tasksubuntu12.04
ubuntu12.04 时间:2021-03-29 阅读:()
SEEDLabs–HeartbleedAttack1HeartbleedAttackLabCopyrightc2016WenliangDu,SyracuseUniversity.
ThedevelopmentofthisdocumentwaspartiallyfundedbytheNationalScienceFoundationunderAwardNo.
1303306and1318814.
ThisworkislicensedunderaCreativeCommonsAttribution-NonCommercial-ShareAlike4.
0InternationalLicense.
Ahuman-readablesummaryof(andnotasubstitutefor)thelicenseisthefollowing:Youarefreetocopyandredistributethematerialinanymediumorformat.
Youmustgiveappropriatecredit.
Ifyouremix,transform,orbuilduponthematerial,youmustdistributeyourcontributionsunderthesamelicenseastheoriginal.
Youmaynotusethematerialforcommercialpurposes.
1OverviewTheHeartbleedbug(CVE-2014-0160)isasevereimplementationawintheOpenSSLlibrary,whichen-ablesattackerstostealdatafromthememoryofthevictimserver.
Thecontentsofthestolendatadependonwhatisthereinthememoryoftheserver.
Itcouldpotentiallycontainprivatekeys,TLSsessionkeys,usernames,passwords,creditcards,etc.
ThevulnerabilityisintheimplementationoftheHeartbeatprotocol,whichisusedbySSL/TLStokeeptheconnectionalive.
Theobjectiveofthislabisforstudentstounderstandhowseriousthisvulnerabilityis,howtheattackworks,andhowtoxtheproblem.
TheaffectedOpenSSLversionrangeisfrom1.
0.
1to1.
0.
1f.
TheversioninourUbuntuVMis1.
0.
1.
2LabEnvironmentInthislab,weneedtosetuptwoVMs:onecalledattackermachineandtheothercalledvictimserver.
Weusethepre-builtSEEDUbuntu12.
04VM.
TheVMsneedtousetheNAT-Networkadapterforthenetworksetting.
ThiscanbedonebygoingtotheVMsettings,pickingNetwork,andclickingtheAdaptortagtoswitchtheadaptertoNAT-Network.
MakesurebothVMsareonthesameNAT-Network.
ThewebsiteusedinthisattackcanbeanyHTTPSwebsitethatusesSSL/TLS.
However,sinceitisillegaltoattackarealwebsite,wehavesetupawebsiteinourVM,andconducttheattackonourownVM.
Weuseanopen-sourcesocialnetworkapplicationcalledELGG,andhostitinthefollowingURL:https://www.
heartbleedlabelgg.
com.
Weneedtomodifythe/etc/hostsleontheattackermachinetomaptheservernametotheIPad-dressoftheserverVM.
Searchthefollowinglinein/etc/hosts,andreplacetheIPaddress127.
0.
0.
1withtheactualIPaddressoftheserverVMthathoststheELGGapplication.
127.
0.
0.
1www.
heartbleedlabelgg.
com3LabTasksBeforeworkingonthelabtasks,youneedtounderstandhowtheheartbeatprotocolworks.
Theheartbeatprotocolconsistsoftwomessagetypes:HeartbeatRequestpacketandHeartbeatResponsepacket.
ClientsendsaHeartbeatRequestpackettotheserver.
Whentheserverreceivesit,itsendsbackacopyofthereceivedmessageintheHeartbeatResponsepacket.
Thegoalistokeeptheconnectionalive.
TheprotocolisillustratedinFigure1.
SEEDLabs–HeartbleedAttack2Figure1:OverviewoftheHeartbeatProtocol3.
1Task1:LaunchtheHeartbleedAttack.
Inthistask,studentswilllaunchtheHeartbleedattackonoursocialnetworksiteandseewhatkindofdamagescanbeachieved.
TheactualdamageoftheHeartbleedattackdependsonwhatkindofinformationisstoredintheservermemory.
Iftherehasnotbeenmuchactivityontheserver,youwillnotbeabletostealusefuldata.
Therefore,weneedtointeractwiththewebserveraslegitimateusers.
LetusdoitastheSEEDLabs–HeartbleedAttack3administrator,anddothefollowings:Visithttps://www.
heartbleedlabelgg.
comfromyourbrowser.
Loginasthesiteadministrator.
(UserName:admin;Password:seedelgg)AddBobyasfriend.
