authenticatedapnic
apnic 时间:2021-01-10 阅读:()
IssueDate:Revision:CryptographyApplications:VPNandIPsec30May20152.
0-draftOverviewIntroductiontoVPNIPsecFundamentalsTunnelandTransportModeIPsecArchitectureandComponentsofIPsecInternetKeyExchangeConfiguringIPsecforIPv4andIPv62VirtualPrivateNetworkCreatesasecuretunneloverapublicnetwork–Clienttofirewall–Routertorouter–FirewalltofirewallUsestheInternetasthepublicbackbonetoaccessasecureprivatenetwork–RemoteemployeescanaccesstheirofficenetworkTwotypes:–Remoteaccess–Site-to-siteVPN3VPNImplementationHardware–UsuallyaVPN-typerouter–Pros:highestnetworkthroughput,plugandplay,dualpurpose–Cons:costandlackofflexibilitySoftware–Idealfortwoend-pointsindifferentorganisations–Pros:flexible,andlowrelativecost–Cons:lackofefficiency,morelabortrainingrequired,lowerproductivity;higherlaborcostsFirewall–Pros:costeffective,tri-purpose,hardenstheoperatingsystem–Cons:stillrelativelycostly4VPNProtocolsPPTP(Point-to-PointtunnelingProtocol)–DevelopedbyMicrosofttosecuredial-upconnections–Operatesinthedata-linklayerL2F(Layer2ForwardingProtocol)–DevelopedbyCisco–SimilarasPPTPL2TP(Layer2TunnelingProtocol)–IETFstandard–CombinesthefunctionalityofPPTPandL2FIPsec(InternetProtocolSecurity)–OpenstandardforVPNimplementation–Operatesonthenetworklayer5OtherModernVPNsMPLSVPN–Usedforlargeandsmallenterprises–Pseudowire,VPLS,VPRNGRETunnel–PacketencapsulationprotocoldevelopedbyCisco–Notencrypted–ImplementedwithIPsecL2TPIPsec–UsesL2TPprotocol–UsuallyimplementedalongwithIPsec–IPsecprovidesthesecurechannel,whileL2TPprovidesthetunnel6AdvantagesofVPNCheaperconnection–UsetheInternetconnectioninsteadofaprivateleaselineScalability–Flexibilityofgrowth–EfficiencywithbroadbandtechnologyAvailability–AvailableeverywherethereisanInternetconnection7DisadvantagesofVPNVPNsrequireanin-depthunderstandingofpublicnetworksecurityissuesandproperdeploymentprecautionsAvailabilityandperformancedependsonfactorslargelyoutsideoftheircontrolVPNsneedtoaccommodateprotocolsotherthanIPandexistinginternalnetworktechnology8IPsecProvidesLayer3security(RFC2401)–Transparenttoapplications(noneedforintegratedIPsecsupport)AsetofprotocolsandalgorithmsusedtosecureIPdataatthenetworklayerCombinesdifferentcomponents:–Securityassociations(SA)–Authenticationheaders(AH)–Encapsulatingsecuritypayload(ESP)–InternetKeyExchange(IKE)AsecuritycontextfortheVPNtunnelisestablishedviatheISAKMP9IPSecInternetWhatisIPSecIETFstandardthatenablesencryptedcommunicationbetweenpeers:–Consistsofopenstandardsforsecuringprivatecommunications–Networklayerencryptionensuringdataconfidentiality,integrity,andauthentication–Scalesfromsmalltoverylargenetworks10IPsecStandardsRFC4301"TheIPSecurityArchitecture"–DefinestheoriginalIPsecarchitectureandelementscommontobothAHandESPRFC4302–Definesauthenticationheaders(AH)RFC4303–DefinestheEncapsulatingSecurityPayload(ESP)RFC2408–ISAKMPRFC5996–IKEv2(Sept2010)RFC4835–CryptographicalgorithmimplementationforESPandAH11BenefitsofIPsecConfidentiality–ByencryptingdataIntegrity–RoutersateachendofatunnelcalculatesthechecksumorhashvalueofthedataAuthentication–Signaturesandcertificates–AllthesewhilestillmaintainingtheabilitytoroutethroughexistingIPnetworks"IPsecisdesignedtoprovideinteroperable,highquality,cryptographically-basedsecurityforIPv4andIPv6"-(RFC2401)12BenefitsofIPsecDataintegrityandsourceauthentication–Data"signed"bysenderand"signature"isverifiedbytherecipient–Modificationofdatacanbedetectedbysignature"verification"–Because"signature"isbasedonasharedsecret,itgivessourceauthenticationAnti-replayprotection–Optional;thesendermustprovideitbuttherecipientmayignoreKeymanagement–IKE–sessionnegotiationandestablishment–Sessionsarerekeyedordeletedautomatically–Secretkeysaresecurelyestablishedandauthenticated–Remotepeerisauthenticatedthroughvaryingoptions13DifferentLayersofEncryptionNetworkLayer-IPsecLinkLayerEncryptionApplicationLayer–SSL,PGP,SSH,HTTPS14IPsecModesTunnelMode–EntireIPpacketisencryptedandbecomesthedatacomponentofanew(andlarger)IPpacket.
–FrequentlyusedinanIPsecsite-to-siteVPNTransportMode–IPsecheaderisinsertedintotheIPpacket–Nonewpacketiscreated–Workswellinnetworkswhereincreasingapacket'ssizecouldcauseanissue–Frequentlyusedforremote-accessVPNs15Tunnelvs.
