programuserinit
userinit 时间:2021-04-04 阅读:()
WhyPCsAreFragileandWhatWeCanDoAboutIt:AStudyofWindowsRegistryProblemsArchanaGanapathiYi-MinWangNiLaoJi-RongWenApril5,2004TechnicalReportMSR-TR-2004-25MicrosoftResearchMicrosoftCorporationOneMicrosoftWayRedmond,WA98052ThisreportisanextendedversionofthepapertoappearinProc.
IEEEInternationalConferenceonDependableSystemsandNetworks(DSN),June2004.
2004IEEE.
Personaluseofthismaterialispermitted.
However,permissiontoreprint/republishthismaterialforadvertisingorpromotionalpurposesorforcreatingnewcollectiveworksforresaleorredistributiontoserversorlists,ortoreuseanycopyrightedcomponentofthisworkinotherworksmustbeobtainedfromtheIEEE.
WhyPCsAreFragileandWhatWeCanDoAboutIt:AStudyofWindowsRegistryProblemsArchanaGanapathiYi-MinWangNiLaoandJi-RongWenUniversityofCaliforniaMicrosoftResearchMicrosoftResearchBerkeley,CARedmond,WABeijing,ChinaAbstractSoftwareconfigurationproblemsareamajorsourceoffailuresincomputersystems.
Inthispaper,wepresentanewframeworkforcategorizingconfigurationproblems,andapplythiscategorizationtoactualWindowsRegistry-relatedproblemsobtainedfromvarioussources.
Althoughinfrequent,Registry-relatedproblemsaredifficulttodiagnoseandrepair.
Consequently,theyhavebeenasourceofmajorfrustrationamongPCusers.
WeclassifyproblemsbasedontheirmanifestationandthescopeofimpacttogainusefulinsightsintohowproblemsaffectusersandwhyPCsarefragile.
WethendescribetechniquestoidentifyandeliminatesuchRegistryfailures.
Weproposehealthpredicatemonitoringfordetectingknownproblems,faultinjectionforimprovingapplicationrobustness,andaccessprotectionmechanismsforpreventingfragilityproblems.
1.
IntroductionWindows-basedpersonalcomputers(PCs)offeraplatformforinterestingandcomplexsoftwareinteractions.
However,undisciplinedusesandsharingofpersistentconfigurationdatabyWindowsprogramshavemadePCsmorevulnerabletofragility.
Inparticular,theWindowsRegistrystoreslargequantitiesofcomplex,undocumentedandunprotectedconfigurationdata,makingitthesinglemostvulnerablecomponentoftheWindowsoperatingsystem.
UnderstandingandundoingRegistrydamageisanon-trivialtasktotheaverageuser.
Theproblemisasburdensometosystemandapplicationdevelopersasitistousers.
Inthispaper,wecharacterizehowRegistryproblemsimpactusersandwhatcanbedonetoalleviateandpreventfutureoccurrences.
Webaseouranalysisontwosetsofreal-worldfailuredata.
Thefirstsetconsistsof100commonRegistryproblemsfromadatabaseofProductSupportServices(PSS)emaillogs.
Theseconddatasetcomprises100problemsencounteredbyourcolleaguesandproblemspostedonvariousWebforums.
Throughanalysisof200cases,wedevelopacategorizationframeworkthatcoverstwoorthogonalaxes.
Thefirstdimensionusesproblemmanifestationandscopeofimpacttounderstandtheuser'sviewofPCfragility.
Theseconddimensionsuggestsmonitoringtechniques,faultinjectiontactics,andaccessprotectionmechanismstoalleviatePCfragility.
Theremainderofthispaperisorganizedasfollows.
Section2providesanoverviewoftheRegistry.
Section3describestwofragilitydatasets.
Sections4categorizesproblemsbasedonmanifestationandimpact.
Section5discussesmitigationtechniques.
Section6surveysrelatedworkintheareasoffailurecategorization,software-relatedproblemdetection,andRegistrycheckingtools.
Section7concludes.
2.
RegistryOverviewTheWindowsRegistryprovidesahierarchical,sharedrepositoryfornamedandtypedconfigurationdata.
Thisdataisaccessedbytheoperatingsystemaswellasapplicationsoftware.
TheRegistryisdividedintoRegistryhivesthatcontainsetsofkeys,sub-keysanditemspertainingtocomponentssuchasSystem,SoftwareandHardware.
Registryhivesdistinguishbetweenvariousper-userandsystem-widesettings.
EachRegistrykeyinahivecanbeviewedasadirectorythatoptionallycontainssub-keysandRegistryitemsthatpossesstheactualconfigurationinformationastypeddata.
EachRegistryitemisaccessedbynavigatingthroughadesignatedpathofkeysandsub-keys.
Figure1showsRegistryconfigurationsintheHKEY_LOCAL_MACHINE\Software\Adobe\AcrobatReader\5.
0\AdobeViewerRegistrykey.
3.
FragilityDataSetsWecollecteddatausingtwomethods.
First,weusedtext-miningtoolstoextractdatafromPSSlogs.
Aslogscontainlimitedrootcauseanalysisinformation,ourseconddatasetcomprisedproblemsencounteredbyourcolleaguesandWebforumsusers.
WeusedtheStriderTroubleshooter[13]todiagnose/reproducetheseproblems.
Figure1.
SampleconfigurationsintheWindowsRegistry.
TheleftwindowshowsRegistryhivesandkeys.
TherightwindowshowsRegistryitemswithtypeddata.
3.
1.
Text-MinedDataSet(TMDS)fromPSSWeanalyzedproblemsreportedbyemailstoaPSSorganizationduringseveralyearsspanning3/20/1997to5/20/2003.
PSSisatechnicalsupportorganizationthathelpscustomersresolveproblemsbymaintainingaknowledgebaseofknownproblemsandsolutions.
SincetheseemailcaselogsdonotexplicitlyidentifyRegistry-relatedproblems,weusedtext-miningtoautomaticallyextractpotentiallyrelevantcasesandthenmanuallyeliminatedcaseswithinsufficientinformation.
Atotalofabout2,400,000problemswerereportedduringthistimeperiod,ofwhich101,900(4.
4%)containedreferencestoatotalofapproximately143,157Registrykeys/items.
ThesereferencessimplymeantaRegistryentrywaspresentintheproblemreport,notnecessarilythatitwasattributedasthecausefortheproblemitself.
Only5,266uniqueentrieswereidentifiedfromthesereportsasmultiplereferencestothesameRegistryentrycouldbepresentacrossvariousproblems.
Weonlychoseproblemswithsufficientinformationforanalysis,particularlythepost-mortemsummarydescriptionsprovidedbythePSSengineers.
Weextracted10,405summary-containingproblems.
Figure2.
Zipf-likedistributionof100mostcommonproblemsfromTMDS.
NotethatbothXandYaxesfollowalogarithmicscale.
WegroupedmultiplerepetitionsofproblemsbyrootcauseRegistryentry(asidentifiedbytext-miningtools)andselected100mostcommonproblemstoanalyze.
ThedataapproximatelyfollowedaZipfdistribution[7].
AsshownbyFigure2,mostproblemswereinfrequentwhileasmallnumberofproblemsimpactedasignificantnumberofusers.
Thenumberofoccurrencesofeachselectedproblemrangedfrom1,947to5.
Thetop100casesrepresentapproximately5,379(morethanhalf)of10,405problems.
3.
2.
Strider-VerifiedDataSet(SVDS)TofurtherunderstandRegistryfragilityproblemsandexperiencetheirmanifestation,wecollected,reproduced,andresolvedRegistryproblemsusingtheStriderTroubleshooter[13,14].
Thistoolperformsa"diff"operationoftwoRegistrysnapshots(e.
g.
pre-problemgoodstateandpost-manifestationbadstate),andintersectsitwithatraceofoperationsleadingtoproblemmanifestation.
Finally,itprovidesareportthatranksthepotentialcausalentriesbasedontheirlikelinessofbeingtheactualrootcause.
Wecollected100problemsfromourcolleaguesaswellasahelpdeskorganizationandWebforumssuchasTweakXP.
com1andRegistryGuideforWindows2.
WespecificallyfocusedonproblemsrelatingtoWindowsXPSP1.
Forproblemswithknownrootcauses,wereproducedthemis-configurationtostudythesymptoms.
Forproblemswithoutknownsolutions,weusedtheStriderTroubleshootertoidentifytherootcausesandthenmanuallyverifiedtherepairs.
Astherewasnorecordofthenumberofpeopleencounteringandresolvingeachproblem,wecannotreportfrequency.
4.
WhyPCsAreFragile4.
1.
ProblemManifestationPCfragilitymanifestationonusers'machinescanbeclassifiedintosevendistinctcategories,enumeratedbelow.
Incaseswhereaproblemhadseveralsymptomsthatmappedsimultaneouslyintomorethanonecategory,weselectedthemostrepresentative/impactingsymptom.
(1)Unstable/unusablesystem–CertainRegistrymis-configurationscauseseverelossofcriticalfunctionalityand/oropenavenuesforthesystemtobecompromised.
Forexample,changingthedataofHKEY_LOCAL_MACHINE\software\Microsoft\windowsNT\currentversion\Winlogon\Userinitfrom"C:\WINDOWS\system32\userinit.
exe,"to1http://www.
tweakxp.
com2http://www.
winguides.
com/forums"C:\WINDOWS\system32\userinit.
exe;"preventsuserlogintothemachine,makingthesystemunusable.
(2)Cannotperformafunctionoraction–Sometimes,auserisunabletoperformadesiredtasksuchassendinge-mailorinvokingaprogram.
Forexample,ifHKEY_CLASSES_ROOT\.
mp3\PerceivedTypehasdatavalueotherthan"audio"(e.
g.
