自己的如何保护自己的电脑 ip 不让别人攻击掉线(How do you protect your computer IP from being dropped)
如何保护自己的电脑ip不让别人攻击掉线How do you protectyour computer IP from being dropped
How do you protect your computer IP from being attacked? Somepeople will say that attack you IP let you drop he implementedafter you really lost how to do reward points: 100 - to solvetime: 2009-1-10 22:35 he said on QQ UT that let you drop offfor a while you tell me how to deal with him is my IP. I can'tchange the fixed do not always let him get ah
If I am an Internet cafe, it is impossible to install firewallsin every station. Is there any other good way?:
You see, it might be useful to you.
Cancel folder to hide share
If youuse the Windows 2000/XP system, right click the C or otherdisk, choose to share, you will be surprised to find that ithas been set to"share this folder in the"network neighborhood"can't see the content, how is this going on?
Originally, by default, Windows 2000/XP will open allpartitions hidden shared from the control panel / managementtools / computer management "window to select" system tools /share / share ", you can see each disk partition name behindwith a" $". But as long as the type the computer name or IPC$",the system will ask the user name and password, unfortunately,most of the individual users Administrator password is empty,the intruder can easily see the C content, the network securityhas brought great hidden danger.
How do you eliminate default sharing?The method is very simple,open the registry editor, enter
"HKEY_LOCAL_MACH INESYSTEMCurrentCont rol Set Sev i ce sLanmanwork
stationparameters", a new name "AutoShareWKs" double bytevalue, and its value is "0", and then restart the computer, thisshare was canceled.
Two, refuse malicious code
Malicious web pages have become one of the biggest threats tobroadband. Modem was used before because it was slow to openpages, shut down malicious web pages before being fully opened,and avoided the possibility of being caught. Broadband is nowso fast that it can easily be attacked by malicious web pages.Malicious web pages are generally destructive because they arewritten in malicious code. These malicious code is equivalentto some small programs, as long as the opening of the web pagewill be run. Therefore, to avoid malicious web attacks, as longas the prohibition of the operation of these malicious code onit.
Run the IE browser, click "tools /Internet options / safety /custom level, the security level is defined as" security levelhigh", "ActiveX controls and plug-ins in the second, third setto"disabled", the other is set to"tip", then click"ok". Afterthis setting, when you use IE to browse web pages, you caneffectively avoid malicious web pages malicious code attacks.Three, seal hacker' s back door"
As the saying goes "There are no waves without wind. ", sincehackers can enter the system, there must be open for them, aslong as the "back door" blocked the back door, so that hackersno place to start, there is no menace from the rear!
1. cut out unnecessary agreements
For servers and hosts, it' s enough to just install the TCP/IPprotocol. Right click the network neighbor, select properties,right-click the local connection, select properties, anduninstall unnecessary protocols. Among them, NETBIOS is theroot of many security flaws. For those hosts that do not needto provide file and print sharing, they can also close theNETBIOS that is bound to the TCP/IP protocol and avoid attacksagainst NETBIOS. Select the "TCP/IP protocol / property /advanced", enter the advanced TCP/IP settings dialog box,select the WINS tab, tick the disable TCP/IP on NETBIOS, andclose NETBIOS.
2. close file and print sharing"
File andprint sharing should be avery useful feature, but it' sa good security hole for hacking when you don't need it. So,without the need for "file and print sharing", we can turn itoff. Right click the network neighbor, select properties, andthen click the file and print sharing button to remove the hookin the two check boxes in the pop-up file and print share dialogbox.
Although the file and print share is closed, there is no
guarantee of security, and the registry must be modified toprevent it from changing file and print sharing". Open theregistry editor, select the
"HKEY_CURRENT_USERSoftwareMi crosof tWindowsCurrentVersi onPol
iciesNetWork" key, new types of DWORD keys in the key, the keyis called "NoFileSharingControl" key to "1" said the banfunction, so as to achieve the prohibition to change the fileand print sharing ";" 0 "key allows this function.
In this "network neighbor"property dialog box, "f ile and printsharing" no longer exists.
