server隐士ddos
隐士ddos 时间:2021-01-13 阅读:()
DetectingDDoSattackbasedonPSOClusteringalgorithmXiaohongHao1,a,BoyuMeng1,b,KaichengGu1,c1SchoolofComputer&Communication,LanZhouUniversityofTechnology,Lanzhou730050a;316475958@qq.
combboyu8816@163.
com;cgkc1314@qq.
comKeyword:application-tierDistributedDenialofService;browsebehavior;particleclusteringalgorithm;anomalydetection.
Abstract.
First,thisarticleanalyzestheApplicationlayerDistributedDenialofService(DDoS)'sattackprincipleandcharacteristic.
Accordingtothedifferencebetweennormalusers'browsingpatternsandabnormalones,usersessionsareextractedfromtheweblogsofnormalusersandsimilaritiesbetweendifferentsessionsarecalculated.
BecausetraditionalK-meanClusteringalgorithmiseasytofailintolocaloptimal,theParticleSwarmOptimizationK-meanClusteringalgorithmisusedtogenerateadetectingmodel.
ThismodelcanbeenusedtodetectwhethertheundeterminedsessionsareDDoSattacksornot.
Theexperimentshowthatthismethodcandetectattackseffectivelyandhaveagoodperformanceinadaptability.
IntroductionDistributeddenialofserviceattacksisoneofthemajorthreatstothesecurityoftheInternet,whichintheabsenceofanywarningconsumeresourcesofthetarget,itcanbemadeatthenetworklayerorapplicationlayer[1].
ApplicationlayerDDoShavetwoattackmethods[2]:bandwidthdepletionmodeandthehostresourcedepletionmode.
Atpresent,methodstosolvethesesimilarproblemincluding:Intrusiondetectiontechnologybasedondatapacket[3]Detectionmethodbasedonflowlimitation[4],Detectionmethodbasedonfrequencyofaccess[5],DetectionmethodbasedonHiddensemi-Markovmodel[6],Detectionmethodbasedontheanalysisofuserbehaviordatamining[7].
Theliterature[8]proposesanewDosdetectionbasedondatamining,whichcombinedApriorialgorithmandk-meanclusteringalgorithm.
ItusingnetworkdatatodetectDDoS,soitcannotcopewiththeapplicationlayerDDos.
Thek-meanalgorithmhaveitselfflawed,itoverlyneedtoselectthefitclustercentersandforsomeinitialvalue,itmayconvergetosub-optimalsolution.
ApplicationlayerDDoSdetectionbasedonPSOclusteringalgorithmPrincipleandmodelofdetection:ThispaperestablishdetectionmodelwhichisusingtoidentifytheapplicationlayerDDoSformanalysisuserbehavior.
SystemdesignasshowninFigure1.
Figure1.
systemmoduledesignDescriptionofuserbrowsingbehaviorTheWeblogrecordsinformationabouteachuseraccesstotheserver,itincludingtheuser'sIPaddress,client,customeridentification,timeofWebserverreceivestherequest,customerrequests,requeststatuscode,transmittedbytessuchassomeaccessdata.
ExtractWeblog,preprocesstheinformationandtranslatetheresultsintoSession:1122{,,u,,u,,,u}kkiiSipttt(1)CalculatethedistancebetweensessionsInordertomoreaccuratelydescribetheuserbrowsingbehavior,betterreflectsthenormallegitimateusersandanomalyattacksusersbrowseaccesstothedifferenceinbehavior,soanalysisthesimilaritiesanddifferencesincontent,time,page-viewsandsequence.
Thispaperrefertothemethodwhichusethreevectorsandamatrixtodetaileddescripttheuser'ssessionfeatures.
Thencalculatethesimilaritybetweensession,themoresimilaritythedistancemoresmall.
Sotheabstractdistancecanbedefinedas1d=.
Definition1(contentvector):12(w,w,,w)knW,lengthofthevectorisn.
Itindicatestheservercontainspagenumber.
Theformulaisasfollows:[1,n](W,W)(W,W)iipqipqn()()(2)Definition2(timevector):12(t,t,,t)knT1,lengthofthevectorisn.
Itofuserbrowsingpagei.
Thesimilarityformulaoftwohitvectorsisasfollows:(T,T)1d(T,T)pqpq(3)Definition3(hitvector):12(hit,hit,,hit)knHit,lengthofthevectorisn.
Itindicatestimesnumberofauserbrowsapage,itreflectstheuser'sinterestdegreeeachpages.