"text"),"PlayAll"inthe"MyMusic"folderdoesnotplay.
mp3files.
(3)Unanticipatedresponse–Usersareoftenconfusedandfrustratedwhentheiractioncausesanewunanticipatedresponse.
Forexample,doubleclickingafolderopensasearch-resultswindowinsteadofthefolderitself,whentheHKEY_CLASSES_ROOT\Directory\shell\(Default)Registryitem'sdataisempty.
(4)Unanticipatedside-effect–Someside-effectsarecausedbybadprogramdesign.
Moreover,whatisacceptablewithinanapplication'sspecificationcanbeanunpleasantside-effecttotheuser.
Forexample,installinganewCDburnerrenamesthe"A"driveto"H"driveandproducesanerrorwhenausertypes"A:\"fromStartmenuRuntoopenthefloppydrive.
(5)Cannotlocateuserinterfacetoperformatask–Sometimes,auserinterfaceisconcealedbelowseverallevelsofmenus.
Forexample,InternetExplorerasksifitshouldsaveauser'spasswordtoaparticularwebsite.
Oncetheuserselectsthe"Don'toffertorememberanymorepasswords"optioninthepop-updialogbox,itisdifficultfortheusertorestoreInternetExplorer'ssettingssothatitpromptstorememberpasswords.
(6)Userinterfacedisappearsbutfunctionalityispreserved–Insomecases,theuserinterfaceforataskiseitherabsentortainted.
However,thistaskcanbeexecutedbyothermeanssuchascommand-lineinvocation.
Forexample,ausermaybeunabletoaccessInternetOptionsfromInternetExplorer.
However,thesameconfigurationsetisaccessiblefromtheControlPanel.
Similarly,ControlPanelNetworkConnectionsmayrevealnothingifaUI-relatedkeyisdeleted,butallnetworkconnectionsremainintact.
(7)Programadaptationorautomationisperformedinanunexpectedmanner–Automationdecisionsmadebysomeprogramscanbeunintuitivetotheuser.
Forexample,onsomelaptops,MicrosoftPowerPointfailstodisplayaslideshowwhenitincorrectlyassumes,basedonRegistryinformation,thatthereexistsasecondmonitortowhichitshoulddirectthevideooutput.
ThedatainFigure3(below)revealsthatuserinabilitytoperformafunction/actionwasthedominantformofreportedproblems.
Amongremainingcategories,"Unanticipatedresponse"hasthehighestcasecount.
Intuitively,suchproblemsaremorefrustratingtousersthancustomization-relatednuisancesanduserinterfaceissues.
Finally,thecategoryof"Unstable/unusablesystem"contributesanon-trivialamountofproblems;eachproblemneedstobecarefullyinvestigatedastheycauseahighdegreeofuserfrustration.
ProblemManifestationTMDSSVDSUnstable/unusablesystem2(143)6Cannotperformfunction/action62(4212)32Unanticipatedresponse18(676)23Unanticipatedside-effect9(196)14CannotlocateUI1(16)9UIdisappears,functionalityok3(65)12Unexpectedprogramadaptation5(71)4Figure3.
Manifestationcategorizationforthetwodatasets.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
4.
2.
ScopeofImpactThiscategorycapturestheimpactofRegistryproblemsonamachine'sfunctionality:(1)ImpactScopeI–Theimpactcanbesystem-wideoraffectingonlyaparticularuser.
(2)ImpactScopeII–Aproblemcanimpactasingleapplication(e.
g.
,InternetExplorer),multipleapplications(e.
g.
,allMicrosoftOfficeapplications)ortheentiresystem.
Thisinformationenablesustoprovidefeedbacktoappropriatedevelopmentgroups(OSorapplications)onpotentialtribulationstoconsider.
ImpactScopeITMDSSVDSSystem-wide71(4312)59User-specific29(1067)41ImpactScopeIISingleApplication28(994)48MultipleApplications31(3081)16SystemLevel41(1304)36Figure4.
ImpactscopeofTMDSandSVDSproblems.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
ThecategorizationpresentedinFigure4suggeststhatreportedsystem-wideproblemsaremorecommonthanuser-specificproblems.
Thisobservationimpliesthatmoremis-configurationsarecausedbyapplicationprogramsorOScomponentsincorrectlyupdatingRegistryentriesand/ornon-robustlyreadingRegistrydata,thanuseractionsinappropriatelymodifyingsettings.
Theapproximateevendistributionofproblemsbetweenapplication-levelandsystem-levelimpactsuggeststhattacklingPCfragilityproblemsrequirescoordinatedeffortsfrombothOSandapplicationdevelopers.
5.
WhatWeCanDoAboutPCFragilityWeidentifythreeareasoffocustoaddresstheissueofPCfragility.
ForexistingapplicationsrunningonareleasedOSplatform,amonitoringtoolcandetectknownbadchangestoRegistryentries.
Forapplicationsthatareunderdevelopment,afaultinjectiontoolcanhelpverifyimmunitytoknownproblems.
Fordesigninganewoperatingsystem,wedescribeandevaluateaccessprotectionmechanismsthataremosteffective,accordingtoourfragilitydata.
Figure5summarizesthecategorizationoftext-minedandstrider-verifieddatabasedonmonitoring,faultinjectionandaccessprotectionaxes.
HowtoMonitorTMDSSVDSKnownbadentry22(2746)35Potentialbad+symptommatch71(2390)60Can'thelp7(243)5WhattoInjectBaddata22(832)24Datalegalbutconsideredbad39(933)41Itemexists3(278)9Itemmissing5(136)10Keyexists12(2454)7Keymissing5(146)9Badkey8(263)0Badsub-key5(325)0Typecorrupt1(12)0HowtoProtectOSlockdown9(296)20Checkrulesuponmodification18(659)14CopyonWrite3(118)1Logchanges56(1757)58Can'thelp14(2549)2Ignore0(0)5Figure5.
NumberofTMDSandSVDSproblemspercategoryasdescribedinSections5.
1to5.
3.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
5.
1.
MonitoringTechniquesDuringtheinterimperiodbetweenRegistry-problemdiscoveryandconsequentrepairbydevelopers,PCmonitoringisessential.
MaintainingaknowledgebaseofknownbadpredicatesfrompastRegistrytroubleshootsprovidesaninvaluableresourceforproblemdiagnosisandprevention.
Monitoringcanbeperformedeitherperiodicallyorbyregisteringtoreceivechangenotifications.
Suchprotectivemeasurescanpreventproblemsfromcausingeventualfailuresandeasetroubleshootingafterfailureoccurrence.
Ingeneral,aRegistryentry'spresenceorabsenceofdatacanpositivelyidentifyproblems.
Forexample,considertheSirCamviruschangingthedataoftheHKEY_CLASSES_ROOT\exefile\shell\open\command\(Default)Registryitemfrom"%1"%*toC:\recycled\sirc32.
exe"%1"%*.
Thischangewouldgeneratea"FileNotFound"errorwhentheuserdouble-clicksa.
exefile.
ThepresenceofdataC:\recycled\sirc32.
exe"%1"%*canbemonitoredtopositivelyidentifytheproblem.
Similarly,theabsenceofHKEY_CLASSES_ROOT\CLSID\{00021401-0000-0000-C000-000000000046}\shellex\MayChangeDefaultMenucanbemonitoredtopositivelyidentifytheproblemofdysfunctionalshortcutsthatfailtolaunchanapplicationwhentheuserdoubleclicksthem.
ThebreakdowninFigure5showsthatmanyoftheproblemswestudiedcanbeimmediatelyflaggedupondetectionofknownbadRegistryentries.
Inothercases,thesoftwareusedbytheuserandtheunderlyingenvironmentdictateifthedataofaRegistryentryisproblematic.
Furthermore,manyconfigurationsarepurelyforpurposesofcustomization;anunusualconfigurationinoneuser'sperspectivemaynotnecessarilybeaproblem,ratheravalidchoicemadebyadifferentuserorthesameuseratanearliertime.
Insuchcases,themonitormustrecordthe"potentiallybad"Registryentryandawaitusercomplainttoperformsymptom-basedtroubleshooting.
Itisimportanttonotwarntheuserupondetectingeverysuchknown"potentiallybad"entryasnumerousfalsepositivescaneventuallyleadtheusertodisablethemonitoringtool.
Forexample,ifHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\InternetSettings\EnableAutodialissetto1,someversionsofWindowsMediaPlayer's"OpenURL"functionwillfaileveniftheuserhasInternetconnectivity.
However,someusersdonotusethisapplicationandmaysetEnableAutodialto1forpreferredfunctionalityofotherInternetapplications.
Themonitorisunsurewhethertheuserintendedtomakethischange,asitisavalidcustomization.
Alternately,themonitorcanbefullypreparedtopointtotheentryastherootcauseifandwhentheusercomplainswithasymptommatchingpreviouslyreportedoccurrences.
Policy-relatedsettingsalsobelongtothe"Potentialbadentry+symptommatching"categoryandaccountforasignificantpercentageofthecaseswestudied.
Inacorporateenvironment,policy-relatedRegistryentriesallowtheITorganizationtodisablecertainfunctionsonemployees'desktopstoincreasestabilityandsimplifymaintenance.
Manysuchsettingshavecausedusercomplaintsastheycouldnotperformthefunctionsthatwerenormallyavailabletothemoutsidethecorporateenvironment.
Obviously,weshouldnotwarnallemployeesaboutpotentialproblemswhentheITorganizationimplementsanewpolicybecausemostpeoplemayneverusethedisabledfunction.
Nevertheless,ourmonitorcanquicklypointtotherootcausewhenauseractuallycomplainswithamatchingsymptom.
Wenotethatasmallpercentageofproblemsarecategorizedas"Can'thelp".