3. disable the Guest account
There are many intrusions through this account to furtheraccess the administrator password or permissions. If you don'twant to give your computer to someone else as a toy, it' sforbidden. Open the control panel, double-click the user andpassword, click the Advanced tab, and then click the advancedbutton to eject the local user and group window. Right clickon the Guest account, select properties, and select "theaccount is disabled" on the "general" page". In addition, theAdministrator account name change can prevent hackers knowtheir own administrator account, which will largely guaranteecomputer security.
4. prohibit the establishment of empty connections
By default, any user can connect to the server via an emptyconnection, enumerate the account number, and guess thepassword. Therefore, we must prohibit the establishment of
empty connections. There are two ways:
Method one is to modify the registry: open the registry"HKEY_LOCAL_MACHINESystemCurrentControlSetControlLSA", theDWORD value "RestrictAnonymous" key to "1" can be.
Finally, I suggest you put your own system patches, Microsoftthose endless patches are still very useful!
Four, hide the IP address
Hackers often use some network detection technology to checkour host information, the main purpose is to get the IP addressof the host in the network. IP address is a very importantconcept in network security, if the attackers know your IPaddress, is ready for his attack, he can ask the IP to launcha variety of attacks, such as DoS (denial of service) attack,Floop overflow attack etc. . The primary way to hide IP addressesis to use proxy servers.
Compared with the direct connection to Internet, the use ofproxy servers canprotect the IP address of Internet users, thusensuring Internet security. The principle of the proxy serveris the client (user computer) and remote server (such as theuser wants to access remote WWW server) set up between a"station", when a client request to a remote server, proxyserver first intercept the user' s request, and the proxy serverwill service request to the server. In order to achieve betweenthe client and the remote server connection. Obviously, afterthe proxy server is used, other users can only detect the IPaddress of the proxy server, not the IP address of the user,
thus realizing the purpose of hiding the user' s IP address andensuring the security of the user' s Internet access. There aremany websites offering free proxy servers, and you can also findthem yourself using proxies, hunters, and other tools.Five, turn off unnecessary ports
A hacker often scans your computer' s ports during an invasion.If the port monitor (such as Netwatch) is installed, the monitorwill have a warning prompt. If you encounter this kind ofintrusion, software tools available to close the port, forexample, to provide web service 80 and 443 port closure with"Norton Internet Security", some other commonly used ports canbe turned off.
Six, replace the administrator account
Administrator accounts have the highest system privileges, andonce the account is used, the consequences can be disastrous.One of the common ways of hacking is to try to get the passwordfor the Administrator account, so we have to reconfigure theAdministrator account.
The first is to set up a strong and complex password for theAdministrator account, then we rename the Administratoraccount, and then create a Administrator account with noadministrator privileges to cheat the intruder. As a result,it is difficult for intruders to figure out which accounts haveadministrator rights and, to some extent, reduce the risk.Seven, to prevent the invasion of Guest accounts
The Guest account, known as the guest account, has access tothe computer but is restricted. Unfortunately, Guest alsoopened convenient ways for hacking! There are many articles onhow to use Guest users to get administrator privileges, so wemust put an end to the system invasion based on Guest accounts.It' s best to disable or completely delete Guest accounts, butin some cases you have to use Guest accounts, you need to dodefensive work in other ways. First, set up a strong passwordfor Guest, and then specify the access rights of the Guestaccount to the physical path. For example, if you want toprevent Guest users can access the tool folder, right-click thefolder, select the "security" tab in the pop-up menu, can beseen from all users can access this folder. Delete all usersexcept administrators. Or set permissions for the appropriateuser in the permissions,
For example, you can only list folders, directories, and read,so that' s much safer.
Eight. Install the necessary security software
We should also install and use the necessary software incomputer hacking, antivirus software and firewall is necessary.Open them on the Internet so that even when hackers attack, oursecurity is guaranteed.
Nine, to prevent Trojans
Trojan horse program will steal useful information embedded in
the computer, so we have to prevent hackers implanted Trojanhorse, the commonly used method is:
When downloading files, first put them in your own new folder,and then use antivirus software to detect and play the role ofpreventing in advance.