(GotoMore->MembersandclickBoby->AddFriend)SendBobyaprivatemessage.
Afteryouhavedoneenoughinteractionaslegitimateusers,youcanlaunchtheattackandseewhatinformationyoucangetoutofthevictimserver.
WritingtheprogramtolaunchtheHeartbleedattackfromscratchisnoteasy,becauseitrequiresthelow-levelknowledgeoftheHeartbeatprotocol.
Fortunately,otherpeoplehavealreadywrittentheattackcode.
Therefore,wewillusetheexistingcodetogainrst-handexperienceintheHeartbleedattack.
Thecodethatweuseiscalledattack.
py,whichwasoriginallywrittenbyJaredStafford.
Wemadesomesmallchangestothecodeforeducationalpurposes.
Youcandownloadthecodefromthelab'swebsite,changeitspermissionsotheleisexecutable.
Youcanthenruntheattackcodeasfollows:$.
/attack.
pywww.
heartbleedlabelgg.
comYoumayneedtoruntheattackcodemultipletimestogetusefuldata.
Tryandseewhetheryoucangetthefollowinginformationfromthetargetserver.
Usernameandpassword.
User'sactivity(whattheuserhasdone).
Theexactcontentoftheprivatemessage.
ForeachpieceofsecretthatyoustealfromtheHeartbleedattack,youneedtoshowthescreen-dumpastheproofandexplainhowyoudidtheattack,andwhatyourobservationsare.
3.
2Task2:FindtheCauseoftheHeartbleedVulnerabilityInthistask,studentswillcomparetheoutcomeofthebenignpacketandthemaliciouspacketsentbytheattackercodetondoutthefundamentalcauseoftheHeartbleedvulnerability.
TheHeartbleedattackisbasedontheHeartbeatrequest.
Thisrequestjustsendssomedatatotheserver,andtheserverwillcopythedatatoitsresponsepacket,soallthedataareechoedback.
Inthenormalcase,supposethattherequestincludes3bytesofdata"ABC",sothelengtheldhasavalue3.
Theserverwillplacethedatainthememory,andcopy3bytesfromthebeginningofthedatatoitsresponsepacket.
Intheattackscenario,therequestmaycontain3bytesofdata,butthelengtheldmaysay1003.
Whentheserverconstructsitsresponsepacket,itcopiesfromthestartingofthedata(i.
e.
"ABC"),butitcopies1003bytes,insteadof3bytes.
Theseextra1000typesobviouslydonotcomefromtherequestpacket;theycomefromtheserver'sprivatememory,andtheymaycontainotheruser'sinformation,secretkeys,password,etc.
Inthistask,wewillplaywiththelengtheldoftherequest.
First,let'sunderstandhowtheHeartbeatresponsepacketisbuiltfromFigure2.
WhentheHeartbeatrequestpacketcomes,theserverwillparsethepackettogetthepayloadandthePayloadlengthvalue(whichishighlightedinFigure2).
Here,thepayloadisonlya3-bytestring"ABC"andthePayloadlengthvalueisexactly3.
Theserverprogramwillblindlytakethislengthvaluefromtherequestpacket.
ItthenbuildstheresponsepacketbypointingtoSEEDLabs–HeartbleedAttack4Figure2:TheBenignHeartbeatCommunicationFigure3:TheHeartbleedAttackCommunicationthememorystoring"ABC"andcopyPayloadlengthbytestotheresponsepayload.
Inthisway,theresponsepacketwouldcontaina3-bytestring"ABC".
WecanlaunchtheHeartBleedattacklikewhatisshowninFigure3.
Wekeepthesamepayload(3bytes),butsetthePayloadlengtheldto1003.
TheserverwillagainblindlytakethisPayloadlengthvaluewhenbuildingtheresponsepacket.
Thistime,theserverprogramwillpointtothestring"ABC"andcopy1003bytesfromthememorytotheresponsepacketasapayload.
Besidesthestring"ABC",theextra1000bytesarecopiedintotheresponsepacket,whichcouldbeanythingfromthememory,suchassecretactivity,logginginformation,passwordandsoon.
OurattackcodeallowsyoutoplaywithdifferentPayloadlengthvalues.
Bydefault,thevalueissettoaquitelargeone(0x4000),butyoucanreducethesizeusingthecommandoption"-l"(letterell)SEEDLabs–HeartbleedAttack5or"--length"asshowninthefollowingexamples:$.