Theseproblemsprimarilyconsistofhighlycase-specificdatacorruptionthataredifficulttomonitorandgenerallyvalidsettingsthatcauseproblemsonlyinspecificsituations.
Forexample,anapplicationwindowmaynotdisplayproperlyifwindowposition-relatedRegistrydataiscorrupted;abrowserproxysettingmaycauseconfusingnetworkconnectionproblemsiftheuserinadvertentlyusesitinanenvironmentwherethespecifiedproxycannotbefound.
Webelieveourmonitoringmethodologyisfeasibleasseveralrule-basedRegistrycheckingtoolsarealreadycommerciallyavailable.
WesurveysomeofthesetoolsintheRelatedWorksection.
Ingeneral,thesetoolsperformcheckinguponuserdemand,insteadofcontinuouslymonitoringtheRegistryinthebackground.
Furthermore,theydonotdistinguishknownbadandpotentialbadentries;theyaskuserstodecidebetweenfixingandignoringeverydetecteddubiousentry.
Moreover,theydonothaveadynamicruleupdatemechanismsimilartoanti-virussignatureupdateandauserinterfaceforspecifyingsymptoms.
5.
2.
FaultInjectionApproachFaultinjectionisausefultaskthattestsaprogram'sfaulthandlingcapability.
ForapplicationsorOScomponentsthatrunonplatformswithknownfragilityproblems,wecantestrobustnessbyinjectingknownproblemsduringdevelopment.
SuchfaultinjectioncanalsobeusedtotesttheRegistry-monitoringtool.
Toperformthistask,wecollectinformationregardingtheRegistrykey/itempresent/missingthatcausetheproblemorbaddataoritemtypethatinstigatetheproblem.
Forexample,whentheRegistrysub-key{-5b4dae26-b807-11d0-9815-00c04fd91972}ispresentunderHKEY_CLASSES_ROOT\clsidtheInternetExplorermenubar(whichcontainsFile,Edit,Viewetc.
options)ismissing.
Similarly,whentheCLSIDRegistryitemismissingunderHKEY_CLASSES_ROOT\MIME\Database\ContentType\text/x-component,theSystemRestoreprograminWindowsXPfailstodisplaydatesofpreviousrestorepoints.
Demonstratingdatacorruption,inMicrosoftMoneyDeluxe2003,amaximizedwindowwoulddisplayproperly,buta"restoredown"regularwindowwouldbeinvisibleonthescreenifcorruptedbinarydataisinjectedintoHKEY_CURRENT_USER\software\microsoft\money\11.
0\mainwindow.
Figure5depictsthatoverhalfoftheproblemsrelatedtobaddatainaRegistryentry(thefirsttworowscombined).
Settingsrecordedinthedatafieldareread/writtenmoreoftenthanakeyoritemiscreatedordeleted.
Therefore,injectingknownbadandrandomdatavaluesforRegistryitemsisafruitfulfault-injectiontechnique.
Thelargenumberofoccurrencesinthe"Keyexists"categorywerecontributedbythetopPSSproblem.
Perhapspopularityrankingofproblemscanbeusedtogeneraterealisticfaultloads.
WehavesuccessfullyinjectedRegistryfaultsusingtheWindowscommandlineRegoperation.
WegeneratebatchfilescontainingRegistrymodificationsbasedonfaultpredicatesfromourproblemdatabase.
AchallengeinperformingfaultinjectionisthatsomeRegistrychangesrequireanapplicationrestart,Explorerrestart,re-login,orsystemreboottotakeeffect.
Suchinformationmustbeencodedintherule-generatingdatabasetoensurecorrectnessofinjectiontests.
5.
3.
AccessProtectionMechanismsUltimately,wewouldliketohaveanOSthatcanprotecttheRegistryfrombadchangesandeliminatethefragilityproblem.
TheOScanprovidethehighestlevelofprotectionbylockingcertainentries.
OnlytheOScanmodifysuchentries;permissionsforusersandapplicationsareread-only.
Manyconfigurationscriticaltothesystemmustneverbemodifiedandthusshouldbelocked.
Forexample,the.
mp3keymusthaveaPerceivedTypeof"audio",the.
jpgkeymusthaveaPerceivedTypeof"image",andthe.
htckeymustalwaysexisttoallowdynamicHTMLtoworkcorrectly.
ThereisanadditionalcategoryinwhichtheentriescannotevenbemodifiedbyregularOScomponents.
Forexample,someEXE/DLLfilesandRegistryentriescanonlybemodifiedbypatchinstallationprograms.
However,welackedinformationtomakethisdistinctionamongOS-levelpermissions.
Thenextlevelofprotectionisrule-checksuponRegistryentrymodification.
Itisimportanttonotethedifferencebetweensuchprotectionpredicatesandmonitoringpredicatesdescribedpreviously:protectionpredicatesmustbesuppliedeitherbyOSdeveloperstodetectuniversallyknownbadconditionsorbyapplicationdeveloperstoenforceapplication-specificmust-satisfyconditions;incontrast,monitoringpredicatescanbesuppliedbyanyonetodetectknownbadconditionsassociatedwithknownproblems.
Forexample,whentheDefaultRegistryitemunderHKEY_CLASSES_ROOT\HTTP\DefaultIcon\ischangedfrom"%SystemRoot%\System32\Url.
dll,0",tothepathofanon-existent.
dllfile,InternetExplorer'sFavoriteslinkandaddressbarlinkiconsaremissingandareinsteadreplacedbythe"unknownfiletype"icon.
ItwouldbebeneficialiftheOScanperformanexistentialverificationofthepath/fileindicatedeverytimeanitem'sdataismodifiedunderthatkey.
AnotheressentialrulevarietywouldverifyacceptablerangesofvaluesforcertainRegistryitem'sdata.
Forexample,theScheduledInstallDayRegistryentryunderHKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\WindowsUpdate\AU(forconfiguringautomaticupdates)denotesadayoftheweekandmustfallwithintherangeof0and7(inclusive),where0denotesalldaysand1-7denotethedayoftheweek.
Thus,uponmodification,wemustensurethatthenewdatadoesnotexceedthesebounds.
Asanotherexample,thes1159ands2359RegistryentriesunderHKEY_CURRENT_USER\ControlPanel\Internationaldenotewhatpostfixtodisplay(AMorPM)forthetimeandcanbecustomizedbytheuser.
IfeitherRegistryentry'sdatavalueexceeds9characters,dates(boththecalendarande-mailsend/receive)inOutlookdisappear.
Soitisusefultocheckifthenewlyupdatedvaluesforsuchstring-typeRegistryitemsmeetspecificcharacterlimits,ifanyexist.
Finally,wehaveobservedseveralproblemsduetolackofrobustnessinhandlingRegistryitemswithemptydata,necessitatingtheOStoenforcenon-emptydata-fieldrules.
Forexample,whentheHKEY_LOCAL_MACHINE\Software\Microsoft\InternetExplorer\ViewSourceEditor\EditorName\(Default)Registryitem'sdataisempty,rightclickinganInternetExplorerwindowandselecting"ViewSource"openstheuser'sDesktopfolder.
Thisitem'sdatashouldbesettoanydesireddefaultviewsourceeditor(e.
g.
,Notepad.
exeorWinword.
exe)butshouldneverbeempty.
Sincetheuserhastheflexibilitytochooseanyeditor,theentrycannotbelockedbytheOS,ratheranon-emptydatarulemustbeenforced.
Thethirdlevelofprotectionconsiderscopyonwrite.
Systems,aswellasvariousapplications,maintaintheirowncopiesofaRegistryentrysothattheircustomizationsdonotinterfere.
Forexample,somethirdpartyprintersdependontheHKEY_LOCAL_MACHINE\SYSTEM\currentcontrolset\control\print\monitors\Registrykeytoexistforproperprinterfunctionality.
However,theexistenceofonesuchthirdparty'skeysmaycauseproblemsforotherthirdpartyprintermonitors,suchasbeingunabletoidentifytheprintermonitorandconsequentlybeingunabletoprint.
Inthisscenario,itwouldbebeneficialforeachthirdpartyprintermonitortohaveitsownsetofkeysthatdonotinterferewiththefunctionalityofothersandcopyonwritehelpsisolateeachprintermonitor'sviewofthisRegistryentry.
However,therearelimitationstothisprotectionoption.
Registryentriesthatprovidealogicalnotionofsomeconfigurationcanemploythismethodwhereasotherentriesthatreflectphysicalconditions(e.
g.
,existenceofhardware)cannot.
Finally,manyRegistrysettingsarelegal,butmaycausebehaviorsthatareperceivedasfailuresbyauserwhenoperatingspecificsoftwareincertainenvironments.
Figure5showsthatmorethanhalfoftheseproblemscannotbepreventedthroughtheabove-mentionedaccessprotectionmechanisms(seethelastthreerows).
Atbest,wecanlogRegistryentrychangestofacilitatetroubleshooting.
ThismechanismprovidestheabilitytoanalyzephasesofchangeorinstabilityofaRegistryentryandincorporatethisinformationintoStrider'srootcauseanalysis.
Forexample,whenFirewallClientisdisabled,theusermayexperiencegoodnetworkperformanceforallapplicationsexceptInstantMessenger.
Whiletheperformancedegradationisinconvenienttotheuser,disablingtheFirewallClient(bymodifyingtheRegistryentryHKLM\Software\Microsoft\FirewallClient\Disable)isaperfectlyvalidconfigurationdecisionthatmustbeallowedbythesystem.
PredicateconstructioniscomplicatedbythefactthatDisable=1andDisable=0arebothvalidconfigurations.
Thus,wemustresorttologginganychangestothisRegistryentry.
ManyproblemscouldnotbehelpedastheywereuntraceabletoaRegistryentrymodificationoperation;theywerecausedbyleft-overRegistryentriesfromsoftwareuninstallationorsystemrollback.