(Hit,Hit)1d(Hit,Hit)pqpq(4)Definition4(sequencematrix):kHisannmatrix,itrecordsthenumberoftimesofjumpingbetweenthevariouspagesinthesession.
Thesimilarityformulaoftwotimevectorsisasfollows:(i,j)(i,j)(1,n)(1,n)2(H,H)(H,H)pqijpqn(5)Consideringthesimilaritybetweenthreevectorandamatrix,theoverallsimilarity(S,S)pq,isasfollows:(W,W)(T,T)(Hit,Hit)(H,H)(S,S)4pqpqpqpqpq(6)Numericallygreater,thesessionaremoresimilar,thedistancebetweentheresessionsissmaller.
Sothedistanceisasfollows:Theformulaisasfollow1d(S,S)(S,S)pqpq(7)DetectionofattacksTheSessionsisdefinedas,{Si1,2,N}iS,,SiisaN-dimensionalpatternvector.
Thesolutionistodivide12M1,letthetotaldispersionoftheallclusterstobeminimum.
Thetotaldistanceofallsamplestothecorrespondingcluster'scentersisminimum.
Theformulaisasfollow:()1(S,)jijMijXJdS(8)()Sjisthecluster'scenterj,()(S,S)jidisthedistancebetweenthesampleandthecluster'scenterj.
PSOClusteringalgorithmThispaperconsiderthecluster'scenterasaparticle'scorrespondedsolution,theparticle'slocationiscombinedwithcluster'scenter.
TherearetwoformsofapplicationlayerDDoSattacksandnormaluser,sothenumberofclustersisM=3.
Algorithmflowchartisasfollows:idPgdPgdPFigure2.
FlowchartPSOclusteringalgorithmExperimentalresultsandanalysisThispaperusethedatafromCentralSouthUniversity'svisualresearchgroup.
TForthelargeamountsofthedata,thepaperrandomlycollect100sampleand20attacksampledatafromtheWeblogofuseraaccesslogs.
ProgramdevelopmentplatformisMATLAB2014a.
TheclusteranalysisresultsinFigure3.
DatSkItcanbattacksnumaccesstoleanalysis,thConclusioThispapapplicationalgorithmexceptionbehavior,dbetweeneaSimulationperformancReference[1]Fenapplication[2]Chulayer[D].
C[3]Douate-of-art[J[4]Sunacks[J].
AC[5]Mu].
Journalo[6]YiGuangdongtaSessiok120beseenthatmberslightegitimateusheaccuracynperanalysisnlayerDDanddescribaccessbehadescribetheachsession,nexperimenceinadaptaesnYan,Jiajian,2008,25uanXu.
ResChongqingugligerisC,J],ComputenChang-huCTEElectrouthuprasannofSoftwareXie.
Researg:SunYatFigure3.
onActualtmodeldetlymorethaser'sbehaviywillbeincstheprincipDoSattacksbeuser'sbeavior,accoreuser'sbrothendetectntsshowthability.
aWang,Jinfe(4):966searchandiUniversity,,MitrokotsaerNetwork,a,LiuBin.
onicaSINCnaM,Manim.
2007,4(18rchonkey-senUniveClusteringTablattackSess20tectionrateannumberoior.
IfincreareasedaccoplesandchadetectionmehaviorofbrdingtotheowsingbehattheattackshatthismeengZhao.
D-969.
mplementat,2012.
aA.
DDoS,2004,(44):SurveyonNCA.
2009,7(maranG.
Di8):967-977technologyersity,2008resultsofEle1ClusteriionDeteisabout86ofactualatasetheamouordingly.
aracteristicsmethodwhbrowsingWedifferenceaviorbydasbehaviorbethodcandDDoSattackationofDDoattacksand643-666.
NewSolutio(37):1562-1istributedByofHTTP8Euclideanspingresultsectingattack236%fromthtacksistheuntofthedofapplicatihichisbaseWebpages.
oflegitimaataminingtbyusingPardetectattackdetectionoSattackdeddefencesmonAgainst1570.
BasedonWeattackdetecpaceprojectkSessionheTable1.
emodelcanata,aftercoionlayerDDedonPartiConsiderthateandabnotechnique,cticleSwarmckseffectivnsummary[etectionalgmachanismsDistributedebUser'sBctiononapptionAccuracy86%ThereasonnnotreflectorrespondingDoSattacksicleSwarmheattacksanormaluser'calculatethmClusteringvelyandha[J].