TransportModeIPsecPayloadTCPHeaderIPHeaderWithoutIPsecTransportModeIPsecTunnelModeIPsecPayloadTCPHeaderIPHeaderIPsecHeaderIPHeaderPayloadTCPHeaderIPHeaderIPsecHeaderNewIPHeader16TransportvsTunnelMode17TransportMode:EndsystemsaretheinitiatorandrecipientofprotectedtrafficTunnelMode:GatewaysactonbehalfofhoststoprotecttrafficRoutingUpdateTFTPFileTransferFileTransferIPsecArchitectureESPAHIKEIPsecSecurityPolicyEncapsulatingSecurityPayloadAuthenticationHeaderTheInternetKeyExchange18SecurityAssociations(SA)AcollectionofparametersrequiredtoestablishasecuresessionUniquelyidentifiedbythreeparametersconsistingof–SecurityParameterIndex(SPI)–IPdestinationaddress–Securityprotocol(AHorESP)identifierAnSAiseitheruni-orbidirectional–IKESAsarebidirectional–IPsecSAsareunidirectionalTwoSAsrequiredforabidirectionalcommunicationAsingleSAcanbeusedforAHorESP,butnotboth–mustcreatetwo(ormore)SAsforeachdirectionifusingbothAHandESP19SecurityParameterIndex(SPI)Aunique32-bitidentificationnumberthatispartoftheSecurityAssociation(SA)ItenablesthereceivingsystemtoselecttheSAunderwhichareceivedpacketwillbeprocessed.
Hasonlylocalsignificance,definedbythecreatoroftheSA.
CarriedintheESPorAHheaderWhenanESP/AHpacketisreceived,theSPIisusedtolookupallofthecryptoparameters20HowtoSetUpSAManually–Sometimesreferredtoas"manualkeying"–Youconfigureoneachnode:Participatingnodes(I.
e.
trafficselectors)AHand/orESP[tunnelortransport]CryptographicalgorithmandkeyAutomatically–UsingIKE(InternetKeyExchange)21ISAKMPInternetSecurityAssociationandKeyManagementProtocolUsedforestablishingSecurityAssociations(SA)andcryptographickeysOnlyprovidestheframeworkforauthenticationandkeyexchange,butkeyexchangeisindependentKeyexchangeprotocols–InternetKeyExchange(IKE)–KerberizedInternetNegotiationofKeys(KINK)22AuthenticationHeader(AH)Providessourceauthenticationanddataintegrity–ProtectionagainstsourcespoofingandreplayattacksAuthenticationisappliedtotheentirepacket,withthemutablefieldsintheIPheaderzeroedoutIfbothAHandESPareappliedtoapacket,AHfollowsESPOperatesontopofIPusingprotocol51InIPv4,AHprotectsthepayloadandallheaderfieldsexceptmutablefieldsandIPoptions(suchasIPsecoption)23AHHeaderFormatNextHeader(8bits):indicateswhichupperlayerprotocolisprotected(UDP,TCP,ESP)PayloadLength(8bits):sizeofAHin32-bitlongwords,minus2Reserved(16bits):forfutureuse;mustbesettoallzeroesfornowSPI(32bits):arbitrary32-bitnumberthatspecifiestothereceivingdevicewhichsecurityassociationisbeingused(securityprotocols,algorithms,keys,times,addresses,etc)SequenceNumber(32bits):startat1andmustneverrepeat.
ItisalwayssetbutreceivermaychoosetoignorethisfieldAuthenticationData:ICVisadigitalsignatureoverthepacketanditvariesinlengthdependingonthealgorithmused(SHA-1,MD5)012345678910111213141516171819202122232425262728293031NextHeaderPayloadLengthReservedSecurityParameterIndex(SPI)SequenceNumberAuthenticationData[IntegrityCheckValue(ICV)]24EncapsulatingSecurityPayload(ESP)UsesIPprotocol50ProvidesallthatisofferedbyAH,plusdataconfidentiality–usessymmetrickeyencryptionMustencryptand/orauthenticateineachpacket–EncryptionoccursbeforeauthenticationAuthenticationisappliedtodataintheIPsecheaderaswellasthedatacontainedaspayload25ESPHeaderFormatSPI:arbitrary32-bitnumberthatspecifiesSAtothereceivingdeviceSeq#:startat1andmustneverrepeat;receivermaychoosetoignoreIV:usedtoinitializeCBCmodeofanencryptionalgorithmPayloadData:encryptedIPheader,TCPorUDPheaderanddataPadding:usedforencryptionalgorithmswhichoperateinCBCmodePaddingLength:numberofbytesaddedtothedatastream(maybe0)NextHeader:thetypeofprotocolfromtheoriginalheaderwhichappearsintheencryptedpartofthepacketAuthenticationHeader:ICVisadigitalsignatureoverthepacketanditvariesinlengthdependingonthealgorithmused(SHA-1,MD5)012345678910111213141516171819202122232425262728293031NextHeaderPaddingLengthPayloadData(Variable)Padding(0-255bytes)InitializationVector(IV)SequenceNumberSecurityParameterIndex(SPI)AuthenticationData(ICV)ENCRYPTED26PacketFormatAlterationforAHTransportModeOriginalIPHeaderTCP/UDPDataOriginalIPHeaderAHHeaderTCP/UDPDataAuthenticationHeaderWithoutAHWithAHAuthenticatedexceptformutablefieldsinIPheader(ToS,TTL,HeaderChecksum,Offset,Flags)27PacketFormatAlterationforESPTransportModeOriginalIPHeaderTCP/UDPDataOriginalIPHeaderESPHeaderEncapsulatingSecurityPayloadBeforeapplyingESP:AfterapplyingESP:EncryptedESPAuthenticationAuthenticatedTCP/UDPDataESPTrailer28PacketFormatAlterationforAHTunnelModeOriginalIPHeaderTCP/UDPDataNewIPHeaderAHHeaderDataAuthenticationHeaderBeforeapplyingAH:AfterapplyingAH:AuthenticatedexceptformutablefieldsinnewIPheaderOriginalIPHeader(ToS,TTL,HeaderChecksum,Offset,Flags)29PacketFormatAlterationforESPTunnelModeOriginalIPHeaderTCP/UDPDataNewIPHeaderESPHeaderEncapsulatingSecurityPayloadBeforeapplyingESP:AfterapplyingESP:EncryptedESPAuthenticationAuthenticatedOriginalIPHeaderTCP/UDPDataESPTrailer30InternetKeyExchange(IKE)"AnIPseccomponentusedforperformingmutualauthenticationandestablishingandmaintainingSecurityAssociations.
