmayalsowanttousethisinformation.
HOWTOUSETHISINTELLIGENCEiDefenseisprovidingthisinformationsothatcustomersareawareofthemodusoperandiofahighlyactivethreatgroupthatistargetingfinancialinstitutionsforfinancialgain.
SOCanalystsandengineerscanusethisIA'sdetailedinformationpertainingtotheworkingsofamalwarefamilyandindicatorsofcompromise(IoCs)tocontainormitigatethediscussedthreatthroughmonitoringorblocking.
SOCanalystscanusetheinformationprovidedintheAnalysisandMitigationsectionsofthisIAforhuntingactivitiesforsystemsthatmayhavealreadybeencompromised.
AnalystsandsecurityengineerscanusetheIoCsbyaddingthemtohuntinglistsonendpointdetectionandresponse(EDR)solutionsaswellasnetwork-andhost-basedblackliststodetectanddenymalwareimplantationandcommand-and-control(C2)communication.
IntelligenceanalystsmaywanttousetheinformationprovidedinthisIAtobetterinformtheirownanalyses.
TheprovidedinformationcanalsohelpinformongoingintelligenceCopyright2018AccentureSecurity.
Allrightsreserved.
3analysesandforensicinvestigations,particularlyforcompromisediscovery,damageassessment,andattribution.
Managementandexecutiveleadershipmayusethisinformationtoassesstherisksassociatedwiththethreatdescribedhereintomakeoperationalandpolicydecisionsaccordingly.
HOWTHISINTELLIGENCEHELPSADDRESSEXISTINGORPOTENTIALTHREATSKnowledgeofthegroup'stactics,techniques,andprocedures(TTPs)shouldhelptobetterinformdetectionandresponsetoattacksbythisthreatgroup.
CAMPAIGNANALYSISiDefenseanalystscameacrosstwospear-phishingcampaignsinOctober2017involvingtheuseofamalwarefamilypubliclyknownasSOCKSBOT.
OnecampaignspoofstheHalykBank(Exhibit1)andanotherspoofsthePrivatBank(Exhibit2):Exhibit1:Spear-PhishingEmailSpoofingHalykBankCopyright2018AccentureSecurity.
Allrightsreserved.
4Exhibit2:ContentofaSpear-PhishingE-mailSpoofingPrivatBankSharedonthePublicForumdoneckforum.
comAsExhibits1and2show,bothemailscontainanidenticalmessage,evendowntothelocationoftheembeddedhyperlinks.
TheonlydifferencesaretheembeddedURLsandthesignatureoftheemailinordertoreflectthefinancialinstitutiontheattackerswerespoofing.
Thisinformationsuggestssomesortofphishingkitwaslikelyusedtogeneratethephishingemails.
Anapproximatetranslationofthee-mailspoofingHalykBankisasfollows:Subject:Notificationofopeninganaccount(HalykBankofKazakhstan)Dearcustomer,anaccountwiththePeople'sBankofKazakhstanhasbeenopenedinyourname,youcanfinddetailedinformationintheattachedfile.
Ifyoudidnotreceiveanenvelopewithaloginandpassword,thenyouneedtoregistertoaccessthePersonalArea.
Incaseoflossoflogin/password,youcanregisteranewoneinthesection"Passwordrecovery".
Ifintheprocessofworkyouhaveanyquestionsorproblems,pleasecontacttheCustomerServiceDepartmentatthecontactslistedbelow.
Ourspecialistsarealwaysreadytohelpyou.
Theembeddedmalicioushyperlinksusedintherespectiveattacksareasfollows:hxxp://halyk-bank[.
]com/dog.
ziphxxp://privatbank-ua[.
]com/dog.
zipSubsequenttechnicalanalysisoftheinfectionchaininvolvedlediDefensetouncoveran18-monthlongcampaignofspoofingbanksinCIScountries,withthemostrecentcampaignobservedonMay28,2018spoofingtheIdeaBankCJSC:Copyright2018AccentureSecurity.