In the "start", "program", "start", "start", "start","program", "Startup", see if there are any unknown runningitems, if so, delete them.
? all the
HKEY_LOCAL_MACHINE\SOFTWARE\Microsof t\Windows\CurrentVers ion\Run in the registry under the "Run"prefix for all suspiciousprocedures can be deleted.
Ten, do not return to strangers mail
Some hackers may be posing as some formal website name, username and password and then make a highfalutin reason to senda letter to you to ask you to enter the Internet, if you pressthe "OK", your account number and password into the hackermailbox. So don' t just return a stranger' s mail. Even if he saysit sounds good, he won't be fooled.
Do a good job of IE security settings
ActiveX controls and Applets have strong functions, but thereare also hidden dangers that are exploited. Malicious code ina web page is often a small programwritten using these controls.As long as the page is opened, it will be run. Therefore, to
avoid malicious web attacks, only prohibit the operation ofthese malicious code. IE provides awide variety of options forthis. The settings are: Tools > Internet Options > Security >Custom levels, and you are advised to disable ActiveX controlsand related options. There is nothing wrong withbeing careful!In addition, in the IE security settings, we can only setInternet, local Intranet, trusted sites, restricted sites.However, Microsoft to hide the "my computer" safety set here,by modifying the registry to the options open, so that we canhave more choices in dealing with the control of ActiveX andApplets, and have a greater impact on the local computersecurity.
The following is the specific method: open the "Start Menu"run", in the pop-up" run "dialog box, enter the Regedit. exe, openthe registry editor, click the" + "in front of the numberexpanded to: HKEY_CURRE-NT_USER\Software\Microsoft\Windows\CurrentVersion\InternetSettings\Zones\0, DWORD f ind the valueof"Flags "ontheright side of thewindow, the default key valueis sixteen hexadecimal 21 (33 decimal) , click" Flags "in thepopup dialogbox will its value to" 1 "then, close the registryeditor. No need to restart the computer, restart the IE, clickTools > Options Internet Security tab again, see the "mycomputer" icon you will, here you can set the security levelof it. Set its security level higher, so that the preventionis more stringent.
Next scheme:
If it' s fixed, IP. Then you can choose the proxy server.
- 自己的如何保护自己的电脑 ip 不让别人攻击掉线(How do you protect your computer IP from being dropped)相关文档
- 2018年惠济区视频监控建设项目清单及招标需求参数
- 石化行业工控安全解决方案
- SEED:一套计算机安全教育的教学实验机制
- 竞争性谈判文件
- 北大校园网安全服务
- 攻击防御ARP、IP欺骗及内外网流量攻击.doc
半月湾($59.99/年),升级带宽至200M起步 三网CN2 GIA线路
在前面的文章中就有介绍到半月湾Half Moon Bay Cloud服务商有提供洛杉矶DC5数据中心云服务器,这个堪比我们可能熟悉的某服务商,如果我们有用过的话会发现这个服务商的价格比较贵,而且一直缺货。这里,于是半月湾服务商看到机会来了,于是有新增同机房的CN2 GIA优化线路。在之前的文章中介绍到Half Moon Bay Cloud DC5机房且进行过测评。这次的变化是从原来基础的年付49....

弘速云20.8元/月 ,香港云服务器 2核 1g 10M
弘速云元旦活动本公司所销售的弹性云服务器、虚拟专用服务器(VPS)、虚拟主机等涉及网站接入服务的云产品由具备相关资质的第三方合作服务商提供官方网站:https://www.hosuyun.com公司名:弘速科技有限公司香港沙田直营机房采用CTGNET高速回国线路弹性款8折起优惠码:hosu1-1 测试ip:69.165.77.50地区CPU内存硬盘带宽价格购买地址香港沙田2-8核1-16G20-...

