pwrite卡巴斯基授权文件
卡巴斯基授权文件 时间:2021-02-28 阅读:()
AllFileSystemsAreNotCreatedEqual:OntheComplexityofCraftingCrash-ConsistentApplicationsThanumalayanSankaranarayanaPillai,VijayChidambaram,RamnatthanAlagappan,SamerAl-Kiswany,AndreaC.
Arpaci-Dusseau,RemziH.
Arpaci-DusseauAllFileSystemsAreNotCreatedEqual:OntheComplexityofCraftingCrash-ConsistentApplicationsThanumalayanSankaranarayanaPillai,VijayChidambaram,RamnatthanAlagappan,SamerAl-Kiswany,AndreaC.
Arpaci-Dusseau,RemziH.
Arpaci-DusseauCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicImportantinsystems‐FileSystems‐RelationalDatabases‐Key-ValueStoresCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicImportantinsystems‐FileSystems‐RelationalDatabases‐Key-ValueStoresHardtogetright:ARIESinventedonlyin1992‐ProvingARIEStook5moreyears(1997)Lotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
File-SystemCrashConsistencyLotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
FSconsistencyfocusesoninternalmetadata‐DodirectoriesonlycontainvaliddirectoryentriesFile-SystemCrashConsistencyLotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
FSconsistencyfocusesoninternalmetadata‐DodirectoriesonlycontainvaliddirectoryentriesWhataboutuser-leveldataFile-SystemCrashConsistencyWhatguaranteesdofilesystemsgiveapplications‐Thatcanbeusedforconsistencyofuser-leveldataThisworkstudies.
.
.
Whatguaranteesdofilesystemsgiveapplications‐Thatcanbeusedforconsistencyofuser-leveldataDoapplicationsmaintainconsistencycorrectly‐Importantapplicationsrequireuser-levelconsistency‐Databases,key-valuestores,distributedsystems.
.
.
Thisworkstudies.
.
.
Filesystemguaranteesvarywidely‐Studied16configsofext2,ext3,ext4,btrfs,xfs,reiserfs‐Guaranteesvaryamongconfigsofsamefilesystem‐Guaranteesoftenside-effectsofFSimplementation‐POSIXstandardsofguarantees,ifany,aredebatedWefind.
.
.
Filesystemguaranteesvarywidely‐Studied16configsofext2,ext3,ext4,btrfs,xfs,reiserfs‐Guaranteesvaryamongconfigsofsamefilesystem‐Guaranteesoftenside-effectsofFSimplementation‐POSIXstandardsofguarantees,ifany,aredebatedApplicationsdependonguaranteesinsubtleways‐Studied11applications:Databases,Distributedsystems,Virtualizationsoftware,Key-valuestores,VCS‐60vulnerabilitiesunderaweakfilesystemmodel‐Morethan30vulnerabilitiesunderext3,ext4,btrfsWefind.
.
.
IntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineAfileinitiallycontainsthestring"afoo"‐Assumeeachcharacterin"afoo"isablockofdataTask:Atomicallychangethecontentsto"abar"‐Onapowerloss,wemustretrieveeither"afoo"or"abar"ToyExample:OverviewToyExample:SimpleOverwriteInitialstate/x/f1"afoo"Finalstate/x/f1"abar"Modificationpwrite(/x/f1,2,"bar")IntermediatestatespossibleoncrashToyExample:SimpleOverwriteInitialstate/x/f1"afoo"Modificationpwrite(/x/f1,2,"bar")Finalstate/x/f1"abar"Intermediatestate1/x/f1"aboo"Intermediatestate2/x/f1"afar"Intermediatestates3,4,5.
.
.
.
WhatifcrashatomicityisneededUseapplication-levellogging(a.
k.
a.
undologging/rollbackjournaling)a.
Makeacopyofolddatain"log"fileb.
Modifyactualfilec.
Deletelogfiled.
Onacrash,datacanberecoveredfromthelogToyExample:MaintainingConsistencyWhatifcrashatomicityisneededUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);WritetologActualmodificationDeletelogToyExample:Protocol#1Worksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ToyExample:Protocol#1Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
Worksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
ToyExample:Protocol#1SimplydeletelogfileduringrecoveryWorksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
ToyExample:Protocol#1RecoverfromlogfileduringrecoveryWorksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ToyExample:Protocol#1Worksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ext3(ordered)canre-orderthesetworequests,sendingpwrite(f1)todiskfirst,beforewrite(log1)ToyExample:Protocol#1Worksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Apossibleintermediatestate/x/f1"aboo"/x/log1""Recoverynotpossible!