/attack.
pywww.
heartbleedlabelgg.
com-l0x015B$.
/attack.
pywww.
heartbleedlabelgg.
com--length83Yourtaskistoplaywiththeattackprogramwithdifferentpayloadlengthvaluesandanswerthefollow-ingquestions:Question2.
1:Asthelengthvariabledecreases,whatkindofdifferencecanyouobserveQuestion2.
2:Asthelengthvariabledecreases,thereisaboundaryvaluefortheinputlengthvari-able.
Atorbelowthatboundary,theHeartbeatquerywillreceivearesponsepacketwithoutattachinganyextradata(whichmeanstherequestisbenign).
Pleasendthatboundarylength.
Youmayneedtotrymanydifferentlengthvaluesuntilthewebserversendsbackthereplywithoutextradata.
Tohelpyouwiththis,whenthenumberofreturnedbytesissmallerthantheexpectedlength,thepro-gramwillprint"ServerprocessedmalformedHeartbeat,butdidnotreturnanyextradata.
"3.
3Task3:CountermeasureandBugFixToxtheHeartbleedvulnerability,thebestwayistoupdatetheOpenSSLlibrarytothenewestversion.
Thiscanbeachievedusingthefollowingcommands.
Itshouldbenotedthatonceitisupdated,itishardtogobacktothevulnerableversion.
Therefore,makesureyouhavenishedtheprevioustasksbeforedoingtheupdate.
YoucanalsotakeasnapshotofyourVMbeforetheupdate.
#sudoapt-getupdate#sudoapt-getupgradeTask3.
1TryyourattackagainafteryouhaveupdatedtheOpenSSLlibrary.
Pleasedescribeyourobser-vations.
Task3.
2TheobjectiveofthistaskistogureouthowtoxtheHeartbleedbuginthesourcecode.
ThefollowingC-stylestructure(notexactlythesameasthesourcecode)istheformatoftheHeartbeatrequest/responsepacket.
struct{HeartbeatMessageTypetype;//1byte:requestortheresponseuint16payload_length;//2byte:thelengthofthepayloadopaquepayload[HeartbeatMessage.
payload_length];opaquepadding[padding_length];}HeartbeatMessage;Thersteld(1byte)ofthepacketisthetypeinformation,andthesecondeld(2bytes)isthepayloadlength,followedbytheactualpayloadandpaddings.
Thesizeofthepayloadshouldbethesameasthevalueinthepayloadlengtheld,butintheattackscenario,payloadlengthcanbesettoadifferentvalue.
Thefollowingcodesnippetshowshowtheservercopiesthedatafromtherequestpackettotheresponsepacket.
SEEDLabs–HeartbleedAttack6Listing1:ProcesstheHeartbeatrequestpacketandgeneratetheresponsepacket1/*Allocatememoryfortheresponse,sizeis1byte2*messagetype,plus2bytespayloadlength,plus3*payload,pluspadding4*/56unsignedintpayload;7unsignedintpadding=16;/*Useminimumpadding*/89//Readfromtypefieldfirst10hbtype=*p++;/*Afterthisinstruction,thepointer11*pwillpointtothepayload_lengthfield*.
1213//Readfromthepayload_lengthfield14//fromtherequestpacket15n2s(p,payload);/*Functionn2s(p,payload)reads16bits16*frompointerpandstorethevalue17*intheINTvariable"payload".
*/181920pl=p;//plpointstothebeginningofthepayloadcontent2122if(hbtype==TLS1_HB_REQUEST)23{24unsignedchar*buffer,*bp;25intr;2627/*Allocatememoryfortheresponse,sizeis1byte28*messagetype,plus2bytespayloadlength,plus29*payload,pluspadding30*/3132buffer=OPENSSL_malloc(1+2+payload+padding);33bp=buffer;3435//Enterresponsetype,lengthandcopypayload36*bp++=TLS1_HB_RESPONSE;37s2n(payload,bp);3839//copypayload40memcpy(bp,pl,payload);/*plisthepointerwhich41*pointstothebeginning42*ofthepayloadcontent*/4344bp+=payload;4546//Randompadding47RAND_pseudo_bytes(bp,padding);4849//thisfunctionwillcopythe3+payload+paddingbytes50//fromthebufferandputthemintotheheartbeatresponse51//packettosendbacktotherequestclientside.