"(RFC5996)TypicallyusedforestablishingIPsecsessionsAkeyexchangemechanismFivevariationsofanIKEnegotiation:–Twomodes(aggressiveandmainmodes)–Threeauthenticationmethods(pre-shared,publickeyencryption,andpublickeysignature)UsesUDPport50031IKEModesModeDescriptionMainmodeThreeexchangesofinformationbetweenIPsecpeers.
Initiatorsendsoneormoreproposalstotheotherpeer(responder)ResponderselectsaproposalAggressiveModeAchievessameresultasmainmodeusingonly3packetsFirstpacketsentbyinitiatorcontainingallinfotoestablishSASecondpacketbyresponderwithallsecurityparametersselectedThirdpacketfinalizesauthenticationoftheISAKMPsessionQuickModeNegotiatestheparametersfortheIPsecsession.
EntirenegotiationoccurswithintheprotectionofISAKMPsession32InternetKeyExchange(IKE)PhaseI–Establishasecurechannel(ISAKMPSA)–Usingeithermainmodeoraggressivemode–Authenticatecomputeridentityusingcertificatesorpre-sharedsecretPhaseII–Establishesasecurechannelbetweencomputersintendedforthetransmissionofdata(IPsecSA)–Usingquickmode33OverviewofIKETrafficwhichneedstobeprotectedIPsecPeerIPsecPeerIKEPhase1SecurecommunicationchannelIKEPhase2IPsecTunnelSecuredtrafficexchange123434ISAKMPHeaderFormat012345678910111213141516171819202122232425262728293031InitiatorCookieTotalLengthofMessageFlagsResponderCookieNextPayloadExchangeTypeMessageIDMajorVersionMinorVersion35ISAKMPMessageFormat012345678910111213141516171819202122232425262728293031NextPayload:1byte;identifierfornextpayloadinmessage.
IfitisthelastpayloadItwillbesetto0Reserved:1byte;setto0PayloadLength:2bytes;lengthofpayload(inbytes)includingtheheaderPayload:TheactualpayloaddataNextPayloadReservedPayloadLengthPayloadNextPayloadReservedPayloadLengthPayloadISAKMPHEADER36IKEPhase1(MainMode)MainmodenegotiatesanISAKMPSAwhichwillbeusedtocreateIPsecSAsThreesteps–SAnegotiation(encryptionalgorithm,hashalgorithm,authenticationmethod,whichDFgrouptouse)–DoaDiffie-Hellmanexchange–Provideauthenticationinformation–Authenticatethepeer37IKEPhase1(MainMode)ResponderInitiator12IKEMessage1(SAproposal)IKEMessage2(acceptedSA)IKEMessage3(DHpublicvalue,nonce)IKEMessage4(DHpublicvalue,nonce)IKEMessage5(Authenticationmaterial,ID)IKEMessage6(Authenticationmaterial,ID)43NegotiateIKEPolicyAuthenticatedDHExchangeComputeDHsharedsecretandderivekeyingmaterialProtectIKEPeerIdentityInternet(Encrypted)38IKEPhase1(AggressiveMode)Uses3(vs6)messagestoestablishIKESANodenialofserviceprotectionDoesnothaveidentityprotectionOptionalexchangeandnotwidelyimplemented39IKEPhase2(QuickMode)AlltrafficisencryptedusingtheISAKMPSecurityAssociationEachquickmodenegotiationresultsintwoIPsecSecurityAssociations(oneinbound,oneoutbound)Creates/refresheskeys40IKEPhase2(QuickMode)ResponderInitiator3ComputekeyingmaterialInternetMessage1(authentication/keyingmaterialandSAproposal)Message2(authentication/keyingmaterialandacceptedSA)Message3(hashforproofofintegrity/authentication)125Validatemessage1746Validatemessage3Validatemessage241IKEv2:ReplacementforCurrentIKESpecificationFeaturePreservation–MostfeaturesandcharacteristicsofbaselineIKEv1protocolarebeingpreservedinv2CompilationofFeaturesandExtensions–QuiteafewfeaturesthatwereaddedontopofthebaselineIKEprotocolfunctionalityinv1arebeingreconciledintothemainlinev2frameworkSomeNewFeatures42IKEv2:WhatIsNotChangingFeaturesinv1thathavebeendebatedbutareultimatelybeingpreservedinv2–Mostpayloadsreused–Useofnoncestoensureuniquenessofkeysv1extensionsandenhancementsbeingmergedintomainlinev2specification–Useofa'configurationpayload'similartoMODECFGforaddressassignment–'X-auth'typefunctionalityretainedthroughEAP–UseofNATDiscoveryandNATTraversaltechniques43IKEv2:WhatIsChangingSignificantChangesBeingtotheBaselineFunctionalityofIKE–EAPadoptedasthemethodtoprovidelegacyauthenticationintegrationwithIKE–Publicsignaturekeysandpre-sharedkeys,theonlymethodsofIKEauthentication–Useof'statelesscookie'toavoidcertaintypesofDOSattacksonIKE–Continuousphaseofnegotiation44HowDoesIKEv2WorkIKE_SA_INIT(TwoMessages)IKE_AUTH(TwoMessages)ProtectedDataIKE_SAAuthenticationParametersNegotiatedIKEAuthenticationOccursandOneCHILD_SACreatedCREATE_CHILD_SA(TwoMessages)SecondCHILD_SACreated45ConsiderationsForUsingIPsecSecurityServices–Dataoriginauthentication–Dataintegrity–Replayprotection–ConfidentialitySizeofnetworkHowtrustedareendhosts–canaprioricommunicationpoliciesbecreatedVendorsupportWhatothermechanismscanaccomplishsimilarattackriskmitigation46Non-VendorSpecificDeploymentIssuesHistoricalPerception–Configurationnightmare–NotinteroperablePerformancePerception–Needempiricaldata–WhereistherealperformancehitStandardsNeedCohesion47VendorSpecificDeploymentIssuesLackofinteroperabledefaults–AdefaultdoesNOTmandateaspecificsecuritypolicy–DefaultscanbemodifiedbyendusersConfigurationcomplexity–Toomanyknobs–Vendor-specificterminologyGoodNews:IPv6supportinmostcurrentimplementations48IPsecConcernsAreenoughpeopleawarethatIKEv2isnotbackwardscompatiblewithIKEv1–IKEv1isusedinmostIPsecimplementations–WillIKEv2implementationsfirsttryIKEv2andthenreverttoIKEv1IsIPsecimplementedforIPv6–SomeimplementationsshipIPv6capabledeviceswithoutIPseccapabilityandhostrequirementsischangedfromMUSTtoSHOULDimplementOSPFv3–Allvendors'IF'theyimplementIPsecusedAH–LateststandardtodescribehowtouseIPsecsaysMUSTuseESPw/NullencryptionandMAYuseAH49IPsecConcerns(cont)Whatistransportmodeinteroperabilitystatus–WillenduserauthenticationbeinteroperablePKIIssues–Whichcertificatesdoyoutrust–HowdoesIKEv1and/orIKEv2handleproposalswithcertificates–Shouldcommontrustedrootsbeshippedbydefault–Whoisfollowingandimplementingpki4ipsec-ikecert-profile(rfc4945)Havemobilityscenariosbeentested–MobilitystandardsrelyheavilyonIKEv2ESP–howdetermineifESP-NullvsEncrypted50IPsecBestPracticesUseIPsectoprovideintegrityinadditiontoencryption–UseESPoptionUsestrongencryptionalgorithms–AESinsteadofDESUseagoodhashingalgorithm–SHAinsteadofMD5ReducethelifetimeoftheSecurityAssociation(SA)byenablingPerfectForwardSecrecy(PFS)–Increasesprocessorburdensodothisonlyifdataishighlysensitive51ConfiguringIPsecStep1:ConfiguretheIKEPhase1Policy(ISAKMPPolicy)cryptoisakmppolicy[priority]Step2:SettheISAKMPIdentitycryptoisakmpidentity{ipaddress|hostname}Step3:ConfiguretheIPsectransfersetcryptoipsectransform-settransform-set-namemode[tunnel|transport]cryptoipsecsecurity-associationlifetimesecondsseconds52ConfiguringIPsecStep5:Creatingmapwithnamecryptomapcrypto-map-nameseq-numipsec-isakmpmatchaddressaccess-list-idsetpeer[ipaddress|hostname]settransform-settransform-set-namesetsecurity-associationlifetimesecondssecondssetpfs[group1|group2]Step6:ApplytheIPsecPolicytoanInterfacecryptomapcrypto-map-namelocal-addressinterface-id53IPsecLayoutR1R2EncryptedsessionPublicNetwork54RouterConfigurationcryptoisakmppolicy1authenticationpre-shareencryptionaeshashshagroup5cryptoisakmpkeyTraining123address172.
16.
11.
66!
cryptoipsectransform-setESP-AES-SHAesp-aesesp-sha-hmac!
cryptomapLAB-VPN10ipsec-isakmpmatchaddress101settransform-setESP-AES-SHAsetpeer172.
16.
11.
66Phase1SAEncryptionandauthenticationPhase2SA55RouterConfigurationintfa0/1cryptomapLAB-VPNExit!
access-list101permitip172.
16.
16.
00.
0.
0.
255172.
16.
20.
00.
0.
0.
255ApplytoanoutboundinterfaceDefineinterestingVPNtraffic56IPsecDebugCommandsshcryptoipsecsashcryptoisakmppeersshcryptoisakmpsashcryptomap57Capture:Telnet58Capture:Telnet+IPsec59PrettyGoodIPsecPolicyIKEPhase1(akaISAKMPSAorIKESAorMainMode)–3DES(AES-192ifbothendssupportit)–Lifetime(8hours=480min=28800sec)–SHA-2(256bitkeys)–DHGroup14(akaMODP#14)IKEPhase2(akaIPsecSAorQuickMode)–3DES(AES-192ifbothendssupportit)–Lifetime(1hour=60min=3600sec)–SHA-2(256bitkeys)–PFS2–DHGroup14(akaMODP#14)6061THANKYOUwww.
facebook.
com/APNICwww.
twitter.
com/apnicwww.
youtube.
com/apnicmultimediawww.
flickr.
com/apnicwww.
weibo.