Allrightsreserved.
5Exhibit3:Spear-PhishingEmailSpoofingIdeaBankCJSCTheforummemberreportsthattwospear-phishingemailswerereceived:oneclaimingtobeanotificationaboutopeninganaccountandtheotherclaimingtobeanotificationofaloanbeingtakenout.
Thecontentofthelatteremailisapproximatelytranslatedbelow:Dearclient,inyourname,aloanwasissuedtoIdeaBank,formoredetails,seetheattachedfileinwhichthefullnameandphonenumberofyourpersonalloanexpertisindicated,theamountandconditionsforrepayingtheloan.
Anenvelopewithacreditagreementwassenttoyouraddress.
Incaseyoudidnotreceivetheenvelope,youshouldcontactyourpersonalexpert.
Incaseoflossofthecontract,youcanrestoreitatthenearestbranchofthebankorrequestaduplicatethroughyourpersonalexpert.
Foranyquestionsyouareinterestedin,youcancontactyourpersonalexpertortheCustomerServiceDepartmentatthecontactslistedbelow.
Ourspecialistsarealwaysreadytohelpyou.
Yoursfaithfully,IdeaBankCJSCPhoneforcallsfromabroad:+375(17)306-33-14Intheattacksobserved,allinvolvedaphishingemailwithtwoembeddedURLsdirectingtheusertodownloadafilenameddog.
zip.
Basedonthecontentofthee-mailsandthedomainnames,thefollowingbankswerespoofedinthiscampaign:HalykBank(Kazakhstan)PrivatBank(Ukraine)IdeaBank(Belarus)Copyright2018AccentureSecurity.
Allrightsreserved.
6TejaraBank(Iran)Itisalsonoteworthythatinbothphishingkits,therearealwaystwohyperlinkslinkingtothesamemaliciousfile:oneinthebodyofthemessageandoneattheendofthee-mailinalinkcalledДоговор(whichtranslatestoContract).
Thenextsectiondetailstheinfectionchainthatfollowstheinitialdownload.
INFECTIONCHAINANALYSISThegeneralinfectionchainobservedinthiscampaignisasshowninExhibit4:Exhibit4:TheInfectionChainUsedintheSOCKSBOTCampaignSTAGE1-JAVASCRIPTDROPPERBothlinksdeliveredaZIParchivefilenameddog.
zip:hxxp://halyk-bank[.
]com/dog.
zip-211fbf34749df5e717e8b11fecb3f648hxxp://privatbank-ua[.
]com/dog.
zip-b3fb88a5aa791aea141bf3b4cf045355BothcontainaJavaScriptfilenameddog.
jswiththeMD5signatures9a273653364dfb143ff196d826d2bac4and21a09cf81f3584a741c7167f622d6c50,respectively.
TheJavaScriptfilecontainsheavilyobfuscatedcodeasExhibit5shows.
Themaliciouscodeisinfacthiddenascommentsandisdynamicallydeobfuscatedoncethescripthasbeenexecuted.
Copyright2018AccentureSecurity.
Allrightsreserved.
7Exhibit5:ObfuscatedCodeindog.
jsOncedeobfuscated(seeExhibit6),itisclearthatthecodeisdesignedtodotwothings:1.
Tolookforarunninganti-virusprocesses,suchasavp.
exe(KasperskyAntivirus).
Notethatsomevariantsofthemalwarealsosearchforekrn.
exe(ESET),cis.
exe(Comodo)andavgnt.
exe(Avira).
2.
TodropandexecuteaPowerShellscriptnamedsetup.
ps1.
ThisscriptisgeneratedbasedonBase64encodeddatastoredinvariablesnameddllDataandcode.
3.
Deletesetup.
ps1Exhibit6:DeobfuscatedCodeindog.
jsCopyright2018AccentureSecurity.
Allrightsreserved.