52OPENSSL_free(buffer);SEEDLabs–HeartbleedAttack753r=ssl3_write_bytes(s,TLS1_RT_HEARTBEAT,buffer,543+payload+padding);55}PleasepointouttheproblemfromthecodeinListing1andprovideasolutiontoxthebug(i.
e.
,whatmodicationisneededtoxthebug).
Youdonotneedtorecompilethecode;justdescribehowyoucanxtheprobleminyourlabreport.
Moreover,pleasecommentonthefollowingdiscussionsbyAlice,Bob,andEvaregardingthefunda-mentalcauseoftheHeartbleedvulnerability:Alicethinksthefundamentalcauseismissingtheboundarycheckingduringthebuffercopy;Bobthinksthecauseismissingtheuserinputvalidation;Evathinksthatwecanjustdeletethelengthvaluefromthepackettosolveeverything.
4SubmissionStudentsneedtosubmitadetailedlabreporttodescribewhattheyhavedoneandwhattheyhaveobserved.
Reportshouldincludetheevidencestosupporttheobservations.
Evidencesincludepackettraces,screendumps,etc.
References[1]Heartbleedattack-Implementation:https://alexandreborgesbrazil.
les.
wordpress.
com/2014/04/hearbleedattackversiona1.
pdf[2]Heartbleedattack-Interestingexplanation:http://xkcd.
com/1354/
ThedevelopmentofthisdocumentwaspartiallyfundedbytheNationalScienceFoundationunderAwardNo.
1303306and1318814.
ThisworkislicensedunderaCreativeCommonsAttribution-NonCommercial-ShareAlike4.
0InternationalLicense.
Ahuman-readablesummaryof(andnotasubstitutefor)thelicenseisthefollowing:Youarefreetocopyandredistributethematerialinanymediumorformat.
Youmustgiveappropriatecredit.
Ifyouremix,transform,orbuilduponthematerial,youmustdistributeyourcontributionsunderthesamelicenseastheoriginal.
Youmaynotusethematerialforcommercialpurposes.
1OverviewTheHeartbleedbug(CVE-2014-0160)isasevereimplementationawintheOpenSSLlibrary,whichen-ablesattackerstostealdatafromthememoryofthevictimserver.
Thecontentsofthestolendatadependonwhatisthereinthememoryoftheserver.
Itcouldpotentiallycontainprivatekeys,TLSsessionkeys,usernames,passwords,creditcards,etc.
ThevulnerabilityisintheimplementationoftheHeartbeatprotocol,whichisusedbySSL/TLStokeeptheconnectionalive.
Theobjectiveofthislabisforstudentstounderstandhowseriousthisvulnerabilityis,howtheattackworks,andhowtoxtheproblem.
TheaffectedOpenSSLversionrangeisfrom1.
0.
1to1.
0.
1f.
TheversioninourUbuntuVMis1.
0.
1.
2LabEnvironmentInthislab,weneedtosetuptwoVMs:onecalledattackermachineandtheothercalledvictimserver.
Weusethepre-builtSEEDUbuntu12.
04VM.
TheVMsneedtousetheNAT-Networkadapterforthenetworksetting.
ThiscanbedonebygoingtotheVMsettings,pickingNetwork,andclickingtheAdaptortagtoswitchtheadaptertoNAT-Network.
MakesurebothVMsareonthesameNAT-Network.
ThewebsiteusedinthisattackcanbeanyHTTPSwebsitethatusesSSL/TLS.
However,sinceitisillegaltoattackarealwebsite,wehavesetupawebsiteinourVM,andconducttheattackonourownVM.
Weuseanopen-sourcesocialnetworkapplicationcalledELGG,andhostitinthefollowingURL:https://www.
heartbleedlabelgg.
com.
Weneedtomodifythe/etc/hostsleontheattackermachinetomaptheservernametotheIPad-dressoftheserverVM.
Searchthefollowinglinein/etc/hosts,andreplacetheIPaddress127.
0.
0.
1withtheactualIPaddressoftheserverVMthathoststheELGGapplication.
127.
0.
0.
1www.
heartbleedlabelgg.
com3LabTasksBeforeworkingonthelabtasks,youneedtounderstandhowtheheartbeatprotocolworks.