com/APNICrir62
0-draftOverviewIntroductiontoVPNIPsecFundamentalsTunnelandTransportModeIPsecArchitectureandComponentsofIPsecInternetKeyExchangeConfiguringIPsecforIPv4andIPv62VirtualPrivateNetworkCreatesasecuretunneloverapublicnetwork–Clienttofirewall–Routertorouter–FirewalltofirewallUsestheInternetasthepublicbackbonetoaccessasecureprivatenetwork–RemoteemployeescanaccesstheirofficenetworkTwotypes:–Remoteaccess–Site-to-siteVPN3VPNImplementationHardware–UsuallyaVPN-typerouter–Pros:highestnetworkthroughput,plugandplay,dualpurpose–Cons:costandlackofflexibilitySoftware–Idealfortwoend-pointsindifferentorganisations–Pros:flexible,andlowrelativecost–Cons:lackofefficiency,morelabortrainingrequired,lowerproductivity;higherlaborcostsFirewall–Pros:costeffective,tri-purpose,hardenstheoperatingsystem–Cons:stillrelativelycostly4VPNProtocolsPPTP(Point-to-PointtunnelingProtocol)–DevelopedbyMicrosofttosecuredial-upconnections–Operatesinthedata-linklayerL2F(Layer2ForwardingProtocol)–DevelopedbyCisco–SimilarasPPTPL2TP(Layer2TunnelingProtocol)–IETFstandard–CombinesthefunctionalityofPPTPandL2FIPsec(InternetProtocolSecurity)–OpenstandardforVPNimplementation–Operatesonthenetworklayer5OtherModernVPNsMPLSVPN–Usedforlargeandsmallenterprises–Pseudowire,VPLS,VPRNGRETunnel–PacketencapsulationprotocoldevelopedbyCisco–Notencrypted–ImplementedwithIPsecL2TPIPsec–UsesL2TPprotocol–UsuallyimplementedalongwithIPsec–IPsecprovidesthesecurechannel,whileL2TPprovidesthetunnel6AdvantagesofVPNCheaperconnection–UsetheInternetconnectioninsteadofaprivateleaselineScalability–Flexibilityofgrowth–EfficiencywithbroadbandtechnologyAvailability–AvailableeverywherethereisanInternetconnection7DisadvantagesofVPNVPNsrequireanin-depthunderstandingofpublicnetworksecurityissuesandproperdeploymentprecautionsAvailabilityandperformancedependsonfactorslargelyoutsideoftheircontrolVPNsneedtoaccommodateprotocolsotherthanIPandexistinginternalnetworktechnology8IPsecProvidesLayer3security(RFC2401)–Transparenttoapplications(noneedforintegratedIPsecsupport)AsetofprotocolsandalgorithmsusedtosecureIPdataatthenetworklayerCombinesdifferentcomponents:–Securityassociations(SA)–Authenticationheaders(AH)–Encapsulatingsecuritypayload(ESP)–InternetKeyExchange(IKE)AsecuritycontextfortheVPNtunnelisestablishedviatheISAKMP9IPSecInternetWhatisIPSecIETFstandardthatenablesencryptedcommunicationbetweenpeers:–Consistsofopenstandardsforsecuringprivatecommunications–Networklayerencryptionensuringdataconfidentiality,integrity,andauthentication–Scalesfromsmalltoverylargenetworks10IPsecStandardsRFC4301"TheIPSecurityArchitecture"–DefinestheoriginalIPsecarchitectureandelementscommontobothAHandESPRFC4302–Definesauthenticationheaders(AH)RFC4303–DefinestheEncapsulatingSecurityPayload(ESP)RFC2408–ISAKMPRFC5996–IKEv2(Sept2010)RFC4835–CryptographicalgorithmimplementationforESPandAH11BenefitsofIPsecConfidentiality–ByencryptingdataIntegrity–RoutersateachendofatunnelcalculatesthechecksumorhashvalueofthedataAuthentication–Signaturesandcertificates–AllthesewhilestillmaintainingtheabilitytoroutethroughexistingIPnetworks"IPsecisdesignedtoprovideinteroperable,highquality,cryptographically-basedsecurityforIPv4andIPv6"-(RFC2401)12BenefitsofIPsecDataintegrityandsourceauthentication–Data"signed"bysenderand"signature"isverifiedbytherecipient–Modificationofdatacanbedetectedbysignature"verification"–Because"signature"isbasedonasharedsecret,itgivessourceauthenticationAnti-replayprotection–Optional;thesendermustprovideitbuttherecipientmayignoreKeymanagement–IKE–sessionnegotiationandestablishment–Sessionsarerekeyedordeletedautomatically–Secretkeysaresecurelyestablishedandauthenticated–Remotepeerisauthenticatedthroughvaryingoptions13DifferentLayersofEncryptionNetworkLayer-IPsecLinkLayerEncryptionApplicationLayer–SSL,PGP,SSH,HTTPS14IPsecModesTunnelMode–EntireIPpacketisencryptedandbecomesthedatacomponentofanew(andlarger)IPpacket.
–FrequentlyusedinanIPsecsite-to-siteVPNTransportMode–IPsecheaderisinsertedintotheIPpacket–Nonewpacketiscreated–Workswellinnetworkswhereincreasingapacket'ssizecouldcauseanissue–Frequentlyusedforremote-accessVPNs15Tunnelvs.
TransportModeIPsecPayloadTCPHeaderIPHeaderWithoutIPsecTransportModeIPsecTunnelModeIPsecPayloadTCPHeaderIPHeaderIPsecHeaderIPHeaderPayloadTCPHeaderIPHeaderIPsecHeaderNewIPHeader16TransportvsTunnelMode17TransportMode:EndsystemsaretheinitiatorandrecipientofprotectedtrafficTunnelMode:GatewaysactonbehalfofhoststoprotecttrafficRoutingUpdateTFTPFileTransferFileTransferIPsecArchitectureESPAHIKEIPsecSecurityPolicyEncapsulatingSecurityPayloadAuthenticationHeaderTheInternetKeyExchange18SecurityAssociations(SA)AcollectionofparametersrequiredtoestablishasecuresessionUniquelyidentifiedbythreeparametersconsistingof–SecurityParameterIndex(SPI)–IPdestinationaddress–Securityprotocol(AHorESP)identifierAnSAiseitheruni-orbidirectional–IKESAsarebidirectional–IPsecSAsareunidirectionalTwoSAsrequiredforabidirectionalcommunicationAsingleSAcanbeusedforAHorESP,butnotboth–mustcreatetwo(ormore)SAsforeachdirectionifusingbothAHandESP19SecurityParameterIndex(SPI)Aunique32-bitidentificationnumberthatispartoftheSecurityAssociation(SA)ItenablesthereceivingsystemtoselecttheSAunderwhichareceivedpacketwillbeprocessed.
Hasonlylocalsignificance,definedbythecreatoroftheSA.