ToyExample:Protocol#1Worksinext3(data-journal),(data-ordered)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#2Worksinext3(data-journal),(data-ordered)!
Doesn'tworkinext3(writeback)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);Apossibleintermediatestates/x/f1"afoo"/x/log1"2,3,#!
@"Filesizealoneincreasesforlog1,andgarbageoccurs.
Recoverycannotdifferentiatebetweengarbageanddata!
CrashhereToyExample:Protocol#2Worksinext3(data-journal),(data-ordered),(writeback)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#3Worksinext3(data-journal),(data-ordered),(writeback)Notenough,accordingtoLinuxmanpagesUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);Apossibleintermediatestates/x/f1"aboo"Thelogfile'sdirectoryentrymightneverbecreatedToyExample:Protocol#3WorksinallfilesystemsUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);fsync(/x);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#4Worksinallfilesystems(Additionalfsync()requiredfordurabilityinallFS)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);fsync(/x);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);fsync(/x);ToyExample:Protocol#5Filesystemsvaryincrash-relatedbehavior‐ext3(ordered)re-orders,whileext3(journaled)doesnotApplicationsusuallydependonsomebehavior‐Dependonordering:Somefsync()callscanbeomittedExample:SummaryIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineTwoclassesofproperties:atomicityandordering‐Atomicityexample:Isawrite()callatomicintheFS‐Orderingexample:Arewrite()callssenttodiskin-orderStudiedext2,ext3,ext4,btrfs,xfs,reiserfs‐Westudied16configurationsofthesixfilesystemsFSBehavior:PersistenceProperties1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()callsMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkloadMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkload3.
Reconstructdisk-statespossibleonapower-loss‐Allstatespossibleifdisk-cachedoesnotre-order‐Afewstateswheredisk-cachere-ordersMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkload3.
Reconstructdisk-statespossibleonapower-loss‐Allstatespossibleifdisk-cachedoesnotre-order‐Afewstateswheredisk-cachere-orders4.
RunFSrecovery,verifypropertyoneachdisk-state‐Example:Isall8KBwrittenatomicallyMethodology:TheBlock-OrderBreaker(BOB)FileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncFileSystemDifferentConfigurationsofFileSystemFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncPersistencePropertiesconsideredFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncIsadirectoryoperation,likerename(),atomiconasystemcrashFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncPropertycertainlynotobeyedWedidnotseeaviolationFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncMainresult:FilesystemsvaryintheirpersistencepropertiesApplicationsshouldnotrelyonpersistencepropertiesTestingapplicationsonaspecificFSisnotenough‐ext3(data-journal):Re-orderingvulnerabilitiesarehiddenFileSystemStudy:ConclusionIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineALICE:Goal"Application-LevelIntelligentCrashExplorer"Goal:Tooltofindcrashvulnerabilitiesofanapplication‐Findvulnerabilitiesacrossallfilesystems‐Relatevulnerabilitiestospecificsourcelines‐RelatevulnerabilitiestofilesystembehaviorALICE:TechniqueUser-suppliedApplicationWorkloadALICEUsersuppliesALICEwithanapplicationworkload–Example:AdatabasetransactionALICE:TechniqueSystem-callTraceALICErunsworkloadandrecordssystem-calltraceALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceAPM:AbstractPersistenceModelAPMmodelsallcrashstatesthatcanoccuronanFS–Default,weakAPMallowsmanypossiblestates–CustomAPMscanbeconfiguredbyuserforaspecificfilesystem–Eg:ext3(ordered)APMallowsstateswithoverwritesre-ordered;ext3(data-journal)APMdoesnotALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceExplorerAPM:AbstractPersistenceModelExplorerreconstructssomestatesusingtheAPMALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceExplorer.
.
.
ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)Explorertargetsspecificstates–Relatingtoatomicityandre-orderingofeachsyscallUser-suppliedApplicationWorkloadTheapplicationisrunoneachreconstructedstate–Usersuppliesapplicationchecker–Example:WasACIDpreservedALICE:TechniqueSystem-callTraceExplorer.
.
.
User-suppliedApplicationCheckerALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)User-suppliedApplicationWorkloadCheckershowswhichstatesarerecoveredfromcorrectlyALICE:TechniqueSystem-callTraceExplorer.