Theheartbeatprotocolconsistsoftwomessagetypes:HeartbeatRequestpacketandHeartbeatResponsepacket.
ClientsendsaHeartbeatRequestpackettotheserver.
Whentheserverreceivesit,itsendsbackacopyofthereceivedmessageintheHeartbeatResponsepacket.
Thegoalistokeeptheconnectionalive.
TheprotocolisillustratedinFigure1.
SEEDLabs–HeartbleedAttack2Figure1:OverviewoftheHeartbeatProtocol3.
1Task1:LaunchtheHeartbleedAttack.
Inthistask,studentswilllaunchtheHeartbleedattackonoursocialnetworksiteandseewhatkindofdamagescanbeachieved.
TheactualdamageoftheHeartbleedattackdependsonwhatkindofinformationisstoredintheservermemory.
Iftherehasnotbeenmuchactivityontheserver,youwillnotbeabletostealusefuldata.
Therefore,weneedtointeractwiththewebserveraslegitimateusers.
LetusdoitastheSEEDLabs–HeartbleedAttack3administrator,anddothefollowings:Visithttps://www.
heartbleedlabelgg.
comfromyourbrowser.
Loginasthesiteadministrator.
(UserName:admin;Password:seedelgg)AddBobyasfriend.
(GotoMore->MembersandclickBoby->AddFriend)SendBobyaprivatemessage.
Afteryouhavedoneenoughinteractionaslegitimateusers,youcanlaunchtheattackandseewhatinformationyoucangetoutofthevictimserver.
WritingtheprogramtolaunchtheHeartbleedattackfromscratchisnoteasy,becauseitrequiresthelow-levelknowledgeoftheHeartbeatprotocol.
Fortunately,otherpeoplehavealreadywrittentheattackcode.
Therefore,wewillusetheexistingcodetogainrst-handexperienceintheHeartbleedattack.
Thecodethatweuseiscalledattack.
py,whichwasoriginallywrittenbyJaredStafford.
Wemadesomesmallchangestothecodeforeducationalpurposes.
Youcandownloadthecodefromthelab'swebsite,changeitspermissionsotheleisexecutable.
Youcanthenruntheattackcodeasfollows:$.
/attack.
pywww.
heartbleedlabelgg.
comYoumayneedtoruntheattackcodemultipletimestogetusefuldata.
Tryandseewhetheryoucangetthefollowinginformationfromthetargetserver.
Usernameandpassword.
User'sactivity(whattheuserhasdone).
Theexactcontentoftheprivatemessage.
ForeachpieceofsecretthatyoustealfromtheHeartbleedattack,youneedtoshowthescreen-dumpastheproofandexplainhowyoudidtheattack,andwhatyourobservationsare.
3.
2Task2:FindtheCauseoftheHeartbleedVulnerabilityInthistask,studentswillcomparetheoutcomeofthebenignpacketandthemaliciouspacketsentbytheattackercodetondoutthefundamentalcauseoftheHeartbleedvulnerability.
TheHeartbleedattackisbasedontheHeartbeatrequest.
Thisrequestjustsendssomedatatotheserver,andtheserverwillcopythedatatoitsresponsepacket,soallthedataareechoedback.
Inthenormalcase,supposethattherequestincludes3bytesofdata"ABC",sothelengtheldhasavalue3.
Theserverwillplacethedatainthememory,andcopy3bytesfromthebeginningofthedatatoitsresponsepacket.
Intheattackscenario,therequestmaycontain3bytesofdata,butthelengtheldmaysay1003.
Whentheserverconstructsitsresponsepacket,itcopiesfromthestartingofthedata(i.
e.
"ABC"),butitcopies1003bytes,insteadof3bytes.
Theseextra1000typesobviouslydonotcomefromtherequestpacket;theycomefromtheserver'sprivatememory,andtheymaycontainotheruser'sinformation,secretkeys,password,etc.
Inthistask,wewillplaywiththelengtheldoftherequest.
First,let'sunderstandhowtheHeartbeatresponsepacketisbuiltfromFigure2.
WhentheHeartbeatrequestpacketcomes,theserverwillparsethepackettogetthepayloadandthePayloadlengthvalue(whichishighlightedinFigure2).
Here,thepayloadisonlya3-bytestring"ABC"andthePayloadlengthvalueisexactly3.