CarriedintheESPorAHheaderWhenanESP/AHpacketisreceived,theSPIisusedtolookupallofthecryptoparameters20HowtoSetUpSAManually–Sometimesreferredtoas"manualkeying"–Youconfigureoneachnode:Participatingnodes(I.
e.
trafficselectors)AHand/orESP[tunnelortransport]CryptographicalgorithmandkeyAutomatically–UsingIKE(InternetKeyExchange)21ISAKMPInternetSecurityAssociationandKeyManagementProtocolUsedforestablishingSecurityAssociations(SA)andcryptographickeysOnlyprovidestheframeworkforauthenticationandkeyexchange,butkeyexchangeisindependentKeyexchangeprotocols–InternetKeyExchange(IKE)–KerberizedInternetNegotiationofKeys(KINK)22AuthenticationHeader(AH)Providessourceauthenticationanddataintegrity–ProtectionagainstsourcespoofingandreplayattacksAuthenticationisappliedtotheentirepacket,withthemutablefieldsintheIPheaderzeroedoutIfbothAHandESPareappliedtoapacket,AHfollowsESPOperatesontopofIPusingprotocol51InIPv4,AHprotectsthepayloadandallheaderfieldsexceptmutablefieldsandIPoptions(suchasIPsecoption)23AHHeaderFormatNextHeader(8bits):indicateswhichupperlayerprotocolisprotected(UDP,TCP,ESP)PayloadLength(8bits):sizeofAHin32-bitlongwords,minus2Reserved(16bits):forfutureuse;mustbesettoallzeroesfornowSPI(32bits):arbitrary32-bitnumberthatspecifiestothereceivingdevicewhichsecurityassociationisbeingused(securityprotocols,algorithms,keys,times,addresses,etc)SequenceNumber(32bits):startat1andmustneverrepeat.
ItisalwayssetbutreceivermaychoosetoignorethisfieldAuthenticationData:ICVisadigitalsignatureoverthepacketanditvariesinlengthdependingonthealgorithmused(SHA-1,MD5)012345678910111213141516171819202122232425262728293031NextHeaderPayloadLengthReservedSecurityParameterIndex(SPI)SequenceNumberAuthenticationData[IntegrityCheckValue(ICV)]24EncapsulatingSecurityPayload(ESP)UsesIPprotocol50ProvidesallthatisofferedbyAH,plusdataconfidentiality–usessymmetrickeyencryptionMustencryptand/orauthenticateineachpacket–EncryptionoccursbeforeauthenticationAuthenticationisappliedtodataintheIPsecheaderaswellasthedatacontainedaspayload25ESPHeaderFormatSPI:arbitrary32-bitnumberthatspecifiesSAtothereceivingdeviceSeq#:startat1andmustneverrepeat;receivermaychoosetoignoreIV:usedtoinitializeCBCmodeofanencryptionalgorithmPayloadData:encryptedIPheader,TCPorUDPheaderanddataPadding:usedforencryptionalgorithmswhichoperateinCBCmodePaddingLength:numberofbytesaddedtothedatastream(maybe0)NextHeader:thetypeofprotocolfromtheoriginalheaderwhichappearsintheencryptedpartofthepacketAuthenticationHeader:ICVisadigitalsignatureoverthepacketanditvariesinlengthdependingonthealgorithmused(SHA-1,MD5)012345678910111213141516171819202122232425262728293031NextHeaderPaddingLengthPayloadData(Variable)Padding(0-255bytes)InitializationVector(IV)SequenceNumberSecurityParameterIndex(SPI)AuthenticationData(ICV)ENCRYPTED26PacketFormatAlterationforAHTransportModeOriginalIPHeaderTCP/UDPDataOriginalIPHeaderAHHeaderTCP/UDPDataAuthenticationHeaderWithoutAHWithAHAuthenticatedexceptformutablefieldsinIPheader(ToS,TTL,HeaderChecksum,Offset,Flags)27PacketFormatAlterationforESPTransportModeOriginalIPHeaderTCP/UDPDataOriginalIPHeaderESPHeaderEncapsulatingSecurityPayloadBeforeapplyingESP:AfterapplyingESP:EncryptedESPAuthenticationAuthenticatedTCP/UDPDataESPTrailer28PacketFormatAlterationforAHTunnelModeOriginalIPHeaderTCP/UDPDataNewIPHeaderAHHeaderDataAuthenticationHeaderBeforeapplyingAH:AfterapplyingAH:AuthenticatedexceptformutablefieldsinnewIPheaderOriginalIPHeader(ToS,TTL,HeaderChecksum,Offset,Flags)29PacketFormatAlterationforESPTunnelModeOriginalIPHeaderTCP/UDPDataNewIPHeaderESPHeaderEncapsulatingSecurityPayloadBeforeapplyingESP:AfterapplyingESP:EncryptedESPAuthenticationAuthenticatedOriginalIPHeaderTCP/UDPDataESPTrailer30InternetKeyExchange(IKE)"AnIPseccomponentusedforperformingmutualauthenticationandestablishingandmaintainingSecurityAssociations.
"(RFC5996)TypicallyusedforestablishingIPsecsessionsAkeyexchangemechanismFivevariationsofanIKEnegotiation:–Twomodes(aggressiveandmainmodes)–Threeauthenticationmethods(pre-shared,publickeyencryption,andpublickeysignature)UsesUDPport50031IKEModesModeDescriptionMainmodeThreeexchangesofinformationbetweenIPsecpeers.
Initiatorsendsoneormoreproposalstotheotherpeer(responder)ResponderselectsaproposalAggressiveModeAchievessameresultasmainmodeusingonly3packetsFirstpacketsentbyinitiatorcontainingallinfotoestablishSASecondpacketbyresponderwithallsecurityparametersselectedThirdpacketfinalizesauthenticationoftheISAKMPsessionQuickModeNegotiatestheparametersfortheIPsecsession.
EntirenegotiationoccurswithintheprotectionofISAKMPsession32InternetKeyExchange(IKE)PhaseI–Establishasecurechannel(ISAKMPSA)–Usingeithermainmodeoraggressivemode–Authenticatecomputeridentityusingcertificatesorpre-sharedsecretPhaseII–Establishesasecurechannelbetweencomputersintendedforthetransmissionofdata(IPsecSA)–Usingquickmode33OverviewofIKETrafficwhichneedstobeprotectedIPsecPeerIPsecPeerIKEPhase1SecurecommunicationchannelIKEPhase2IPsecTunnelSecuredtrafficexchange123434ISAKMPHeaderFormat012345678910111213141516171819202122232425262728293031InitiatorCookieTotalLengthofMessageFlagsResponderCookieNextPayloadExchangeTypeMessageIDMajorVersionMinorVersion35ISAKMPMessageFormat012345678910111213141516171819202122232425262728293031NextPayload:1byte;identifierfornextpayloadinmessage.