.
.
ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)CorrectIncorrectUser-suppliedApplicationWorkloadUser-suppliedApplicationCheckerFromcheckeroutputs,wedeterminevulnerabilitiesALICE:TechniqueSystem-callTraceExplorer.
.
.
Crashvulnerability:Re-orderingsyscall-1and2ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)CorrectIncorrectUser-suppliedApplicationWorkloadUser-suppliedApplicationCheckerHDFSZooKeeperVMWarePlayerLMDBGDBMLevelDBPostgresHSQLDBSQLiteMercurialGitVulnerabilityStudy:ApplicationsNon-relationalDatabasesRelationalDatabasesVersionControlSystemsVirtualizationSoftwareDistributedServicesExample:Gitcreat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Readthefullpapertocorrectlyinterpretresults!
creat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Example:GitAtomicityvulnerabilityWhichsystemcallsneedtobeatomicReadthefullpapertocorrectlyinterpretresults!
creat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Example:GitAtomicityvulnerabilityOrderingvulnerabilityWhichsystem-callre-orderingscauseincorrectnessReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:Default(Weak)APMReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:Default(Weak)APM60VulnerabilitiesManyresultinsilentdataloss,inaccessibleapplicationsReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:BtrfsAPMReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:BtrfsAPM31VulnerabilitiesReadthefullpapertocorrectlyinterpretresults!
Garbageduringfile-appends‐Affects3applications‐But,partialappendswithactualdata:0vulnerabilitiesFSsafetyheuristicsseeminglydon'thelpmuch‐Only2foundvulnerabilitiesby"Flushdatabeforerename"‐HeuristicsmighthelpothertypesofapplicationsNon-synchronousdirectoryoperations‐Affectsdurabilityof6applicationsWhatFSbehavioraffectsapplicationsIn-depth:WhatFSbehaviorsaffectapplicationsVulnerabilitiesunderotherAPMsInteractionswithapplicationdevelopersHownottointerpretourresultsAnefficientFSdesignwithsafetyvalidatedbyALICEInthepaper.
.
.
FSvaryinbehavioraffectingapplicationconsistency‐ext2,ext3,ext4,btrfs,xfs,reiserfsvaryevenamongtheirdifferentconfigurations‐SubtleimplementationdetailsaffectbehaviorApplicationprotocolsarecomplex,vulnerable‐60vulnerabilitiesunderweakAPM‐Morethanhalfexposedunderext3,ext4,btrfs‐Depend(bydesignorunwittingly)onFSimplementationSummaryApartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoApartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoExperiencedAcademic:Realfilesystemsdon'tdothatButdoesjustthatAcademic:Mystudentswouldflunkclassiftheybuiltafilesystemthatway.
.
.
Apartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoExperiencedAcademic:Realfilesystemsdon'tdothatButdoesjustthatAcademic:Mystudentswouldflunkclassiftheybuiltafilesystemthatway.
.
.
Thankyou!
Downloadtools:http://research.
cs.
wisc.
edu/adsl/Software/alice
Arpaci-Dusseau,RemziH.
Arpaci-DusseauAllFileSystemsAreNotCreatedEqual:OntheComplexityofCraftingCrash-ConsistentApplicationsThanumalayanSankaranarayanaPillai,VijayChidambaram,RamnatthanAlagappan,SamerAl-Kiswany,AndreaC.
Arpaci-Dusseau,RemziH.
Arpaci-DusseauCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicImportantinsystems‐FileSystems‐RelationalDatabases‐Key-ValueStoresCrashConsistencyMaintainingdatainvariantsacrossasystemcrash‐Example:DatabasetransactionsshouldbeatomicImportantinsystems‐FileSystems‐RelationalDatabases‐Key-ValueStoresHardtogetright:ARIESinventedonlyin1992‐ProvingARIEStook5moreyears(1997)Lotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
File-SystemCrashConsistencyLotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
FSconsistencyfocusesoninternalmetadata‐DodirectoriesonlycontainvaliddirectoryentriesFile-SystemCrashConsistencyLotsofworkinfilesystemcrashconsistency‐Journaling,copy-on-write,softupdates.
.
.
FSconsistencyfocusesoninternalmetadata‐DodirectoriesonlycontainvaliddirectoryentriesWhataboutuser-leveldataFile-SystemCrashConsistencyWhatguaranteesdofilesystemsgiveapplications‐Thatcanbeusedforconsistencyofuser-leveldataThisworkstudies.