8STAGE2-POWERSHELLDROPPERWITHEMPIREThePowerShellscriptsetup.
ps1usedineachattackhastherespectiveMD5signatures521c81c62836a233a6e771bc3491300fand00c38b787eac602ffaed0b9372f2c443.
Thescriptisdesignedforthefollowing(seeExhibit7):1.
CreateaPowerShellscriptnamedcheckupdate.
ps1inC:\Users\Public\Downloads\(Thispathishardcodedinthemalware).
ThecontentofthisscriptisstoredinavariablenameddataandisBased64encoded2.
Createacmdletthatwould:a.
movethescriptcheckupdate.
ps1tothehomedirectoryforthecurrentPowerShellinstallb.
establishpersistencebycreatingaWindowsservicenamedCheckforupdates,setto"delay-auto"startandexecutecheckupdate.
ps13.
UseamodifiedversionofthefunctionInvoke-EventVwrBypassfromtheEmpirePost-exploitationframeworktobypassUACandexecutetheabovecmdletExhibit7:DeobfuscatedCodeinsetup.
ps1Copyright2018AccentureSecurity.
Allrightsreserved.
9STAGE3-POWERSHELLREFLECTIVELOADERSimilarly,checkupdate.
ps1usedineachattackhastherespectiveMD5signatures54e7f3a1a1a8857e35a45f4eb2a3317dand29573b1fa60bce8e04dd2a4d554a7447.
Unsurprisingly,thisscriptalsocontainsobfuscatedcode.
Themaliciouspayloadiscompressed,Base64encoded,andembeddedwithinthescript,whichissimilartoatechniqueusedinPowerSploit.
However,theobservedtechniqueappearstobeavariantofPowerSploitastheencodedpayloadisfurthersplitintoanumberofchunksthataredynamicallyloadedintoanarrayvariablenamed$OArrasshowninExhibit8:Exhibit8:ObfuscatedCodeincheckupdate.
ps1ThecodeisinfactaPowerShellreflectiveloaderscriptwithadynamic-linklibrary(DLL)binaryembeddedasBase64-encodeddata(Exhibit9).
Copyright2018AccentureSecurity.
Allrightsreserved.
10Exhibit9:DeobfuscatedCodeincheckupdate.
ps1STAGE4-SOCKSBOTThespecificSOCKSBOTsampleanalyzedinthisreporthasthefollowingproperties:Filename:socksbot.
dllMD5:90f35fd205556a04d13216c33cb0dbe3FileSize:17.
0KB(17408bytes)CompiledTimeStamp:2017-10-2717:46:05Copyright2018AccentureSecurity.
Allrightsreserved.
11Asmentionedinthelastsection,theSOCKSBOTimplantistypicallydeliveredasaBase64-encodedstringreflectivelyloaded(viatheReflectiveLoader@@YGKPAX@Zexportedfunction)inanewlystartedsvchost.
exeprocess.
Assuch,theimplantexistsonlyinmemoryandnevertouchesthedisk.
Theimplantwillfirstverifyifanyofthemutexesinthefollowingformatarepresentinordertonotruntwice:Global\%snpsGlobal\%sstpExhibit10showsanexampleofacreatedmutex.
Exhibit10:MutexCreationa321c0d8979a05bdnpsTheSOCKSBOTimplanthasthefollowingcapabilities:Enumerateprocesses(processlist)TakescreenshotsDownload,upload,write,andexecutefilesCreateandinjectintonewprocessesCommunicatetoC2viasocketsThisimplantwillcommunicatewiththedesignatedC2serverbyfirstcreatingabufferandwill,onfirstexecution,communicatetotheC2serverthatithassuccessfullyinfectedatargetbyusinga.
phpURIthatispseudo-randomlygenerated.
SOCKSBOTusestheObtainUserAgentStringAPItodeterminethedefaultuser-agentofthemachine.
AnexampleofarequesttotheC246.
166.
163[.
]243isshowninExhibit11.
Exhibit11:TraffictotheC2ServerTheC2serverortheoperatoroftheSOCKSBOTimplantcanthenrespondwithaspecificHTTPstatuscodetoperformasetofactions.