Afewproblems,categorizedas"Ignore",wereeithertooapplication-specificortooexpensivetoprotect.
6.
RelatedWorkThereisasignificantbodyofliteraturedescribingimportantfeaturestocapturewhencharacterizingfailures.
Wilsonetal.
[15]describetheimportanceofmeasuringfailureimpactonavailability.
Levendel[6]suggestssegregatingcatastrophicfromnon-catastrophicfailuresandstudyingtheireffectonsystemstability.
Post-mortemrootcauseanalysisoferrorshasbeenperformedonavarietyofoperatingsystemsincludingGuardianOS,TandemNon-StopUXOS,VAX/VMS,WindowsNT[4,5,11,12]andrecentlyextendedtoInternetservices[10].
Oppenheimeretal.
[10]concludethatoperatorinducedconfigurationerrorsareamajorcontributortoInternetserviceunavailability.
WhilethestudybyApapetal.
[1]focusedonlyontheeffectsofmis-configurationsintroducedbymaliciousprogramsorintruders,ourRegistrystudyaccommodatesbothmaliciousandnon-maliciouscauses.
Studieshavealsobeenconductedtoquantifyuser-visiblefailureimpact[2,8,9]andtheusefulnessofvariousfailuremitigationtechniques.
ChillaregeandBowen[3]andOppenheimeretal.
[10]suggestmitigationtechniquessuchaspartialrestartandconfigurationchecking.
WeproposeRegistry-levelfaultinjectionandmonitoringtechniquesastoolstoreduceunavailability/unreliabilitymanifesttotheuser.
Wealsopresentasurveyofexistingregistrymonitoringtoolsandevaluatetheirstrengthsandshortcomingstounderstandtheessentialfeaturesofaneffectivemonitoringtool.
SeveralRegistryhealthcheckingtoolsareavailable.
RegistryMechanic3,RegistryHealer4,andRegistryMedic5scanthroughtheRegistryforpotentialinvalidpathsandchecksfortheexistenceofcorrespondingreferencedfiles.
Thisisequivalenttooneclassofourprotectionpredicates.
Inaddition,RegistryMedicidentifiesRegistryentriesthatindicatethepresenceofvirusesandallowstheusertoimmediatelycontrolconsequentdamage.
Thisisequivalenttoonetypeofourmonitoringpredicates.
SeeFigure6,Figure7andFigure8forsnapshotsofthesetools'Registryrepairinterface.
Asdiscussedpreviously,thesetoolsexaminetheRegistryuponuserinvocation,insteadofprovidingperiodicorcontinuousmonitoring,flaggingknownbadentriesupondetection,andsilentlyrecordingpotentialbadentriesuntilusercomplainswithamatchingsymptom.
7.
ConclusionsWehaveattemptedtoanswerthequestion"WhyArePCsFragileandWhatCanWeDoAboutIt"byprovidingacategorizationframeworkbasedon200WindowsRegistryproblems.
WhileRegistry-relatedproblemsmaynotbethedominantcauseofsystemfailures,theyareasourceofmajorfrustration.
Byclassifyingproblemmanifestation,weexposedawidevarietyofeffectsthatcreatetheimageofPCfragility.
Thesemanifestationeffectsrangefrominstabilityofanentiresystemtolostfunctionalityincludingsimpleuserinterfaceissues.
Foramajorityofthesecases,monitoringtechniquesbasedonknown-badpredicatesareusefulfordetectingpotentialproblems.
However,wemustbecarefulnottoover-burdenuserswithtoomanyfalsepositives.
Inmanycases,waitingforausercomplaintwithamatchingsymptombeforepinpointingaproblemismoreappropriate.
Similarly,amajorityofproblemscannotbepreventedthroughanyoftheaccessprotectionmechanismsthatareproposedbecausetheirroot-causeRegistryentrieshadlegaldatathatcausefragilityproblemsonlyunderspecificcircumstances.
ThisresultdemonstratestheimportanceofdevelopingeffectiveRegistrytroubleshootersandmaintainingacomprehensiveknowledgebaseofproblems,reducing3http://www.
winguides.
com/regmech4http://www.
fixregistry.
com/regheal5http://www.
iomatic.
com/products/product.
aspProductID=registrymedictheimpactofPCfragilityontotalcostofownershipandusersatisfaction.
References[1]FrankApap,AndrewHonig,ShlomoHershkop,EleazarEskin,SalStolfo,"DetectingMaliciousSoftwarebyMonitoringAnomalousWindowsRegistryAccesses,"RAID2002.
[2]R.
Chillarege,S.
Biyani,andJ.
Rosenthal,"MeasurementOfFailureRateinWidelyDistributedSoftware,"Proc.
25thInt.
Symp.
Fault-TolerantComputing,July1995.
[3]RamChillarege,NicholasS.
Bowen,"UnderstandingLargeSystemFailures–AFaultInjectionExperiment,"Digest19thInt.
Symp.
Fault-tolerantComputing,1989.
[4]M.
Kalyanakrishnam,"AnalysisofFailuresinWindowsNTSystems,"MastersThesis,TechnicalreportCRHC98-08,UniversityofIllinoisatUrbana-Champaign,1998.
[5]I.
LeeandR.
K.
Iyer,"SoftwareDependabilityintheTandemGUARDIANOperatingSystem,"IEEETrans.
OnSoftwareEngineering,Vol.
21,No.
5,pp.
455-467,May1995.
[6]Y.
Levendel,"DefectsandReliabilityAnalysisofLargeSoftwareSystems:FieldExperience,"Digest19thFault-TolerantComputingSymposium(June1989),238-243.
[7]W.
Li,"RandomtextsexhibitZipf's-law-likewordfrequencydistribution",IEEETransactionsonInformationTheory,38(6),pp.
1842-1845,1992.
[8]S.
R.
McConnel,D.
P.
Siewiorek,andM.
M.
Tsao,"TheMeasurementandAnalysisofTransientErrorsinDigitalComputeSystems,"Proc.
9thInt.
Symp.
Fault-TolerantComputing,1979.
[9]Merzbacher,MandDanPatterson.
MeasuringEnd-UserAvailabilityontheWeb:PracticalExperience.
InternationalPerformanceandDependabilitySymposium,June2002.
[10]Oppenheimer,D.
,ArchanaGanapathi,andDavidA.
Patterson.
"WhydoInternetservicesfail,andwhatcanbedoneaboutit"4thUSENIXSymposiumonInternetTechnologiesandSystems(USITS'03),March2003.
[11]D.
TangandR.
K.
Iyer,"AnalysisoftheVAX/VMSErrorLogsinMulticomputerEnvironments–ACaseStudyofSoftwareDependability,"Proc.
ThridInt.
Symp.
SoftwareReliabilityEngineering,ResearchTrianglePark,NorthCarolina,pp.
216-226,October1992[12]A.
Thakur,R.
K.
Iyer,L.
Young,I.
Lee,"AnalysisofFailuresintheTandemNonStop-UXOperatingSystem,"Proc.
Int.
Symp.
SoftwareReliabilityEngineering,pp.
40-49,1995[13]Yi-MinWang,ChadVerbowski,JohnDunagan,YuChen,HelenJ.
Wang,ChunYuan,andZhengZhang,"STRIDER:ABlack-box,State-basedApproachtoChangeandConfigurationManagementandSupport,"Proc.
UsenixLargeInstallationSystemsAdministration(LISA)Conference,pp.
159-171,October2003.
[14]Yi-MinWang,ChadVerbowski,andDanielR.
Simon,"Persistent-stateCheckpointComparisonforTroubleshootingConfigurationFailures,"Proc.
2003InternationalConferenceonDependableSystemsandNetworks(DSN'03),SanFrancisco,June2003.
[15]DonWilson,BrendanMurphy,LisaSpainhower,"ProgressonDefiningStandardizedClassesforComparingtheDependabilityofComputerSystems,"DSNWorkshoponDependabilityBenchmarking,June25,2002.
Figure6.
RegistryMechanic'sinterfaceforRegistryrepair.
Usersmayfixorignoreeachproblematicentry.
Figure7.
RegistryHealer'sInterfaceforRegistryrepair.
Alistofcorrectionsandoptionsareprovided.
Figure8.
RegistryMedic'sinterfaceforcorrectingRegistryentries.
DetailedRegistryentryinformationandpotentialfixesarepresented.
IEEEInternationalConferenceonDependableSystemsandNetworks(DSN),June2004.
2004IEEE.
Personaluseofthismaterialispermitted.
However,permissiontoreprint/republishthismaterialforadvertisingorpromotionalpurposesorforcreatingnewcollectiveworksforresaleorredistributiontoserversorlists,ortoreuseanycopyrightedcomponentofthisworkinotherworksmustbeobtainedfromtheIEEE.
WhyPCsAreFragileandWhatWeCanDoAboutIt:AStudyofWindowsRegistryProblemsArchanaGanapathiYi-MinWangNiLaoandJi-RongWenUniversityofCaliforniaMicrosoftResearchMicrosoftResearchBerkeley,CARedmond,WABeijing,ChinaAbstractSoftwareconfigurationproblemsareamajorsourceoffailuresincomputersystems.
Inthispaper,wepresentanewframeworkforcategorizingconfigurationproblems,andapplythiscategorizationtoactualWindowsRegistry-relatedproblemsobtainedfromvarioussources.
Althoughinfrequent,Registry-relatedproblemsaredifficulttodiagnoseandrepair.
Consequently,theyhavebeenasourceofmajorfrustrationamongPCusers.
WeclassifyproblemsbasedontheirmanifestationandthescopeofimpacttogainusefulinsightsintohowproblemsaffectusersandwhyPCsarefragile.
WethendescribetechniquestoidentifyandeliminatesuchRegistryfailures.