.
.
Whatguaranteesdofilesystemsgiveapplications‐Thatcanbeusedforconsistencyofuser-leveldataDoapplicationsmaintainconsistencycorrectly‐Importantapplicationsrequireuser-levelconsistency‐Databases,key-valuestores,distributedsystems.
.
.
Thisworkstudies.
.
.
Filesystemguaranteesvarywidely‐Studied16configsofext2,ext3,ext4,btrfs,xfs,reiserfs‐Guaranteesvaryamongconfigsofsamefilesystem‐Guaranteesoftenside-effectsofFSimplementation‐POSIXstandardsofguarantees,ifany,aredebatedWefind.
.
.
Filesystemguaranteesvarywidely‐Studied16configsofext2,ext3,ext4,btrfs,xfs,reiserfs‐Guaranteesvaryamongconfigsofsamefilesystem‐Guaranteesoftenside-effectsofFSimplementation‐POSIXstandardsofguarantees,ifany,aredebatedApplicationsdependonguaranteesinsubtleways‐Studied11applications:Databases,Distributedsystems,Virtualizationsoftware,Key-valuestores,VCS‐60vulnerabilitiesunderaweakfilesystemmodel‐Morethan30vulnerabilitiesunderext3,ext4,btrfsWefind.
.
.
IntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineAfileinitiallycontainsthestring"afoo"‐Assumeeachcharacterin"afoo"isablockofdataTask:Atomicallychangethecontentsto"abar"‐Onapowerloss,wemustretrieveeither"afoo"or"abar"ToyExample:OverviewToyExample:SimpleOverwriteInitialstate/x/f1"afoo"Finalstate/x/f1"abar"Modificationpwrite(/x/f1,2,"bar")IntermediatestatespossibleoncrashToyExample:SimpleOverwriteInitialstate/x/f1"afoo"Modificationpwrite(/x/f1,2,"bar")Finalstate/x/f1"abar"Intermediatestate1/x/f1"aboo"Intermediatestate2/x/f1"afar"Intermediatestates3,4,5.
.
.
.
WhatifcrashatomicityisneededUseapplication-levellogging(a.
k.
a.
undologging/rollbackjournaling)a.
Makeacopyofolddatain"log"fileb.
Modifyactualfilec.
Deletelogfiled.
Onacrash,datacanberecoveredfromthelogToyExample:MaintainingConsistencyWhatifcrashatomicityisneededUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);WritetologActualmodificationDeletelogToyExample:Protocol#1Worksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ToyExample:Protocol#1Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
Worksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
ToyExample:Protocol#1SimplydeletelogfileduringrecoveryWorksinext3(data-journal)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Somepossibleintermediatestates/x/f1"afoo"/x/log1""/x/f1"afoo"/x/log1"2,3,f"/x/f1"aboo"/x/log1"2,3,foo"1.
2.
3.
ToyExample:Protocol#1RecoverfromlogfileduringrecoveryWorksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ToyExample:Protocol#1Worksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);ext3(ordered)canre-orderthesetworequests,sendingpwrite(f1)todiskfirst,beforewrite(log1)ToyExample:Protocol#1Worksinext3(data-journal)!
Doesn'tworkinext3(data-ordered)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");pwrite(/x/f1,2,"bar");unlink(/x/log1);Apossibleintermediatestate/x/f1"aboo"/x/log1""Recoverynotpossible!
ToyExample:Protocol#1Worksinext3(data-journal),(data-ordered)!
UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#2Worksinext3(data-journal),(data-ordered)!
Doesn'tworkinext3(writeback)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);Apossibleintermediatestates/x/f1"afoo"/x/log1"2,3,#!
@"Filesizealoneincreasesforlog1,andgarbageoccurs.
Recoverycannotdifferentiatebetweengarbageanddata!