Theserverprogramwillblindlytakethislengthvaluefromtherequestpacket.
ItthenbuildstheresponsepacketbypointingtoSEEDLabs–HeartbleedAttack4Figure2:TheBenignHeartbeatCommunicationFigure3:TheHeartbleedAttackCommunicationthememorystoring"ABC"andcopyPayloadlengthbytestotheresponsepayload.
Inthisway,theresponsepacketwouldcontaina3-bytestring"ABC".
WecanlaunchtheHeartBleedattacklikewhatisshowninFigure3.
Wekeepthesamepayload(3bytes),butsetthePayloadlengtheldto1003.
TheserverwillagainblindlytakethisPayloadlengthvaluewhenbuildingtheresponsepacket.
Thistime,theserverprogramwillpointtothestring"ABC"andcopy1003bytesfromthememorytotheresponsepacketasapayload.
Besidesthestring"ABC",theextra1000bytesarecopiedintotheresponsepacket,whichcouldbeanythingfromthememory,suchassecretactivity,logginginformation,passwordandsoon.
OurattackcodeallowsyoutoplaywithdifferentPayloadlengthvalues.
Bydefault,thevalueissettoaquitelargeone(0x4000),butyoucanreducethesizeusingthecommandoption"-l"(letterell)SEEDLabs–HeartbleedAttack5or"--length"asshowninthefollowingexamples:$.
/attack.
pywww.
heartbleedlabelgg.
com-l0x015B$.
/attack.
pywww.
heartbleedlabelgg.
com--length83Yourtaskistoplaywiththeattackprogramwithdifferentpayloadlengthvaluesandanswerthefollow-ingquestions:Question2.
1:Asthelengthvariabledecreases,whatkindofdifferencecanyouobserveQuestion2.
2:Asthelengthvariabledecreases,thereisaboundaryvaluefortheinputlengthvari-able.
Atorbelowthatboundary,theHeartbeatquerywillreceivearesponsepacketwithoutattachinganyextradata(whichmeanstherequestisbenign).
Pleasendthatboundarylength.
Youmayneedtotrymanydifferentlengthvaluesuntilthewebserversendsbackthereplywithoutextradata.
Tohelpyouwiththis,whenthenumberofreturnedbytesissmallerthantheexpectedlength,thepro-gramwillprint"ServerprocessedmalformedHeartbeat,butdidnotreturnanyextradata.
"3.
3Task3:CountermeasureandBugFixToxtheHeartbleedvulnerability,thebestwayistoupdatetheOpenSSLlibrarytothenewestversion.
Thiscanbeachievedusingthefollowingcommands.
Itshouldbenotedthatonceitisupdated,itishardtogobacktothevulnerableversion.
Therefore,makesureyouhavenishedtheprevioustasksbeforedoingtheupdate.
YoucanalsotakeasnapshotofyourVMbeforetheupdate.
#sudoapt-getupdate#sudoapt-getupgradeTask3.
1TryyourattackagainafteryouhaveupdatedtheOpenSSLlibrary.
Pleasedescribeyourobser-vations.
Task3.
2TheobjectiveofthistaskistogureouthowtoxtheHeartbleedbuginthesourcecode.
ThefollowingC-stylestructure(notexactlythesameasthesourcecode)istheformatoftheHeartbeatrequest/responsepacket.
struct{HeartbeatMessageTypetype;//1byte:requestortheresponseuint16payload_length;//2byte:thelengthofthepayloadopaquepayload[HeartbeatMessage.
payload_length];opaquepadding[padding_length];}HeartbeatMessage;Thersteld(1byte)ofthepacketisthetypeinformation,andthesecondeld(2bytes)isthepayloadlength,followedbytheactualpayloadandpaddings.
Thesizeofthepayloadshouldbethesameasthevalueinthepayloadlengtheld,butintheattackscenario,payloadlengthcanbesettoadifferentvalue.
Thefollowingcodesnippetshowshowtheservercopiesthedatafromtherequestpackettotheresponsepacket.
SEEDLabs–HeartbleedAttack6Listing1:ProcesstheHeartbeatrequestpacketandgeneratetheresponsepacket1/*Allocatememoryfortheresponse,sizeis1byte2*messagetype,plus2bytespayloadlength,plus3*payload,pluspadding4*/56unsignedintpayload;7unsignedintpadding=16;/*Useminimumpadding*/89//Readfromtypefieldfirst10hbtype=*p++;/*Afterthisinstruction,thepointer11*pwillpointtothepayload_lengthfield*.