Studyongorithmson:ClassificadDenialofSBrowsingBeplication-rate%nofdetectstallnormalgclusterings,provideaClusteringasanuser's'sbrowsingesimilaritygalgorithm.
aveagoodncomputerapplicationationandstServiceAttehaviours[Jlayer[D].
slgagsgy.
drn.
[7]FengyuWang,ShoufengCao,JunXiao.
ADDoSdetectionmethodofcommunityoutreachbasedonWebapplicationlayer[J].
Journalofsoftware,2013,24(6):1263-1273.
[8]NengGao,DengguoFeng,.
ADOSattackdetectionbasedondataminingtechnology[J].
ChineseJournalofComputers,2006,29(6):944-950
combboyu8816@163.
com;cgkc1314@qq.
comKeyword:application-tierDistributedDenialofService;browsebehavior;particleclusteringalgorithm;anomalydetection.
Abstract.
First,thisarticleanalyzestheApplicationlayerDistributedDenialofService(DDoS)'sattackprincipleandcharacteristic.
Accordingtothedifferencebetweennormalusers'browsingpatternsandabnormalones,usersessionsareextractedfromtheweblogsofnormalusersandsimilaritiesbetweendifferentsessionsarecalculated.
BecausetraditionalK-meanClusteringalgorithmiseasytofailintolocaloptimal,theParticleSwarmOptimizationK-meanClusteringalgorithmisusedtogenerateadetectingmodel.
ThismodelcanbeenusedtodetectwhethertheundeterminedsessionsareDDoSattacksornot.
Theexperimentshowthatthismethodcandetectattackseffectivelyandhaveagoodperformanceinadaptability.
IntroductionDistributeddenialofserviceattacksisoneofthemajorthreatstothesecurityoftheInternet,whichintheabsenceofanywarningconsumeresourcesofthetarget,itcanbemadeatthenetworklayerorapplicationlayer[1].
ApplicationlayerDDoShavetwoattackmethods[2]:bandwidthdepletionmodeandthehostresourcedepletionmode.
Atpresent,methodstosolvethesesimilarproblemincluding:Intrusiondetectiontechnologybasedondatapacket[3]Detectionmethodbasedonflowlimitation[4],Detectionmethodbasedonfrequencyofaccess[5],DetectionmethodbasedonHiddensemi-Markovmodel[6],Detectionmethodbasedontheanalysisofuserbehaviordatamining[7].
Theliterature[8]proposesanewDosdetectionbasedondatamining,whichcombinedApriorialgorithmandk-meanclusteringalgorithm.
ItusingnetworkdatatodetectDDoS,soitcannotcopewiththeapplicationlayerDDos.
Thek-meanalgorithmhaveitselfflawed,itoverlyneedtoselectthefitclustercentersandforsomeinitialvalue,itmayconvergetosub-optimalsolution.
ApplicationlayerDDoSdetectionbasedonPSOclusteringalgorithmPrincipleandmodelofdetection:ThispaperestablishdetectionmodelwhichisusingtoidentifytheapplicationlayerDDoSformanalysisuserbehavior.
SystemdesignasshowninFigure1.
Figure1.
systemmoduledesignDescriptionofuserbrowsingbehaviorTheWeblogrecordsinformationabouteachuseraccesstotheserver,itincludingtheuser'sIPaddress,client,customeridentification,timeofWebserverreceivestherequest,customerrequests,requeststatuscode,transmittedbytessuchassomeaccessdata.
ExtractWeblog,preprocesstheinformationandtranslatetheresultsintoSession:1122{,,u,,u,,,u}kkiiSipttt(1)CalculatethedistancebetweensessionsInordertomoreaccuratelydescribetheuserbrowsingbehavior,betterreflectsthenormallegitimateusersandanomalyattacksusersbrowseaccesstothedifferenceinbehavior,soanalysisthesimilaritiesanddifferencesincontent,time,page-viewsandsequence.
Thispaperrefertothemethodwhichusethreevectorsandamatrixtodetaileddescripttheuser'ssessionfeatures.
Thencalculatethesimilaritybetweensession,themoresimilaritythedistancemoresmall.
Sotheabstractdistancecanbedefinedas1d=.
Definition1(contentvector):12(w,w,,w)knW,lengthofthevectorisn.
Itindicatestheservercontainspagenumber.
Theformulaisasfollows:[1,n](W,W)(W,W)iipqipqn()()(2)Definition2(timevector):12(t,t,,t)knT1,lengthofthevectorisn.
Itofuserbrowsingpagei.