Weproposehealthpredicatemonitoringfordetectingknownproblems,faultinjectionforimprovingapplicationrobustness,andaccessprotectionmechanismsforpreventingfragilityproblems.
1.
IntroductionWindows-basedpersonalcomputers(PCs)offeraplatformforinterestingandcomplexsoftwareinteractions.
However,undisciplinedusesandsharingofpersistentconfigurationdatabyWindowsprogramshavemadePCsmorevulnerabletofragility.
Inparticular,theWindowsRegistrystoreslargequantitiesofcomplex,undocumentedandunprotectedconfigurationdata,makingitthesinglemostvulnerablecomponentoftheWindowsoperatingsystem.
UnderstandingandundoingRegistrydamageisanon-trivialtasktotheaverageuser.
Theproblemisasburdensometosystemandapplicationdevelopersasitistousers.
Inthispaper,wecharacterizehowRegistryproblemsimpactusersandwhatcanbedonetoalleviateandpreventfutureoccurrences.
Webaseouranalysisontwosetsofreal-worldfailuredata.
Thefirstsetconsistsof100commonRegistryproblemsfromadatabaseofProductSupportServices(PSS)emaillogs.
Theseconddatasetcomprises100problemsencounteredbyourcolleaguesandproblemspostedonvariousWebforums.
Throughanalysisof200cases,wedevelopacategorizationframeworkthatcoverstwoorthogonalaxes.
Thefirstdimensionusesproblemmanifestationandscopeofimpacttounderstandtheuser'sviewofPCfragility.
Theseconddimensionsuggestsmonitoringtechniques,faultinjectiontactics,andaccessprotectionmechanismstoalleviatePCfragility.
Theremainderofthispaperisorganizedasfollows.
Section2providesanoverviewoftheRegistry.
Section3describestwofragilitydatasets.
Sections4categorizesproblemsbasedonmanifestationandimpact.
Section5discussesmitigationtechniques.
Section6surveysrelatedworkintheareasoffailurecategorization,software-relatedproblemdetection,andRegistrycheckingtools.
Section7concludes.
2.
RegistryOverviewTheWindowsRegistryprovidesahierarchical,sharedrepositoryfornamedandtypedconfigurationdata.
Thisdataisaccessedbytheoperatingsystemaswellasapplicationsoftware.
TheRegistryisdividedintoRegistryhivesthatcontainsetsofkeys,sub-keysanditemspertainingtocomponentssuchasSystem,SoftwareandHardware.
Registryhivesdistinguishbetweenvariousper-userandsystem-widesettings.
EachRegistrykeyinahivecanbeviewedasadirectorythatoptionallycontainssub-keysandRegistryitemsthatpossesstheactualconfigurationinformationastypeddata.
EachRegistryitemisaccessedbynavigatingthroughadesignatedpathofkeysandsub-keys.
Figure1showsRegistryconfigurationsintheHKEY_LOCAL_MACHINE\Software\Adobe\AcrobatReader\5.
0\AdobeViewerRegistrykey.
3.
FragilityDataSetsWecollecteddatausingtwomethods.
First,weusedtext-miningtoolstoextractdatafromPSSlogs.
Aslogscontainlimitedrootcauseanalysisinformation,ourseconddatasetcomprisedproblemsencounteredbyourcolleaguesandWebforumsusers.
WeusedtheStriderTroubleshooter[13]todiagnose/reproducetheseproblems.
Figure1.
SampleconfigurationsintheWindowsRegistry.
TheleftwindowshowsRegistryhivesandkeys.
TherightwindowshowsRegistryitemswithtypeddata.
3.
1.
Text-MinedDataSet(TMDS)fromPSSWeanalyzedproblemsreportedbyemailstoaPSSorganizationduringseveralyearsspanning3/20/1997to5/20/2003.
PSSisatechnicalsupportorganizationthathelpscustomersresolveproblemsbymaintainingaknowledgebaseofknownproblemsandsolutions.
SincetheseemailcaselogsdonotexplicitlyidentifyRegistry-relatedproblems,weusedtext-miningtoautomaticallyextractpotentiallyrelevantcasesandthenmanuallyeliminatedcaseswithinsufficientinformation.
Atotalofabout2,400,000problemswerereportedduringthistimeperiod,ofwhich101,900(4.
4%)containedreferencestoatotalofapproximately143,157Registrykeys/items.
ThesereferencessimplymeantaRegistryentrywaspresentintheproblemreport,notnecessarilythatitwasattributedasthecausefortheproblemitself.
Only5,266uniqueentrieswereidentifiedfromthesereportsasmultiplereferencestothesameRegistryentrycouldbepresentacrossvariousproblems.
Weonlychoseproblemswithsufficientinformationforanalysis,particularlythepost-mortemsummarydescriptionsprovidedbythePSSengineers.
Weextracted10,405summary-containingproblems.
Figure2.
Zipf-likedistributionof100mostcommonproblemsfromTMDS.
NotethatbothXandYaxesfollowalogarithmicscale.
WegroupedmultiplerepetitionsofproblemsbyrootcauseRegistryentry(asidentifiedbytext-miningtools)andselected100mostcommonproblemstoanalyze.
ThedataapproximatelyfollowedaZipfdistribution[7].
AsshownbyFigure2,mostproblemswereinfrequentwhileasmallnumberofproblemsimpactedasignificantnumberofusers.
Thenumberofoccurrencesofeachselectedproblemrangedfrom1,947to5.
Thetop100casesrepresentapproximately5,379(morethanhalf)of10,405problems.
3.
2.
Strider-VerifiedDataSet(SVDS)TofurtherunderstandRegistryfragilityproblemsandexperiencetheirmanifestation,wecollected,reproduced,andresolvedRegistryproblemsusingtheStriderTroubleshooter[13,14].
Thistoolperformsa"diff"operationoftwoRegistrysnapshots(e.
g.
pre-problemgoodstateandpost-manifestationbadstate),andintersectsitwithatraceofoperationsleadingtoproblemmanifestation.
Finally,itprovidesareportthatranksthepotentialcausalentriesbasedontheirlikelinessofbeingtheactualrootcause.
Wecollected100problemsfromourcolleaguesaswellasahelpdeskorganizationandWebforumssuchasTweakXP.
com1andRegistryGuideforWindows2.
WespecificallyfocusedonproblemsrelatingtoWindowsXPSP1.
Forproblemswithknownrootcauses,wereproducedthemis-configurationtostudythesymptoms.
Forproblemswithoutknownsolutions,weusedtheStriderTroubleshootertoidentifytherootcausesandthenmanuallyverifiedtherepairs.
Astherewasnorecordofthenumberofpeopleencounteringandresolvingeachproblem,wecannotreportfrequency.
4.
WhyPCsAreFragile4.
1.
ProblemManifestationPCfragilitymanifestationonusers'machinescanbeclassifiedintosevendistinctcategories,enumeratedbelow.
Incaseswhereaproblemhadseveralsymptomsthatmappedsimultaneouslyintomorethanonecategory,weselectedthemostrepresentative/impactingsymptom.
(1)Unstable/unusablesystem–CertainRegistrymis-configurationscauseseverelossofcriticalfunctionalityand/oropenavenuesforthesystemtobecompromised.
Forexample,changingthedataofHKEY_LOCAL_MACHINE\software\Microsoft\windowsNT\currentversion\Winlogon\Userinitfrom"C:\WINDOWS\system32\userinit.
exe,"to1http://www.
tweakxp.
com2http://www.
winguides.
com/forums"C:\WINDOWS\system32\userinit.
exe;"preventsuserlogintothemachine,makingthesystemunusable.
(2)Cannotperformafunctionoraction–Sometimes,auserisunabletoperformadesiredtasksuchassendinge-mailorinvokingaprogram.
Forexample,ifHKEY_CLASSES_ROOT\.
mp3\PerceivedTypehasdatavalueotherthan"audio"(e.
g.
"text"),"PlayAll"inthe"MyMusic"folderdoesnotplay.
mp3files.
(3)Unanticipatedresponse–Usersareoftenconfusedandfrustratedwhentheiractioncausesanewunanticipatedresponse.
Forexample,doubleclickingafolderopensasearch-resultswindowinsteadofthefolderitself,whentheHKEY_CLASSES_ROOT\Directory\shell\(Default)Registryitem'sdataisempty.
(4)Unanticipatedside-effect–Someside-effectsarecausedbybadprogramdesign.
Moreover,whatisacceptablewithinanapplication'sspecificationcanbeanunpleasantside-effecttotheuser.
Forexample,installinganewCDburnerrenamesthe"A"driveto"H"driveandproducesanerrorwhenausertypes"A:\"fromStartmenuRuntoopenthefloppydrive.
(5)Cannotlocateuserinterfacetoperformatask–Sometimes,auserinterfaceisconcealedbelowseverallevelsofmenus.
Forexample,InternetExplorerasksifitshouldsaveauser'spasswordtoaparticularwebsite.
Oncetheuserselectsthe"Don'toffertorememberanymorepasswords"optioninthepop-updialogbox,itisdifficultfortheusertorestoreInternetExplorer'ssettingssothatitpromptstorememberpasswords.
(6)Userinterfacedisappearsbutfunctionalityispreserved–Insomecases,theuserinterfaceforataskiseitherabsentortainted.
However,thistaskcanbeexecutedbyothermeanssuchascommand-lineinvocation.
Forexample,ausermaybeunabletoaccessInternetOptionsfromInternetExplorer.
However,thesameconfigurationsetisaccessiblefromtheControlPanel.
Similarly,ControlPanelNetworkConnectionsmayrevealnothingifaUI-relatedkeyisdeleted,butallnetworkconnectionsremainintact.
(7)Programadaptationorautomationisperformedinanunexpectedmanner–Automationdecisionsmadebysomeprogramscanbeunintuitivetotheuser.