1213//Readfromthepayload_lengthfield14//fromtherequestpacket15n2s(p,payload);/*Functionn2s(p,payload)reads16bits16*frompointerpandstorethevalue17*intheINTvariable"payload".
*/181920pl=p;//plpointstothebeginningofthepayloadcontent2122if(hbtype==TLS1_HB_REQUEST)23{24unsignedchar*buffer,*bp;25intr;2627/*Allocatememoryfortheresponse,sizeis1byte28*messagetype,plus2bytespayloadlength,plus29*payload,pluspadding30*/3132buffer=OPENSSL_malloc(1+2+payload+padding);33bp=buffer;3435//Enterresponsetype,lengthandcopypayload36*bp++=TLS1_HB_RESPONSE;37s2n(payload,bp);3839//copypayload40memcpy(bp,pl,payload);/*plisthepointerwhich41*pointstothebeginning42*ofthepayloadcontent*/4344bp+=payload;4546//Randompadding47RAND_pseudo_bytes(bp,padding);4849//thisfunctionwillcopythe3+payload+paddingbytes50//fromthebufferandputthemintotheheartbeatresponse51//packettosendbacktotherequestclientside.
52OPENSSL_free(buffer);SEEDLabs–HeartbleedAttack753r=ssl3_write_bytes(s,TLS1_RT_HEARTBEAT,buffer,543+payload+padding);55}PleasepointouttheproblemfromthecodeinListing1andprovideasolutiontoxthebug(i.
e.
,whatmodicationisneededtoxthebug).
Youdonotneedtorecompilethecode;justdescribehowyoucanxtheprobleminyourlabreport.
Moreover,pleasecommentonthefollowingdiscussionsbyAlice,Bob,andEvaregardingthefunda-mentalcauseoftheHeartbleedvulnerability:Alicethinksthefundamentalcauseismissingtheboundarycheckingduringthebuffercopy;Bobthinksthecauseismissingtheuserinputvalidation;Evathinksthatwecanjustdeletethelengthvaluefromthepackettosolveeverything.
4SubmissionStudentsneedtosubmitadetailedlabreporttodescribewhattheyhavedoneandwhattheyhaveobserved.
Reportshouldincludetheevidencestosupporttheobservations.
Evidencesincludepackettraces,screendumps,etc.
References[1]Heartbleedattack-Implementation:https://alexandreborgesbrazil.
les.
wordpress.
com/2014/04/hearbleedattackversiona1.
pdf[2]Heartbleedattack-Interestingexplanation:http://xkcd.
com/1354/
- tasksubuntu12.04相关文档
- 谈判ubuntu12.04
- 濮阳市政府采购招标文件编号:PC[2017]164----豫盛华采字GK第102号货物类公开招标文件项目名称:物联网实训室设备
- individualubuntu12.04
- TXubuntu12.04
- 语料ubuntu12.04
- updatedubuntu12.04
wordpress外贸企业主题 wordpress经典外贸企业建站主题
WordPress经典外贸企业建站主题,经典配色扁平化简约设计+跨屏自适应移动端设备,特色外贸企业建站功能模块+在线Inquiry询单功能,更有利于Google等英文搜索优化和站点收录。采用标准的HTML5+CSS3语言开发,兼容当下的各种主流浏览器: IE 6+(以及类似360、遨游等基于IE内核的)、Firefox、Google Chrome、Safari、Opera等;同时支持移动终端的常用...
标准互联(450元)襄阳电信100G防御服务器 10M独立带宽
目前在标准互联这边有两台香港云服务器产品,这不看到有通知到期提醒才关注到。平时我还是很少去登录这个服务商的,这个服务商最近一年的促销信息比较少,这个和他们的运营策略有关系。已经从开始的倾向低价和个人用户云服务器市场,开始转型到中高端个人和企业用户的独立服务器。在这篇文章中,有看到标准互联有推出襄阳电信高防服务器100GB防御。有三款促销方案我们有需要可以看看。我们看看几款方案配置。型号内存硬盘IP...