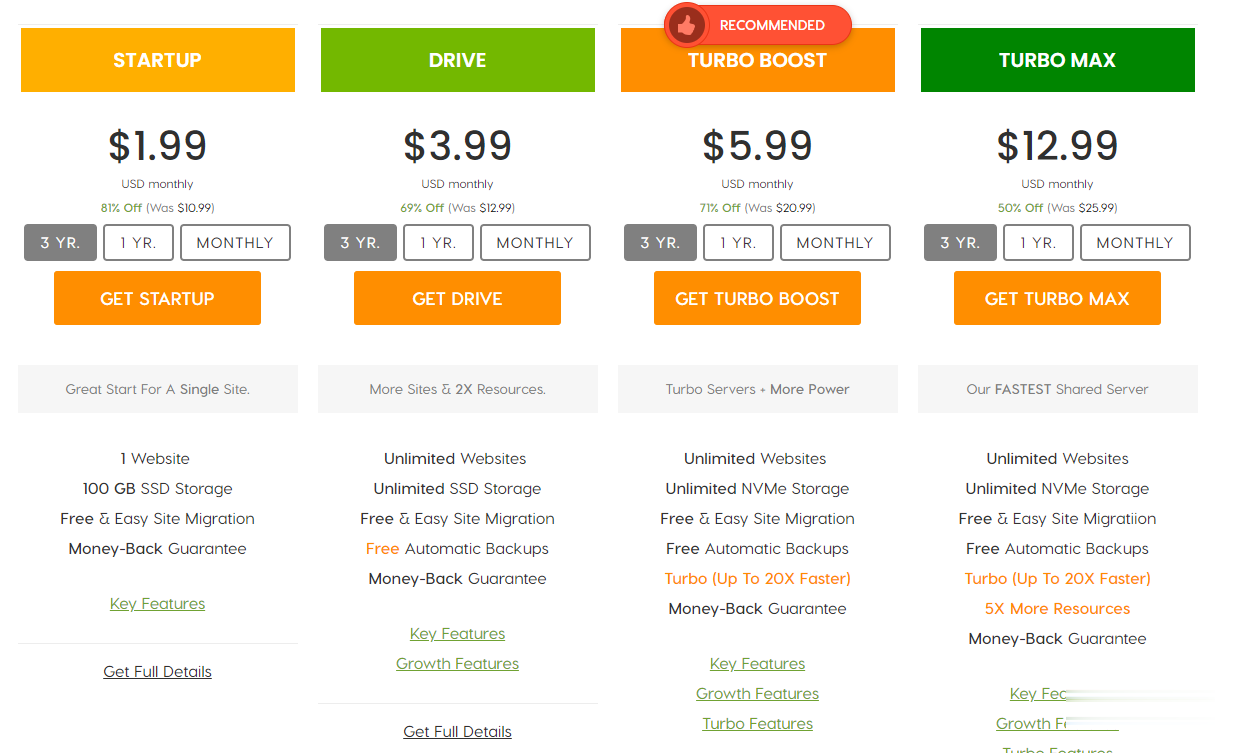
A2Hosting三年付$1.99/月,庆祝18周年/WordPress共享主机最高优惠81%/100GB SSD空间/无限流量
A2Hosting主机,A2Hosting怎么样?A2Hosting是UK2集团下属公司,成立于2003年的老牌国外主机商,产品包括虚拟主机、VPS和独立服务器等,数据中心提供包括美国、新加坡softlayer和荷兰三个地区机房。A2Hosting在国外是一家非常大非常有名气的终合型主机商,拥有几百万的客户,非常值得信赖,国外主机论坛对它家的虚拟主机评价非常不错,当前,A2Hosting主机庆祝1...
-
绵阳电信绵阳电信宽带套餐资费推荐博客外链求博客外链方法ghostxp3GhostXP3电脑公司特别版V499怎么安装渗透测试网站渗透测试怎么做?今日热点怎么删除怎么删除手机百度实时热点硬盘人500G的硬盘容量是多少啊?保护气球什么气球可以骑?2012年正月十五农历2012年正月15早上9点多生的!命里缺什么!是什么命相二层交换机二层交换机是什么意思,三层呢iphone6上市时间苹果6什么时候出来