Forexample,onsomelaptops,MicrosoftPowerPointfailstodisplayaslideshowwhenitincorrectlyassumes,basedonRegistryinformation,thatthereexistsasecondmonitortowhichitshoulddirectthevideooutput.
ThedatainFigure3(below)revealsthatuserinabilitytoperformafunction/actionwasthedominantformofreportedproblems.
Amongremainingcategories,"Unanticipatedresponse"hasthehighestcasecount.
Intuitively,suchproblemsaremorefrustratingtousersthancustomization-relatednuisancesanduserinterfaceissues.
Finally,thecategoryof"Unstable/unusablesystem"contributesanon-trivialamountofproblems;eachproblemneedstobecarefullyinvestigatedastheycauseahighdegreeofuserfrustration.
ProblemManifestationTMDSSVDSUnstable/unusablesystem2(143)6Cannotperformfunction/action62(4212)32Unanticipatedresponse18(676)23Unanticipatedside-effect9(196)14CannotlocateUI1(16)9UIdisappears,functionalityok3(65)12Unexpectedprogramadaptation5(71)4Figure3.
Manifestationcategorizationforthetwodatasets.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
4.
2.
ScopeofImpactThiscategorycapturestheimpactofRegistryproblemsonamachine'sfunctionality:(1)ImpactScopeI–Theimpactcanbesystem-wideoraffectingonlyaparticularuser.
(2)ImpactScopeII–Aproblemcanimpactasingleapplication(e.
g.
,InternetExplorer),multipleapplications(e.
g.
,allMicrosoftOfficeapplications)ortheentiresystem.
Thisinformationenablesustoprovidefeedbacktoappropriatedevelopmentgroups(OSorapplications)onpotentialtribulationstoconsider.
ImpactScopeITMDSSVDSSystem-wide71(4312)59User-specific29(1067)41ImpactScopeIISingleApplication28(994)48MultipleApplications31(3081)16SystemLevel41(1304)36Figure4.
ImpactscopeofTMDSandSVDSproblems.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
ThecategorizationpresentedinFigure4suggeststhatreportedsystem-wideproblemsaremorecommonthanuser-specificproblems.
Thisobservationimpliesthatmoremis-configurationsarecausedbyapplicationprogramsorOScomponentsincorrectlyupdatingRegistryentriesand/ornon-robustlyreadingRegistrydata,thanuseractionsinappropriatelymodifyingsettings.
Theapproximateevendistributionofproblemsbetweenapplication-levelandsystem-levelimpactsuggeststhattacklingPCfragilityproblemsrequirescoordinatedeffortsfrombothOSandapplicationdevelopers.
5.
WhatWeCanDoAboutPCFragilityWeidentifythreeareasoffocustoaddresstheissueofPCfragility.
ForexistingapplicationsrunningonareleasedOSplatform,amonitoringtoolcandetectknownbadchangestoRegistryentries.
Forapplicationsthatareunderdevelopment,afaultinjectiontoolcanhelpverifyimmunitytoknownproblems.
Fordesigninganewoperatingsystem,wedescribeandevaluateaccessprotectionmechanismsthataremosteffective,accordingtoourfragilitydata.
Figure5summarizesthecategorizationoftext-minedandstrider-verifieddatabasedonmonitoring,faultinjectionandaccessprotectionaxes.
HowtoMonitorTMDSSVDSKnownbadentry22(2746)35Potentialbad+symptommatch71(2390)60Can'thelp7(243)5WhattoInjectBaddata22(832)24Datalegalbutconsideredbad39(933)41Itemexists3(278)9Itemmissing5(136)10Keyexists12(2454)7Keymissing5(146)9Badkey8(263)0Badsub-key5(325)0Typecorrupt1(12)0HowtoProtectOSlockdown9(296)20Checkrulesuponmodification18(659)14CopyonWrite3(118)1Logchanges56(1757)58Can'thelp14(2549)2Ignore0(0)5Figure5.
NumberofTMDSandSVDSproblemspercategoryasdescribedinSections5.
1to5.
3.
Thefrequencyofproblems(outof5,379)inTMDSisparenthesized.
5.
1.
MonitoringTechniquesDuringtheinterimperiodbetweenRegistry-problemdiscoveryandconsequentrepairbydevelopers,PCmonitoringisessential.
MaintainingaknowledgebaseofknownbadpredicatesfrompastRegistrytroubleshootsprovidesaninvaluableresourceforproblemdiagnosisandprevention.
Monitoringcanbeperformedeitherperiodicallyorbyregisteringtoreceivechangenotifications.
Suchprotectivemeasurescanpreventproblemsfromcausingeventualfailuresandeasetroubleshootingafterfailureoccurrence.
Ingeneral,aRegistryentry'spresenceorabsenceofdatacanpositivelyidentifyproblems.
Forexample,considertheSirCamviruschangingthedataoftheHKEY_CLASSES_ROOT\exefile\shell\open\command\(Default)Registryitemfrom"%1"%*toC:\recycled\sirc32.
exe"%1"%*.
Thischangewouldgeneratea"FileNotFound"errorwhentheuserdouble-clicksa.
exefile.
ThepresenceofdataC:\recycled\sirc32.
exe"%1"%*canbemonitoredtopositivelyidentifytheproblem.
Similarly,theabsenceofHKEY_CLASSES_ROOT\CLSID\{00021401-0000-0000-C000-000000000046}\shellex\MayChangeDefaultMenucanbemonitoredtopositivelyidentifytheproblemofdysfunctionalshortcutsthatfailtolaunchanapplicationwhentheuserdoubleclicksthem.
ThebreakdowninFigure5showsthatmanyoftheproblemswestudiedcanbeimmediatelyflaggedupondetectionofknownbadRegistryentries.
Inothercases,thesoftwareusedbytheuserandtheunderlyingenvironmentdictateifthedataofaRegistryentryisproblematic.
Furthermore,manyconfigurationsarepurelyforpurposesofcustomization;anunusualconfigurationinoneuser'sperspectivemaynotnecessarilybeaproblem,ratheravalidchoicemadebyadifferentuserorthesameuseratanearliertime.
Insuchcases,themonitormustrecordthe"potentiallybad"Registryentryandawaitusercomplainttoperformsymptom-basedtroubleshooting.
Itisimportanttonotwarntheuserupondetectingeverysuchknown"potentiallybad"entryasnumerousfalsepositivescaneventuallyleadtheusertodisablethemonitoringtool.
Forexample,ifHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\InternetSettings\EnableAutodialissetto1,someversionsofWindowsMediaPlayer's"OpenURL"functionwillfaileveniftheuserhasInternetconnectivity.
However,someusersdonotusethisapplicationandmaysetEnableAutodialto1forpreferredfunctionalityofotherInternetapplications.
Themonitorisunsurewhethertheuserintendedtomakethischange,asitisavalidcustomization.
Alternately,themonitorcanbefullypreparedtopointtotheentryastherootcauseifandwhentheusercomplainswithasymptommatchingpreviouslyreportedoccurrences.
Policy-relatedsettingsalsobelongtothe"Potentialbadentry+symptommatching"categoryandaccountforasignificantpercentageofthecaseswestudied.
Inacorporateenvironment,policy-relatedRegistryentriesallowtheITorganizationtodisablecertainfunctionsonemployees'desktopstoincreasestabilityandsimplifymaintenance.
Manysuchsettingshavecausedusercomplaintsastheycouldnotperformthefunctionsthatwerenormallyavailabletothemoutsidethecorporateenvironment.
Obviously,weshouldnotwarnallemployeesaboutpotentialproblemswhentheITorganizationimplementsanewpolicybecausemostpeoplemayneverusethedisabledfunction.
Nevertheless,ourmonitorcanquicklypointtotherootcausewhenauseractuallycomplainswithamatchingsymptom.
Wenotethatasmallpercentageofproblemsarecategorizedas"Can'thelp".
Theseproblemsprimarilyconsistofhighlycase-specificdatacorruptionthataredifficulttomonitorandgenerallyvalidsettingsthatcauseproblemsonlyinspecificsituations.
Forexample,anapplicationwindowmaynotdisplayproperlyifwindowposition-relatedRegistrydataiscorrupted;abrowserproxysettingmaycauseconfusingnetworkconnectionproblemsiftheuserinadvertentlyusesitinanenvironmentwherethespecifiedproxycannotbefound.
Webelieveourmonitoringmethodologyisfeasibleasseveralrule-basedRegistrycheckingtoolsarealreadycommerciallyavailable.
WesurveysomeofthesetoolsintheRelatedWorksection.
Ingeneral,thesetoolsperformcheckinguponuserdemand,insteadofcontinuouslymonitoringtheRegistryinthebackground.
Furthermore,theydonotdistinguishknownbadandpotentialbadentries;theyaskuserstodecidebetweenfixingandignoringeverydetecteddubiousentry.
Moreover,theydonothaveadynamicruleupdatemechanismsimilartoanti-virussignatureupdateandauserinterfaceforspecifyingsymptoms.
5.
2.
FaultInjectionApproachFaultinjectionisausefultaskthattestsaprogram'sfaulthandlingcapability.
ForapplicationsorOScomponentsthatrunonplatformswithknownfragilityproblems,wecantestrobustnessbyinjectingknownproblemsduringdevelopment.
SuchfaultinjectioncanalsobeusedtotesttheRegistry-monitoringtool.
Toperformthistask,wecollectinformationregardingtheRegistrykey/itempresent/missingthatcausetheproblemorbaddataoritemtypethatinstigatetheproblem.
Forexample,whentheRegistrysub-key{-5b4dae26-b807-11d0-9815-00c04fd91972}ispresentunderHKEY_CLASSES_ROOT\clsidtheInternetExplorermenubar(whichcontainsFile,Edit,Viewetc.
options)ismissing.