Exhibit12showsthisoptionintheimplant.
Copyright2018AccentureSecurity.
Allrightsreserved.
12Exhibit12:C2OptionsThefollowingstatuscodesaresupported:200:createandstartnewsocket202:enumerateprocessesandtakescreenshot203:performasetofactions(download,upload,execute)Exhibit13showsanexampleofpossibleactions:Exhibit13:HTTPStatusCode203ReturnOptionsTheactionsthattheoperatorcanperformareasfollows:WriteandexecutefilesCopyright2018AccentureSecurity.
Allrightsreserved.
13ExecutePowerShellscriptsExecuteaPowerShellscriptandexitSOCKSBOTcanthuswriteotherPowerShellscriptstothe%TEMP%folderandexecutethesehiddenfromtheuser.
Thisisachievedwiththefollowingcommand:%s\System32\WindowsPowerShell\v1.
0\powershell.
exe-ExecutionPolicyBypass-NoLogo-NonInteractive-NoProfile-WindowStyleHidden-File"%s"ThisallowstheattackertouploadotherobfuscatedPowerShellscriptsonthemachineand,assuch,makesSOCKSBOTapowerfulandpersistentbackdoor.
Altogether,theSOCKSBOTsamplesobservedandanalyzedinthisreportareasfollows:90f35fd205556a04d13216c33cb0dbe32a4d16ddad27c6eb60e197b6b07c2df014f71d5cb8f15f0a9943b5d709a85b7392dfd0534b080234f9536371be63e37a039d9e47e4474bee24785f8ec530769555a57741f49d6c887992353bc47846bcOnlythreedifferentC2servershavebeenobserved:5.
8.
88[.
]6446.
166.
163[.
]2435.
135.
73[.
]113INFECTIONCHAINVARIATIONSWhilethedescribedinfectionchainaboveisthemostcommoninfectionchainobserved,iDefenseanalystshavealsoobservedanumberofdifferentvariationsinrelatedcampaigns:1.
SOCKSBOTDropper2.
dog.
jsObfuscation3.
RandomPowerShellScriptNames4.
ReflectiveloadingPowerShellScriptObfuscationVARIATION1:SOCKSBOTDROPPERAsidefromthePowerShellreflectiveloader,iDefenseanalystshavealsoidentifiedadropperexecutablebinarywiththefollowingpropertiesthatwasusedtoreflectivelyloadSOCKSBOTintoachosenprocess(usuallysvchost.
exe):Filename:MD5:14f71d5cb8f15f0a9943b5d709a85b73FileSize:23.
6KB(24200bytes)CompiledTimeStamp:2017-02-0113:40:14Copyright2018AccentureSecurity.
Allrightsreserved.
14Signer:MagnumTravelClub(Serial:1F8A3E60EEC1E3AA63B39BDD26E110FB)Notethatthebinarywassignedwithacode-signingcertificatepurportedlyfromanorganizationcalledMagnumTravelClub.
ThisdropperwillcreateacopyofitselfinC:\Programdata\Logsasahiddensystemfileandwillthendeletetheoriginalfile.
Anothercopywillbecreatedin%appdata%\Microsoft\Windows\StartMenu\Programs\Startupwiththesamepropertiestoensurepersistence.
Finally,thedropperwillstartanewsvchost.
exeprocessinasuspendedstateandconsequentlyreflectivelyload(andinject)theSOCKSBOTimplantintotheprocess.
AnadditionalWindowsservicemaybecreatedforpersistenceaswell,whichisdonebyfirstenumeratingexistinglegitimateservicesandcreatinganewservicespoofingoneoftheserviceswithanalmostidenticalname.
Inthiscase,anewservicenamedXindowsErrorReportingServicewascreated(seeExhibit14).
Exhibit14:ServiceCreationWhilethisdropperdoesindeedloadtheSOCKSBOTimplant,allotheriterationsorcampaignshaveusedscripts,inparticularJavaScriptandPowerShell,toreflectivelyloadtheSOCKSBOTpayload.