IfitisthelastpayloadItwillbesetto0Reserved:1byte;setto0PayloadLength:2bytes;lengthofpayload(inbytes)includingtheheaderPayload:TheactualpayloaddataNextPayloadReservedPayloadLengthPayloadNextPayloadReservedPayloadLengthPayloadISAKMPHEADER36IKEPhase1(MainMode)MainmodenegotiatesanISAKMPSAwhichwillbeusedtocreateIPsecSAsThreesteps–SAnegotiation(encryptionalgorithm,hashalgorithm,authenticationmethod,whichDFgrouptouse)–DoaDiffie-Hellmanexchange–Provideauthenticationinformation–Authenticatethepeer37IKEPhase1(MainMode)ResponderInitiator12IKEMessage1(SAproposal)IKEMessage2(acceptedSA)IKEMessage3(DHpublicvalue,nonce)IKEMessage4(DHpublicvalue,nonce)IKEMessage5(Authenticationmaterial,ID)IKEMessage6(Authenticationmaterial,ID)43NegotiateIKEPolicyAuthenticatedDHExchangeComputeDHsharedsecretandderivekeyingmaterialProtectIKEPeerIdentityInternet(Encrypted)38IKEPhase1(AggressiveMode)Uses3(vs6)messagestoestablishIKESANodenialofserviceprotectionDoesnothaveidentityprotectionOptionalexchangeandnotwidelyimplemented39IKEPhase2(QuickMode)AlltrafficisencryptedusingtheISAKMPSecurityAssociationEachquickmodenegotiationresultsintwoIPsecSecurityAssociations(oneinbound,oneoutbound)Creates/refresheskeys40IKEPhase2(QuickMode)ResponderInitiator3ComputekeyingmaterialInternetMessage1(authentication/keyingmaterialandSAproposal)Message2(authentication/keyingmaterialandacceptedSA)Message3(hashforproofofintegrity/authentication)125Validatemessage1746Validatemessage3Validatemessage241IKEv2:ReplacementforCurrentIKESpecificationFeaturePreservation–MostfeaturesandcharacteristicsofbaselineIKEv1protocolarebeingpreservedinv2CompilationofFeaturesandExtensions–QuiteafewfeaturesthatwereaddedontopofthebaselineIKEprotocolfunctionalityinv1arebeingreconciledintothemainlinev2frameworkSomeNewFeatures42IKEv2:WhatIsNotChangingFeaturesinv1thathavebeendebatedbutareultimatelybeingpreservedinv2–Mostpayloadsreused–Useofnoncestoensureuniquenessofkeysv1extensionsandenhancementsbeingmergedintomainlinev2specification–Useofa'configurationpayload'similartoMODECFGforaddressassignment–'X-auth'typefunctionalityretainedthroughEAP–UseofNATDiscoveryandNATTraversaltechniques43IKEv2:WhatIsChangingSignificantChangesBeingtotheBaselineFunctionalityofIKE–EAPadoptedasthemethodtoprovidelegacyauthenticationintegrationwithIKE–Publicsignaturekeysandpre-sharedkeys,theonlymethodsofIKEauthentication–Useof'statelesscookie'toavoidcertaintypesofDOSattacksonIKE–Continuousphaseofnegotiation44HowDoesIKEv2WorkIKE_SA_INIT(TwoMessages)IKE_AUTH(TwoMessages)ProtectedDataIKE_SAAuthenticationParametersNegotiatedIKEAuthenticationOccursandOneCHILD_SACreatedCREATE_CHILD_SA(TwoMessages)SecondCHILD_SACreated45ConsiderationsForUsingIPsecSecurityServices–Dataoriginauthentication–Dataintegrity–Replayprotection–ConfidentialitySizeofnetworkHowtrustedareendhosts–canaprioricommunicationpoliciesbecreatedVendorsupportWhatothermechanismscanaccomplishsimilarattackriskmitigation46Non-VendorSpecificDeploymentIssuesHistoricalPerception–Configurationnightmare–NotinteroperablePerformancePerception–Needempiricaldata–WhereistherealperformancehitStandardsNeedCohesion47VendorSpecificDeploymentIssuesLackofinteroperabledefaults–AdefaultdoesNOTmandateaspecificsecuritypolicy–DefaultscanbemodifiedbyendusersConfigurationcomplexity–Toomanyknobs–Vendor-specificterminologyGoodNews:IPv6supportinmostcurrentimplementations48IPsecConcernsAreenoughpeopleawarethatIKEv2isnotbackwardscompatiblewithIKEv1–IKEv1isusedinmostIPsecimplementations–WillIKEv2implementationsfirsttryIKEv2andthenreverttoIKEv1IsIPsecimplementedforIPv6–SomeimplementationsshipIPv6capabledeviceswithoutIPseccapabilityandhostrequirementsischangedfromMUSTtoSHOULDimplementOSPFv3–Allvendors'IF'theyimplementIPsecusedAH–LateststandardtodescribehowtouseIPsecsaysMUSTuseESPw/NullencryptionandMAYuseAH49IPsecConcerns(cont)Whatistransportmodeinteroperabilitystatus–WillenduserauthenticationbeinteroperablePKIIssues–Whichcertificatesdoyoutrust–HowdoesIKEv1and/orIKEv2handleproposalswithcertificates–Shouldcommontrustedrootsbeshippedbydefault–Whoisfollowingandimplementingpki4ipsec-ikecert-profile(rfc4945)Havemobilityscenariosbeentested–MobilitystandardsrelyheavilyonIKEv2ESP–howdetermineifESP-NullvsEncrypted50IPsecBestPracticesUseIPsectoprovideintegrityinadditiontoencryption–UseESPoptionUsestrongencryptionalgorithms–AESinsteadofDESUseagoodhashingalgorithm–SHAinsteadofMD5ReducethelifetimeoftheSecurityAssociation(SA)byenablingPerfectForwardSecrecy(PFS)–Increasesprocessorburdensodothisonlyifdataishighlysensitive51ConfiguringIPsecStep1:ConfiguretheIKEPhase1Policy(ISAKMPPolicy)cryptoisakmppolicy[priority]Step2:SettheISAKMPIdentitycryptoisakmpidentity{ipaddress|hostname}Step3:ConfiguretheIPsectransfersetcryptoipsectransform-settransform-set-namemode[tunnel|transport]cryptoipsecsecurity-associationlifetimesecondsseconds52ConfiguringIPsecStep5:Creatingmapwithnamecryptomapcrypto-map-nameseq-numipsec-isakmpmatchaddressaccess-list-idsetpeer[ipaddress|hostname]settransform-settransform-set-namesetsecurity-associationlifetimesecondssecondssetpfs[group1|group2]Step6:ApplytheIPsecPolicytoanInterfacecryptomapcrypto-map-namelocal-addressinterface-id53IPsecLayoutR1R2EncryptedsessionPublicNetwork54RouterConfigurationcryptoisakmppolicy1authenticationpre-shareencryptionaeshashshagroup5cryptoisakmpkeyTraining123address172.