CrashhereToyExample:Protocol#2Worksinext3(data-journal),(data-ordered),(writeback)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#3Worksinext3(data-journal),(data-ordered),(writeback)Notenough,accordingtoLinuxmanpagesUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);Apossibleintermediatestates/x/f1"aboo"Thelogfile'sdirectoryentrymightneverbecreatedToyExample:Protocol#3WorksinallfilesystemsUpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);fsync(/x);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);ToyExample:Protocol#4Worksinallfilesystems(Additionalfsync()requiredfordurabilityinallFS)UpdateProtocolcreat(/x/log1);write(/x/log1,"2,3,checksum,foo");fsync(/x/log1);fsync(/x);pwrite(/x/f1,2,"bar");fsync(/x/f1);unlink(/x/log1);fsync(/x);ToyExample:Protocol#5Filesystemsvaryincrash-relatedbehavior‐ext3(ordered)re-orders,whileext3(journaled)doesnotApplicationsusuallydependonsomebehavior‐Dependonordering:Somefsync()callscanbeomittedExample:SummaryIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineTwoclassesofproperties:atomicityandordering‐Atomicityexample:Isawrite()callatomicintheFS‐Orderingexample:Arewrite()callssenttodiskin-orderStudiedext2,ext3,ext4,btrfs,xfs,reiserfs‐Westudied16configurationsofthesixfilesystemsFSBehavior:PersistenceProperties1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()callsMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkloadMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkload3.
Reconstructdisk-statespossibleonapower-loss‐Allstatespossibleifdisk-cachedoesnotre-order‐Afewstateswheredisk-cachere-ordersMethodology:TheBlock-OrderBreaker(BOB)1.
Runuser-levelworkloadsstressingtheproperty‐Example:write(8KB)fortestingatomicityofwrite()calls2.
Recordblock-leveltraceoftheworkload3.
Reconstructdisk-statespossibleonapower-loss‐Allstatespossibleifdisk-cachedoesnotre-order‐Afewstateswheredisk-cachere-orders4.
RunFSrecovery,verifypropertyoneachdisk-state‐Example:Isall8KBwrittenatomicallyMethodology:TheBlock-OrderBreaker(BOB)FileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncFileSystemDifferentConfigurationsofFileSystemFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncPersistencePropertiesconsideredFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncIsadirectoryoperation,likerename(),atomiconasystemcrashFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncPropertycertainlynotobeyedWedidnotseeaviolationFileSystemStudy:ResultsFilesystemconfigurationAtomicityOrderingOnesectoroverwriteAppendcontentManysectoroverwriteDirectoryoperationOverwrite→AnyopAppend→AnyopDir-op→AnyopAppend→Renameext2asyncsyncext3writebackordereddata-journalext4writebackorderedno-delallocdata-journalbtrfsxfsdefaultwsyncMainresult:FilesystemsvaryintheirpersistencepropertiesApplicationsshouldnotrelyonpersistencepropertiesTestingapplicationsonaspecificFSisnotenough‐ext3(data-journal):Re-orderingvulnerabilitiesarehiddenFileSystemStudy:ConclusionIntroductionAnExampleBOB:ExaminingFileSystemBehaviorALICE:ExaminingApplicationsConclusionOutlineALICE:Goal"Application-LevelIntelligentCrashExplorer"Goal:Tooltofindcrashvulnerabilitiesofanapplication‐Findvulnerabilitiesacrossallfilesystems‐Relatevulnerabilitiestospecificsourcelines‐RelatevulnerabilitiestofilesystembehaviorALICE:TechniqueUser-suppliedApplicationWorkloadALICEUsersuppliesALICEwithanapplicationworkload–Example:AdatabasetransactionALICE:TechniqueSystem-callTraceALICErunsworkloadandrecordssystem-calltraceALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceAPM:AbstractPersistenceModelAPMmodelsallcrashstatesthatcanoccuronanFS–Default,weakAPMallowsmanypossiblestates–CustomAPMscanbeconfiguredbyuserforaspecificfilesystem–Eg:ext3(ordered)APMallowsstateswithoverwritesre-ordered;ext3(data-journal)APMdoesnotALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceExplorerAPM:AbstractPersistenceModelExplorerreconstructssomestatesusingtheAPMALICEUser-suppliedApplicationWorkloadALICE:TechniqueSystem-callTraceExplorer.
.
.
ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)Explorertargetsspecificstates–Relatingtoatomicityandre-orderingofeachsyscallUser-suppliedApplicationWorkloadTheapplicationisrunoneachreconstructedstate–Usersuppliesapplicationchecker–Example:WasACIDpreservedALICE:TechniqueSystem-callTraceExplorer.
.
.
User-suppliedApplicationCheckerALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)User-suppliedApplicationWorkloadCheckershowswhichstatesarerecoveredfromcorrectlyALICE:TechniqueSystem-callTraceExplorer.
.
.
ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)CorrectIncorrectUser-suppliedApplicationWorkloadUser-suppliedApplicationCheckerFromcheckeroutputs,wedeterminevulnerabilitiesALICE:TechniqueSystem-callTraceExplorer.
.
.
Crashvulnerability:Re-orderingsyscall-1and2ALICEAPM:AbstractPersistenceModelCrashstate#1(Violatesatomicityofsyscall-1)Crashstate#2(Violatesorderingofsyscall-1and2)CorrectIncorrectUser-suppliedApplicationWorkloadUser-suppliedApplicationCheckerHDFSZooKeeperVMWarePlayerLMDBGDBMLevelDBPostgresHSQLDBSQLiteMercurialGitVulnerabilityStudy:ApplicationsNon-relationalDatabasesRelationalDatabasesVersionControlSystemsVirtualizationSoftwareDistributedServicesExample:Gitcreat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Readthefullpapertocorrectlyinterpretresults!
creat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Example:GitAtomicityvulnerabilityWhichsystemcallsneedtobeatomicReadthefullpapertocorrectlyinterpretresults!
creat(index.
lock)mkdir(o/x)creat(o/x/tmp_y)append(o/x/tmp_y)fsync(o/x/tmp_y)link(o/x/tmp_y,o/x/y)unlink(o/x/tmp_y)append(index.
lock)rename(index.
lock,index)stdout(finishedadd)Example:GitAtomicityvulnerabilityOrderingvulnerabilityWhichsystem-callre-orderingscauseincorrectnessReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:Default(Weak)APMReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:Default(Weak)APM60VulnerabilitiesManyresultinsilentdataloss,inaccessibleapplicationsReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:BtrfsAPMReadthefullpapertocorrectlyinterpretresults!
VulnerabilityStudy:BtrfsAPM31VulnerabilitiesReadthefullpapertocorrectlyinterpretresults!
Garbageduringfile-appends‐Affects3applications‐But,partialappendswithactualdata:0vulnerabilitiesFSsafetyheuristicsseeminglydon'thelpmuch‐Only2foundvulnerabilitiesby"Flushdatabeforerename"‐HeuristicsmighthelpothertypesofapplicationsNon-synchronousdirectoryoperations‐Affectsdurabilityof6applicationsWhatFSbehavioraffectsapplicationsIn-depth:WhatFSbehaviorsaffectapplicationsVulnerabilitiesunderotherAPMsInteractionswithapplicationdevelopersHownottointerpretourresultsAnefficientFSdesignwithsafetyvalidatedbyALICEInthepaper.
.
.
FSvaryinbehavioraffectingapplicationconsistency‐ext2,ext3,ext4,btrfs,xfs,reiserfsvaryevenamongtheirdifferentconfigurations‐SubtleimplementationdetailsaffectbehaviorApplicationprotocolsarecomplex,vulnerable‐60vulnerabilitiesunderweakAPM‐Morethanhalfexposedunderext3,ext4,btrfs‐Depend(bydesignorunwittingly)onFSimplementationSummaryApartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoApartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoExperiencedAcademic:Realfilesystemsdon'tdothatButdoesjustthatAcademic:Mystudentswouldflunkclassiftheybuiltafilesystemthatway.
.
.
Apartingnote.
.
.
.
ExperiencedApp-Developer:POSIXdoesn'tletFSesdothatCanyoupointustotheexactPOSIXdocumentationDeveloper:Ican'tfindit,butIremembersomeonesayingsoExperiencedAcademic:Realfilesystemsdon'tdothatButdoesjustthatAcademic:Mystudentswouldflunkclassiftheybuiltafilesystemthatway.
.
.
Thankyou!
Downloadtools:http://research.
cs.
wisc.