Thesimilarityformulaoftwohitvectorsisasfollows:(T,T)1d(T,T)pqpq(3)Definition3(hitvector):12(hit,hit,,hit)knHit,lengthofthevectorisn.
Itindicatestimesnumberofauserbrowsapage,itreflectstheuser'sinterestdegreeeachpages.
(Hit,Hit)1d(Hit,Hit)pqpq(4)Definition4(sequencematrix):kHisannmatrix,itrecordsthenumberoftimesofjumpingbetweenthevariouspagesinthesession.
Thesimilarityformulaoftwotimevectorsisasfollows:(i,j)(i,j)(1,n)(1,n)2(H,H)(H,H)pqijpqn(5)Consideringthesimilaritybetweenthreevectorandamatrix,theoverallsimilarity(S,S)pq,isasfollows:(W,W)(T,T)(Hit,Hit)(H,H)(S,S)4pqpqpqpqpq(6)Numericallygreater,thesessionaremoresimilar,thedistancebetweentheresessionsissmaller.
Sothedistanceisasfollows:Theformulaisasfollow1d(S,S)(S,S)pqpq(7)DetectionofattacksTheSessionsisdefinedas,{Si1,2,N}iS,,SiisaN-dimensionalpatternvector.
Thesolutionistodivide12M1,letthetotaldispersionoftheallclusterstobeminimum.
Thetotaldistanceofallsamplestothecorrespondingcluster'scentersisminimum.
Theformulaisasfollow:()1(S,)jijMijXJdS(8)()Sjisthecluster'scenterj,()(S,S)jidisthedistancebetweenthesampleandthecluster'scenterj.
PSOClusteringalgorithmThispaperconsiderthecluster'scenterasaparticle'scorrespondedsolution,theparticle'slocationiscombinedwithcluster'scenter.
TherearetwoformsofapplicationlayerDDoSattacksandnormaluser,sothenumberofclustersisM=3.
Algorithmflowchartisasfollows:idPgdPgdPFigure2.
FlowchartPSOclusteringalgorithmExperimentalresultsandanalysisThispaperusethedatafromCentralSouthUniversity'svisualresearchgroup.
TForthelargeamountsofthedata,thepaperrandomlycollect100sampleand20attacksampledatafromtheWeblogofuseraaccesslogs.
ProgramdevelopmentplatformisMATLAB2014a.
TheclusteranalysisresultsinFigure3.
DatSkItcanbattacksnumaccesstoleanalysis,thConclusioThispapapplicationalgorithmexceptionbehavior,dbetweeneaSimulationperformancReference[1]Fenapplication[2]Chulayer[D].
C[3]Douate-of-art[J[4]Sunacks[J].
AC[5]Mu].
Journalo[6]YiGuangdongtaSessiok120beseenthatmberslightegitimateusheaccuracynperanalysisnlayerDDanddescribaccessbehadescribetheachsession,nexperimenceinadaptaesnYan,Jiajian,2008,25uanXu.
ResChongqingugligerisC,J],ComputenChang-huCTEElectrouthuprasannofSoftwareXie.
Researg:SunYatFigure3.
onActualtmodeldetlymorethaser'sbehaviywillbeincstheprincipDoSattacksbeuser'sbeavior,accoreuser'sbrothendetectntsshowthability.
aWang,Jinfe(4):966searchandiUniversity,,MitrokotsaerNetwork,a,LiuBin.
onicaSINCnaM,Manim.
2007,4(18rchonkey-senUniveClusteringTablattackSess20tectionrateannumberoior.
IfincreareasedaccoplesandchadetectionmehaviorofbrdingtotheowsingbehattheattackshatthismeengZhao.
D-969.
mplementat,2012.
aA.
DDoS,2004,(44):SurveyonNCA.
2009,7(maranG.
Di8):967-977technologyersity,2008resultsofEle1ClusteriionDeteisabout86ofactualatasetheamouordingly.
aracteristicsmethodwhbrowsingWedifferenceaviorbydasbehaviorbethodcandDDoSattackationofDDoattacksand643-666.
NewSolutio(37):1562-1istributedByofHTTP8Euclideanspingresultsectingattack236%fromthtacksistheuntofthedofapplicatihichisbaseWebpages.
oflegitimaataminingtbyusingPardetectattackdetectionoSattackdeddefencesmonAgainst1570.