VARIATION2:DOG.
JSOBFUSCATIONWhilemostdog.
jssamplesobservedwereobfuscatedasreportedintheinfectionchainsection,therearealsoversionsthatwerenotobfuscatedatallorwereobfuscatedusingadifferentobfuscationtechniquesuchasdifferentcharacterencoding(Exhibit15):Copyright2018AccentureSecurity.
Allrightsreserved.
15Exhibit15:ADifferentObfuscationTechniqueUsedindog.
jsOnceexecuted,thissample(MD5:b01cf8f375bc0aff2cfe3dc1b4c1823c)willdeobfuscateandgenerateanewfilecalled~~1.
tmpin%appdata%\Futures.
Thescriptisdeletedafterexecution.
VARIATION3:RANDOMPOWERSHELLSCRIPTNAMESCertainvariantsofdog.
jsalsohaveanewfunctiontorandomlygeneratefilenamesforthesecond-andthird-stagePowerShellscripts:functionmakerndps1(){vartext="";varpossible="ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789";for(vari=0;i<5;i++)text+=possible.
charAt(Math.
floor(Math.
random()*possible.
length));returntext+'.
ps1';}4.
REFLECTIVELOADINGPOWERSHELLSCRIPTOBFUSCATIONAsidefromchangestothedog.
jsobfuscation,iDefenseanalystshavealsofoundadifferentobfuscationtechniqueusedtoobscurethecodeinthereflectiveloadingscript(seeExhibit16):Copyright2018AccentureSecurity.
Allrightsreserved.
16Exhibit16:DifferentObfuscationTechniqueUsedintheReflectiveLoadingPowerShellScriptThesampleconcernedhastheMD5signaturec38b06f871d2268972fa01725b59d7ed.
Notealsothattheexecutioncommandusedforpersistenceisagainencoded(seeExhibit17):Exhibit17:ObfuscatedExecutionCommandinCheckforupdateServiceUsedforPersistenceATTRIBUTIONBasedonthepreferencetospooffinancialinstitutionsinCIScountries,thenetworkinfrastructureusedandtheobservedtargeting,iDefenseassesseswithmoderateconfidencethatthereportedcampaignisunlikelytobeassociatedwithCANDLEFISH.
Furthermore,iDefenseanalystshaveidentifiedanumberofinterestingandnoteworthyoverlapswithFIN7:IdenticalWHOISinformationusedindomainsassociatedwiththeGoldfincampaignandFIN7,aswellasnetworkhostingoverlapShareduseofaPowerShellobfuscationtechniqueCopyright2018AccentureSecurity.
Allrightsreserved.
17OVERLAP1:IDENTICALWHOISINFORMATIONANDNETWORKHOSTINGOVERLAPResearchshowsthatthedomainsprivat-bankau[.
]com,halyk-bank[.
]com,andtejara-bank[.
]comallhavetheorganizationnameGoldfinLLC,anear-identicalregistrantaddress(seebelow),anda@rambler.
rue-mailaddressusedastheregistrante-mailaddress.
RegistrantOrganization:GoldfinLLCRegistrantStreet:ulArbat5RegistrantCity:MoscowRegistrantState/Province:MoscowRegistrantPostalCode:115343RegistrantCountry:RUThispatternoverlapswithtwootherdomains-despanabrandfood[.
]comandsilverdiners[.
]com(seeExhibit18)-thatiDefensecurrentassesseswithlowconfidencearelikelyassociatedwithFIN7duetothefollowing:1.
SpoofingrestaurantchainsDespaaBrandFoods(legitimatedomaindespanabrandfoods.
com)andSilverDiner(legitimatedomainsilverdiners.
com),aknowntechniqueassociatedwithFIN7.
Thewebsitedespanabrandfood[.
]comremainsindexedbyGoogle(seeExhibit19)2.