edu/adsl/Software/alice
- pwrite卡巴斯基授权文件相关文档
- 标准卡巴斯基授权文件
- 信息卡巴斯基授权文件
- 信任卡巴斯基授权文件
- 数据卡巴斯基授权文件
- 居中卡巴斯基授权文件
- 节点卡巴斯基授权文件
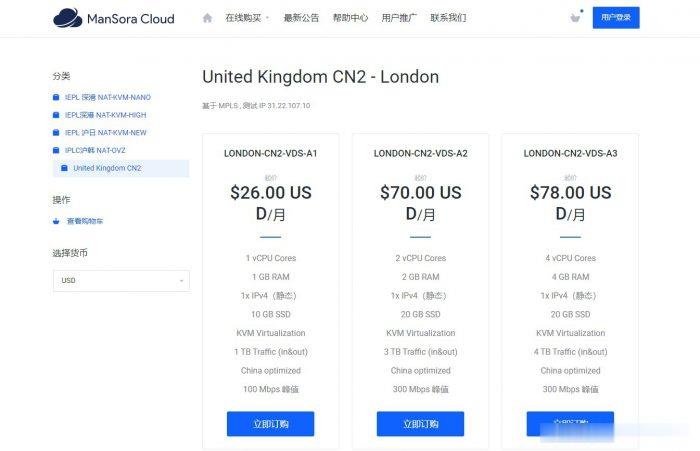
ManSora:英国CN2 VPS,1核/1GB内存/10GB SSD/1TB流量/100Mbps/KVM,$18.2/月
mansora怎么样?mansora是一家国人商家,主要提供沪韩IEPL、沪日IEPL、深港IEPL等专线VPS。现在新推出了英国CN2 KVM VPS,线路为AS4809 AS9929,可解锁 Netflix,并有永久8折优惠。英国CN2 VPS,$18.2/月/1GB内存/10GB SSD空间/1TB流量/100Mbps端口/KVM,有需要的可以关注一下。点击进入:mansora官方网站地址m...
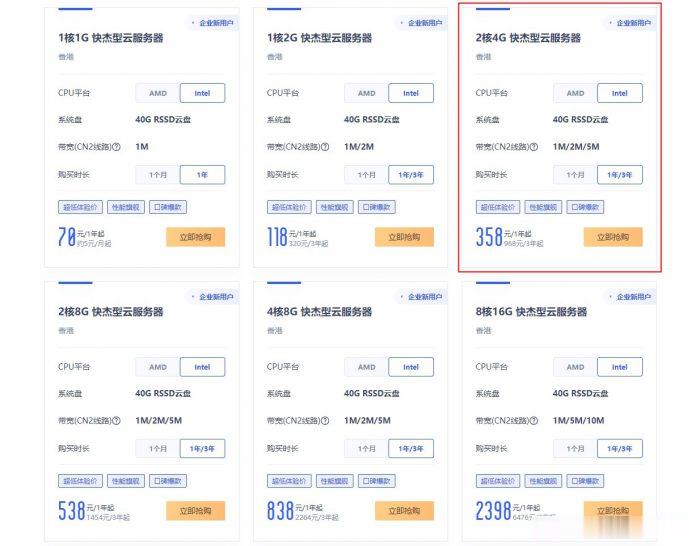
ucloud香港服务器优惠活动:香港2核4G云服务器低至358元/年,968元/3年
ucloud香港服务器优惠降价活动开始了!此前,ucloud官方全球云大促活动的香港云服务器一度上涨至2核4G配置752元/年,2031元/3年。让很多想购买ucloud香港云服务器的新用户望而却步!不过,目前,ucloud官方下调了香港服务器价格,此前2核4G香港云服务器752元/年,现在降至358元/年,968元/3年,价格降了快一半了!UCloud活动路子和阿里云、腾讯云不同,活动一步到位,...
随风云-内蒙古三线BGP 2-2 5M 25/月 ,香港CN2 25/月 ,美国CERA 25/月 所有云服务器均支持5天无理由退款
公司成立于2021年,专注为用户提供低价高性能云计算产品,致力于云计算应用的易用性开发,面向全球客户提供基于云计算的IT解决方案与客户服务,拥有丰富的国内BGP、三线高防、香港等优质的IDC资源。公司一直秉承”以人为本、客户为尊、永续创新”的价值观,坚持”以微笑收获友善, 以尊重收获理解,以责任收获支持,以谦卑收获成长”的行为观向客户提供全面优质的互...

卡巴斯基授权文件为你推荐
-
回收站在哪回收站在哪?个性qq资料`谁有最新 最有个性的QQ个性资料微信如何建群微信可以建立两个人的群吗?有一个是自己手机区号打电话怎么加区号?中小企业信息化小企业需要信息化吗?需要的话要怎么实现信息化呢?网易公开课怎么下载怎么下载网易公开课里的视频 .......蘑菇街美丽说蘑菇街、美丽说这类网站前期是怎么推广的?qq怎么发邮件手机QQ怎么发邮件qq怎么发邮件怎么发送QQ邮件雅虎天盾我机器上有瑞星杀毒和防火墙 我用雅虎天盾来查杀木马怎样?