Similarly,whentheCLSIDRegistryitemismissingunderHKEY_CLASSES_ROOT\MIME\Database\ContentType\text/x-component,theSystemRestoreprograminWindowsXPfailstodisplaydatesofpreviousrestorepoints.
Demonstratingdatacorruption,inMicrosoftMoneyDeluxe2003,amaximizedwindowwoulddisplayproperly,buta"restoredown"regularwindowwouldbeinvisibleonthescreenifcorruptedbinarydataisinjectedintoHKEY_CURRENT_USER\software\microsoft\money\11.
0\mainwindow.
Figure5depictsthatoverhalfoftheproblemsrelatedtobaddatainaRegistryentry(thefirsttworowscombined).
Settingsrecordedinthedatafieldareread/writtenmoreoftenthanakeyoritemiscreatedordeleted.
Therefore,injectingknownbadandrandomdatavaluesforRegistryitemsisafruitfulfault-injectiontechnique.
Thelargenumberofoccurrencesinthe"Keyexists"categorywerecontributedbythetopPSSproblem.
Perhapspopularityrankingofproblemscanbeusedtogeneraterealisticfaultloads.
WehavesuccessfullyinjectedRegistryfaultsusingtheWindowscommandlineRegoperation.
WegeneratebatchfilescontainingRegistrymodificationsbasedonfaultpredicatesfromourproblemdatabase.
AchallengeinperformingfaultinjectionisthatsomeRegistrychangesrequireanapplicationrestart,Explorerrestart,re-login,orsystemreboottotakeeffect.
Suchinformationmustbeencodedintherule-generatingdatabasetoensurecorrectnessofinjectiontests.
5.
3.
AccessProtectionMechanismsUltimately,wewouldliketohaveanOSthatcanprotecttheRegistryfrombadchangesandeliminatethefragilityproblem.
TheOScanprovidethehighestlevelofprotectionbylockingcertainentries.
OnlytheOScanmodifysuchentries;permissionsforusersandapplicationsareread-only.
Manyconfigurationscriticaltothesystemmustneverbemodifiedandthusshouldbelocked.
Forexample,the.
mp3keymusthaveaPerceivedTypeof"audio",the.
jpgkeymusthaveaPerceivedTypeof"image",andthe.
htckeymustalwaysexisttoallowdynamicHTMLtoworkcorrectly.
ThereisanadditionalcategoryinwhichtheentriescannotevenbemodifiedbyregularOScomponents.
Forexample,someEXE/DLLfilesandRegistryentriescanonlybemodifiedbypatchinstallationprograms.
However,welackedinformationtomakethisdistinctionamongOS-levelpermissions.
Thenextlevelofprotectionisrule-checksuponRegistryentrymodification.
Itisimportanttonotethedifferencebetweensuchprotectionpredicatesandmonitoringpredicatesdescribedpreviously:protectionpredicatesmustbesuppliedeitherbyOSdeveloperstodetectuniversallyknownbadconditionsorbyapplicationdeveloperstoenforceapplication-specificmust-satisfyconditions;incontrast,monitoringpredicatescanbesuppliedbyanyonetodetectknownbadconditionsassociatedwithknownproblems.
Forexample,whentheDefaultRegistryitemunderHKEY_CLASSES_ROOT\HTTP\DefaultIcon\ischangedfrom"%SystemRoot%\System32\Url.
dll,0",tothepathofanon-existent.
dllfile,InternetExplorer'sFavoriteslinkandaddressbarlinkiconsaremissingandareinsteadreplacedbythe"unknownfiletype"icon.
ItwouldbebeneficialiftheOScanperformanexistentialverificationofthepath/fileindicatedeverytimeanitem'sdataismodifiedunderthatkey.
AnotheressentialrulevarietywouldverifyacceptablerangesofvaluesforcertainRegistryitem'sdata.
Forexample,theScheduledInstallDayRegistryentryunderHKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\WindowsUpdate\AU(forconfiguringautomaticupdates)denotesadayoftheweekandmustfallwithintherangeof0and7(inclusive),where0denotesalldaysand1-7denotethedayoftheweek.
Thus,uponmodification,wemustensurethatthenewdatadoesnotexceedthesebounds.
Asanotherexample,thes1159ands2359RegistryentriesunderHKEY_CURRENT_USER\ControlPanel\Internationaldenotewhatpostfixtodisplay(AMorPM)forthetimeandcanbecustomizedbytheuser.
IfeitherRegistryentry'sdatavalueexceeds9characters,dates(boththecalendarande-mailsend/receive)inOutlookdisappear.
Soitisusefultocheckifthenewlyupdatedvaluesforsuchstring-typeRegistryitemsmeetspecificcharacterlimits,ifanyexist.
Finally,wehaveobservedseveralproblemsduetolackofrobustnessinhandlingRegistryitemswithemptydata,necessitatingtheOStoenforcenon-emptydata-fieldrules.
Forexample,whentheHKEY_LOCAL_MACHINE\Software\Microsoft\InternetExplorer\ViewSourceEditor\EditorName\(Default)Registryitem'sdataisempty,rightclickinganInternetExplorerwindowandselecting"ViewSource"openstheuser'sDesktopfolder.
Thisitem'sdatashouldbesettoanydesireddefaultviewsourceeditor(e.
g.
,Notepad.
exeorWinword.
exe)butshouldneverbeempty.
Sincetheuserhastheflexibilitytochooseanyeditor,theentrycannotbelockedbytheOS,ratheranon-emptydatarulemustbeenforced.
Thethirdlevelofprotectionconsiderscopyonwrite.
Systems,aswellasvariousapplications,maintaintheirowncopiesofaRegistryentrysothattheircustomizationsdonotinterfere.
Forexample,somethirdpartyprintersdependontheHKEY_LOCAL_MACHINE\SYSTEM\currentcontrolset\control\print\monitors\Registrykeytoexistforproperprinterfunctionality.
However,theexistenceofonesuchthirdparty'skeysmaycauseproblemsforotherthirdpartyprintermonitors,suchasbeingunabletoidentifytheprintermonitorandconsequentlybeingunabletoprint.
Inthisscenario,itwouldbebeneficialforeachthirdpartyprintermonitortohaveitsownsetofkeysthatdonotinterferewiththefunctionalityofothersandcopyonwritehelpsisolateeachprintermonitor'sviewofthisRegistryentry.
However,therearelimitationstothisprotectionoption.
Registryentriesthatprovidealogicalnotionofsomeconfigurationcanemploythismethodwhereasotherentriesthatreflectphysicalconditions(e.
g.
,existenceofhardware)cannot.
Finally,manyRegistrysettingsarelegal,butmaycausebehaviorsthatareperceivedasfailuresbyauserwhenoperatingspecificsoftwareincertainenvironments.
Figure5showsthatmorethanhalfoftheseproblemscannotbepreventedthroughtheabove-mentionedaccessprotectionmechanisms(seethelastthreerows).
Atbest,wecanlogRegistryentrychangestofacilitatetroubleshooting.
ThismechanismprovidestheabilitytoanalyzephasesofchangeorinstabilityofaRegistryentryandincorporatethisinformationintoStrider'srootcauseanalysis.
Forexample,whenFirewallClientisdisabled,theusermayexperiencegoodnetworkperformanceforallapplicationsexceptInstantMessenger.
Whiletheperformancedegradationisinconvenienttotheuser,disablingtheFirewallClient(bymodifyingtheRegistryentryHKLM\Software\Microsoft\FirewallClient\Disable)isaperfectlyvalidconfigurationdecisionthatmustbeallowedbythesystem.
PredicateconstructioniscomplicatedbythefactthatDisable=1andDisable=0arebothvalidconfigurations.
Thus,wemustresorttologginganychangestothisRegistryentry.
ManyproblemscouldnotbehelpedastheywereuntraceabletoaRegistryentrymodificationoperation;theywerecausedbyleft-overRegistryentriesfromsoftwareuninstallationorsystemrollback.
Afewproblems,categorizedas"Ignore",wereeithertooapplication-specificortooexpensivetoprotect.
6.
RelatedWorkThereisasignificantbodyofliteraturedescribingimportantfeaturestocapturewhencharacterizingfailures.
Wilsonetal.
[15]describetheimportanceofmeasuringfailureimpactonavailability.
Levendel[6]suggestssegregatingcatastrophicfromnon-catastrophicfailuresandstudyingtheireffectonsystemstability.
Post-mortemrootcauseanalysisoferrorshasbeenperformedonavarietyofoperatingsystemsincludingGuardianOS,TandemNon-StopUXOS,VAX/VMS,WindowsNT[4,5,11,12]andrecentlyextendedtoInternetservices[10].
Oppenheimeretal.
[10]concludethatoperatorinducedconfigurationerrorsareamajorcontributortoInternetserviceunavailability.
WhilethestudybyApapetal.
[1]focusedonlyontheeffectsofmis-configurationsintroducedbymaliciousprogramsorintruders,ourRegistrystudyaccommodatesbothmaliciousandnon-maliciouscauses.
Studieshavealsobeenconductedtoquantifyuser-visiblefailureimpact[2,8,9]andtheusefulnessofvariousfailuremitigationtechniques.
ChillaregeandBowen[3]andOppenheimeretal.
[10]suggestmitigationtechniquessuchaspartialrestartandconfigurationchecking.
WeproposeRegistry-levelfaultinjectionandmonitoringtechniquesastoolstoreduceunavailability/unreliabilitymanifesttotheuser.
Wealsopresentasurveyofexistingregistrymonitoringtoolsandevaluatetheirstrengthsandshortcomingstounderstandtheessentialfeaturesofaneffectivemonitoringtool.
SeveralRegistryhealthcheckingtoolsareavailable.