PreviouslyresolvedtotheIPaddress192.
99.
14[.
]211,whichwasreportedbyTrustwaveandtr1dxasassociatedwithFIN7towardslate2016andearly2017.
Inaddition,likemanydomainsassociatedwithFIN7aswellastheCarbanakgroup,manyofthedomainsusedintheGoldfincampaignwerealsoparkedat31.
41.
41[.
]41whichisassociatedwithCISHosting.
However,iDefenseanalystsareawarebothhostsarelikelytobeshared/parkinghostshencetheassociationwithFIN7basedonthisoverlapisoflowconfidence.
Exhibit18:WHOISInformationSimilaritiesbetweenDomainsUsedintheGoldfinCampaignandThoseAssociatedwithFIN7Copyright2018AccentureSecurity.
Allrightsreserved.
18Exhibit19:Spoofingdomaindespanabrandfood[.
]comremainsindexedbyGoogleatthetimeofwriting,showingtheattacker'sintentiontoplagiarisethelegitimatewebsitedespanabrandfoods[.
]comExhibit20illustratestheoverlappinginfrastructurebetweentheGoldfincampaignandinfrastructureassociatedwithFIN7:Exhibit20:MaltegoGraphShowingtheOverlappingInfrastructurebetweenGoldfinCampaignandFIN7Copyright2018AccentureSecurity.
Allrightsreserved.
19OVERLAP2:SHAREDUSEOFAPOWERSHELLOBFUSCATIONTECHNIQUEAsmentionedintheinfectionchainanalysis,thecodeembeddedwithinthethird-stagePowerShellscriptcheckupdate.
ps1isobfuscatedusingatechniquesimilartothatofPowerSploit.
However,thetechniqueusedappearstobeanichevariantastheembeddedpayloadisfurthersplitintochunksanddynamicallyaddedtoanarrayvariablenamed$OArr.
Interestingly,iDefenseanalystshavepreviouslyobservedthisobfuscationusedinaPowerShellcomponent(MD5:87327b4045b9d004697aec7e7a4b9ba8)thatwasdroppedbyaHALFBAKEDsample(MD5:31fcf8a4ec7a4c693eda9336321cf401)backinAugust2017.
HALFBAKEDisamalwarefamilyassociatedwithFIN7.
Exhibit21:SimilarPowerShellObfuscationTechniqueUsedbetweentheGoldfinCampaignandFIN7WhiletheaboveoverlappingfeaturesarenotstrongenoughtobeusedtoconcludethattheGoldfincampaignisassociatedwithFIN7,iDefenseanalystsbelievetheyaresignificantandnoteworthyandmaywelladdtonewevidencethatmaycometolightinthefutureasresearchcontinues.
Theyalsohighlightthecomplexhiddenrelationshipsthatexistbehind-the-scenesinorganizedcybercrime.
MITIGATIONToeffectivelydefendagainstthethreatsdescribedinthisreport,iDefenserecommendsblockingthefollowingaccessURIsandIPaddress:blopsadmvdrl[.
]combipovnerlvd[.
]comkiprovolswe[.
]comkiprovol[.
]comvoievnenibrinw[.
]combnrnboerxce[.
]comtejara-bank[.
]comprivat-bankau[.
]comCopyright2018AccentureSecurity.
Allrightsreserved.
20halyk-bank[.
]comwedogreatpurchases[.
]comprivatbank-ua[.
]commoneyma-r[.
]comfisrteditionps[.
]comessentialetimes[.
]comdewifal[.
]commicro-earth[.
]com5.
8.
88[.
]6446.
166.
163[.
]2435.
135.
73[.