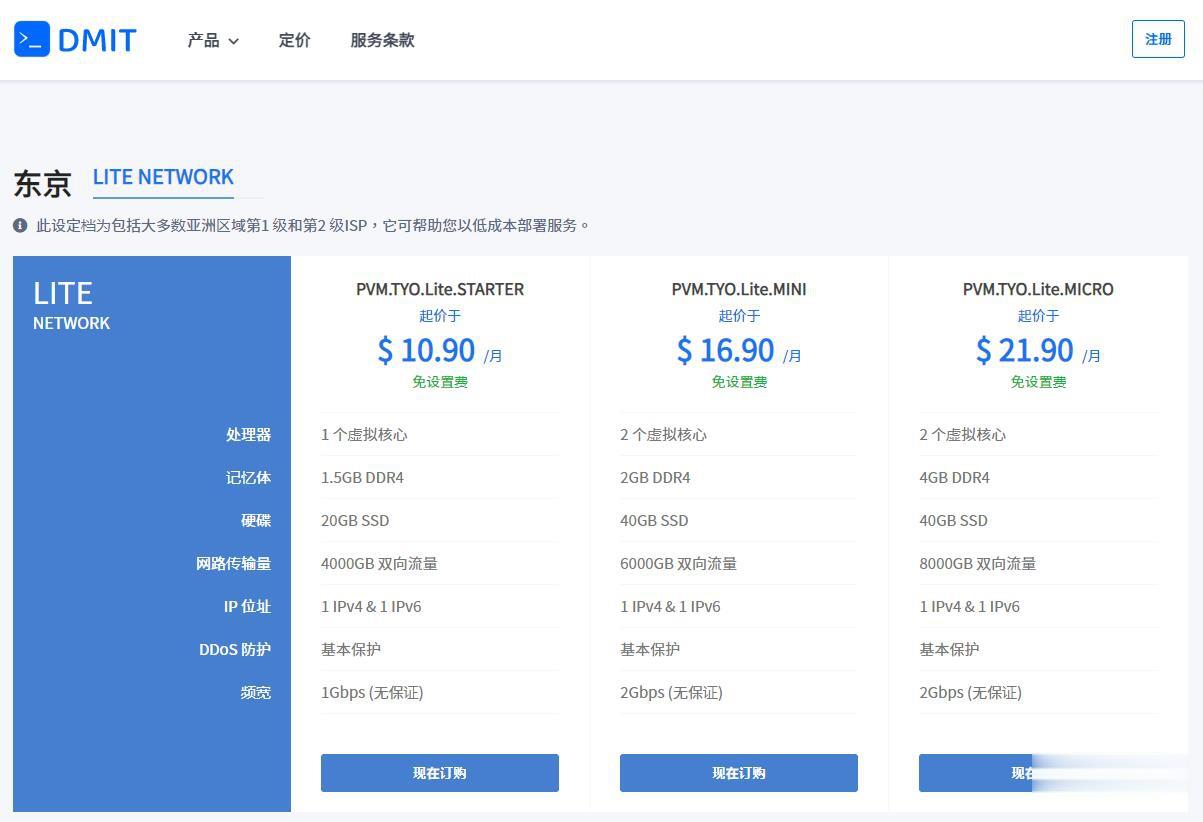
DMIT$10.9/月,日本VPS/三网直连/1核1.5G内存/20GB存储/1Gbps端口
优惠码年付一次性5折优惠码:TYO-Lite-Open-Beta-1y-50OFF永久8折优惠码:TYO-Lite-Open-Beta-Recur-20OFF日本vpsCPU内存SSD流量带宽价格购买1核1.5G20 GB4 TB1Gbps$10.9/月购买2核2 G40 GB6 TB1Gbps$16.9/月购买2核4 G60 GB8 TB1Gbps$21.9/月购买4核4 G80 GB12 TB...
ubuntu12.04为你推荐
-
网易网盘关闭入口如何快速开通网易网盘?摩拜超15分钟加钱摩拜单车免费卡和5元90天能叠加吗甲骨文不满赔偿未签合同被辞退的赔偿百度关键词分析关键词怎么分析?www.qq530.com谁能给我一个听歌的网站?porntimesexy time 本兮 MP3地址yinrentangWeichentang正品怎么样,谁知道?66smsm.comwww.zpwbj.com 这个网址是真的吗?我想知道它的真实性.......谢谢 我就剩50了,都给你了..............xvideos..comxvideos 怎么下载www.jsjtxx.com怎样让电脑安全又高速