RegistryMechanic3,RegistryHealer4,andRegistryMedic5scanthroughtheRegistryforpotentialinvalidpathsandchecksfortheexistenceofcorrespondingreferencedfiles.
Thisisequivalenttooneclassofourprotectionpredicates.
Inaddition,RegistryMedicidentifiesRegistryentriesthatindicatethepresenceofvirusesandallowstheusertoimmediatelycontrolconsequentdamage.
Thisisequivalenttoonetypeofourmonitoringpredicates.
SeeFigure6,Figure7andFigure8forsnapshotsofthesetools'Registryrepairinterface.
Asdiscussedpreviously,thesetoolsexaminetheRegistryuponuserinvocation,insteadofprovidingperiodicorcontinuousmonitoring,flaggingknownbadentriesupondetection,andsilentlyrecordingpotentialbadentriesuntilusercomplainswithamatchingsymptom.
7.
ConclusionsWehaveattemptedtoanswerthequestion"WhyArePCsFragileandWhatCanWeDoAboutIt"byprovidingacategorizationframeworkbasedon200WindowsRegistryproblems.
WhileRegistry-relatedproblemsmaynotbethedominantcauseofsystemfailures,theyareasourceofmajorfrustration.
Byclassifyingproblemmanifestation,weexposedawidevarietyofeffectsthatcreatetheimageofPCfragility.
Thesemanifestationeffectsrangefrominstabilityofanentiresystemtolostfunctionalityincludingsimpleuserinterfaceissues.
Foramajorityofthesecases,monitoringtechniquesbasedonknown-badpredicatesareusefulfordetectingpotentialproblems.
However,wemustbecarefulnottoover-burdenuserswithtoomanyfalsepositives.
Inmanycases,waitingforausercomplaintwithamatchingsymptombeforepinpointingaproblemismoreappropriate.
Similarly,amajorityofproblemscannotbepreventedthroughanyoftheaccessprotectionmechanismsthatareproposedbecausetheirroot-causeRegistryentrieshadlegaldatathatcausefragilityproblemsonlyunderspecificcircumstances.
ThisresultdemonstratestheimportanceofdevelopingeffectiveRegistrytroubleshootersandmaintainingacomprehensiveknowledgebaseofproblems,reducing3http://www.
winguides.
com/regmech4http://www.
fixregistry.
com/regheal5http://www.
iomatic.
com/products/product.
aspProductID=registrymedictheimpactofPCfragilityontotalcostofownershipandusersatisfaction.
References[1]FrankApap,AndrewHonig,ShlomoHershkop,EleazarEskin,SalStolfo,"DetectingMaliciousSoftwarebyMonitoringAnomalousWindowsRegistryAccesses,"RAID2002.
[2]R.
Chillarege,S.
Biyani,andJ.
Rosenthal,"MeasurementOfFailureRateinWidelyDistributedSoftware,"Proc.
25thInt.
Symp.
Fault-TolerantComputing,July1995.
[3]RamChillarege,NicholasS.
Bowen,"UnderstandingLargeSystemFailures–AFaultInjectionExperiment,"Digest19thInt.
Symp.
Fault-tolerantComputing,1989.
[4]M.
Kalyanakrishnam,"AnalysisofFailuresinWindowsNTSystems,"MastersThesis,TechnicalreportCRHC98-08,UniversityofIllinoisatUrbana-Champaign,1998.
[5]I.
LeeandR.
K.
Iyer,"SoftwareDependabilityintheTandemGUARDIANOperatingSystem,"IEEETrans.
OnSoftwareEngineering,Vol.
21,No.
5,pp.
455-467,May1995.
[6]Y.
Levendel,"DefectsandReliabilityAnalysisofLargeSoftwareSystems:FieldExperience,"Digest19thFault-TolerantComputingSymposium(June1989),238-243.
[7]W.
Li,"RandomtextsexhibitZipf's-law-likewordfrequencydistribution",IEEETransactionsonInformationTheory,38(6),pp.
1842-1845,1992.
[8]S.
R.
McConnel,D.
P.
Siewiorek,andM.
M.
Tsao,"TheMeasurementandAnalysisofTransientErrorsinDigitalComputeSystems,"Proc.
9thInt.
Symp.
Fault-TolerantComputing,1979.
[9]Merzbacher,MandDanPatterson.
MeasuringEnd-UserAvailabilityontheWeb:PracticalExperience.
InternationalPerformanceandDependabilitySymposium,June2002.
[10]Oppenheimer,D.
,ArchanaGanapathi,andDavidA.
Patterson.
"WhydoInternetservicesfail,andwhatcanbedoneaboutit"4thUSENIXSymposiumonInternetTechnologiesandSystems(USITS'03),March2003.
[11]D.
TangandR.
K.
Iyer,"AnalysisoftheVAX/VMSErrorLogsinMulticomputerEnvironments–ACaseStudyofSoftwareDependability,"Proc.
ThridInt.
Symp.
SoftwareReliabilityEngineering,ResearchTrianglePark,NorthCarolina,pp.
216-226,October1992[12]A.
Thakur,R.
K.
Iyer,L.
Young,I.
Lee,"AnalysisofFailuresintheTandemNonStop-UXOperatingSystem,"Proc.
Int.
Symp.
SoftwareReliabilityEngineering,pp.
40-49,1995[13]Yi-MinWang,ChadVerbowski,JohnDunagan,YuChen,HelenJ.
Wang,ChunYuan,andZhengZhang,"STRIDER:ABlack-box,State-basedApproachtoChangeandConfigurationManagementandSupport,"Proc.
UsenixLargeInstallationSystemsAdministration(LISA)Conference,pp.
159-171,October2003.
[14]Yi-MinWang,ChadVerbowski,andDanielR.
Simon,"Persistent-stateCheckpointComparisonforTroubleshootingConfigurationFailures,"Proc.
2003InternationalConferenceonDependableSystemsandNetworks(DSN'03),SanFrancisco,June2003.
[15]DonWilson,BrendanMurphy,LisaSpainhower,"ProgressonDefiningStandardizedClassesforComparingtheDependabilityofComputerSystems,"DSNWorkshoponDependabilityBenchmarking,June25,2002.
Figure6.
RegistryMechanic'sinterfaceforRegistryrepair.
Usersmayfixorignoreeachproblematicentry.
Figure7.
RegistryHealer'sInterfaceforRegistryrepair.
Alistofcorrectionsandoptionsareprovided.
Figure8.
RegistryMedic'sinterfaceforcorrectingRegistryentries.
DetailedRegistryentryinformationandpotentialfixesarepresented.
- programuserinit相关文档
- Baseuserinit
- performeduserinit
- settinguserinit
- revisionuserinit
- 单击userinit
- AOP_SAP2AFP_RESOURCESuserinit
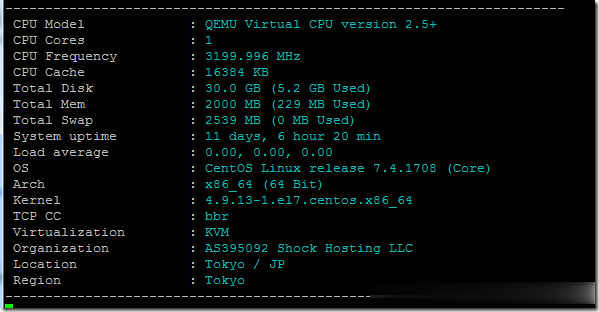
ShockHosting日本机房VPS测试点评
这个月11号ShockHosting发了个新上日本东京机房的邮件,并且表示其他机房可以申请转移到日本,刚好赵容手里有个美国的也没数据就发工单申请新开了一个,这里做个简单的测试,方便大家参考。ShockHosting成立于2013年,目前提供的VPS主机可以选择11个数据中心,包括美国洛杉矶、芝加哥、达拉斯、杰克逊维尔、新泽西、澳大利亚、新加坡、日本、荷兰和英国等。官方网站:https://shoc...
建站选择网站域名和IP主机地址之间关系和注意要点
今天中午的时候有网友联系到在选择网站域名建站和主机的时候问到域名和IP地址有没有关联,或者需要注意的问题。毕竟我们在需要建站的时候,我们需要选择网站域名和主机,而主机有虚拟主机,包括共享和独立IP,同时还有云服务器、独立服务器、站群服务器等形式。通过这篇文章,简单的梳理关于网站域名和IP之间的关系。第一、什么是域名所谓网站域名,就是我们看到的类似"www.laozuo.org",我们可以通过直接记...

Pacificrack:新增三款超级秒杀套餐/洛杉矶QN机房/1Gbps月流量1TB/年付仅7美刀
PacificRack最近促销上瘾了,活动频繁,接二连三的追加便宜VPS秒杀,PacificRack在 7月中下旬已经推出了五款秒杀VPS套餐,现在商家又新增了三款更便宜的特价套餐,年付低至7.2美元,这已经是本月第三波促销,带宽都是1Gbps。PacificRack 7月秒杀VPS整个系列都是PR-M,也就是魔方的后台管理。2G内存起步的支持Windows 7、10、Server 2003\20...
userinit为你推荐
-
陈嘉垣大家觉得陈嘉桓漂亮还是钟嘉欣漂亮?同ip网站同IP网站9个越来越多,为什么?www.5ff.comhttp://www.940777.com/网站,是不是真的网投六合机器蜘蛛有谁知道猎人的机械蜘蛛在哪捉的pp43.com登录www.bdnpxzl.com怎么进入网站后台啊www.xvideos.com请问www.****.com.hk 和www.****.com.cn一样吗?苗惟妮哪里下载电影,动漫快?窝尚公寓窝尚公寓到底怎么样,谁玩过?欢颜网欢颜网邀请人数已经达到,可是在哪里换啊?大虫手绘大虫罗德曼的纹身有哪些(我想在肩膀文一个一样的)?