]113Itwillalsobeusefulforincidentresponseandthreat-huntingpurposestoverifytheexistenceofanyofthefollowingartefacts:ArandomlynamedfileinC:\Programdata\Logsor%appdata%\Microsoft\Windows\StartMenu\Programs\StartupRandomlynamedPowerShellorJavaScriptfilesin%temp%Afilenameddog.
zipanddog.
jsAfilenamed~~1.
tmpin%appdata%\FuturesAservicenamewithsignificantspellingerrorsAservicenamedCheckforupdatesAPowerShellscriptnamedcheckupdate.
ps1indefaultPowerShellinstallationdirectoryAsvchost.
exeprocessthatdoesnothavewininit.
exeasparentprocessItwillalsobeusefultoverifytheexistenceofanyofthefollowinghashesonthehost:de394e9d294d2c325298eb54826ba11609d43765c2259a8df868a5fa6206ae2b9a273653364dfb143ff196d826d2bac46da6025fc7956f644b0b161781071cec211fbf34749df5e717e8b11fecb3f648dae11ed0013d58000f10919b8cba8023949b7e0f9d309e8a7ab32fa4664a7906bdaa27c6284ff95c01178db7a96121a450598c4dc7c299d0cbd92c128a56944e21a09cf81f3584a741c7167f622d6c50b3fb88a5aa791aea141bf3b4cf04535554e7f3a1a1a8857e35a45f4eb2a3317d29573b1fa60bce8e04dd2a4d554a74477b528c9d8150e4a4ab27b90a4e3337637f1aa2b2d539aa7d3dbb067417457309b10c3d00a7ceff0b7050f450968c8f6929573b1fa60bce8e04dd2a4d554a7447c38b06f871d2268972fa01725b59d7edCopyright2018AccentureSecurity.
Allrightsreserved.
21CONTACTUSJoshuaRayjoshua.
a.
ray@accenture.
comHowardMarshallhoward.
marshall@accenture.
comRobertCoderrerobert.
c.
coderre@accenture.
comJaysonJeanjayson.
jean@accenture.
comEmilyCodyemily.
a.
cody@accenture.
comABOUTACCENTUREAccentureisaleadingglobalprofessionalservicescompany,providingabroadrangeofservicesandsolutionsinstrategy,consulting,digital,technologyandoperations.
Combiningunmatchedexperienceandspecializedskillsacrossmorethan40industriesandallbusinessfunctions—underpinnedbytheworld'slargestdeliverynetwork—Accentureworksattheintersectionofbusinessandtechnologytohelpclientsimprovetheirperformanceandcreatesustainablevaluefortheirstakeholders.
Withapproximately425,000peopleservingclientsinmorethan120countries,Accenturedrivesinnovationtoimprovethewaytheworldworksandlives.
Visitusatwww.
accenture.
comABOUTACCENTURESECURITYAccentureSecurityhelpsorganizationsbuildresiliencefromtheinsideout,sotheycanconfidentlyfocusoninnovationandgrowth.
Leveragingitsglobalnetworkofcybersecuritylabs,deepindustryunderstandingacrossclientvaluechainsandservicesthatspanthesecuritylifecycle,Accentureprotectsorganization'svaluableassets,end-to-end.
Withservicesthatincludestrategyandriskmanagement,cyberdefense,digitalidentity,applicationsecurityandmanagedsecurity,Accentureenablesbusinessesaroundtheworldtodefendagainstknownsophisticatedthreats,andtheunknown.
Followus@AccentureSecureonTwitterorvisittheAccentureSecurityblog.
LEGALNOTICE&DISCLAIMER:2018Accenture.
Allrightsreserved.
Accenture,theAccenturelogo,iDefenseandothertrademarks,servicemarks,anddesignsareregisteredorunregisteredtrademarksofAccentureanditssubsidiariesintheUnitedStatesandinforeigncountries.
Alltrademarksarepropertiesoftheirrespectiveowners.
Allmaterialsareintendedfortheoriginalrecipientonly.
ThereproductionanddistributionofthismaterialisforbiddenwithoutexpresswrittenpermissionfromiDefense.
Theopinions,statements,andassessmentsinthisreportaresolelythoseoftheindividualauthor(s)anddonotconstitutelegaladvice,nordotheynecessarilyreflecttheviewsofAccenture,itssubsidiaries,oraffiliates.