16.
11.
66!
cryptoipsectransform-setESP-AES-SHAesp-aesesp-sha-hmac!
cryptomapLAB-VPN10ipsec-isakmpmatchaddress101settransform-setESP-AES-SHAsetpeer172.
16.
11.
66Phase1SAEncryptionandauthenticationPhase2SA55RouterConfigurationintfa0/1cryptomapLAB-VPNExit!
access-list101permitip172.
16.
16.
00.
0.
0.
255172.
16.
20.
00.
0.
0.
255ApplytoanoutboundinterfaceDefineinterestingVPNtraffic56IPsecDebugCommandsshcryptoipsecsashcryptoisakmppeersshcryptoisakmpsashcryptomap57Capture:Telnet58Capture:Telnet+IPsec59PrettyGoodIPsecPolicyIKEPhase1(akaISAKMPSAorIKESAorMainMode)–3DES(AES-192ifbothendssupportit)–Lifetime(8hours=480min=28800sec)–SHA-2(256bitkeys)–DHGroup14(akaMODP#14)IKEPhase2(akaIPsecSAorQuickMode)–3DES(AES-192ifbothendssupportit)–Lifetime(1hour=60min=3600sec)–SHA-2(256bitkeys)–PFS2–DHGroup14(akaMODP#14)6061THANKYOUwww.
facebook.
com/APNICwww.
twitter.
com/apnicwww.
youtube.
com/apnicmultimediawww.
flickr.
com/apnicwww.
weibo.
com/APNICrir62
- authenticatedapnic相关文档
- Singleapnic
- "IPv4AddressAllocationsbyCountry"
- Miseapnic
- 中国apnic
- singleapnic
- probeapnic
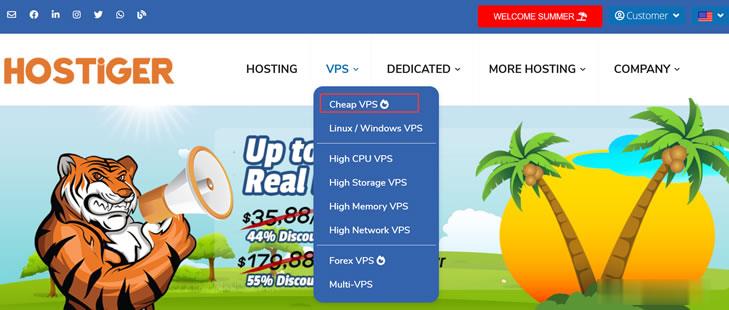
Hostiger发布哥伦布日提供VPS主机首月七折优惠 月费2.79美元
Hostiger商家我们可能以前也是有见过的,以前他们的域名是Hostigger,后来进行微调后包装成现在的。而且推出Columbus Day哥伦布日优惠活动,提供全场的VPS主机首月7折月付2.79美元起的优惠。这里我们普及一下基础知识,Columbus Day ,即为每年10月12日,是一些美洲国家的节日,纪念克里斯托弗·哥伦布在北美登陆,为美国的联邦假日。Hostiger 商家是一个成立于2...
轻云互联22元/月,美国硅谷、圣何塞CN2GIA云服务器,香港沙田cn2建站vps仅25元/月
轻云互联怎么样?轻云互联,广州轻云网络科技有限公司旗下品牌,2018年5月成立以来,轻云互联以性价比的价格一直为提供个人,中大小型企业/团队云上解决方案。本次轻云互联送上的是美国圣何塞cn2 vps(免费50G集群防御)及香港沙田cn2 vps(免费10G集群防御)促销活动,促销产品均为cn2直连中国大陆线路、采用kvm虚拟技术架构及静态内存。目前,轻云互联推出美国硅谷、圣何塞CN2GIA云服务器...

阿里云秋季促销活动 轻量云服务器2G5M配置新购年60元
已经有一段时间没有分享阿里云服务商的促销活动,主要原因在于他们以前的促销都仅限新用户,而且我们大部分人都已经有过账户基本上促销活动和我们无缘。即便老用户可选新产品购买,也是比较配置较高的,所以就懒得分享。这不看到有阿里云金秋活动,有不错的促销活动可以允许产品新购。即便我们是老用户,但是比如你没有购买过他们轻量服务器,也是可以享受优惠活动的。这次轻量服务器在金秋活动中力度折扣比较大,2G5M配置年付...

apnic为你推荐
-
独立ip空间独立IP的空间有什么好处vps主机云主机和VPS主机之间有什么区别免费国外空间哪里的国外免费空间好?域名服务域名系统主要是什么?ip代理地址代理ip地址是怎么来的?网站空间域名什么是网站域名和网站空间海外域名我想了解一下“国内域名”,“国外域名”以及“海外服务器”这三个方面的一些知识虚拟空间哪个好虚拟空间哪个好jsp虚拟空间jsp虚拟主机有支持的吗美国网站空间美国,韩国,香港网站空间