BasedonWeattackdetecpaceprojectkSessionheTable1.
emodelcanata,aftercoionlayerDDedonPartiConsiderthateandabnotechnique,cticleSwarmckseffectivnsummary[etectionalgmachanismsDistributedebUser'sBctiononapptionAccuracy86%ThereasonnnotreflectorrespondingDoSattacksicleSwarmheattacksanormaluser'calculatethmClusteringvelyandha[J].
Studyongorithmson:ClassificadDenialofSBrowsingBeplication-rate%nofdetectstallnormalgclusterings,provideaClusteringasanuser's'sbrowsingesimilaritygalgorithm.
aveagoodncomputerapplicationationandstServiceAttehaviours[Jlayer[D].
slgagsgy.
drn.
[7]FengyuWang,ShoufengCao,JunXiao.
ADDoSdetectionmethodofcommunityoutreachbasedonWebapplicationlayer[J].
Journalofsoftware,2013,24(6):1263-1273.
[8]NengGao,DengguoFeng,.
ADOSattackdetectionbasedondataminingtechnology[J].
ChineseJournalofComputers,2006,29(6):944-950
- server隐士ddos相关文档
- 联网隐士ddos
- SPCIFICATIONS隐士ddos
- unrelated隐士ddos
- contact隐士ddos
- including隐士ddos
- chiffres隐士ddos
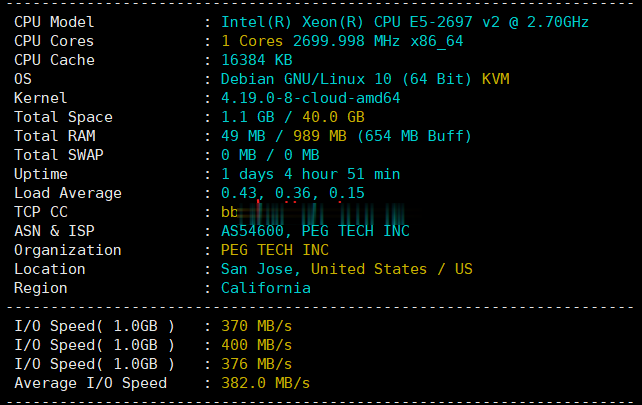
raksmart:全新cloud云服务器系列测评,告诉你raksmart新产品效果好不好
2021年6月底,raksmart开发出来的新产品“cloud-云服务器”正式上线对外售卖,当前只有美国硅谷机房(或许以后会有其他数据中心加入)可供选择。或许你会问raksmart云服务器怎么样啊、raksm云服务器好不好、网络速度快不好之类的废话(不实测的话),本着主机测评趟雷、大家受益的原则,先开一个给大家测评一下!官方网站:https://www.raksmart.com云服务器的说明:底层...
无忧云:洛阳BGP云服务器低至38.4元/月起;雅安高防云服务器/高防物理机优惠
无忧云怎么样?无忧云,无忧云是一家成立于2017年的老牌商家旗下的服务器销售品牌,现由深圳市云上无忧网络科技有限公司运营,是正规持证IDC/ISP/IRCS商家,主要销售国内、中国香港、国外服务器产品,线路有腾讯云国外线路、自营香港CN2线路等,都是中国大陆直连线路,非常适合免备案建站业务需求和各种负载较高的项目,同时国内服务器也有多个BGP以及高防节点。一、无忧云官网点击此处进入无忧云官方网站二...

美国云服务器 1核 1G 30M 50元/季 兆赫云
【双十二】兆赫云:全场vps季付六折优惠,低至50元/季,1H/1G/30M/20G数据盘/500G流量/洛杉矶联通9929商家简介:兆赫云是一家国人商家,成立2020年,主要业务是美西洛杉矶联通9929线路VPS,提供虚拟主机、VPS和独立服务器。VPS采用KVM虚拟架构,线路优质,延迟低,稳定性强。是不是觉得黑五折扣力度不够大?还在犹豫徘徊中?这次为了提前庆祝双十二,特价推出全场季付六折优惠。...

隐士ddos为你推荐
-
国内域名注册。中国域名都在哪里可以注册?美国主机空间买空间网的美国主机咋样?网络服务器租用现在网站服务器租赁一年多少钱?com域名空间.com的域名+300M的空间要多少钱?免费虚拟主机申请在哪个网站申请的免费虚拟主机可以绑定顶级域名?求高手指点!域名主机电脑域名是什么台湾vps做一个论坛,请问需要什么样的vps配置域名申请申请域名需要什么条件?具体点!急!急!!!免费网站空间申请哪里有永久免费的域名空间可以申请虚拟主机是什么什么是虚拟主机?