Giventheinherentnatureofthreatintelligence,thecontentcontainedinthisalertisbasedoninformationgatheredandunderstoodatthetimeofitscreation.
Itissubjecttochange.
ACCENTUREPROVIDESTHEINFORMATIONONAN"AS-IS"BASISWITHOUTREPRESENTATIONORWARRANTYANDACCEPTSNOLIABILITYFORANYACTIONORFAILURETOACTTAKENINRESPONSETOTHEINFORMATIONCONTAINEDORREFERENCEDINTHISALERT.
- Tejara166dd.com相关文档
- BioMed166dd.com
- fs166dd.com
- 填土166dd.com
- KENYA166dd.com
- 集合166dd.com
- Association166dd.com
百星数据(60元/月,600元/年)日本/韩国/香港cn2 gia云服务器,2核2G/40G/5M带宽
百星数据(baixidc),2012年开始运作至今,主要提供境外自营云服务器和独立服务器出租业务,根据网络线路的不同划分为:美国cera 9929、美国cn2 gia、香港cn2 gia、韩国cn2 gia、日本cn2 gia等云服务器及物理服务器业务。目前,百星数据 推出的日本、韩国、香港cn2 gia云服务器,2核2G/40G/5M带宽低至60元/月,600元/年。百星数据优惠码:优惠码:30...

GreenCloudVPS$20/年多国机房可选,1核@Ryzen 3950x/1GB内存/30GB NVMe/10Gbps端口月流量2TB
GreencloudVPS此次在四个机房都上线10Gbps大带宽VPS,并且全部采用AMD处理器,其中美国芝加哥机房采用Ryzen 3950x处理器,新加坡、荷兰阿姆斯特丹、美国杰克逊维尔机房采用Ryzen 3960x处理器,全部都是RAID-1 NVMe硬盘、DDR4 2666Mhz内存,GreenCloudVPS本次促销的便宜VPS最低仅需20美元/年,支持支付宝、银联和paypal。Gree...

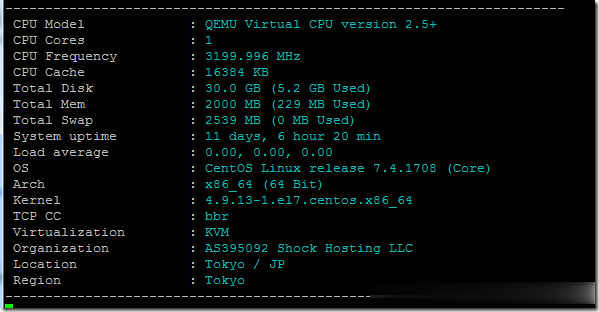
ShockHosting日本机房VPS测试点评
这个月11号ShockHosting发了个新上日本东京机房的邮件,并且表示其他机房可以申请转移到日本,刚好赵容手里有个美国的也没数据就发工单申请新开了一个,这里做个简单的测试,方便大家参考。ShockHosting成立于2013年,目前提供的VPS主机可以选择11个数据中心,包括美国洛杉矶、芝加哥、达拉斯、杰克逊维尔、新泽西、澳大利亚、新加坡、日本、荷兰和英国等。官方网站:https://shoc...
166dd.com为你推荐
-
留学生认证留学生前阶段双认证认证什么内容?www.jjwxc.net有那个网站可以看书?陈嘉垣马德钟狼吻案事件是怎么回事rawtools闪迪32Gsd卡,无法格式化,显示只有30M,并且是raw格式。如何恢复?www.5any.comwww.qbo5.com 这个网站要安装播放器555sss.comms真的是500万像素?javlibrary.com大家有没有在线图书馆WWW。QUESTIA。COM的免费帐号机器蜘蛛挑战或是生存Boss是一只巨型机器蜘蛛的第一人称射击游戏叫什么www.mfav.org海关编码在线查询http://www.ccpit.org.c175qq.com查询QQ登录地址